This document provides definitions and explanations of various file formats and compression techniques, including:
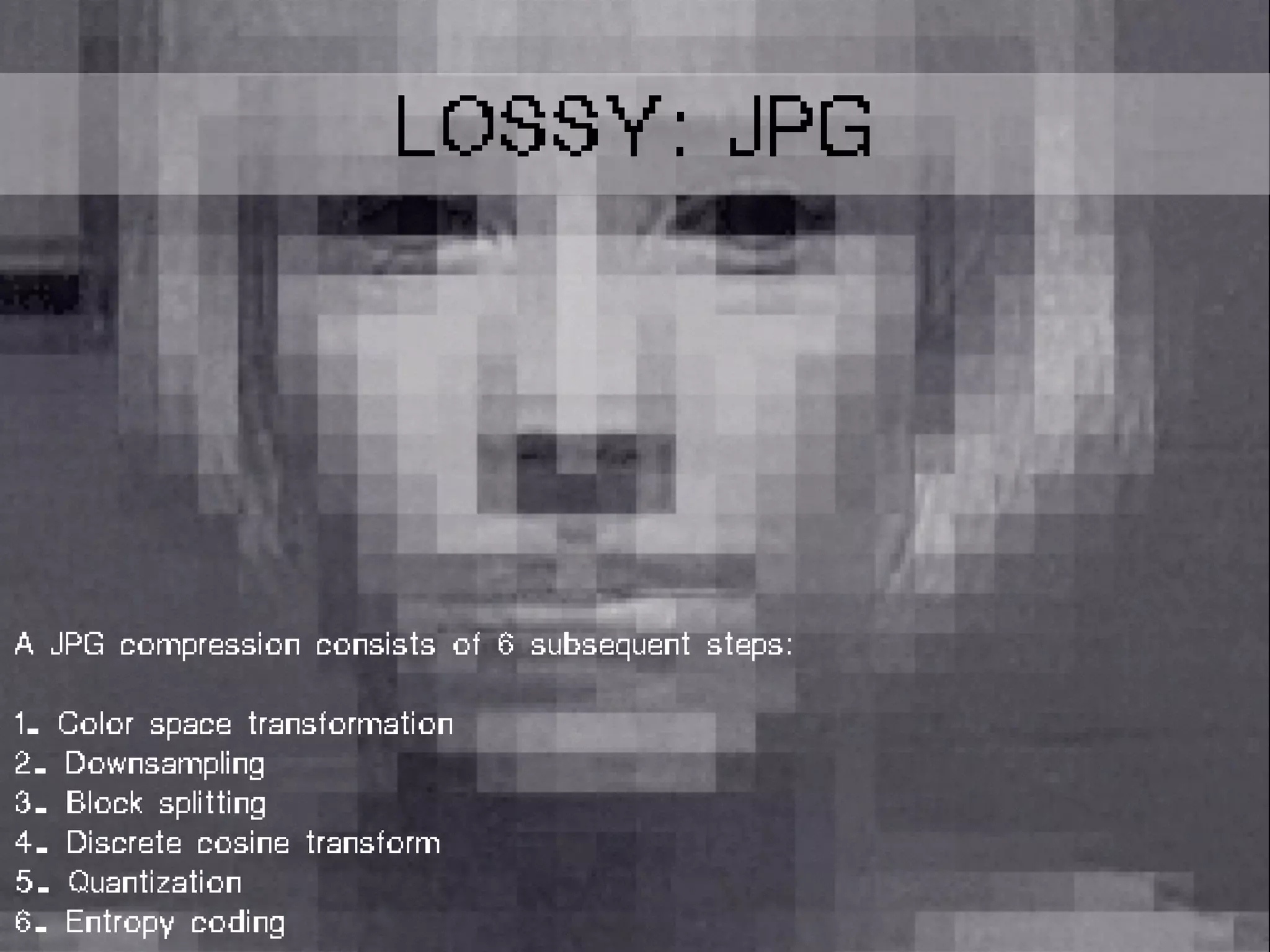
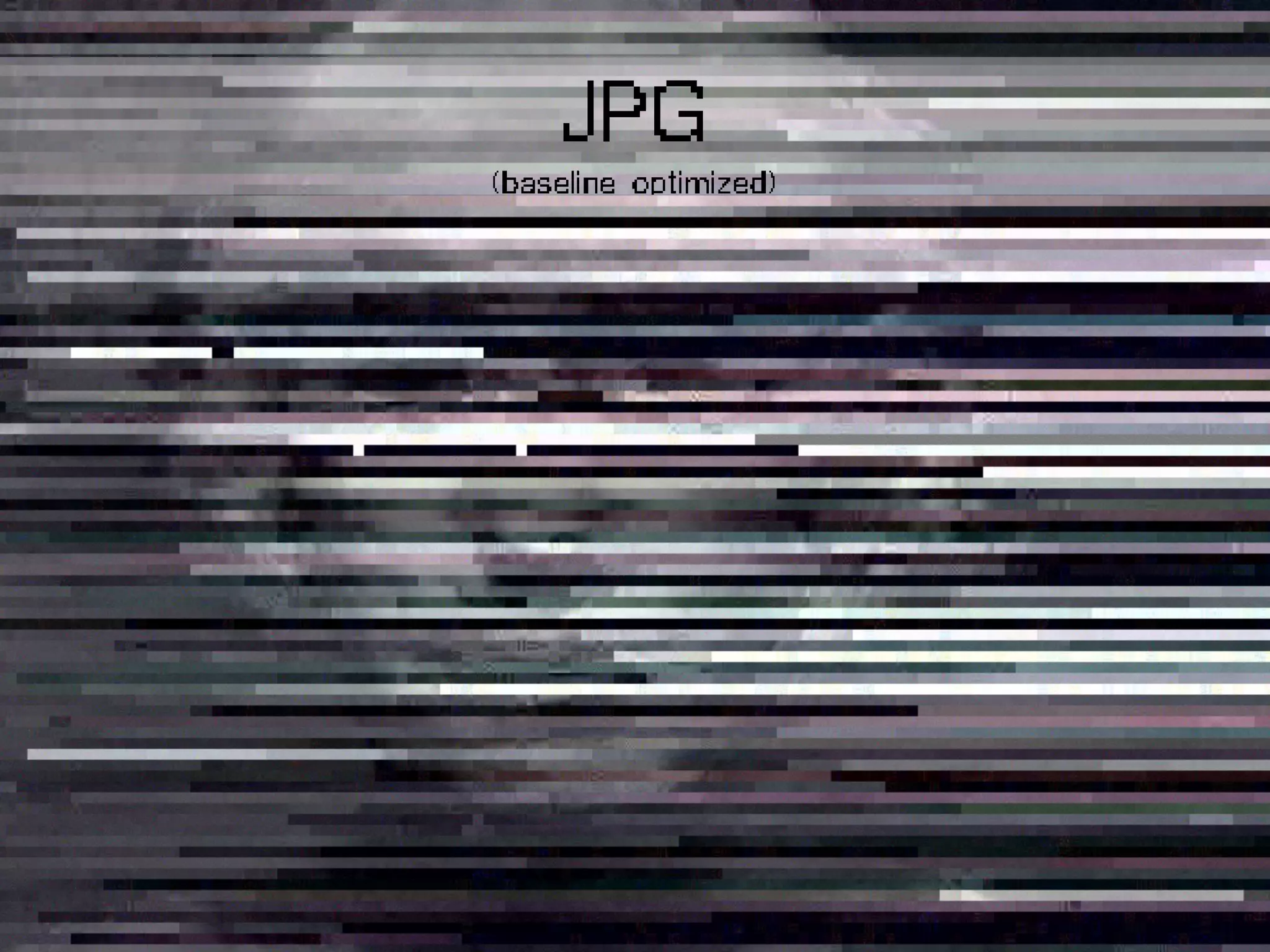
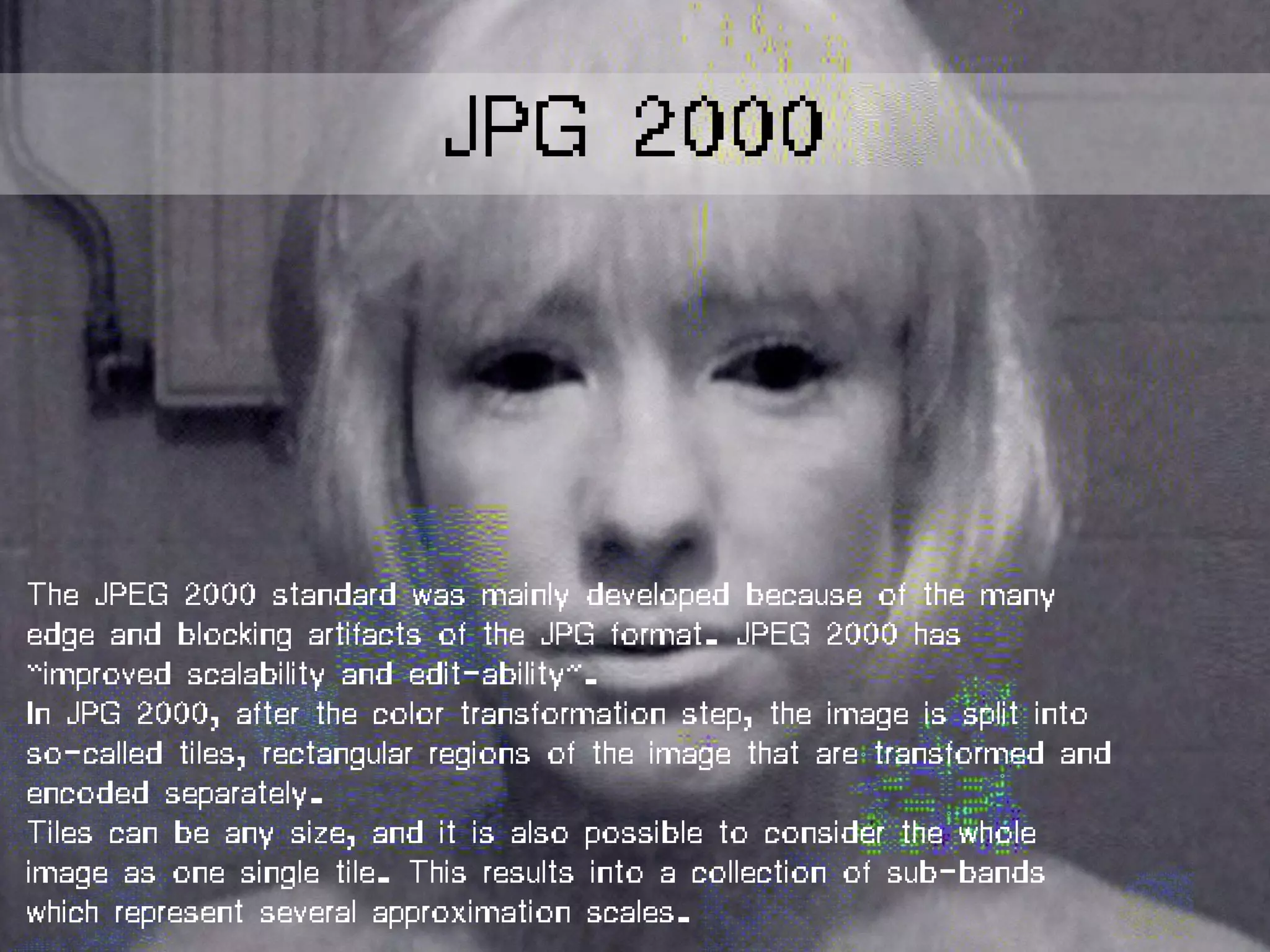
- Lossless vs lossy data compression
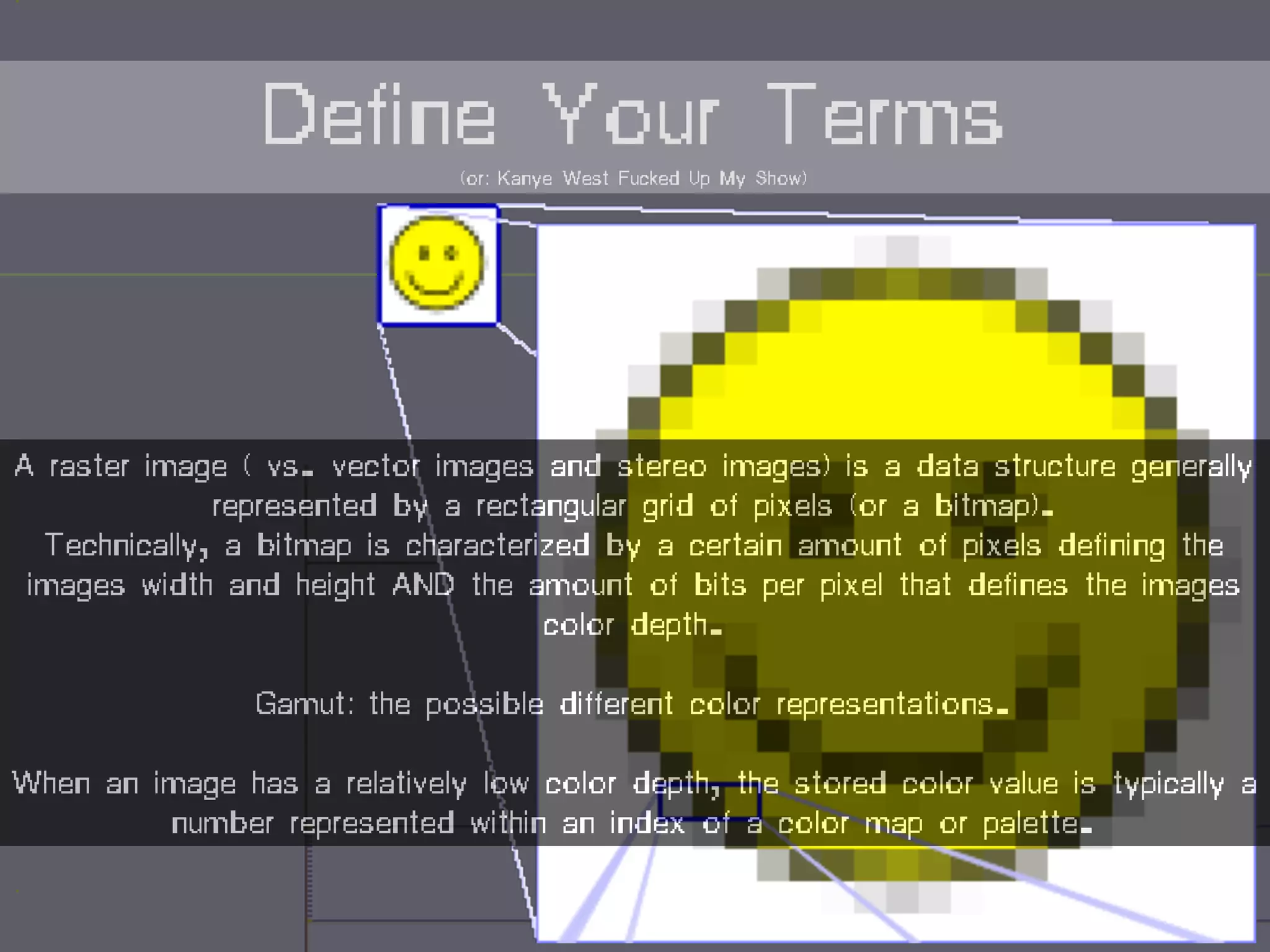
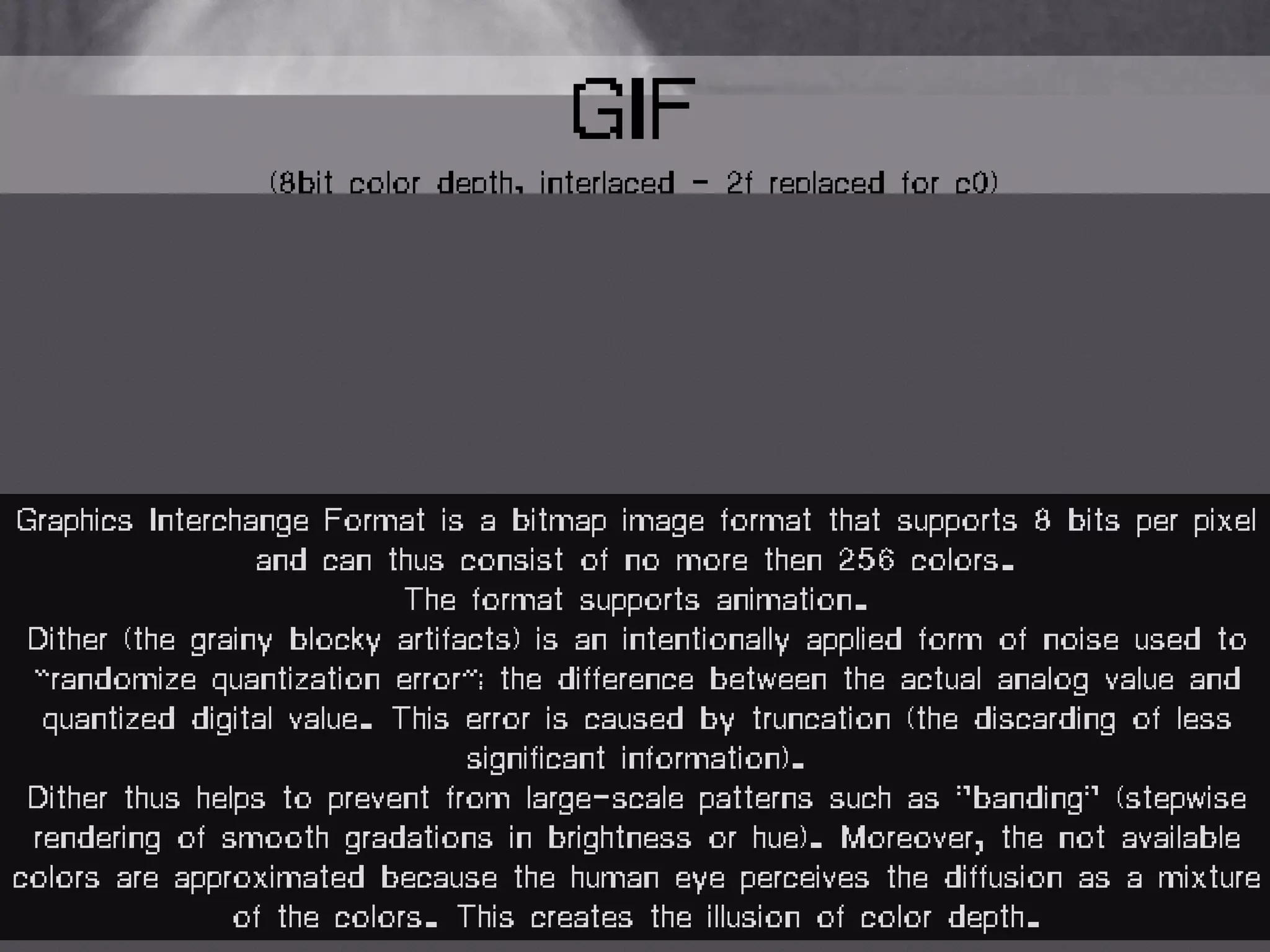
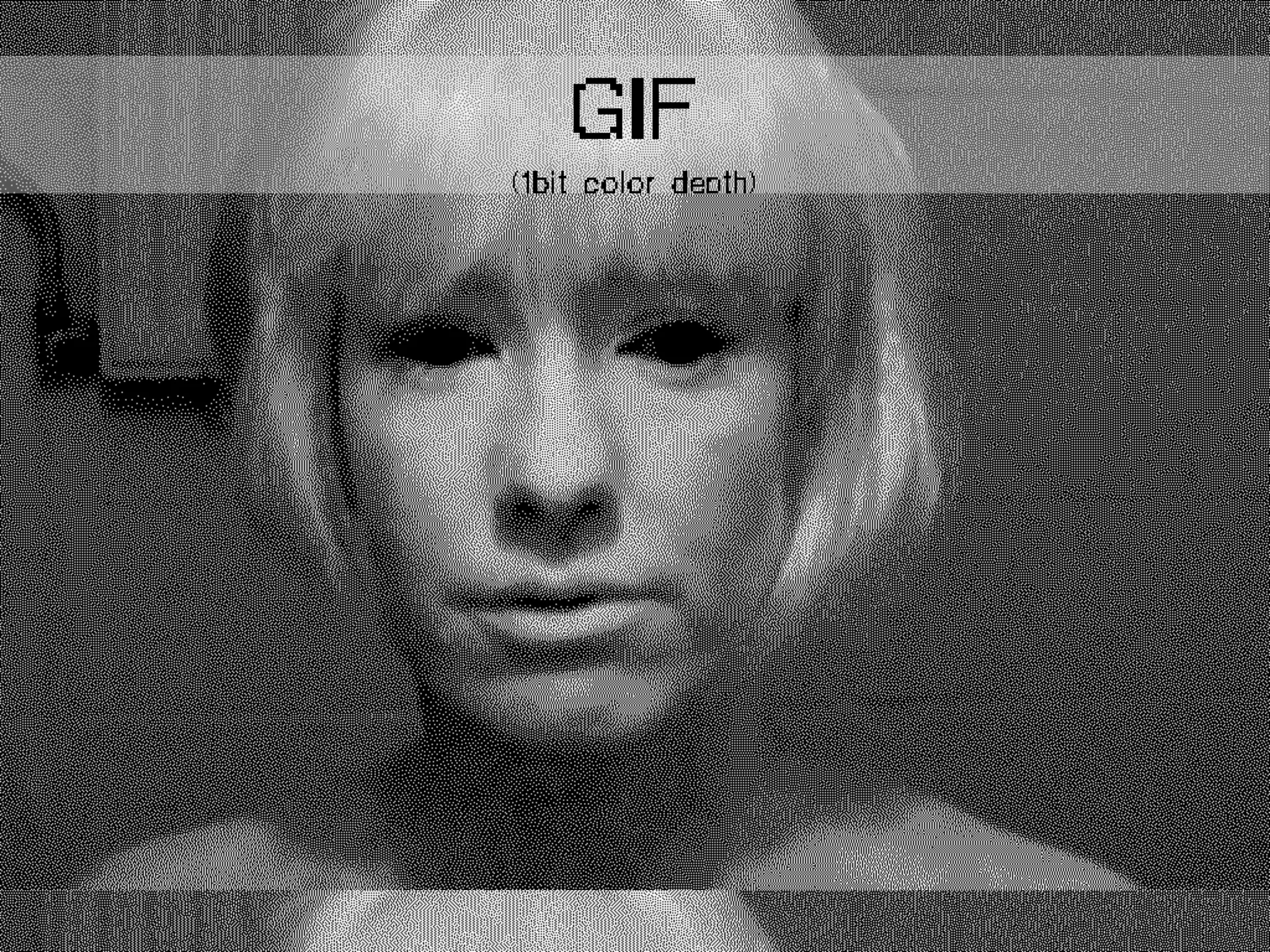
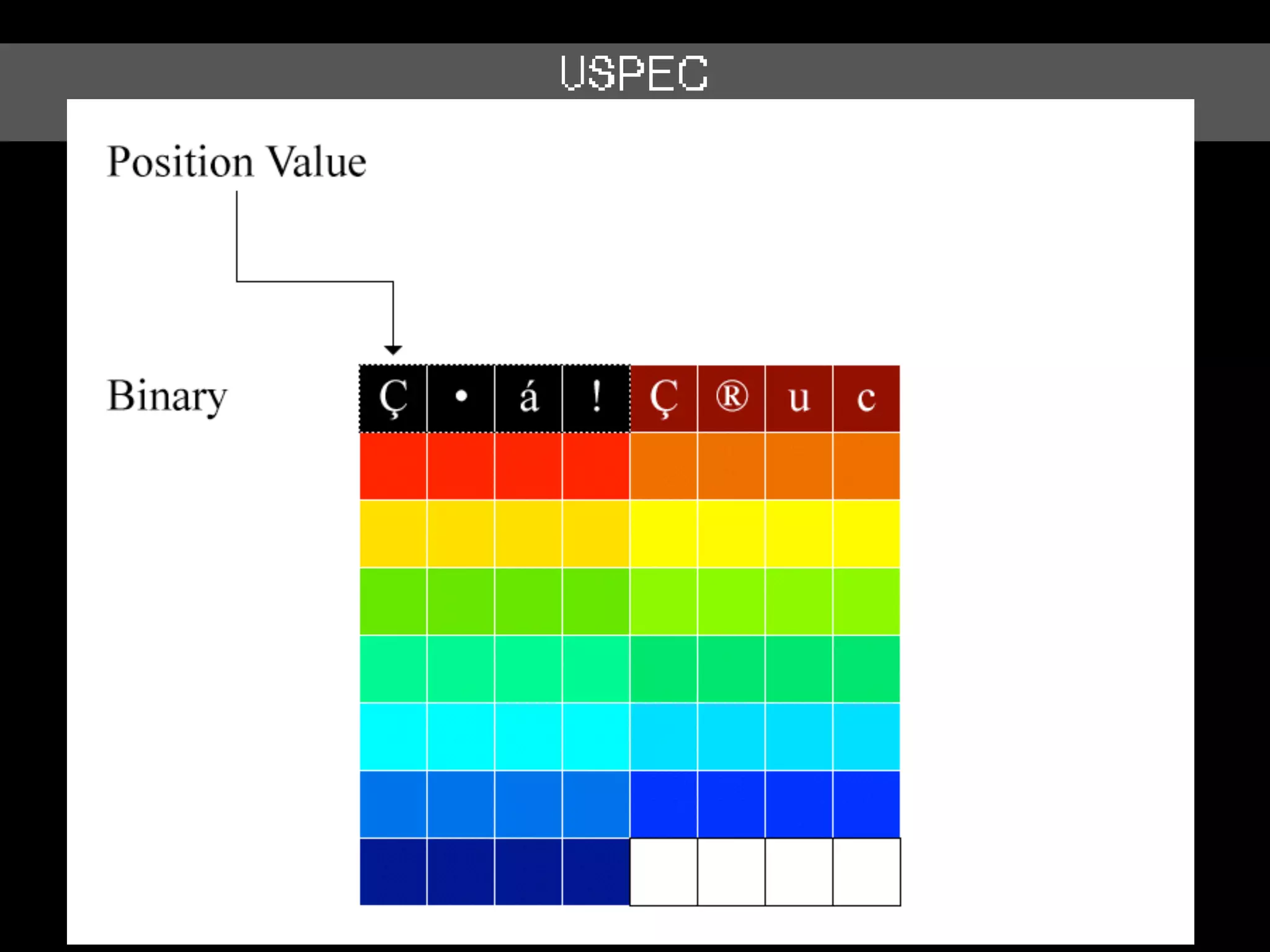
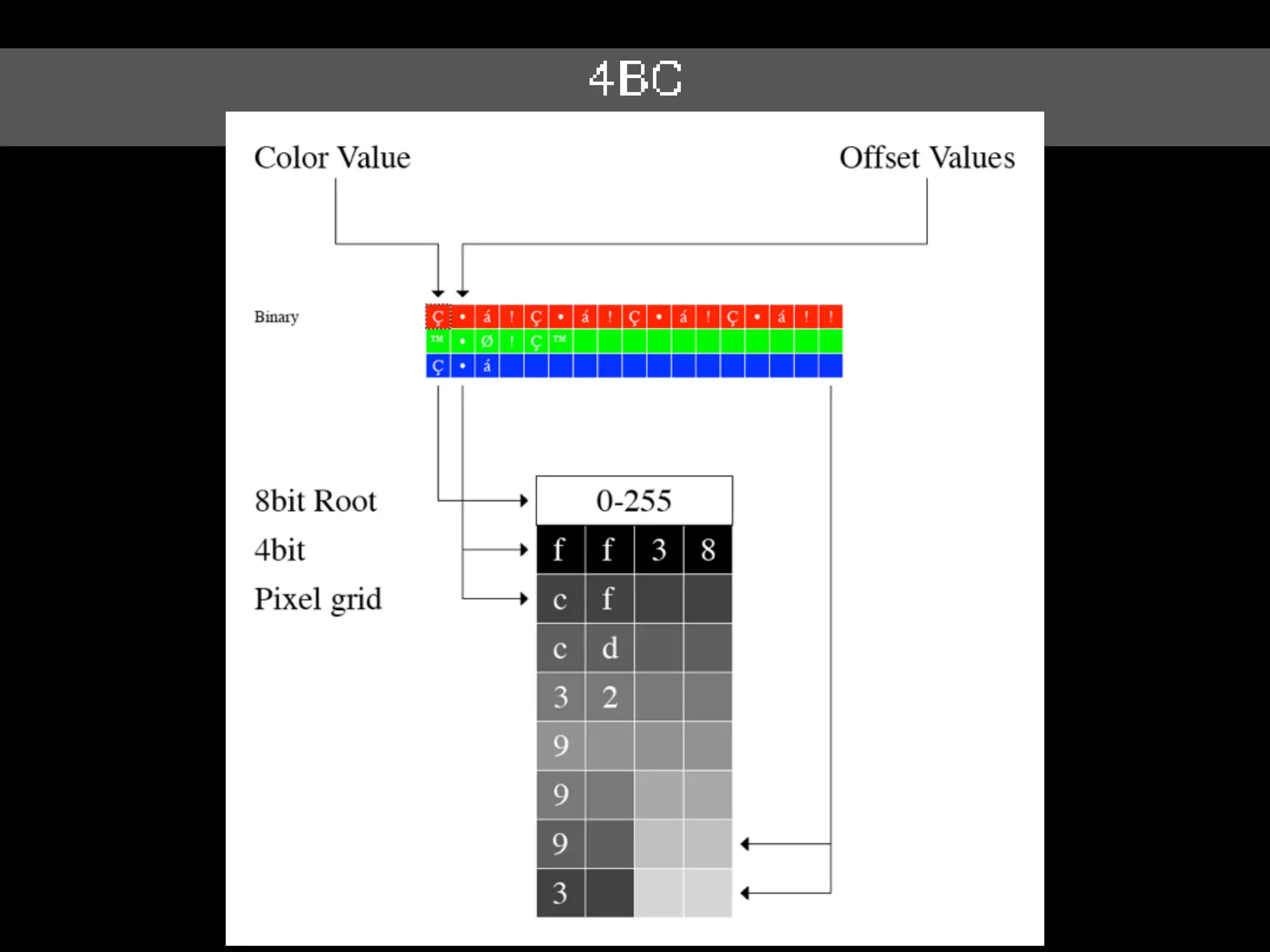
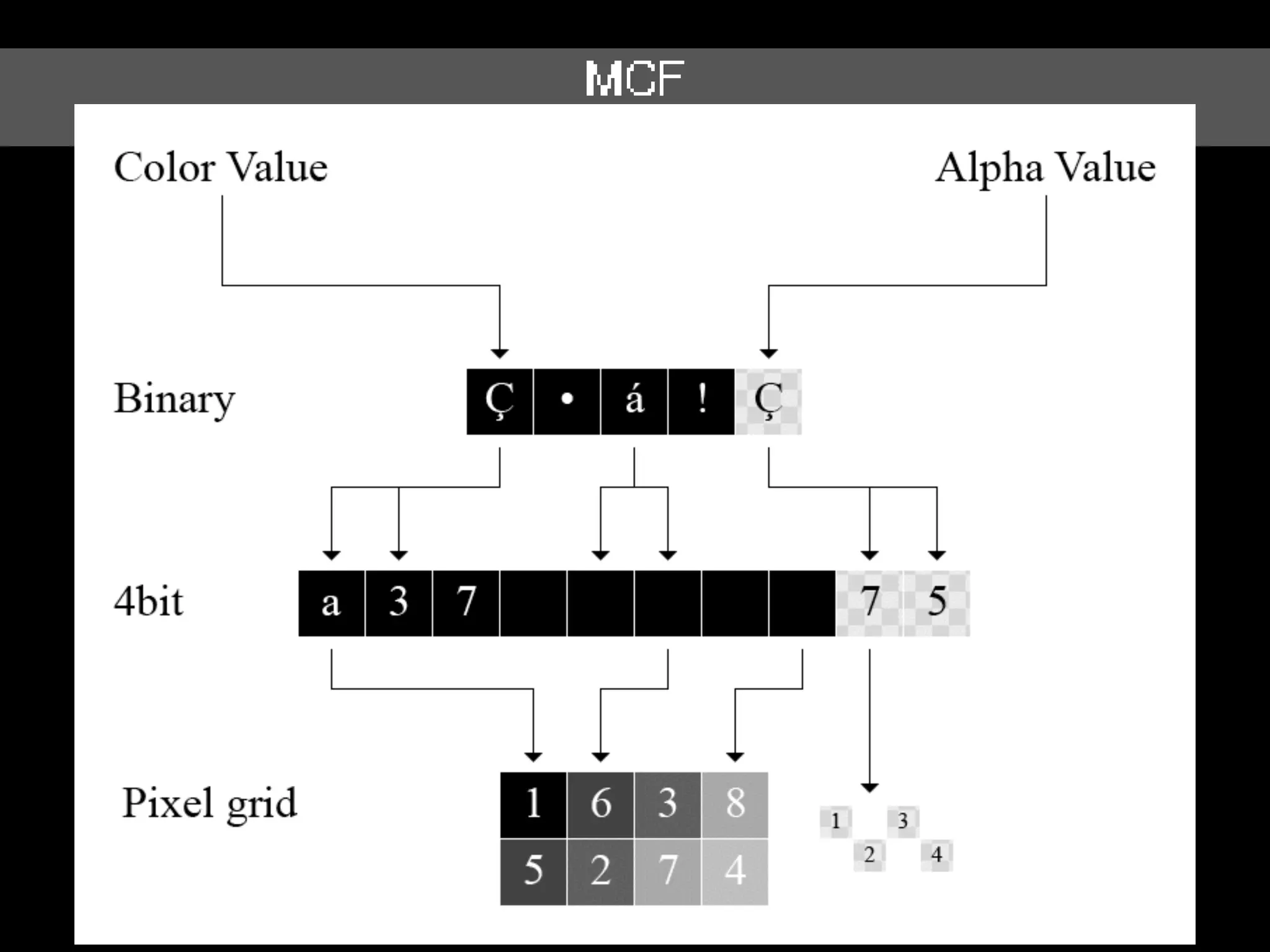
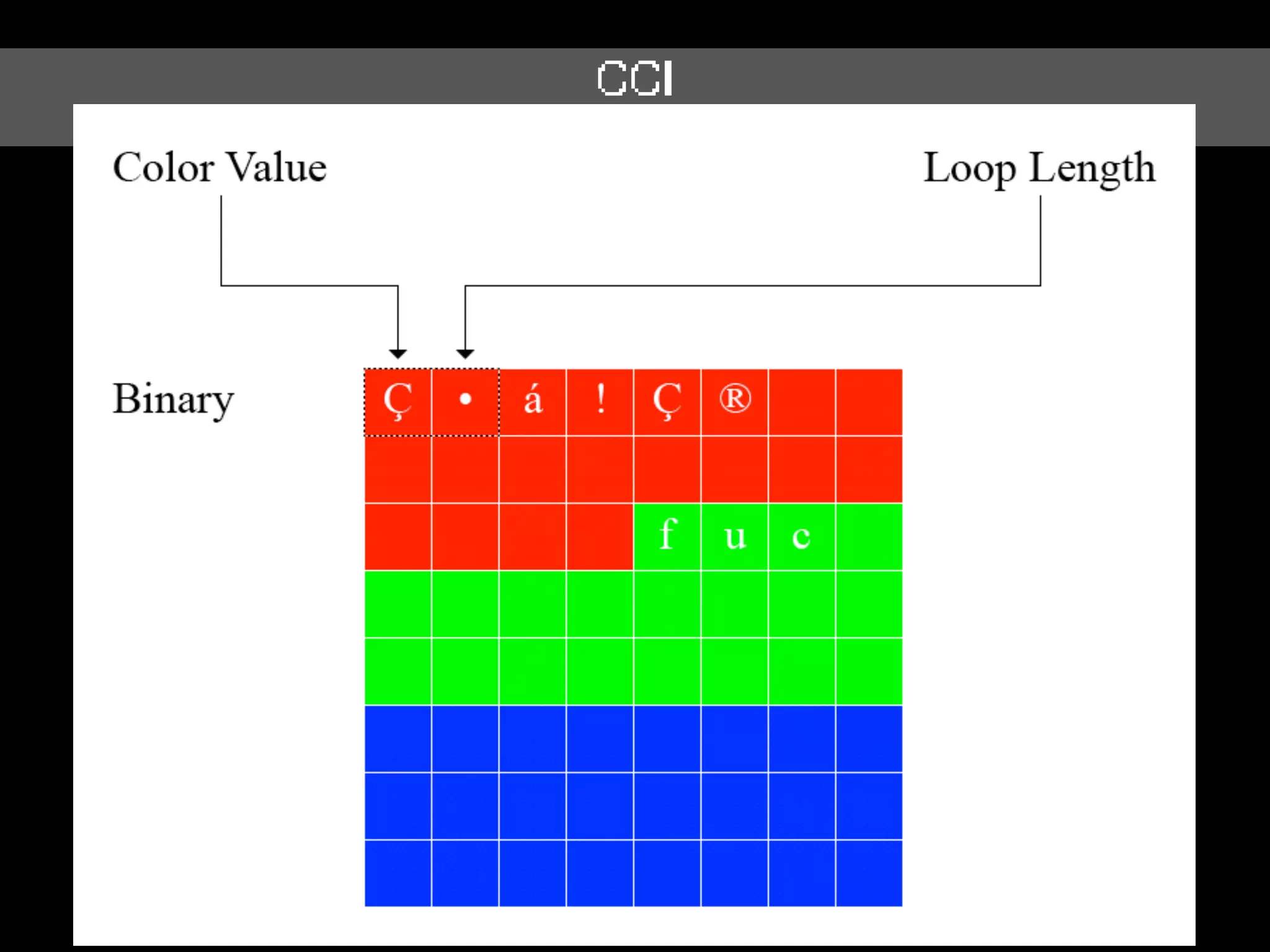
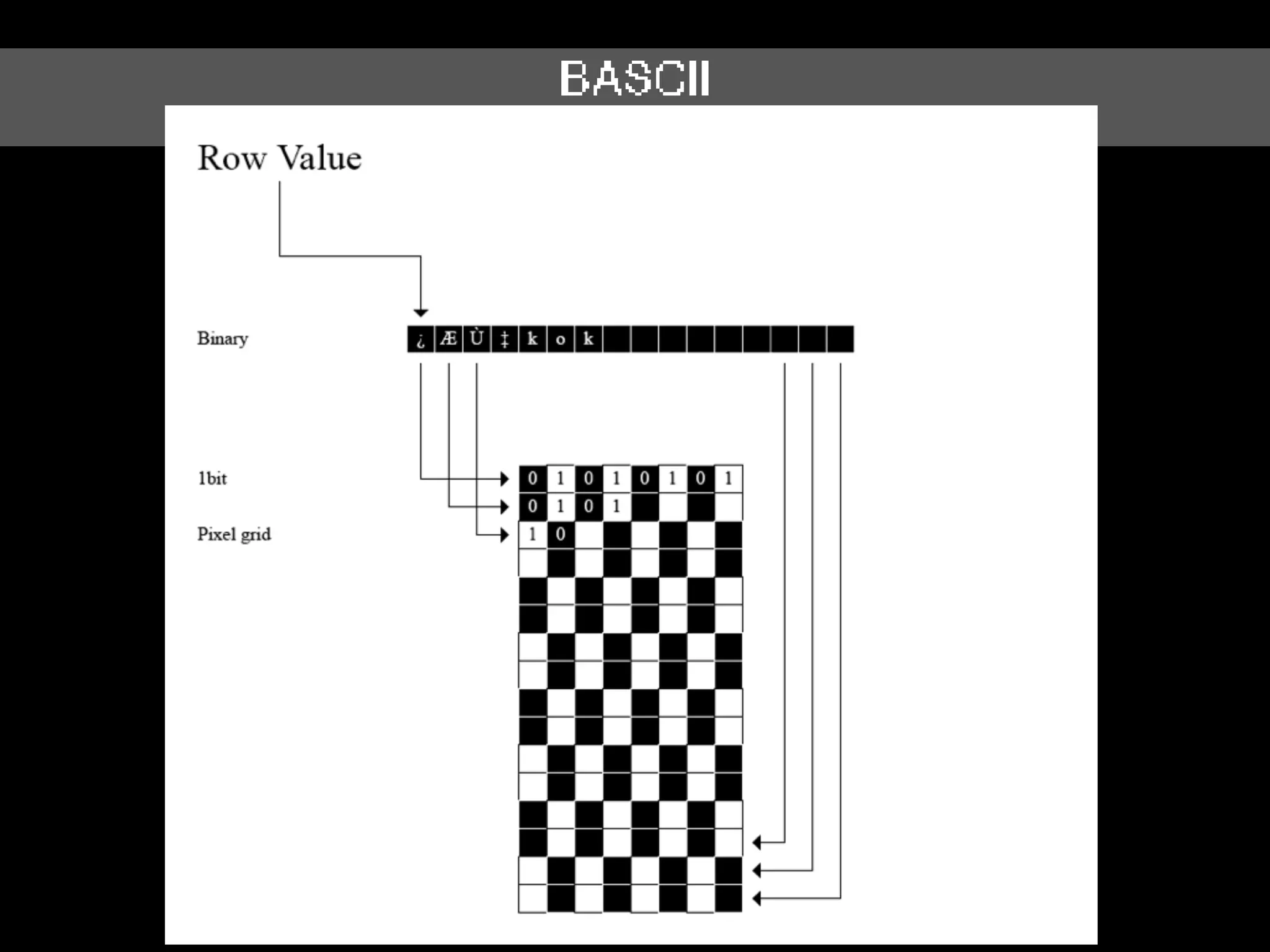
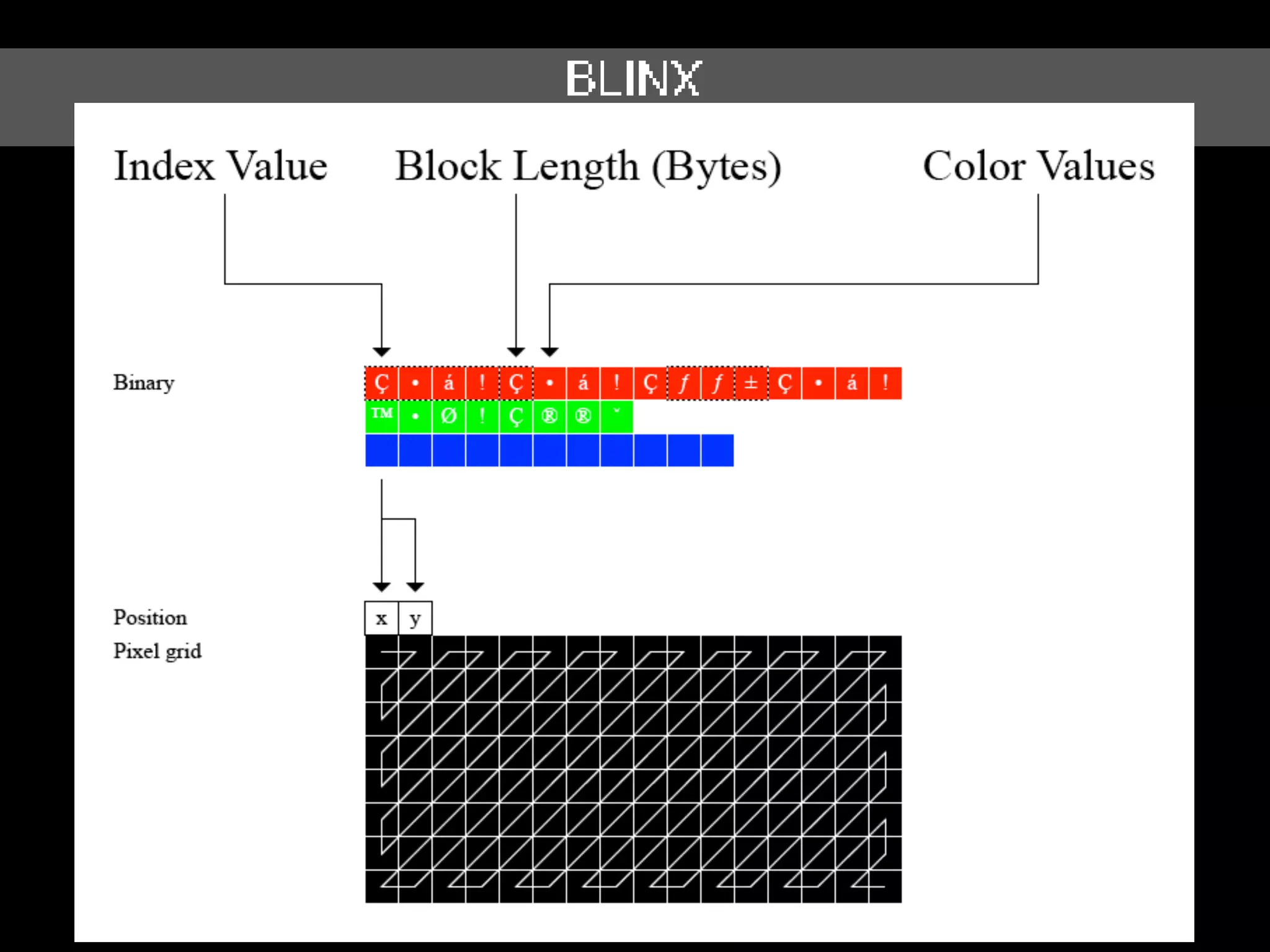
- Raster images and how color depth affects stored color values
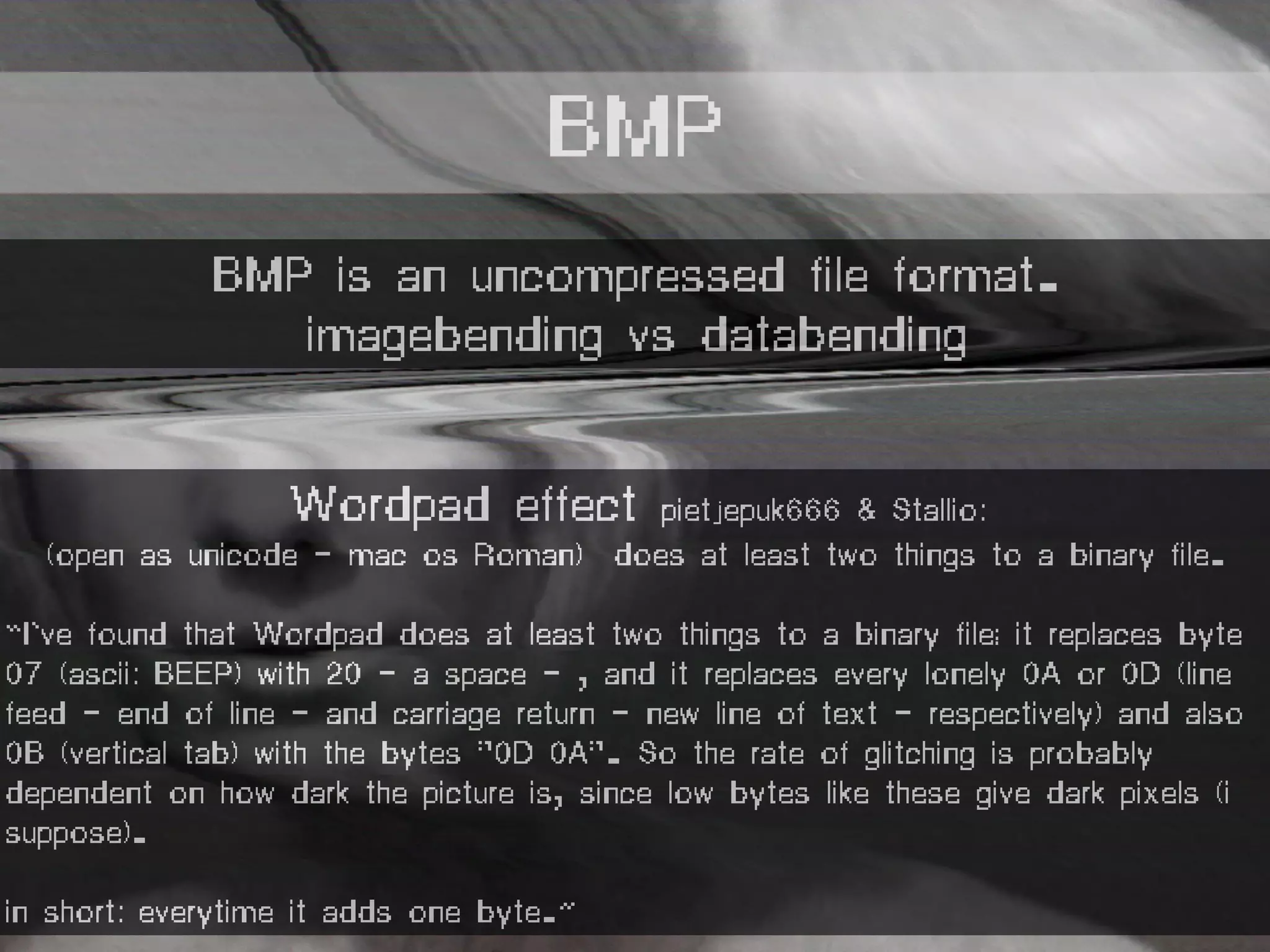
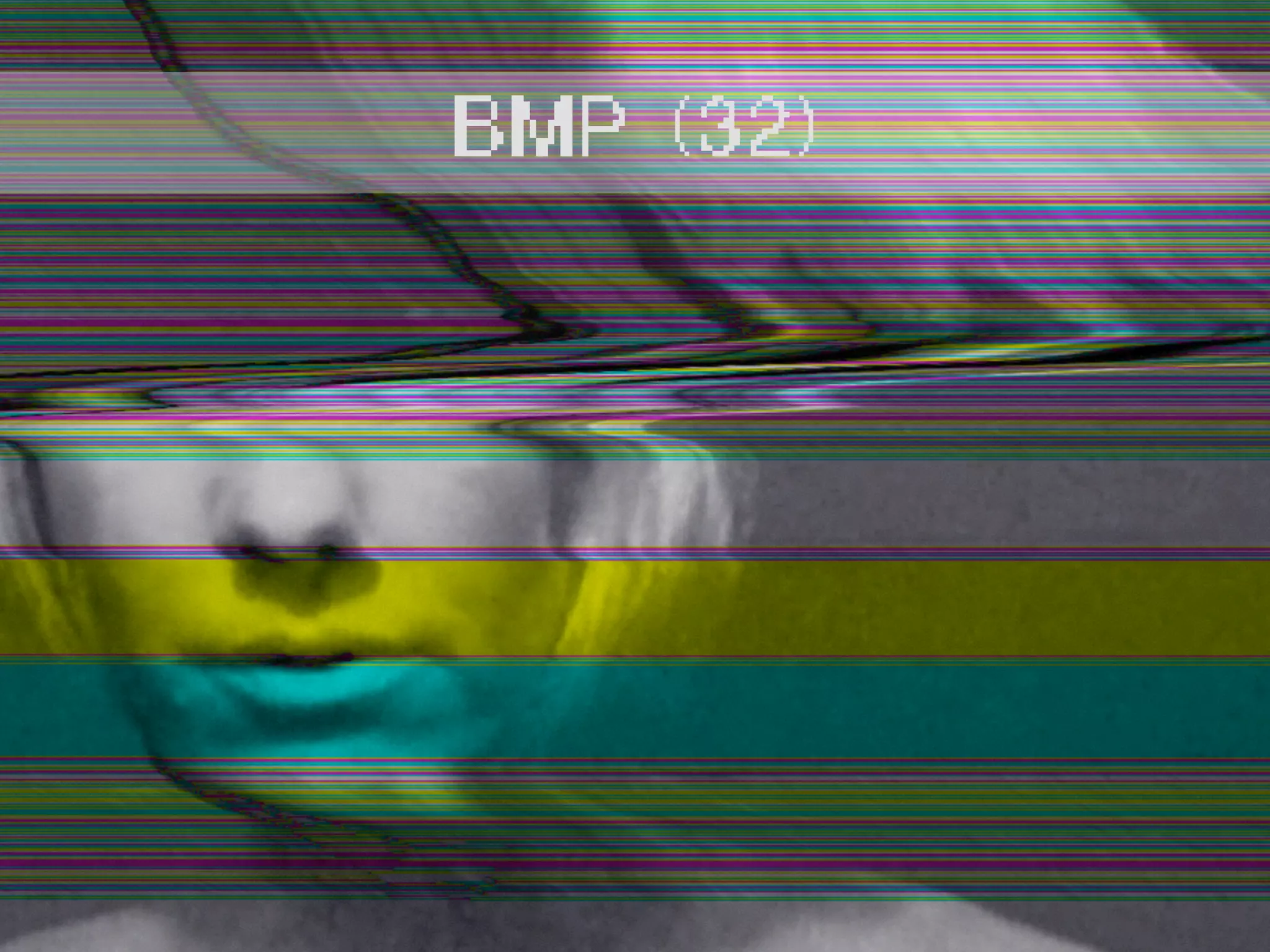
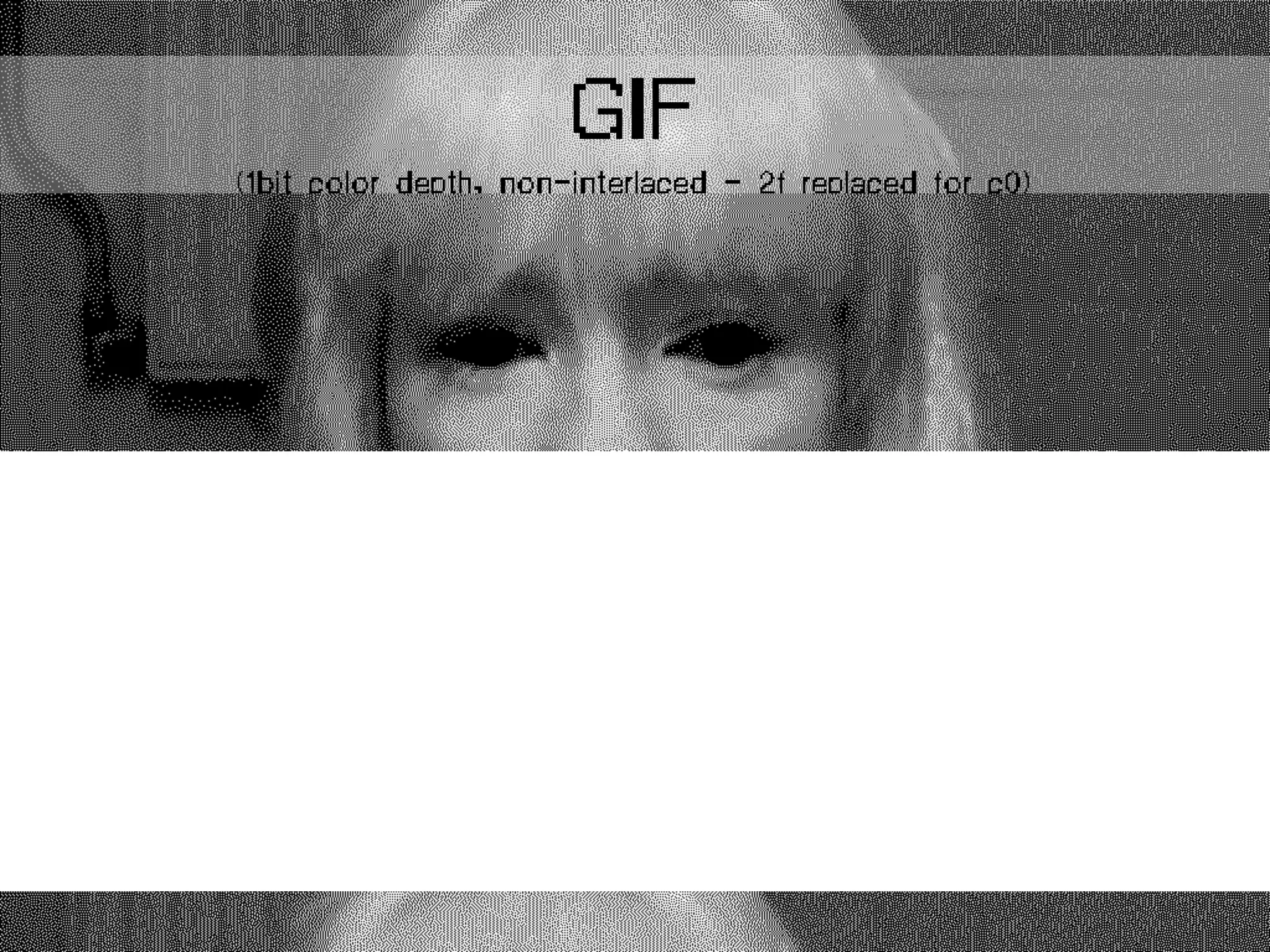
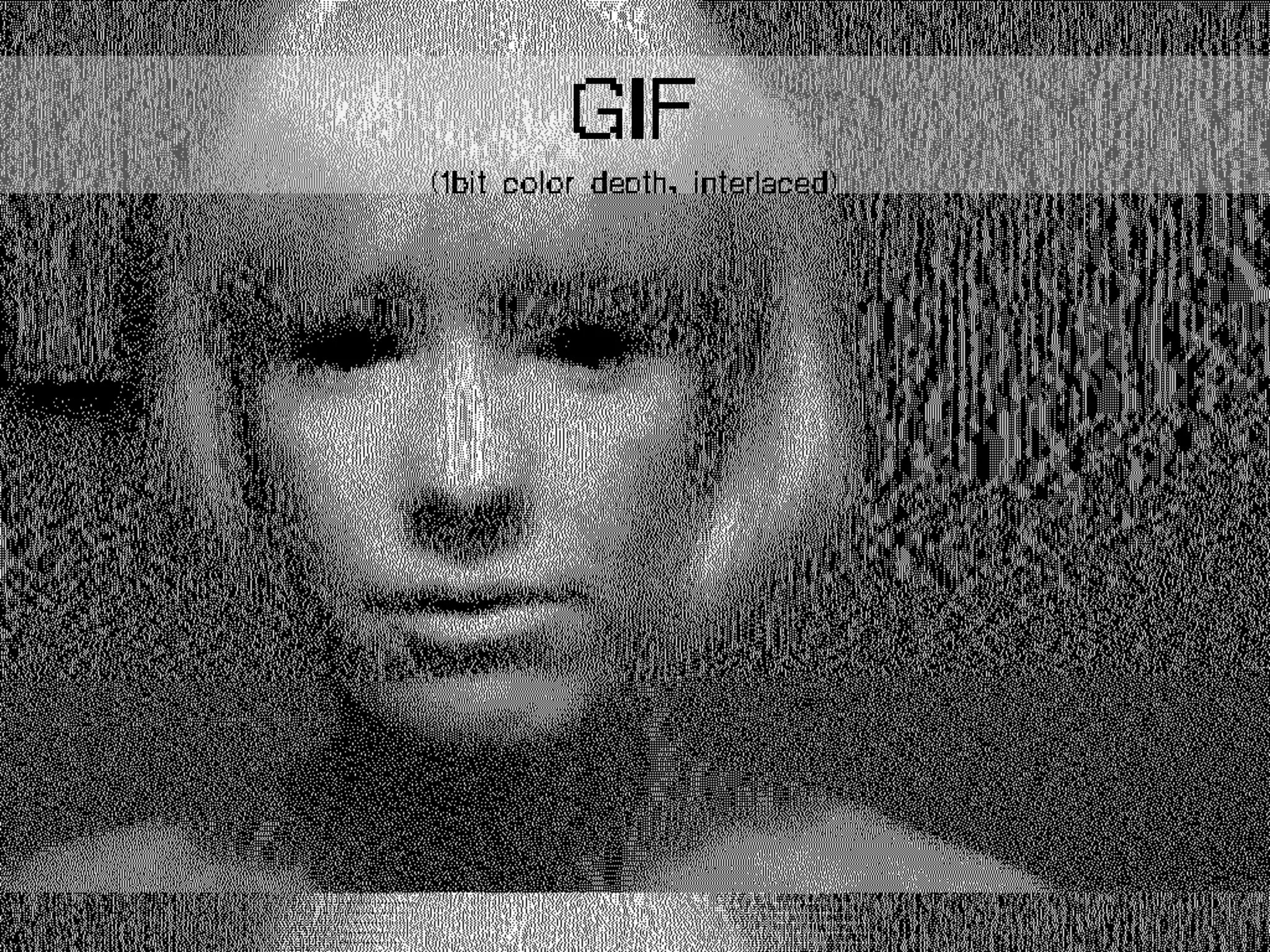
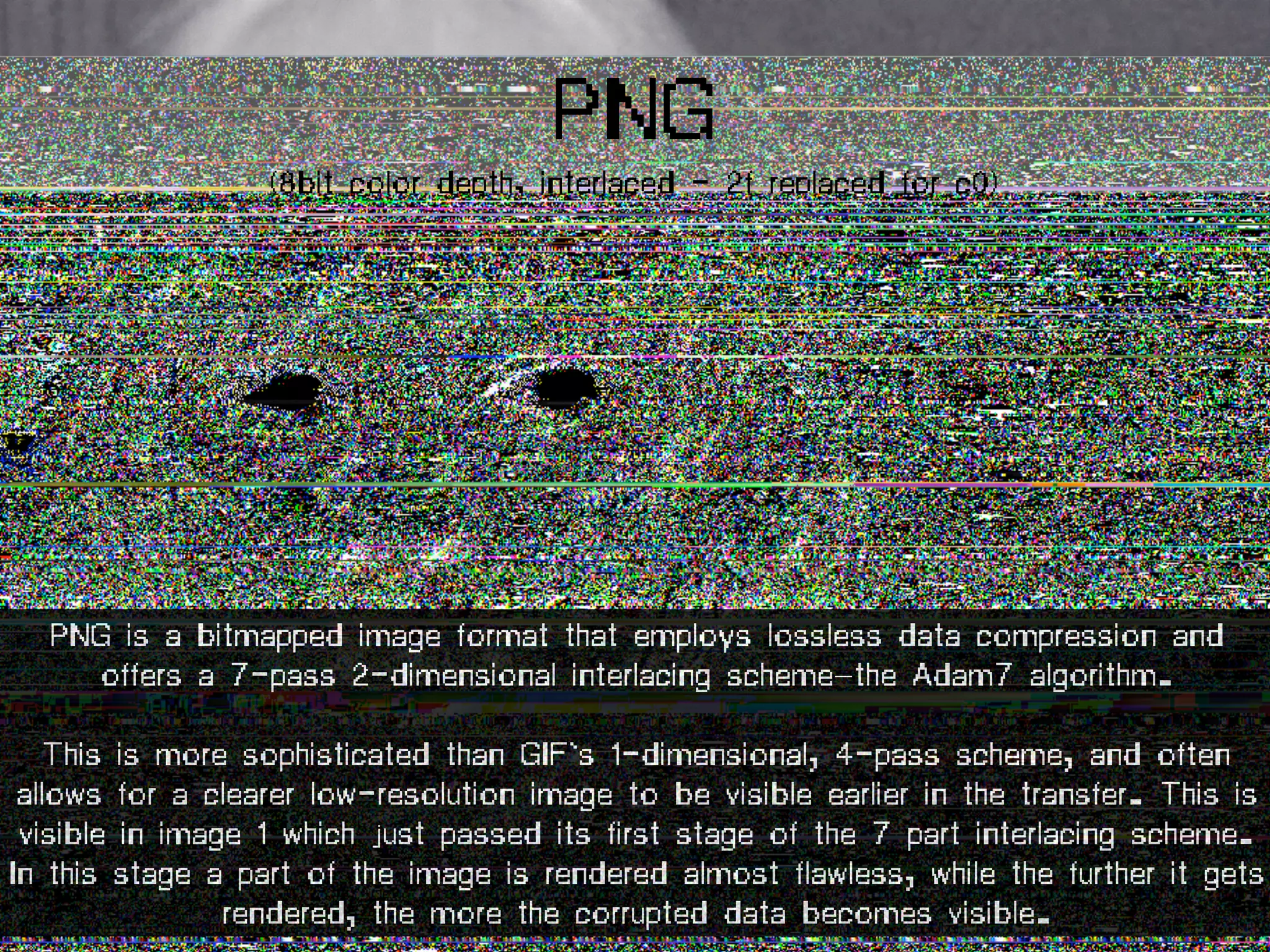
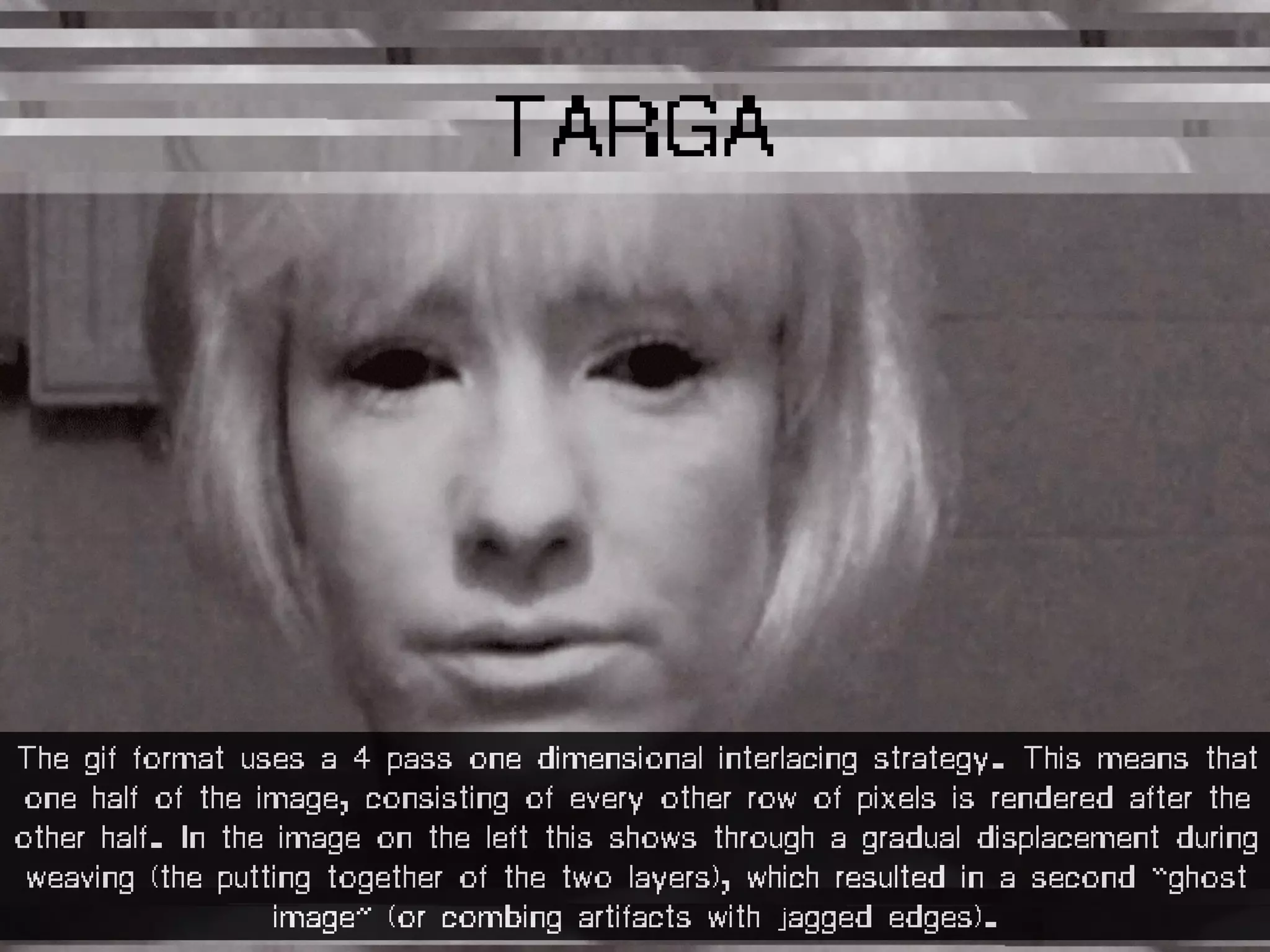
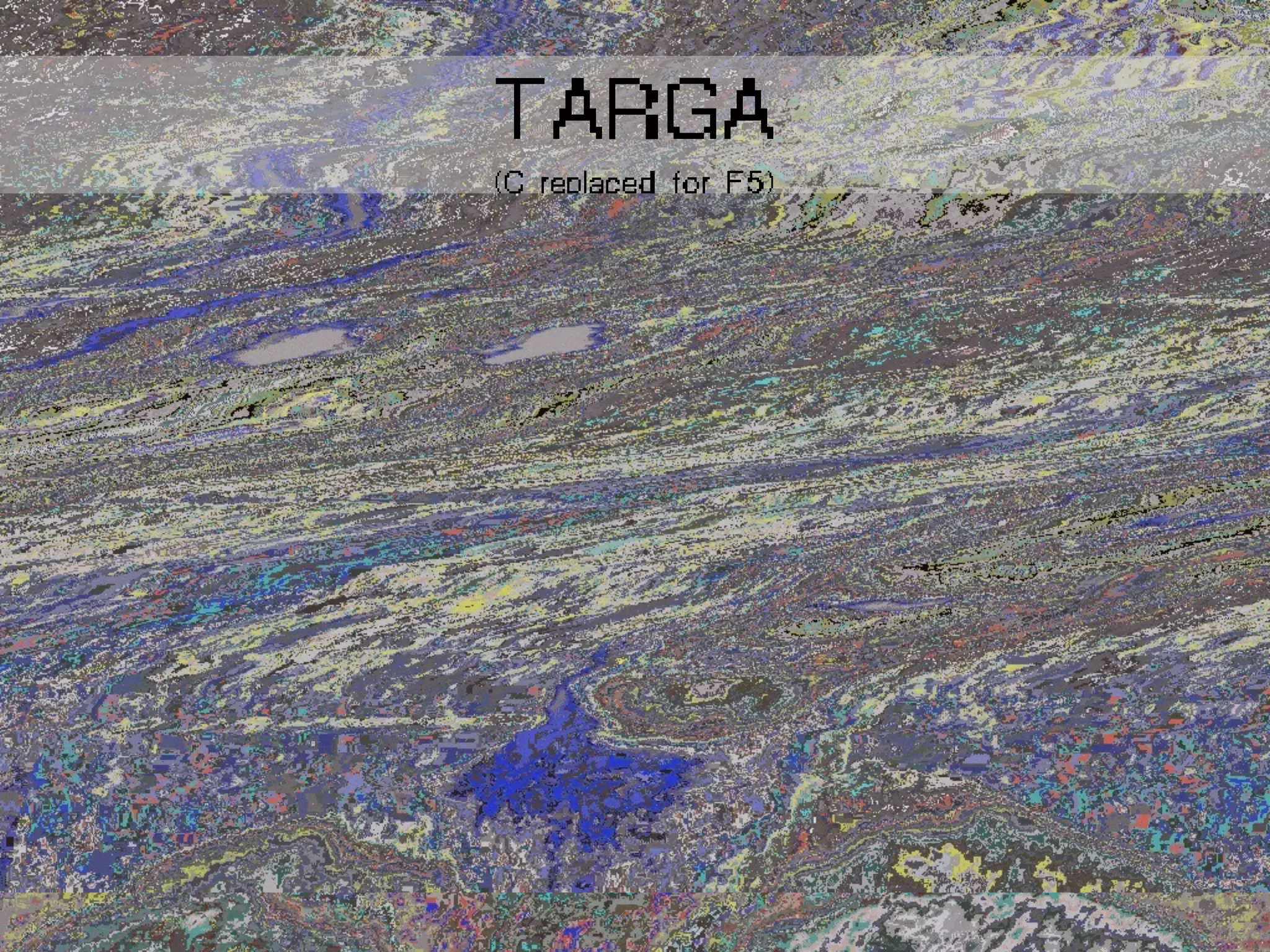
- Image glitching techniques like imagebending and databending
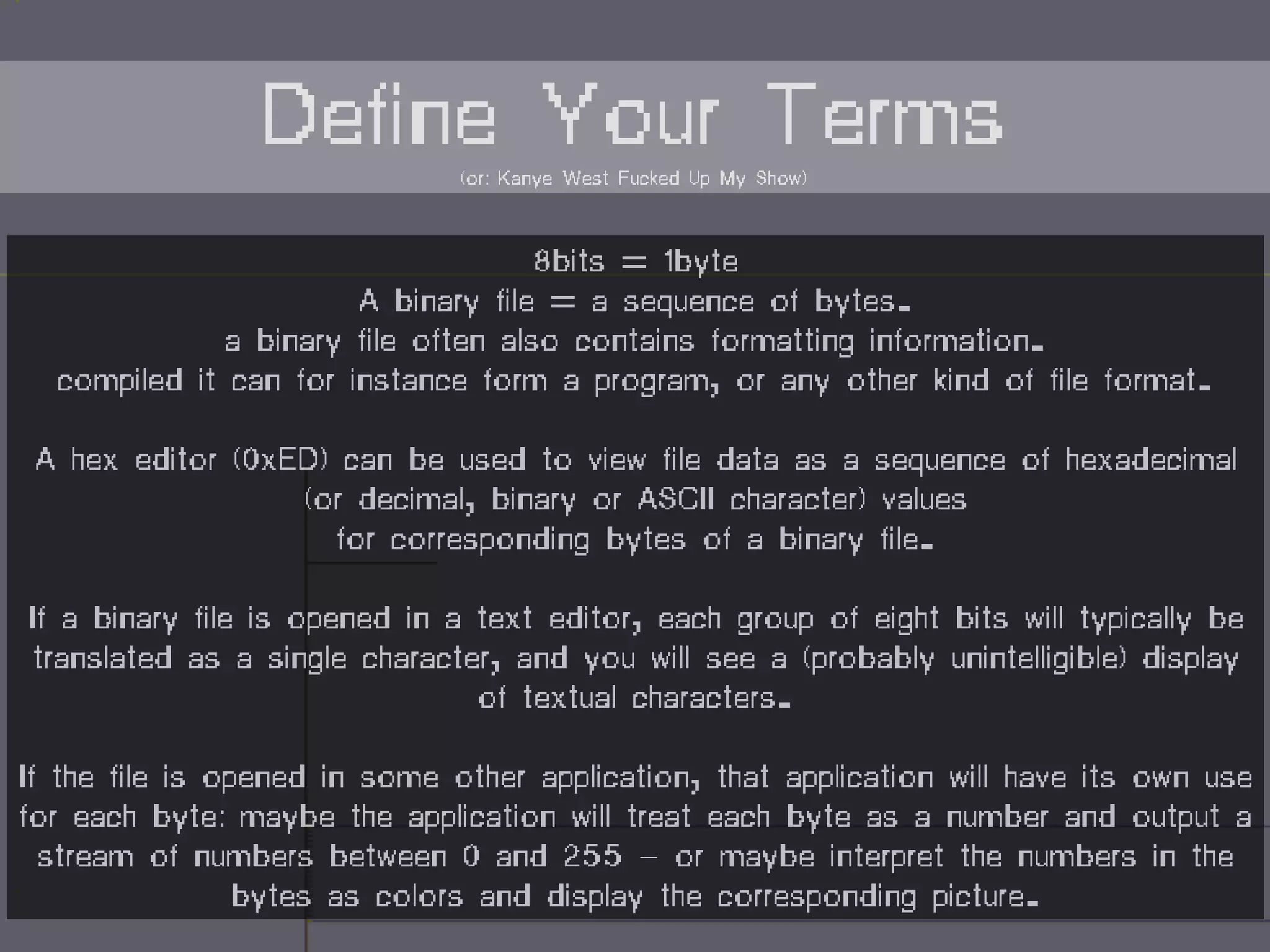
- How bytes and binary files are structured
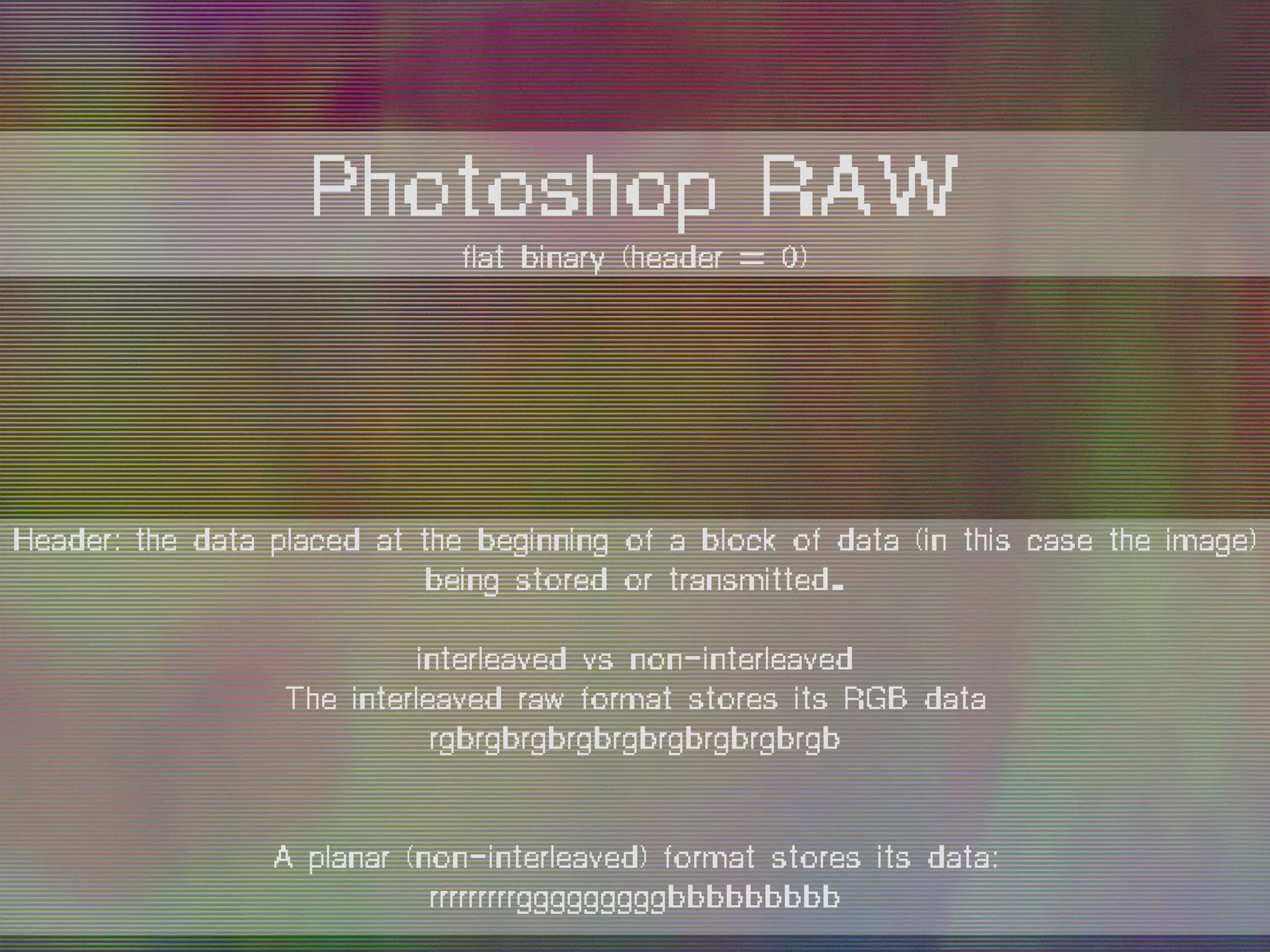
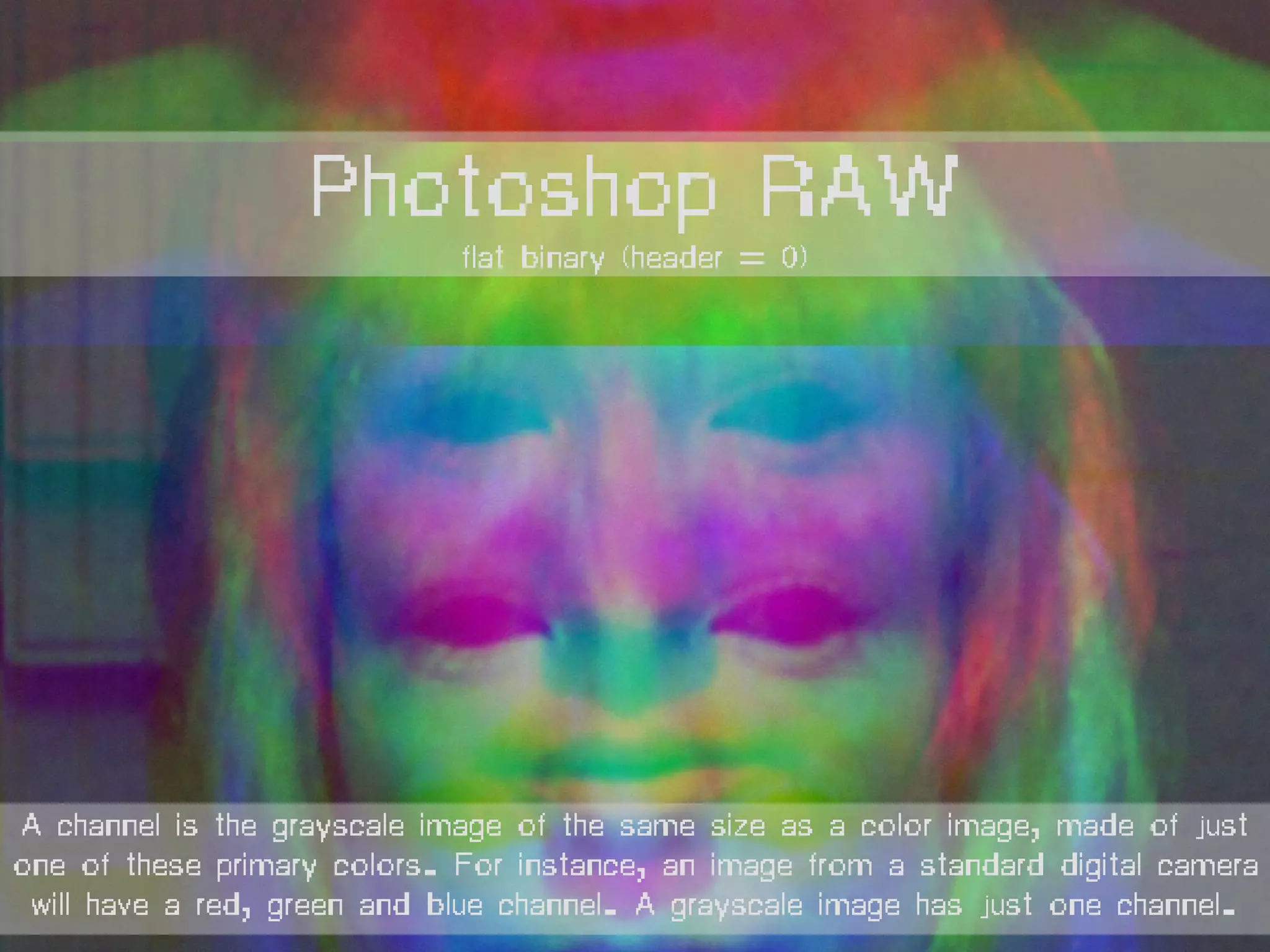
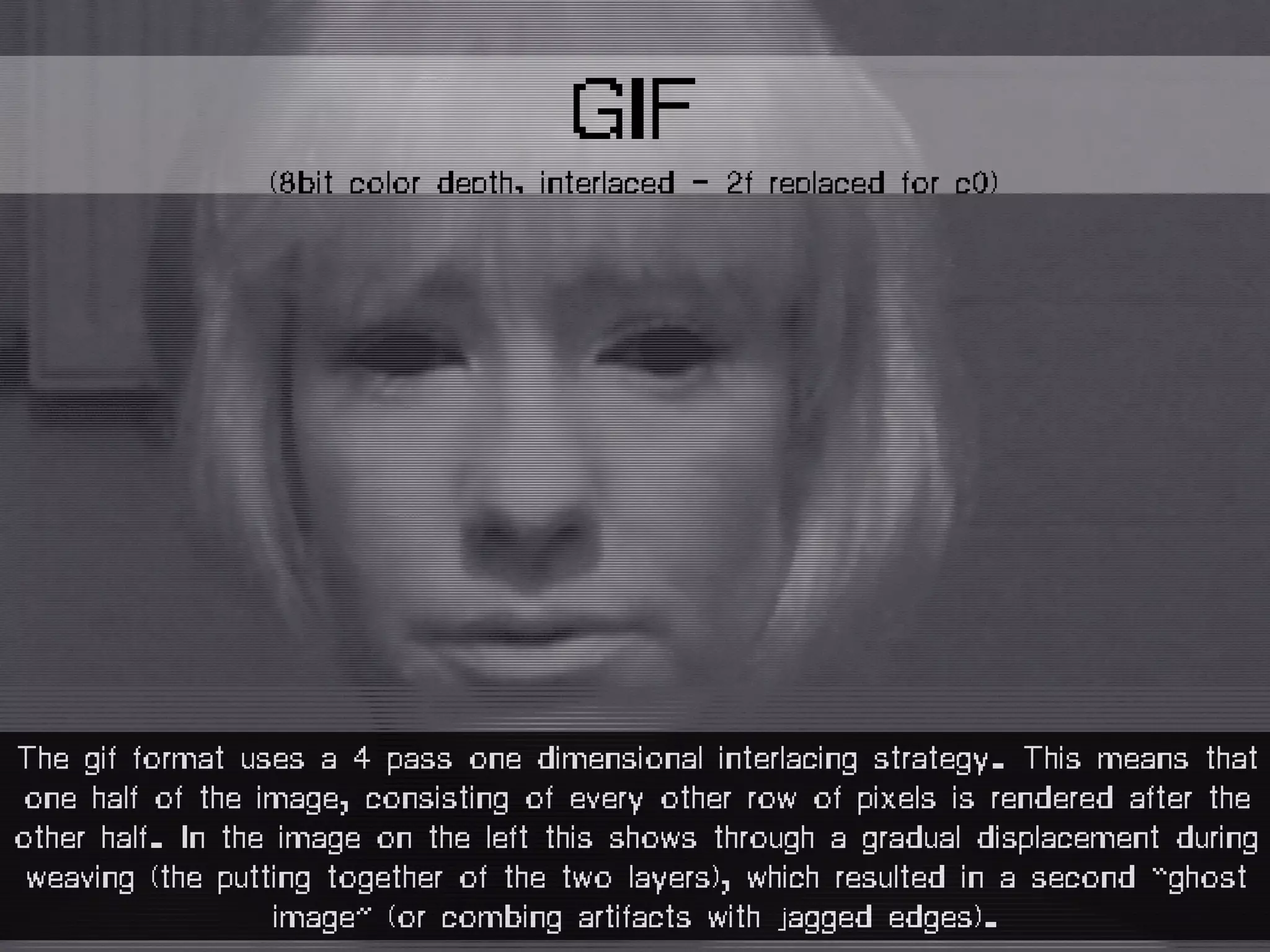
- Components of image files like headers, channels, and interleaved vs non-interleaved formats
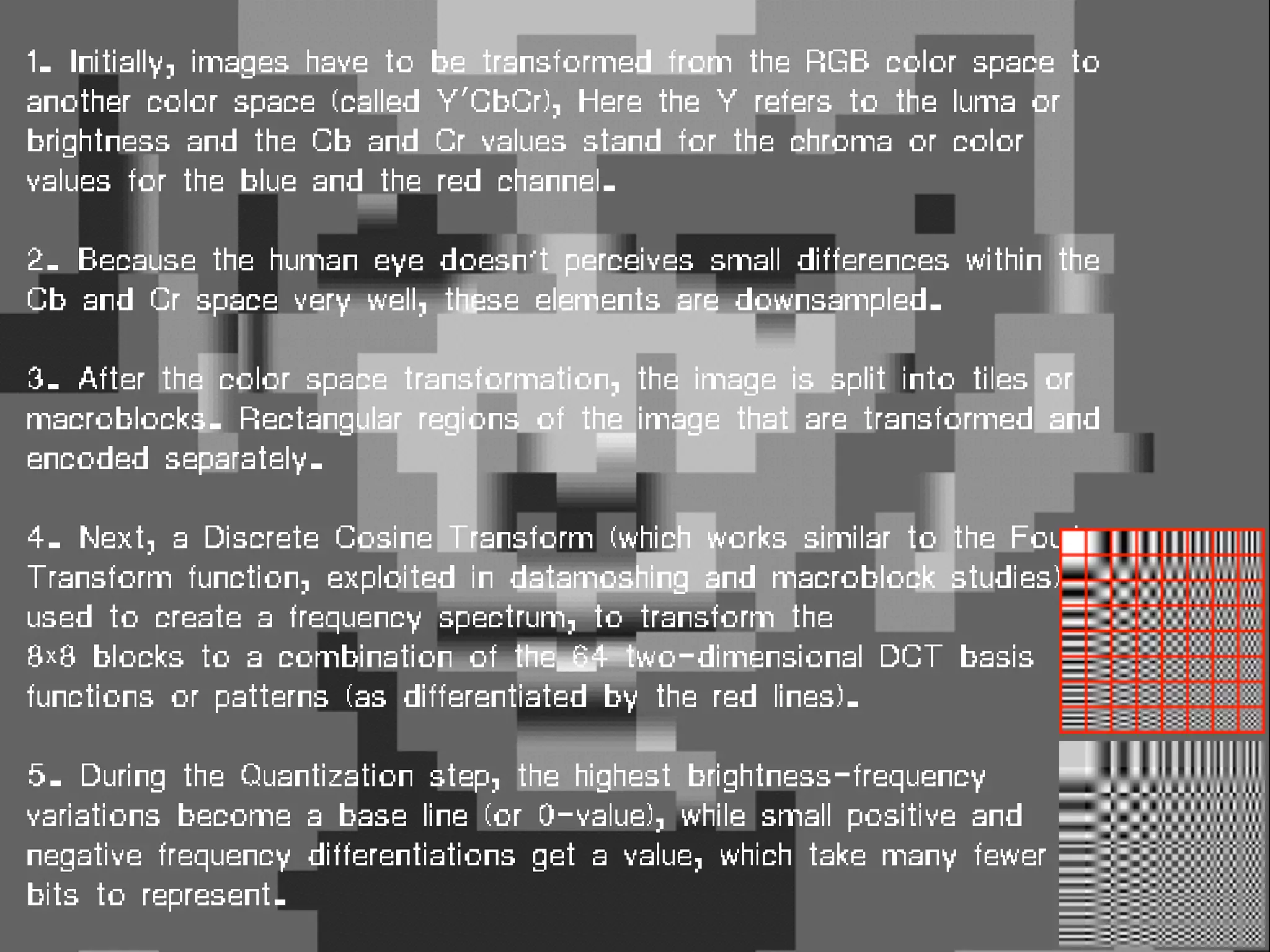
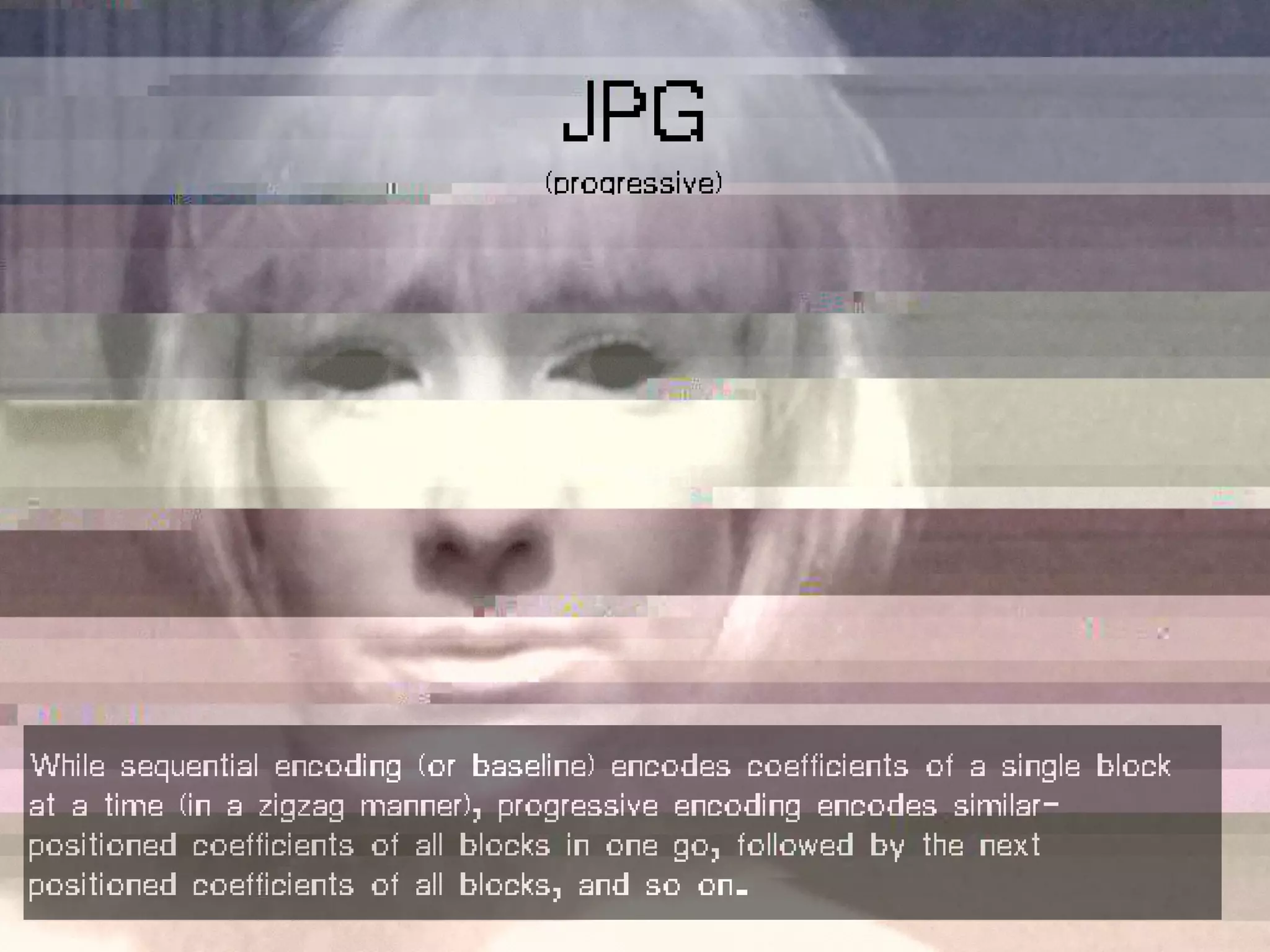
- Explanations of formats like BMP, GIF, PNG, PSD, JPG, TIFF, and others