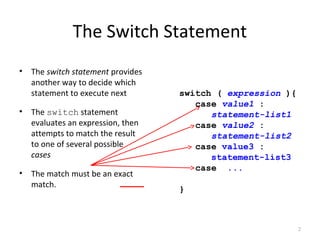
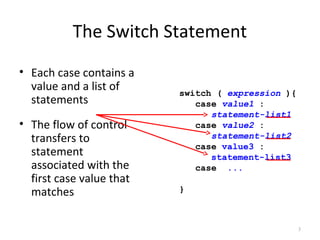
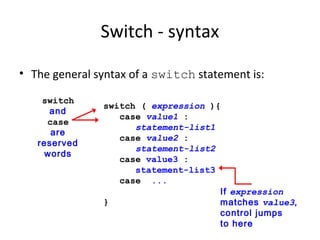
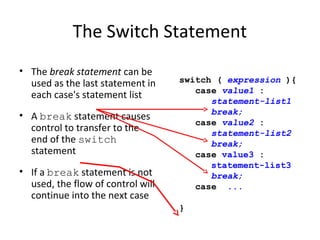
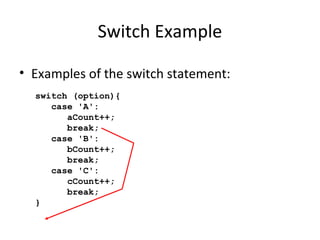
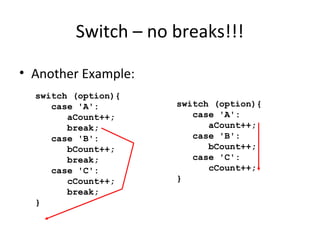
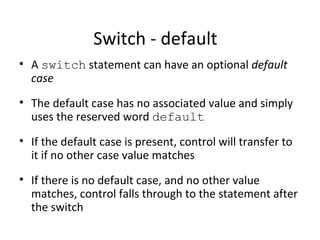
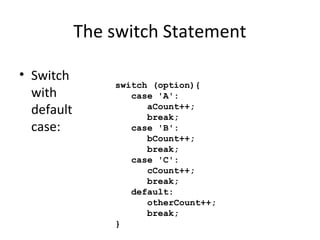
The switch statement provides an alternative way to execute different blocks of code based on the value of an expression. The switch statement evaluates an expression and attempts to match it to the values specified in each case. If a match is found, control passes to that case's statement list. A break statement at the end of each case causes control to pass to the end of the switch statement after execution. If no break is included, execution will continue into the next case. A default case can also be specified to handle any values not explicitly matched.