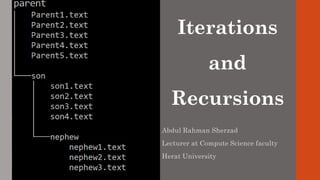
Iterations and Recursions
•
4 likes•1,998 views
The document discusses the differences between recursion and iteration. Recursion involves a method calling itself, with each call reducing the problem size until a base case is reached. Iteration uses loops to repeat a process. Examples include calculating factorials, Fibonacci numbers, and binary search recursively and iteratively. Some problems like directory traversal are simpler using recursion due to its divide-and-conquer approach, while iterations may be preferred for easier explanation or to avoid stack overflows with deep recursions.
Report
Share
Report
Share
Download to read offline
Recommended
sparse matrix in data structure

I have discussed about what is sparse matrix, how to do triplet representation of sparse matrix.
Tree - Data Structure

a. Concept and Definition
b. Binary Tree
c. Introduction and application
d. Operation
e. Types of Binary Tree
• Complete
• Strictly
• Almost Complete
f. Huffman algorithm
g. Binary Search Tree
• Insertion
• Deletion
• Searching
h. Tree Traversal
• Pre-order traversal
• In-order traversal
• Post-order traversal
Slides at myblog
http://www.ashimlamichhane.com.np/2016/07/tree-slide-for-data-structure-and-algorithm/
Assignments at github
https://github.com/ashim888/dataStructureAndAlgorithm/tree/dev/Assignments/assignment_7
Infix to Postfix Conversion Using Stack

Infix to Postfix Conversion Using Stack is one of the most significant example of application of Stack which is an ADT (Abstract Data Type) based on LIFO concept.
Recommended
sparse matrix in data structure

I have discussed about what is sparse matrix, how to do triplet representation of sparse matrix.
Tree - Data Structure

a. Concept and Definition
b. Binary Tree
c. Introduction and application
d. Operation
e. Types of Binary Tree
• Complete
• Strictly
• Almost Complete
f. Huffman algorithm
g. Binary Search Tree
• Insertion
• Deletion
• Searching
h. Tree Traversal
• Pre-order traversal
• In-order traversal
• Post-order traversal
Slides at myblog
http://www.ashimlamichhane.com.np/2016/07/tree-slide-for-data-structure-and-algorithm/
Assignments at github
https://github.com/ashim888/dataStructureAndAlgorithm/tree/dev/Assignments/assignment_7
Infix to Postfix Conversion Using Stack

Infix to Postfix Conversion Using Stack is one of the most significant example of application of Stack which is an ADT (Abstract Data Type) based on LIFO concept.
Regular expressions-Theory of computation

Theory of computation regular expressions
re to dfa
dfa to re
regular expressions to nfa
Pointers in c++

This PPT is based on Pointers in C++. It is entirely based on class XII CBSE syllabus.
Binary Search Tree in Data Structure

Content of slide
Tree
Binary tree Implementation
Binary Search Tree
BST Operations
Traversal
Insertion
Deletion
Types of BST
Complexity in BST
Applications of BST
Hashing

hashing is encryption process mostly used in programming language for security purpose.
This presentation will you understand all about hashing and also different techniques used in it for encryption process
linear search and binary search

linear search and binary search, Class lecture of Data Structure and Algorithms and Python.
Stack, Queue, Tree, Python, Python Code, Computer Science, Data, Data Analysis, Machine Learning, Artificial Intellegence, Deep Learning, Programming, Information Technology, Psuedocide, Tree, pseudocode, Binary Tree, Binary Search Tree, implementation, Binary search, linear search, Binary search operation, real-life example of binary search, linear search operation, real-life example of linear search, example bubble sort, sorting, insertion sort example, stack implementation, queue implementation, binary tree implementation, priority queue, binary heap, binary heap implementation, object-oriented programming, def, in BST, Binary search tree, Red-Black tree, Splay Tree, Problem-solving using Binary tree, problem-solving using BST, inorder, preorder, postorder
Binary Tree in Data Structure

This is an PPT of Data Structure. It include the following topic "Binary Tree in Data Structure".
More Related Content
What's hot
Regular expressions-Theory of computation

Theory of computation regular expressions
re to dfa
dfa to re
regular expressions to nfa
Pointers in c++

This PPT is based on Pointers in C++. It is entirely based on class XII CBSE syllabus.
Binary Search Tree in Data Structure

Content of slide
Tree
Binary tree Implementation
Binary Search Tree
BST Operations
Traversal
Insertion
Deletion
Types of BST
Complexity in BST
Applications of BST
Hashing

hashing is encryption process mostly used in programming language for security purpose.
This presentation will you understand all about hashing and also different techniques used in it for encryption process
linear search and binary search

linear search and binary search, Class lecture of Data Structure and Algorithms and Python.
Stack, Queue, Tree, Python, Python Code, Computer Science, Data, Data Analysis, Machine Learning, Artificial Intellegence, Deep Learning, Programming, Information Technology, Psuedocide, Tree, pseudocode, Binary Tree, Binary Search Tree, implementation, Binary search, linear search, Binary search operation, real-life example of binary search, linear search operation, real-life example of linear search, example bubble sort, sorting, insertion sort example, stack implementation, queue implementation, binary tree implementation, priority queue, binary heap, binary heap implementation, object-oriented programming, def, in BST, Binary search tree, Red-Black tree, Splay Tree, Problem-solving using Binary tree, problem-solving using BST, inorder, preorder, postorder
Binary Tree in Data Structure

This is an PPT of Data Structure. It include the following topic "Binary Tree in Data Structure".
What's hot (20)
Similar to Iterations and Recursions
Module 01 Stack and Recursion

The presentation given at PCCOE, Nigdi, Pune by Prof. Tushar B Kute in workshop on "See through C".
http://tusharkute.com
01 Notes Introduction Analysis of Algorithms Notes

Here is the first set of notes for the first class in Analysis of Algorithm. I added a dedicatory for my dear Fabi... she has showed me what real idealism is....
Recursion, debugging in c

first part of the lecture explains Recursion topic in c language.
Second half shows, what is a debugging, how to debug your program, debugging methods and debugging tool in Eclipse.
1_Introduction.pdf1 Dynamics and Control Topic .docx

1_Introduction.pdf
1
Dynamics and Control
Topic 1: Introduction
2
Tentative Lecture Schedule
3
What is Control?
Think of some “control” examples:
• From your study
• From industry
• From real-life
Commonly used terms in “control”?
4
Open Loop Control vs. Closed Loop Control?
Open Loop Control:
• There is no feedback
• Calibration is the key!
• Can be sensitive to disturbances
5
Open Loop Control:
• Objective: make bread toasted
• Control action: set timer
• Control result (performance)?
• How to improve the performance?
• Use temp sensor
• Use microprocessor and actuator to control the spring
• Worth it?
Feedback
Closed Loop Control:
• There is a feedback (sensor)
• Compare actual behavior with desired behavior
• Make corrections based on the error
• The sensor is the key element of a feedback control
• Design a proper control algorithm is the focus of this
subject!
Room Temp Control: Open or Closed?
• Feedback?
• Control objective?
• Controller?
• System/plant?
• Disturbance?
Applications of Feedback Control
• Manufacturing
Applications of Feedback Control
• Robotics
UNDERWATER ROBOT
Applications of Feedback Control
• Aerospace and Astronautics
Applications of Feedback Control: BIG DOG in Action
BOSTON DYNAMICS
Sensing Actuation Control Plant ControlSystem = + + +
BIG DOG CONTROL: Block Diagram
DISTURBANCE
Environment
Foot
Trajectory
Planning
Desired
Walking
Speed
REFERENCE
Joint angles
& velocities
Robot
Joint
torques
Robot Robot
Virtual
Leg IK
Virtual
Leg FK
Virtual
Leg VM
PD
Servo
Virtual
Leg Coords
Virtual
Leg Forces
State
Machine
Leg State
Gait
Coordination
Mechanisms
Influences to/from other legs
+
IK=inverse kinematics
FK=forward kinematics
VM=virtual model
Exercise:
• Use Block Diagram to represent this driving system
• Indicate: sensor, actuator, control, plant, reference &
disturbance
Brain Hand Foot
Eye
Car _
Desired
Direction
Desired
Speed
Direction
Speed
Controller Actuators Plant
Error Disturbances
Sensor
Control Actuation
Sensor
Plant
_
Reference Response
Error
General Block Diagram Representation
Feedback Control Concept
Not limited to engineering systems only!
Human Grasping Motion
Feedback Control Concept…cont’d
Not limited to engineering systems only!
e.g. Taking Dynamics & Control…
Two Main Criteria of Good Feedback Control
• Acceptable Dynamic Responses
• Stability
Crash of SAAB JAS-39 due to instability
Systematic Control Design Process
Goa.
Recursion and Sorting Algorithms

These slides are part of a full series of slides which covers almost all the basic concepts of data structures and algorithms.
Part 3
C++ Programming Basics.pptx

basics to c++ learning
Operators and Statements
Assignation (=).
Arithmetic operators
Precedence Rules of Arithmetic Operators
Compound assignation operators
Increment and decrement Operators
Relational operators
Logic operators
Type Conversion
Converting Algebraic Expressions to C++
Library Function
#include <iostream.h>
int main()
{
int first, second, sum;
cout << "Abebe: Hey Bekele, I just learned how to add”
<< “ two numbers together."<< endl;
cout << "Bekele: Cool!" <<endl;
cout << "Abebe: Give me the first number."<< endl;
cout << "Bekele: ";
cin >> first;
cout << "Abebe: Give me the second number."<< endl;
cout << "Bekele: ";
cin >> second;
sum = first + second;
cout << "Abebe: OK, here is the answer:";
cout << sum << endl;
cout << "Bekele: Wow! You are amazing!" << endl;
return 0;
Similar to Iterations and Recursions (20)
Functional Programming in Javascript - IL Tech Talks week

Functional Programming in Javascript - IL Tech Talks week
01 Notes Introduction Analysis of Algorithms Notes

01 Notes Introduction Analysis of Algorithms Notes
1_Introduction.pdf1 Dynamics and Control Topic .docx

1_Introduction.pdf1 Dynamics and Control Topic .docx
More from Abdul Rahman Sherzad
Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan

A car without fuel cannot be driven; a mobile, a laptop or a PC without power cannot be used; a website without feeding won't have any visitors; likewise, an organization without data will not stand and cannot be survived.
The data quickly becoming one of the most important resources for any country, company, or organizations. It is the data that enables organizations to explain the past and guess the future through data science and business intelligence tools.
This presentation demonstrates how the Kankor data can be used as a resource in the context of Afghanistan, particularly, the candidates’ names that organizations in Afghanistan do not use for anything.
Read the following paper for more information and examples:
https://www.researchgate.net/publication/322695084_Data_is_the_Fuel_of_Organizations_Opportunities_and_Challenges_in_Afghanistan
PHP Unicode Input Validation Snippets

These useful functions/snippets enable you to validate Unicode characters such as Digits, Person names, and Text mainly used in Afghanistan and Iran.
Feature list:
* Validate Person names commonly used in Afghanistan and Iran. Person names may be in Persian/Dari, Arabic, and English and similar languages;
* Validate only Persian Text;
* Validate only Pashtu Text;
* Validate digit in Persian/Dari, Pashtu and Arabic format;
* Validate digit in all common formats.
Sorting Alpha Numeric Data in MySQL

In SQL, the ORDER BY keyword is used to sort the result-set in ascending (ASC) or descending (DESC) order by some specified column/columns.
It works great for most of the cases. However, for alphanumeric data, it may not return the result-set that you will be expecting.
This presentation explains how this can be addressed using different techniques.
PHP Variable variables Examples

In PHP, variable variables take the value of one variable, and treat that as the name of another variable.
Variable variables are just variables whose names can be programmatically set and accessed. Hence, they are also called dynamic variable names.
Cross Join Example and Applications

Cross joins are used to return every combination of rows from two and more than two tables. Cross Joins are sometimes called a Cartesian product. This presentation illustrates cross join examples and applications in real life.
Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...

Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...Abdul Rahman Sherzad
The increase in enrollment in education and higher education institutions, the increase in the use of the Internet as well as the emergence of technology in educational systems have led to the aggregation of large amounts of student data at educational institutions (schools, colleges, and universities), which makes it vital to use data mining methods to improve the educational settings.
Although educational institutions collect an enormous amount of student data, this data is utilized to produce basic insights and is not used for decisions to improve the educational settings.
To get essential benefits from the data, powerful techniques are required to extract the useful knowledge which is valuable and significant for the decision and policy makers.Web Application Security and Awareness

Secure web programming plus end users' awareness are the last line of defense against attacks targeted at the corporate systems, particularly web applications, in the era of world-wide web.
Most web application attacks occur through Cross Site Scripting (XSS), and SQL Injection. On the other hand, most web application vulnerabilities arise from weak coding with failure to properly validate users' input, and failure to properly sanitize output while displaying the data to the visitors.
The literature also confirms the following web application weaknesses in 2010: 26% improper output handling, 22% improper input handling, and 15% insufficient authentication, and others.
Abdul Rahman Sherzad, lecturer at Computer Science Faculty of Herat University, and Ph.D. student at Technical University of Berlin gave a presentation at 12th IT conference on Higher Education for Afghanistan in MoHE, and then conducted a seminar at Hariwa Institute of Higher Education in Herat, Afghanistan introducing web application security threats by demonstrating the security problems that exist in corporate systems with a strong emphasis on secure development. Major security vulnerabilities, secure design and coding best practices when designing and developing web-based applications were covered.
The main objective of the presentation was raising awareness about the problems that might occur in web-application systems, as well as secure coding practices and principles. The presentation's aims were to build security awareness for web applications, to discuss the threat landscape and the controls users should use during the software development lifecycle, to introduce attack methods, to discuss approaches for discovering security vulnerabilities, and finally to discuss the basics of secure web development techniques and principles.
Database Automation with MySQL Triggers and Event Schedulers

This advanced training seminar on "Database Automation using MySQL Triggers and Event Schedulers" is dedicated to the Computer Science graduates and students of both public and private universities.
In this seminar we are going to look in depth at MySQL Triggers and Event Schedulers– powerful features supported by most popular commercial and open source relational database systems.
The Triggers are powerful tools for protecting the integrity of the data in the databases, logging and auditing of the changes on data, business logic, perform calculations, run further SQL commands, etc.
The Events are very useful to automate some database operations such as optimizing database tables, cleaning up logs, archiving data, or generate complex reports during off-peak time, etc.
The participants will learn about the true concept, implementation and application of MySQL Triggers and Event Schedulers with real life examples and scenarios.
They will also learn how to use the database triggers and event schedulers in many real cases to automate database tasks - such as optimizing database tables, cleaning up logs, archiving data, or generate complex reports during off-peak time.
This seminar is presented by Abdul Rahman Sherzad lecturer at Computer Science faculty of Herat University, and PhD Student at Technical University of Berlin, Germany at Hariwa Institute of Higher Education, Herat, Afghanistan.
Mobile Score Notification System

Education is one of the main pillars and key concerns for each society in general. In developing countries, in particular in Afghanistan, we observe a remarkable increase in enrollment in education and higher education institutions, but most of the students don't have proper access to their scores. For instance, while Kankor result is announced the vast amounts of traffic the visitors generate make the website completely down and inaccessible. Another example, There is no efficient method to access the university scores in particular for students from other provinces. Last but not least, Diploma and certification verification is a lengthy and complicated process, when graduated students apply for jobs and scholarships inside or outside of Afghanistan they are asked to provide their certificate and diploma. One of the solutions can be verification of the graduation documents through SMS.
In Herat Innovation Lab 2015, Education group members under the mentorship of Abdul Rahman Sherzad chose this social and educational domain problem and within three days they designed and developed a prototype solution that enable students to access i.e. Kankor Scores Result, University Scores Result, Faculties Announcements and Events, and Certificate/Diploma Verification via SMS, Mobile and Web Applications effectively and efficiently.
Herat Innovation Lab 2015

Innovation Labs (iLabs) is a social innovation program covering a series of conferences. One the one hand, the goal is to bring social and technology experts together for the networking purpose. On the other hand, the motivation is to harness technology to solve the most challenging social and environmental problems and to build tech-based systems.
Evaluation of Existing Web Structure of Afghan Universities

This presentation looks into the existing web structure and services of all Afghan universities, not only to evaluate the entire infrastructure but also to systematically analyze the gaps and design challenges of web platforms and services as a means of communication and collaboration among various stakeholders including the Ministry of Higher Education, its subsidiaries, students and other related audience.
The presentation finds that the environment for necessary ICT infrastructure and services is up to the expected required standard to provide access to various online resources and systems. The next important finding is the increasing demand by students to access information online rather than the existing traditional paper-based systems. Another very important finding is related to the non-existence of a formal managerial oversight to all the online resources and thus has resulted to a very poor quality of content, outdated information and the services that don't meet the expected needs and challenges.
PHP Basic and Fundamental Questions and Answers with Detail Explanation

These PHP basic and fundamental questions and answers with detail explanation help students and learners to think comprehensive, and to seek more to understand the concept and the root of each topic concretely.
Java Applet and Graphics

This presentation introduces Java Applet and Java Graphics in detail with examples and finally using the concept of both applet and graphics code the analog clock project to depict how to use them in real life challenges and applications.
Fundamentals of Database Systems Questions and Answers

Fundamentals of Database Systems questions and answers with explanation for fresher's and experienced for interview, competitive examination and entrance test.
Everything about Database JOINS and Relationships

Today, we continue our journey into the world of RDBMS (relational database management systems) and SQL (Structured Query Language).
In this presentation, you will understand about some key definitions and then you will learn how to work with multiple tables that have relationships with each other.
First, we will go covering some core concepts and key definitions, and then will begin working with JOINs queries in SQL.
Create Splash Screen with Java Step by Step

This presentation guide you how to make a custom Splash Screen step by step using Java Programming. In addition, you will learn the concept and usage of Java Timer, Java Progress Bar and Window ...
Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java

This presentation explains step by step how to develop and code Fal-e Hafez (Omens of Hafez) Cards in Persian Using JAVA. There are several applications which are coded by different programming languages i.e. Java languages for Desktops and Mobiles, HTML and CSS and PHP for Web Pages, etc. and this shows the importance of Omens of Hafez among the Persian people.
Web Design and Development Life Cycle and Technologies

This presentation is an introduction to the design, creation, and maintenance of web design and development life cycle and web technologies. With it, you will learn about the web technologies, the life cycle of developing an efficient website and web application and finally some web essentials questions will be provided and reviewed.
Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes

A Virtual Keyboard is considered to be a component to use on computers without a real keyboard e.g. Touch Screen Computers and Smart Phones; where a mouse can utilize the keyboard functionalities and features.
In addition, Virtual Keyboard used for the following subjects: Foreign Character Sets, Touchscreen, Bypass Key Loggers, etc.
Java Unicode with Live GUI Examples

With Unicode you can program and accomplish many funny, cool and useful programs and tools as for instance, Abjad Calculator, Bubble Text Generator to write letters in circle, Flip Text Generator to write letters upside down, Google Transliteration to convert English names to Persian/Arabic, etc...
More from Abdul Rahman Sherzad (20)
Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan

Data is the Fuel of Organizations: Opportunities and Challenges in Afghanistan
Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...

Applicability of Educational Data Mining in Afghanistan: Opportunities and Ch...
Database Automation with MySQL Triggers and Event Schedulers

Database Automation with MySQL Triggers and Event Schedulers
Evaluation of Existing Web Structure of Afghan Universities

Evaluation of Existing Web Structure of Afghan Universities
PHP Basic and Fundamental Questions and Answers with Detail Explanation

PHP Basic and Fundamental Questions and Answers with Detail Explanation
Fundamentals of Database Systems Questions and Answers

Fundamentals of Database Systems Questions and Answers
Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java

Fal-e-Hafez (Omens of Hafez) Cards in Persian using Java
Web Design and Development Life Cycle and Technologies

Web Design and Development Life Cycle and Technologies
Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes

Java Virtual Keyboard Using Robot, Toolkit and JToggleButton Classes
Recently uploaded
Quarkus Hidden and Forbidden Extensions

Quarkus has a vast extension ecosystem and is known for its subsonic and subatomic feature set. Some of these features are not as well known, and some extensions are less talked about, but that does not make them less interesting - quite the opposite.
Come join this talk to see some tips and tricks for using Quarkus and some of the lesser known features, extensions and development techniques.
Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL

In software engineering, the right architecture is essential for robust, scalable platforms. Wix has undergone a pivotal shift from event sourcing to a CRUD-based model for its microservices. This talk will chart the course of this pivotal journey.
Event sourcing, which records state changes as immutable events, provided robust auditing and "time travel" debugging for Wix Stores' microservices. Despite its benefits, the complexity it introduced in state management slowed development. Wix responded by adopting a simpler, unified CRUD model. This talk will explore the challenges of event sourcing and the advantages of Wix's new "CRUD on steroids" approach, which streamlines API integration and domain event management while preserving data integrity and system resilience.
Participants will gain valuable insights into Wix's strategies for ensuring atomicity in database updates and event production, as well as caching, materialization, and performance optimization techniques within a distributed system.
Join us to discover how Wix has mastered the art of balancing simplicity and extensibility, and learn how the re-adoption of the modest CRUD has turbocharged their development velocity, resilience, and scalability in a high-growth environment.
OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam

In this slide, we show the simulation example and the way to compile this solver.
In this solver, the Helmholtz equation can be solved by helmholtzFoam. Also, the Helmholtz equation with uniformly dispersed bubbles can be simulated by helmholtzBubbleFoam.
How Recreation Management Software Can Streamline Your Operations.pptx

Recreation management software streamlines operations by automating key tasks such as scheduling, registration, and payment processing, reducing manual workload and errors. It provides centralized management of facilities, classes, and events, ensuring efficient resource allocation and facility usage. The software offers user-friendly online portals for easy access to bookings and program information, enhancing customer experience. Real-time reporting and data analytics deliver insights into attendance and preferences, aiding in strategic decision-making. Additionally, effective communication tools keep participants and staff informed with timely updates. Overall, recreation management software enhances efficiency, improves service delivery, and boosts customer satisfaction.
Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf

Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos
https://www.amb-review.com/tubetrivia-ai
Exclusive Features:
AI-Powered Questions,
Wide Range of Categories,
Adaptive Difficulty,
User-Friendly Interface,
Multiplayer Mode,
Regular Updates.
#TubeTriviaAI
#QuizVideoMagic
#ViralQuizVideos
#AIQuizGenerator
#EngageExciteExplode
#MarketingRevolution
#BoostYourTraffic
#SocialMediaSuccess
#AIContentCreation
#UnlimitedTraffic
Strategies for Successful Data Migration Tools.pptx

Data migration is a complex but essential task for organizations aiming to modernize their IT infrastructure and leverage new technologies. By understanding common challenges and implementing these strategies, businesses can achieve a successful migration with minimal disruption. Data Migration Tool like Ask On Data play a pivotal role in this journey, offering features that streamline the process, ensure data integrity, and maintain security. With the right approach and tools, organizations can turn the challenge of data migration into an opportunity for growth and innovation.
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I didn't get rich from it but it did have 63K downloads (powered possible tens of thousands of websites).
Cracking the code review at SpringIO 2024

Code reviews are vital for ensuring good code quality. They serve as one of our last lines of defense against bugs and subpar code reaching production.
Yet, they often turn into annoying tasks riddled with frustration, hostility, unclear feedback and lack of standards. How can we improve this crucial process?
In this session we will cover:
- The Art of Effective Code Reviews
- Streamlining the Review Process
- Elevating Reviews with Automated Tools
By the end of this presentation, you'll have the knowledge on how to organize and improve your code review proces
How Does XfilesPro Ensure Security While Sharing Documents in Salesforce?

Worried about document security while sharing them in Salesforce? Fret no more! Here are the top-notch security standards XfilesPro upholds to ensure strong security for your Salesforce documents while sharing with internal or external people.
To learn more, read the blog: https://www.xfilespro.com/how-does-xfilespro-make-document-sharing-secure-and-seamless-in-salesforce/
Understanding Globus Data Transfers with NetSage

NetSage is an open privacy-aware network measurement, analysis, and visualization service designed to help end-users visualize and reason about large data transfers. NetSage traditionally has used a combination of passive measurements, including SNMP and flow data, as well as active measurements, mainly perfSONAR, to provide longitudinal network performance data visualization. It has been deployed by dozens of networks world wide, and is supported domestically by the Engagement and Performance Operations Center (EPOC), NSF #2328479. We have recently expanded the NetSage data sources to include logs for Globus data transfers, following the same privacy-preserving approach as for Flow data. Using the logs for the Texas Advanced Computing Center (TACC) as an example, this talk will walk through several different example use cases that NetSage can answer, including: Who is using Globus to share data with my institution, and what kind of performance are they able to achieve? How many transfers has Globus supported for us? Which sites are we sharing the most data with, and how is that changing over time? How is my site using Globus to move data internally, and what kind of performance do we see for those transfers? What percentage of data transfers at my institution used Globus, and how did the overall data transfer performance compare to the Globus users?
2024 RoOUG Security model for the cloud.pptx

How we've evolved the MySQL server security model from a single DBA to the cloud.
Climate Science Flows: Enabling Petabyte-Scale Climate Analysis with the Eart...

The Earth System Grid Federation (ESGF) is a global network of data servers that archives and distributes the planet’s largest collection of Earth system model output for thousands of climate and environmental scientists worldwide. Many of these petabyte-scale data archives are located in proximity to large high-performance computing (HPC) or cloud computing resources, but the primary workflow for data users consists of transferring data, and applying computations on a different system. As a part of the ESGF 2.0 US project (funded by the United States Department of Energy Office of Science), we developed pre-defined data workflows, which can be run on-demand, capable of applying many data reduction and data analysis to the large ESGF data archives, transferring only the resultant analysis (ex. visualizations, smaller data files). In this talk, we will showcase a few of these workflows, highlighting how Globus Flows can be used for petabyte-scale climate analysis.
TROUBLESHOOTING 9 TYPES OF OUTOFMEMORYERROR

Even though at surface level ‘java.lang.OutOfMemoryError’ appears as one single error; underlyingly there are 9 types of OutOfMemoryError. Each type of OutOfMemoryError has different causes, diagnosis approaches and solutions. This session equips you with the knowledge, tools, and techniques needed to troubleshoot and conquer OutOfMemoryError in all its forms, ensuring smoother, more efficient Java applications.
Into the Box 2024 - Keynote Day 2 Slides.pdf

Into the Box Keynote Day 2: Unveiling amazing updates and announcements for modern CFML developers! Get ready for exciting releases and updates on Ortus tools and products. Stay tuned for cutting-edge innovations designed to boost your productivity.
SOCRadar Research Team: Latest Activities of IntelBroker

The European Union Agency for Law Enforcement Cooperation (Europol) has suffered an alleged data breach after a notorious threat actor claimed to have exfiltrated data from its systems. Infamous data leaker IntelBroker posted on the even more infamous BreachForums hacking forum, saying that Europol suffered a data breach this month.
The alleged breach affected Europol agencies CCSE, EC3, Europol Platform for Experts, Law Enforcement Forum, and SIRIUS. Infiltration of these entities can disrupt ongoing investigations and compromise sensitive intelligence shared among international law enforcement agencies.
However, this is neither the first nor the last activity of IntekBroker. We have compiled for you what happened in the last few days. To track such hacker activities on dark web sources like hacker forums, private Telegram channels, and other hidden platforms where cyber threats often originate, you can check SOCRadar’s Dark Web News.
Stay Informed on Threat Actors’ Activity on the Dark Web with SOCRadar!
Vitthal Shirke Microservices Resume Montevideo

Software Engineering, Software Consulting, Tech Lead.
Spring Boot, Spring Cloud, Spring Core, Spring JDBC, Spring Security,
Spring Transaction, Spring MVC,
Log4j, REST/SOAP WEB-SERVICES.
Cyaniclab : Software Development Agency Portfolio.pdf

CyanicLab, an offshore custom software development company based in Sweden,India, Finland, is your go-to partner for startup development and innovative web design solutions. Our expert team specializes in crafting cutting-edge software tailored to meet the unique needs of startups and established enterprises alike. From conceptualization to execution, we offer comprehensive services including web and mobile app development, UI/UX design, and ongoing software maintenance. Ready to elevate your business? Contact CyanicLab today and let us propel your vision to success with our top-notch IT solutions.
Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...

Les Buildpacks existent depuis plus de 10 ans ! D’abord, ils étaient utilisés pour détecter et construire une application avant de la déployer sur certains PaaS. Ensuite, nous avons pu créer des images Docker (OCI) avec leur dernière génération, les Cloud Native Buildpacks (CNCF en incubation). Sont-ils une bonne alternative au Dockerfile ? Que sont les buildpacks Paketo ? Quelles communautés les soutiennent et comment ?
Venez le découvrir lors de cette session ignite
WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation

WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation
Recently uploaded (20)
Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL

Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL
OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam

OpenFOAM solver for Helmholtz equation, helmholtzFoam / helmholtzBubbleFoam
How Recreation Management Software Can Streamline Your Operations.pptx

How Recreation Management Software Can Streamline Your Operations.pptx
Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf

Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf
Strategies for Successful Data Migration Tools.pptx

Strategies for Successful Data Migration Tools.pptx
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...
How Does XfilesPro Ensure Security While Sharing Documents in Salesforce?

How Does XfilesPro Ensure Security While Sharing Documents in Salesforce?
Climate Science Flows: Enabling Petabyte-Scale Climate Analysis with the Eart...

Climate Science Flows: Enabling Petabyte-Scale Climate Analysis with the Eart...
SOCRadar Research Team: Latest Activities of IntelBroker

SOCRadar Research Team: Latest Activities of IntelBroker
Cyaniclab : Software Development Agency Portfolio.pdf

Cyaniclab : Software Development Agency Portfolio.pdf
Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...

Paketo Buildpacks : la meilleure façon de construire des images OCI? DevopsDa...
WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation

WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation
Iterations and Recursions
- 1. Iterations and Recursions Abdul Rahman Sherzad Lecturer at Compute Science faculty Herat University
- 2. Recursive Method? • A recursive method is a method that calls itself. • There are two key requirements in order to make sure that the recursion is successful: With each call the problem should become smaller and simpler. The method will eventually should lead to a point where no longer calls itself – This point is called the base case. When the recursive method is called with a base case, the result is returned to the previous method calls until the original call of the method eventually returns the final result. 2
- 3. Iteration • Repeated execution of a set of instructions is called iteration. • It is the act of repeating a process to perform specific action on a collection of elements, one at a time, each repetition of the process is called an iteration, The results of one iteration are used as the starting point for the next iteration until the condition is met. • Iteration is most commonly expressed using loop statements. For statement While statement Do While statement 3
- 4. Factorial • Factorial of a non-negative integer n is the product of all positive integers less than or equal to n. 5! = 5 * 4 * 3 * 2 * 1 120 • Factorial of n is denoted by n! • Factorial of 0 is 1. • Factorial for a negative number does not exist. 4
- 6. factorial(5)- Recursion Execution • This slide illustrates recursive steps computing 5! Step 1: 5 * factorial(4) Step 2: 4 * factorial(3) Step 3: 3 * factorial(2) Step 4: 2 * factorial(1) Step 5: 1 6 Step 6: return 1 Step 7: return 2 * 1 2 Step 8: return 3 * 2 6 Step 9: return 4 * 6 24 Step 10: return 5 * 24 120
- 8. factorial(5)- Iteration Execution • This slide illustrates recursive steps computing 5! Step 1: result = result * 5 result = 1 * 5 Step 2: result = result * 4 result = 5 * 4 Step 3: result = result * 3 result = 20 * 3 Step 4: result = result * 2 result = 60 * 2 Step 5: return result return 120 8
- 9. Fibonacci Number • The Fibonacci sequence is a series of numbers where a number is found by adding up the two numbers preceding it. • The Fibonacci sequence beings with 0 and 1. • The Fibonacci sequence is written as a rule as follow: Fibonaccin = Fibonaccin-1 + Fibonaccin-2 • The first 11 Fibonacci numbers Fibonaccin for n = 0, 1, 2, … , 11 are: 9 F0 F1 F2 F3 F4 F5 F6 F7 F8 F9 F10 0 1 1 2 3 5 8 13 21 34 55
- 11. fibonacci(5)- Recursion Execution fibonacci(5) fibonacci(4) fibonacci(3) fibonacci(2) fibonacci(1) fibonacci(0) fibonacci(1) fibonacci(2) fibonacci(1) fibonacci(0) fibonacci(3) fibonacci(2) fibonacci(1) fibonacci(0) fibonacci(1) 11 1 0 1 1 2 1 0 1 0 11 3 1 2 5
- 13. GCD (Greatest Common Divisor) • To calculate and find the Greatest Common Divisor (GCD) of two integer numbers num1 and num2 using Euclid’s algorithm is another great and suited example demonstrating recursion. • Euclidean algorithm is defined as follow: if num2 == 0 then GCD (num1, num2) is num1 else GCD (num1, num2) is GCD (num2, modulus(num1 / num2)) • Note: The modulus is the remainder when num1 is divided by num2 and it is computed in Java by using the % operator. 13
- 15. gcd(120, 35)-Recursion Execution • Following steps illustrate calculating gcd(187, 77): Step 1: gcd(120, 35) Step 2: gcd(35, 15) Step 3: gcd(15, 5) Step 4: gcd(5, 0) Step 5: 5 15 Step 6: return 5 Step 7: return 5 Step 8: return 5 Step 9: return 5 Step 10: return 5
- 17. Binary Search • Binary search – also called half-interval search, logarithmic search or binary chop – is a search algorithm that finds the position of a target value within a sorted array. • Binary search is a fast and efficient search algorithm with run-time complexity of Ο(log n). • Binary search works on the principle of divide and conquer. • Binary search compares the target value to the middle element of the array: If they are equal, then the index of item is returned. If they are unequal, the half in which the target cannot lie is eliminated and the search continues on the remaining half until it is successful. If the search ends with the remaining half being empty, the target is not in the array. 17
- 18. Binary Search - Recursion 18
- 19. binarySearch(input,0, 7, 25)-Recursion Execution 1 5 10 20middle 25target 30 44 55 19 binarySearch(input, 0, 7, 25) middle = (0 + 7) / 2 3, check sortedArray[3] 1 5 10 20 25target 30middle 44 55 binarySearch(input, 4, 7, 25) middle = (4 + 7) / 2 5, check sortedArray[5] They are not match; target value ‘25’ is > middle value ‘20’. Hence … 1 5 10 20 25target middle 30 44 55 binarySearch(input, 4, 4, 25) middle = (4 + 4) / 2 4, check sortedArray[4] They are not match; target value ‘25’ is < middle value ‘30’. Hence … They are matched; target value ‘25’ is == middle value ‘25’. Hence … return middle; return 4;
- 20. Binary Search - Iteration 20
- 21. Traverse Directory and Sub-Directories 21
- 22. Traverse Directory and Sub-Directories - Recursion 22
- 23. Traverse Directory and Sub- Directories - Recursion • In such particular cases, recursive solutions are probably better and efficient than non-recursive ones (Iteration and Stack). • Additionally, recursive solutions are easier to code as well as easier to understand than the non-recursive ones. • Caution: The only potential problem with recursions are that they overflow the stack if the directory tree is intensively deep. 23
- 24. Traverse Directory and Sub-Directories – Iteration and Stack 24
- 25. Traverse Directory and Sub- Directories - Iteration • In such cases, Iteration and Stack together are alternative solutions to avoid recursions. • Instead of recursive calls, the list containing the current directory’s files are pushed onto the Stack. In this case, all items inside the parent directory are pushed onto the Stack. • Then the new directory is read in order to traverse them. In this case, all the items inside the son directory are also pushed onto the Stack. • When this processed is finished, the files are popped from the Stack. In this case, all the files inside the son directory, then all the files inside the nephew directory and finally continue with the parent directory. • This will give you a Depth-First traversal. 25
- 26. Conclusion • There are similarities between recursion and iteration. • Actually, any problems that can be solved with iterations can be done with recursions. There are some programming languages that use recursion exclusively. • In the factorial, greatest common divisor and binary search problems, the iterative and recursive solutions use roughly the same algorithms, and their efficiency is approximately the same. • In the exponentiation problem e.g. Fibonacci; the iterative solution takes linear time to complete, while the recursive solution executes in log time. 26
- 27. Conclusion • There are some problems that are simple to solve with recursions, but they are comparatively difficult to solve with iterations (e.g. tree traversal). • Iterations are recommended for algorithms that are easier to explain in terms of iterations. • Recursions are good a problem can be solved by divide and conquer technique (e.g. Searching binary trees). Warning: Infinite recursion causes a Stack Overflow Error! 27
- 28. 28
