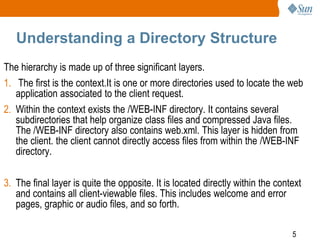
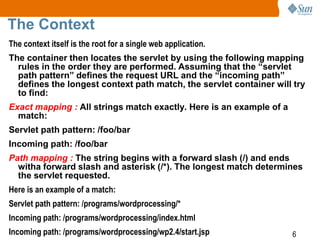
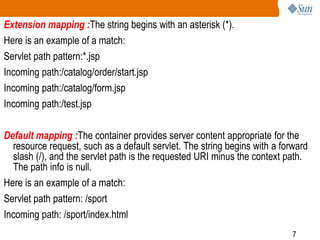
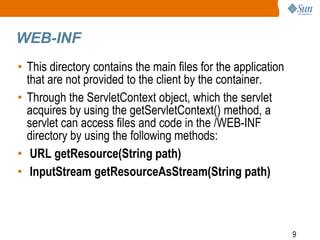
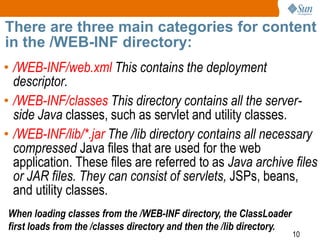
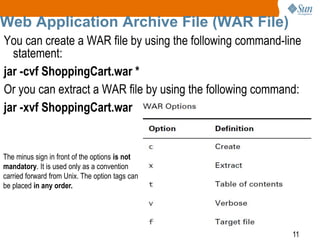
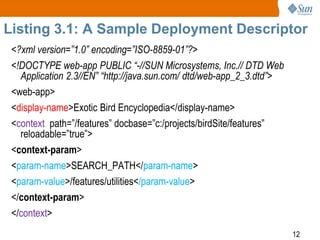
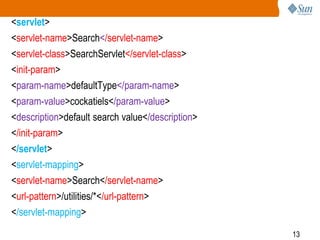
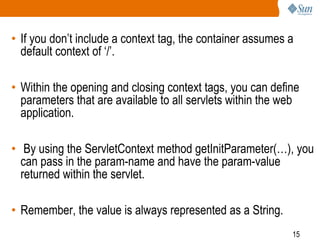
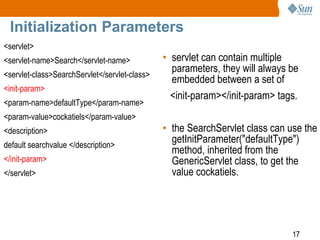
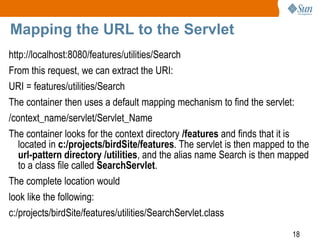
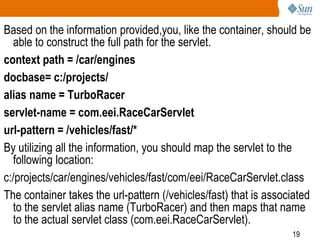
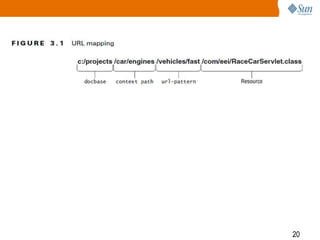
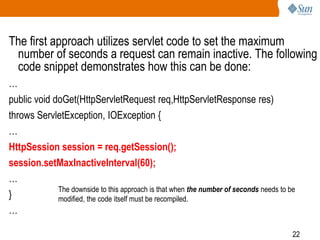
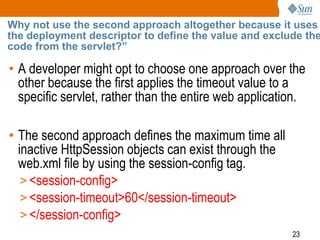
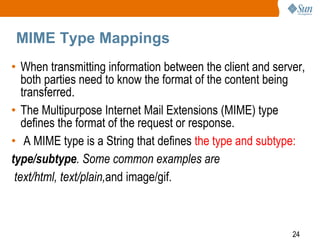
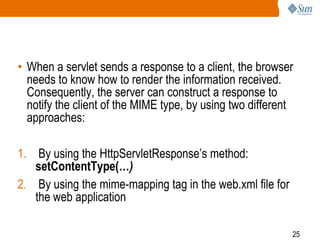
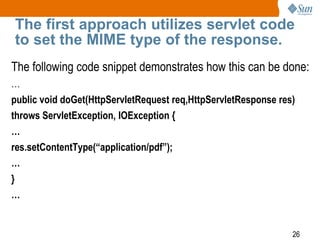
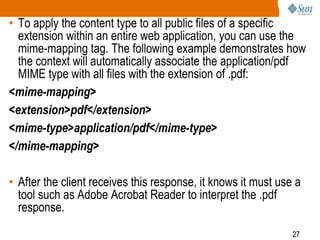
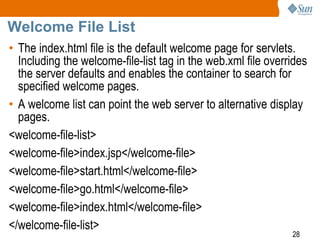
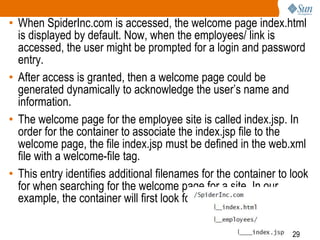
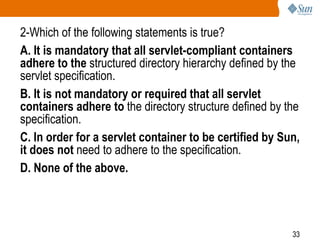
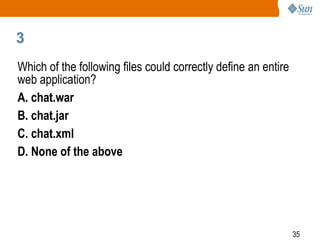
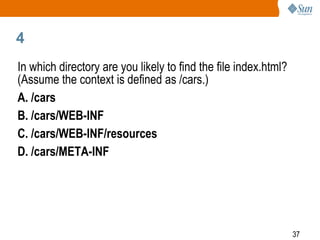
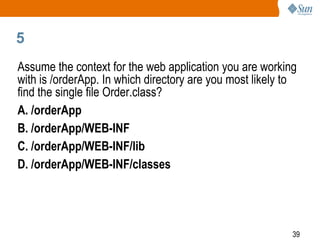
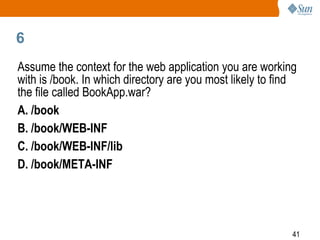
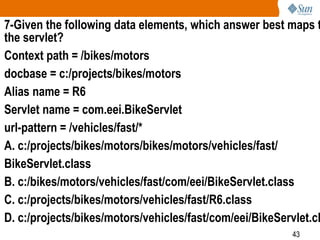
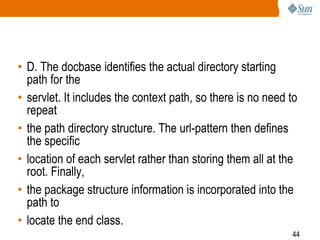
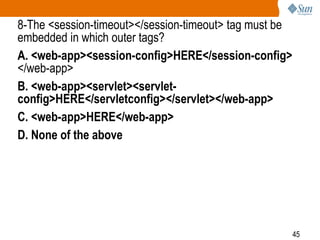
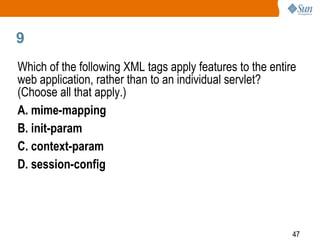
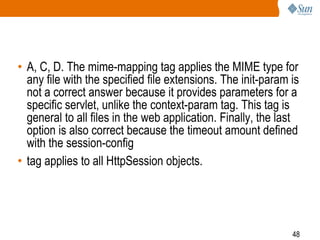
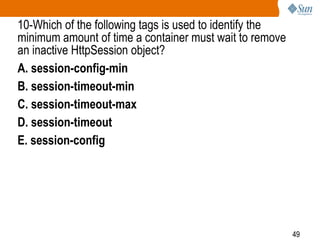
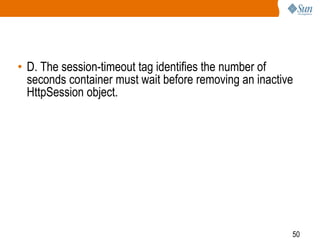
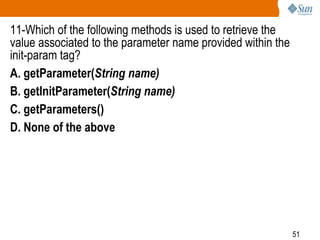
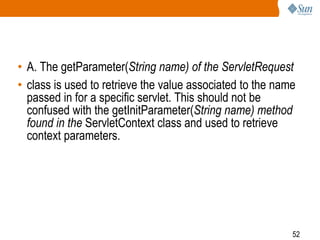
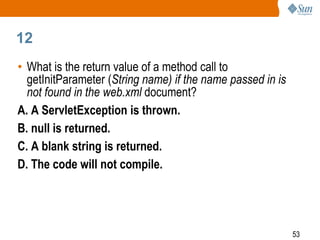
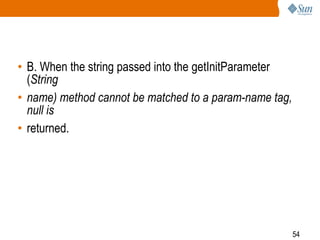
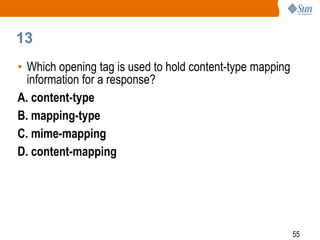
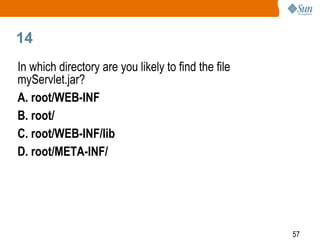
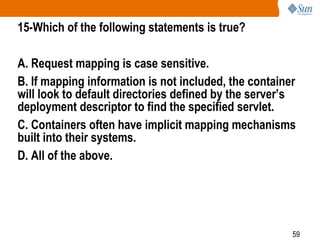
The document provides a comprehensive overview of the structure, components, and configuration of servlet web applications, including the directory layout, deployment descriptors, and request mapping. It covers essential topics such as the /web-inf directory, initialization parameters, session configuration, MIME types, and welcome file lists. The document emphasizes the significance of correctly organizing files and configuration settings to ensure the proper functioning of web applications on the J2EE platform.