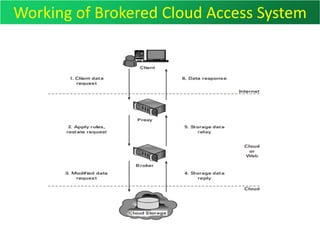
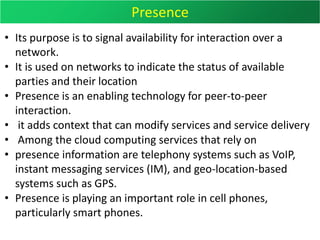
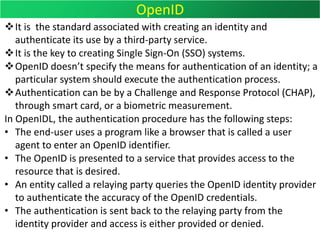
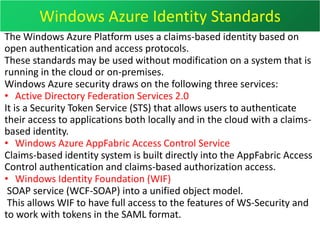
This document discusses various aspects of cloud security including cloud security challenges, areas of concern in cloud computing, how to evaluate risks, cloud computing categories, the cloud security alliance, security service boundaries, responsibilities by service models, securing data, auditing and compliance, identity management protocols, and Windows Azure identity standards. It provides information on policies, controls, and technologies used to secure cloud environments, applications, and data.