Embed presentation
Downloaded 63 times
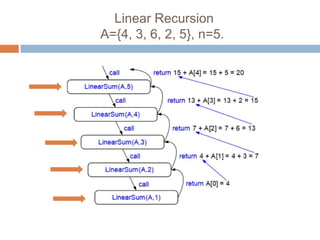
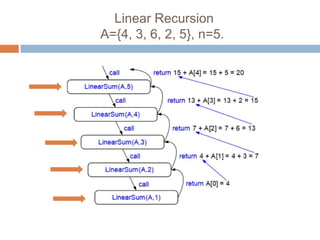
![Linear Recursion
Algorithm LinearSum(A, n)
if n = 1 then
return A[0]
else
return LinearSum(A, n-1) + A[n-1]](https://image.slidesharecdn.com/recursion-170415030718/85/Recursion-Algorithms-and-Data-Structures-7-320.jpg)
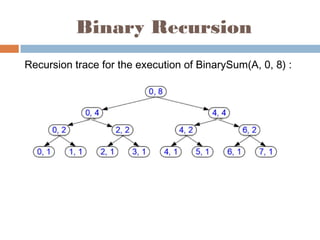
![Binary Recursion
Algorithm BinarySum(A, i, n)
if n = 1 then
return A[i]
else
return BinarySum(A, i, [n/2])+
BinarySum (A, i+[n/2], [n/2])](https://image.slidesharecdn.com/recursion-170415030718/85/Recursion-Algorithms-and-Data-Structures-10-320.jpg)
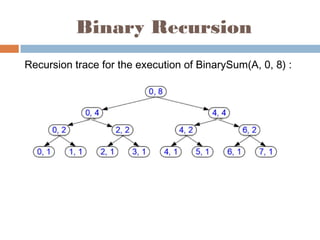
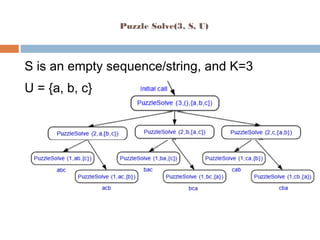
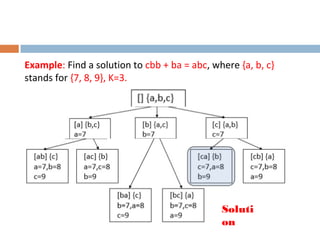
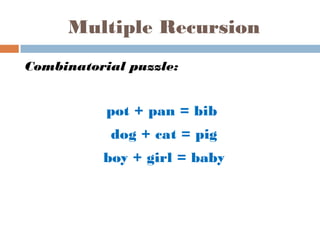
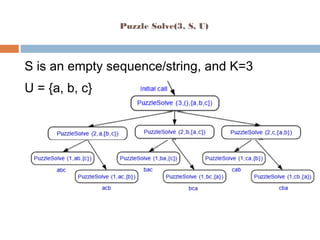
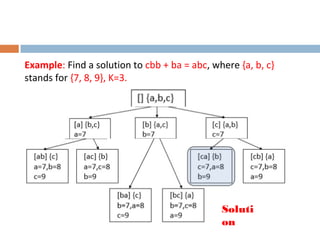
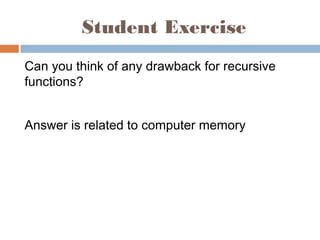
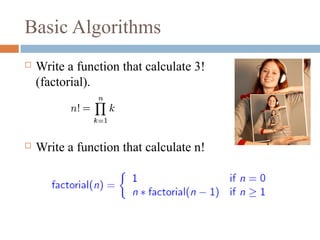
The document discusses basic algorithms, particularly focusing on recursion as a method for solving problems like calculating factorials and summing elements in an array. It describes different types of recursion: linear, binary, and multiple, providing algorithms for each type and examples of their execution. Additionally, it introduces a combinatorial puzzle related to multiple recursion and encourages students to think about the drawbacks of recursive functions.
![Linear Recursion
Algorithm LinearSum(A, n)
if n = 1 then
return A[0]
else
return LinearSum(A, n-1) + A[n-1]](https://image.slidesharecdn.com/recursion-170415030718/85/Recursion-Algorithms-and-Data-Structures-7-320.jpg)
![Binary Recursion
Algorithm BinarySum(A, i, n)
if n = 1 then
return A[i]
else
return BinarySum(A, i, [n/2])+
BinarySum (A, i+[n/2], [n/2])](https://image.slidesharecdn.com/recursion-170415030718/85/Recursion-Algorithms-and-Data-Structures-10-320.jpg)