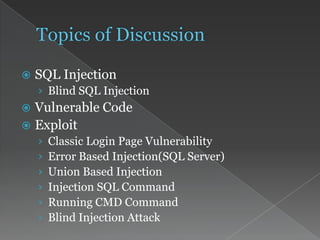
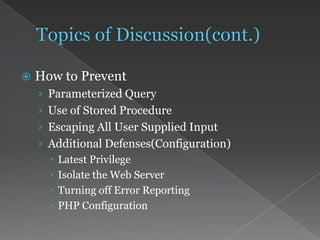
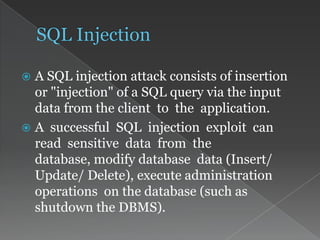
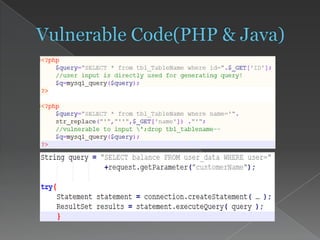
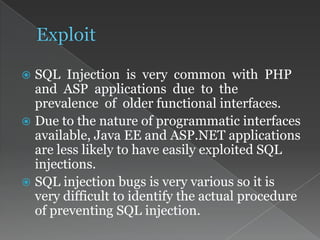
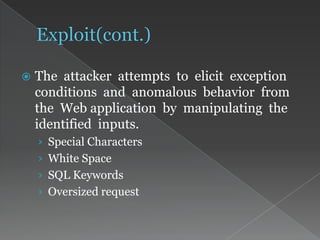
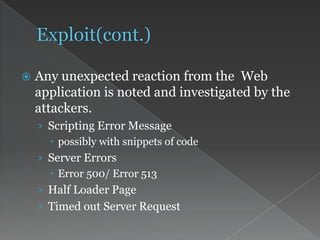
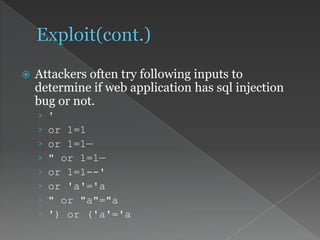
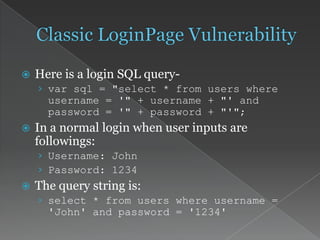
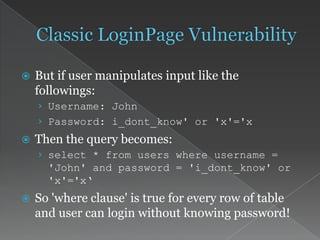
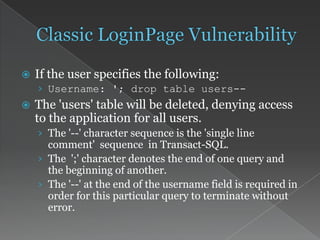
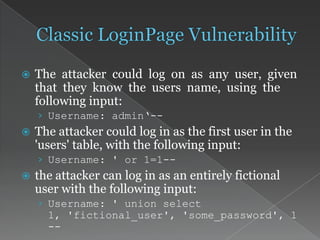
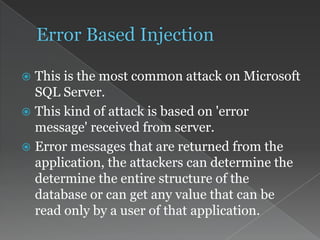
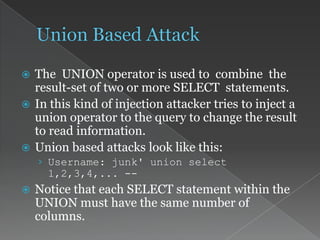
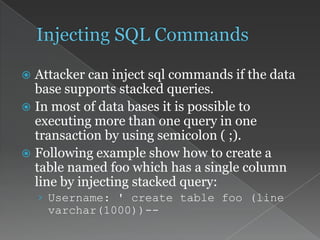
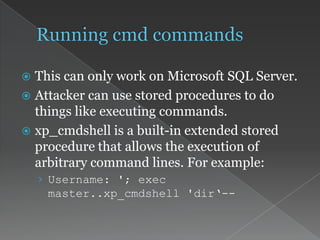
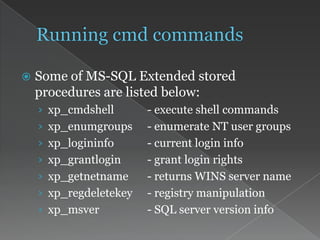
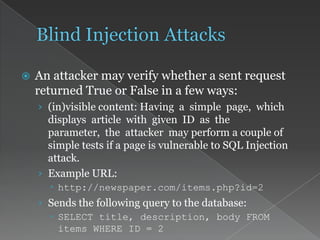
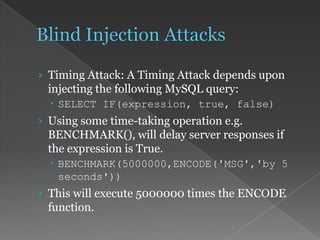
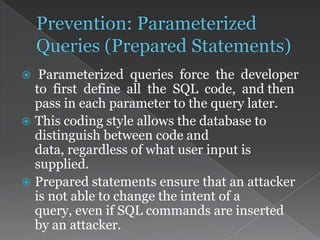
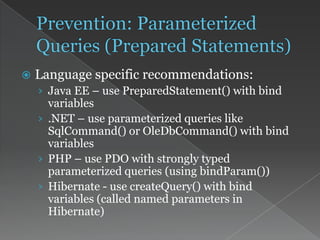
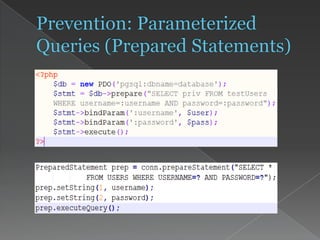
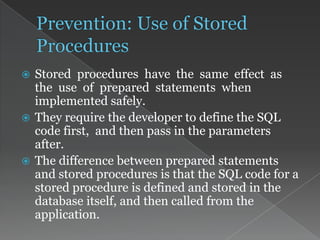
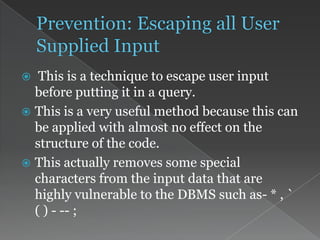
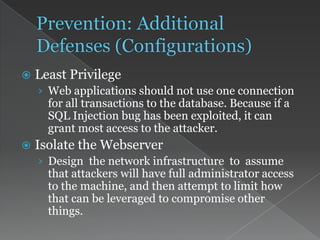
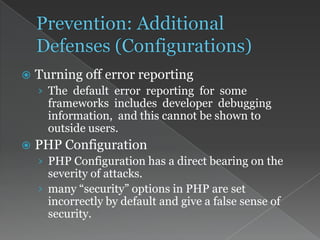
This document discusses SQL injection attacks and how to prevent them. It describes different types of SQL injection like blind SQL injection and union-based injection. It provides examples of vulnerable code and how attackers can exploit it. Finally, it recommends best practices for prevention, including using parameterized queries, stored procedures, input validation, and secure configuration.