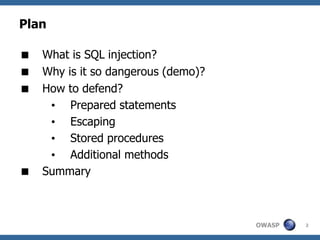
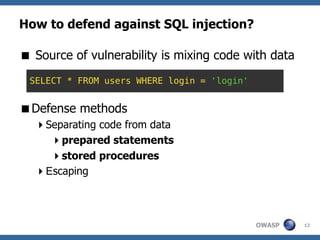
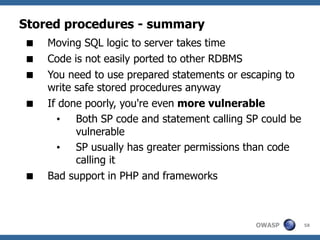
The document is a comprehensive guide on SQL injection, detailing its definition, dangers, examples, and various defense techniques for PHP developers. It emphasizes the importance of using prepared statements, escaping data, and stored procedures to mitigate vulnerabilities in web applications. Additionally, it highlights the need for proper context in defense methods to effectively prevent SQL injection attacks.

![A few facts
Injection vulnerabilities are the 1st on OWASP Top
10 2010 RC
SQLi is responsible for 40–60% cases of data
breach [1] [2]
Modern attack techniques are advanced and
automated
• Vulnerability is not only in WHERE part
• Sometimes it is enough to break a query
Vulnerabilities are found on a daily basis, even in
new applications
OWASP 10](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-10-320.jpg)


![Prepared statements in Doctrine cont.
It can still bite you
$q = Doctrine_Query::create()
->update('Account')
->set('amount', 'amount + 200')
->where("id > {$_GET['id']}");
Correct this to:
->where("id > ?", (int) $_GET['id']);
NEVER put input data directly into SQL
commands
OWASP 19](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-19-320.jpg)
![Prepared statements in Zend Framework
PDO (+ mysqli + oci8 + sqlsrv)
// prepare + execute
$stmt = $db->prepare('INSERT INTO server (key,
value) VALUES (:key,:value)');
$stmt->bindParam('key', $k);
$stmt->bindParam('value', $v);
foreach ($_SERVER as $k => $v)
$stmt->execute();
// prepare + execute in one step
$stmt = $db->query('SELECT * FROM bugs WHERE
reported_by = ? AND bug_status = ?',
array('goofy', 'FIXED'));
while ($row = $stmt->fetch())
echo $row['bug_description'];
OWASP 21](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-21-320.jpg)
![Escaping – how does it work?
Data and commands are still kept in a single variable, but
we try to separate them inline
Numbers
• Cast to (int) / (float) – don't use is_numeric [1]!
Texts are surrounded with single quotes : '
.. WHERE col = 'TEXT DATA' AND ...
• If quote is inside the text, you need a way to distinguish it from
the ending quote
• Prepend a special character e.g. "" to a quote
• Escaping rules depend on context!
OWASP 25](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-25-320.jpg)
![Escaping – context
addslashes()
Returns a string with backslashes before characters that need to be quoted in
database queries etc. These characters are single quote ('), double quote ("),
backslash () and NUL (the NULL byte).
/ Source: php.net manual /
$user = addslashes($_GET['u']);
$pass = addslashes($_GET['p']);
$sql = "SELECT * FROM users WHERE username =
'{$user}' AND password = '{$pass}'";
$ret = exec_sql($sql);
Are you safe?
OWASP 26](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-26-320.jpg)
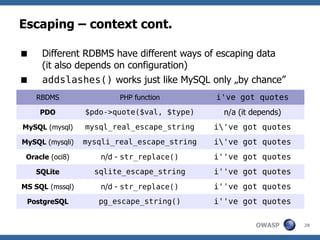
![Escaping – context cont.
// SELECT * FROM users WHERE username =
// '{$user}' AND password = '{$pass}'
$_GET['u'] = "anything'";
$_GET['p'] = " or 1=1 -- ";
// MySQL sees it as :
SELECT * FROM users WHERE username = 'anything''
AND password = ' or 1=1 -- '
// SQLite / MS SQL / Oracle / PostgreSQL:
SELECT * FROM users WHERE username = 'anything''
AND password = ' or 1=1 -- '
Don't use addslashes(), use PHP functions for your
RBDMS
Are you safe now?
OWASP 29](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-29-320.jpg)
![Escaping gotchas – charsets
Errors discovered in 2006 in PostgreSQL and
MySQL [1] [2]
In some multibyte charsets despite escaping you
can cause SQL injection
is „swallowed” by multibyte character
Example:
• BF 27 [ ¬ ' ] BF 5C 27 [ ¬ ' ]
• First 2 bytes are character ¿ in GBK charset
• Server will see ¿'
OWASP 31](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-31-320.jpg)
![Escaping gotchas – charsets
Some Asian charsets are vulnerable
Luckily - not UTF-8!
In PostgreSQL '' escaping was used (instead
of ')
In mysql_real_escape_string()
escaping is done with respect to current
connection charset
• Doesn't always work! [1] [2]
Charset also defines context
OWASP 32](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-32-320.jpg)
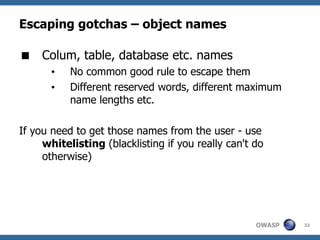
![Escaping gotchas – object names cont.
Example - sorting by column
There's a vuln. in $order, but you can't
escape there
$cat_id = (int) $_GET['cid'];
$order = $_GET['column'];
$stmt = $pdo->prepare("SELECT * FROM products WHERE
cid = :cid ORDER BY $order");
$stmt->bindParam(':cid', $cat_id, PDO::PARAM_INT);
if ($stmt->execute()) {
...
}
OWASP 34](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-34-320.jpg)
![Escaping gotchas – object names cont.
Whitelisting
$columns = array( // list of allowed columns
'product_name','cid','price',
);
if (!in_array($order, $columns, true))
$order = 'product_name'; // default column
Blacklisting
// only a-z and _
$order = preg_replace('/[^a-z_]/', '', $order);
// max 40 characters
$order = substr($order, 0, 40);
OWASP 35](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-35-320.jpg)

![Validation and filtering
Validate all external data
Validate before processing
Filter INPUT - escape OUTPUT
Different validation rules for each parameter -
check e.g.
• Type
• Scalar / array
• Min / max values
• Character data length! [1]
OWASP 61](https://image.slidesharecdn.com/owasp-sql-injection-en-100317143725-phpapp02/85/SQL-Injection-complete-walkthrough-not-only-for-PHP-developers-61-320.jpg)