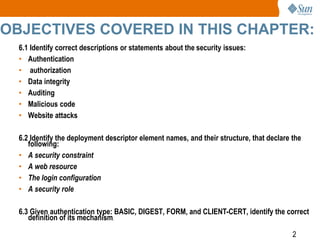
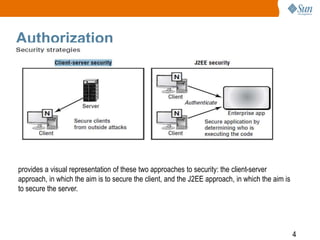
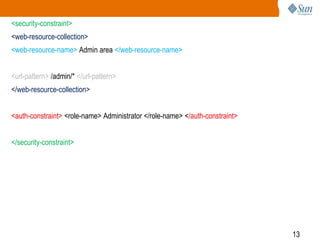
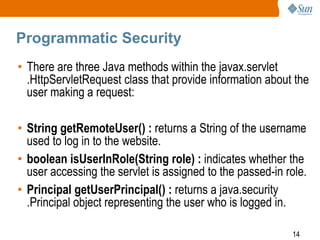
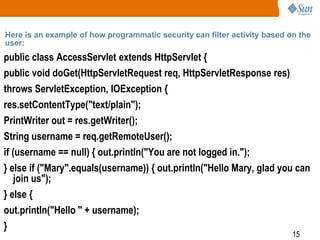
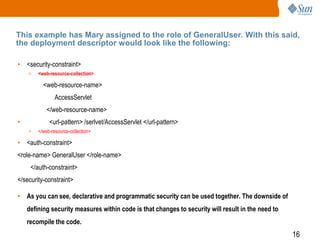
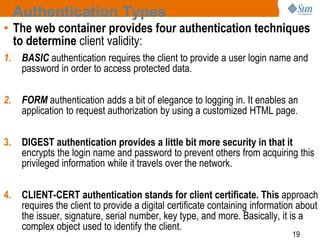
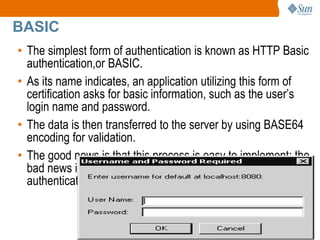
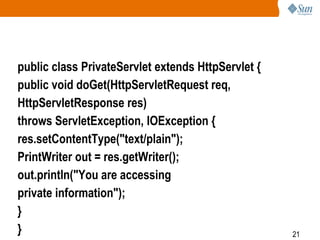
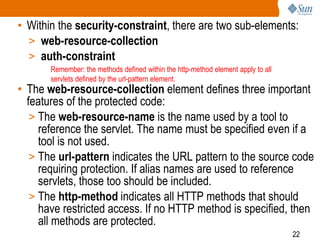
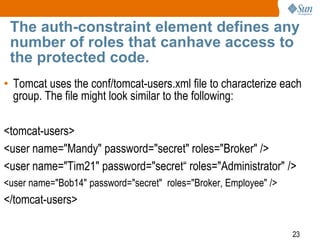
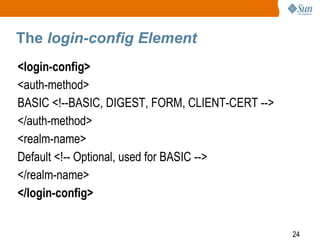
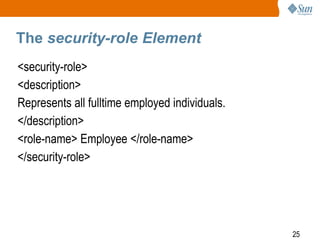
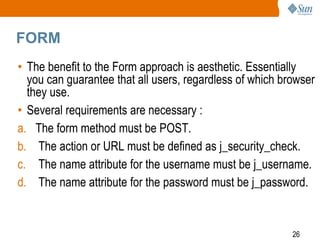
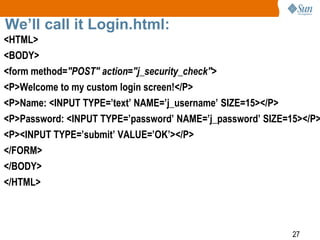
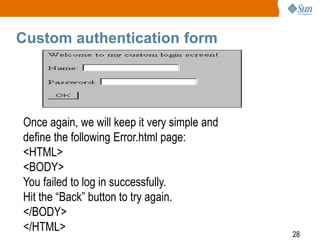
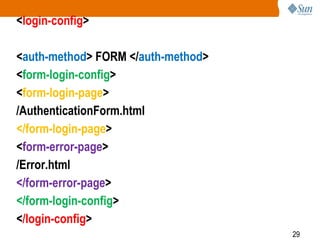
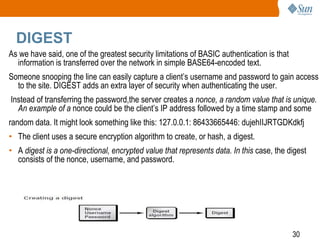
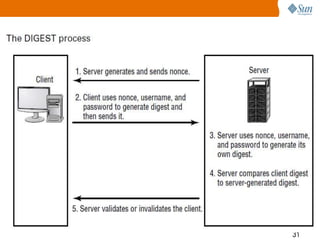
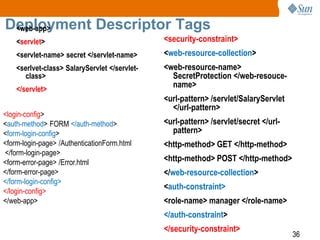
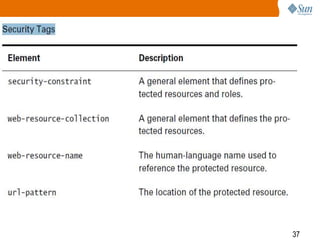
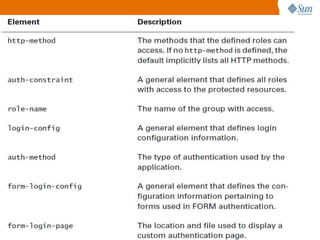
The document outlines key security principles for web applications, addressing authentication, authorization, data integrity, and malicious code protection. It discusses various authentication methods, including basic, digest, form, and client-cert authentication, and emphasizes implementing security through both declarative and programmatic approaches. Additionally, it highlights the importance of auditing user roles and the need for firewalls and antivirus measures against website attacks.