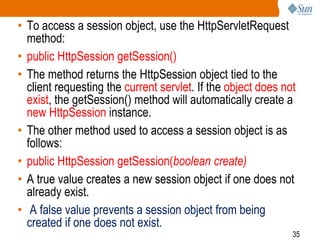
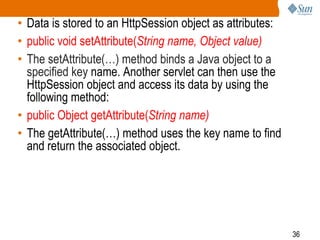
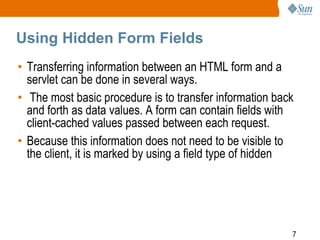
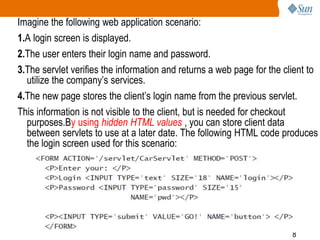
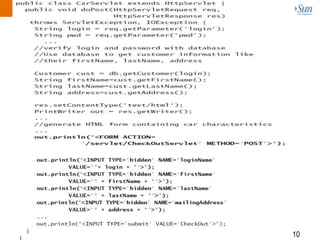
This document covers session management for Java EE web applications, detailing the identification and use of session objects to maintain client data across multiple requests. It discusses various techniques for session tracking, including hidden form fields, URL rewriting, and cookies, while also addressing session lifecycle management, including creation, destruction, and invalidation. Additionally, it explains how to utilize the HttpSession object for easier access to client data and provides methods for session attribute management and listener implementation.

![30
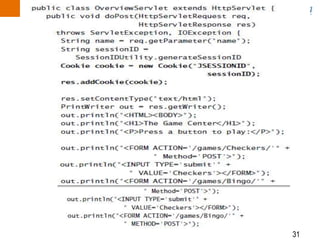
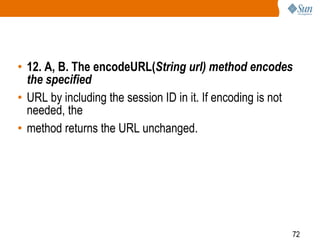
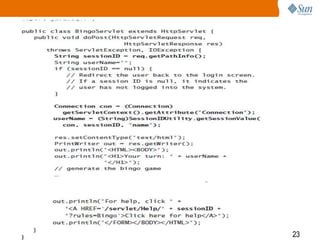
• The servlet specification mandates that the name of the value used to
track the session for a cookie must be called JSESSIONID.
• The ID name must be all uppercase when used within a cookie, but
lowercase when used in URL rewriting.
• A cookie can be added to an HttpServletResponse object in the following
way:
• Cookie cookie = new Cookie(“JSESSIONID”, “567”);
• res.addCookie(cookie);
• If another servlet is interested in accessing this information, it can call the
• getCookies() method of the HttpServletRequest class:
• public Cookie[] getCookies()
• Using our example from the preceding “Rewriting the URL” section, you
• can create a cookie to add the session ID. Listing 6.4 demonstrates how
to use cookies to rewrite the OverviewServlet.](https://image.slidesharecdn.com/sessionmanagement-6-151128152648-lva1-app6891/85/SCWCD-Session-management-CHAP-6-30-320.jpg)