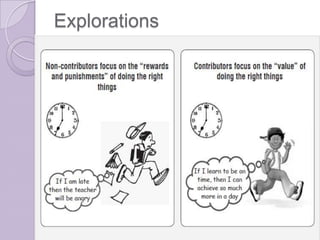
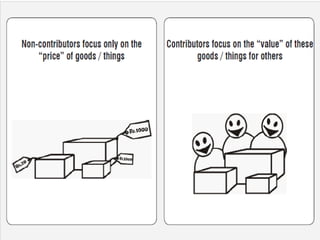
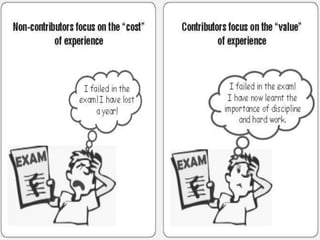
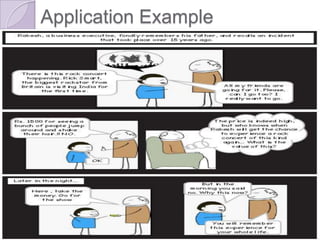
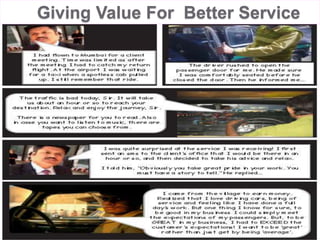
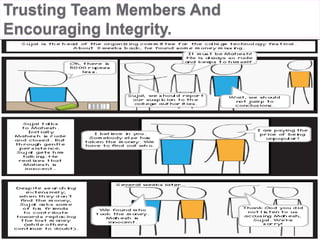
This document outlines the concept of focusing on value as a contributor. It defines focusing on value as aiming to create a positive impact and tangible contributions for stakeholders like oneself, one's family, team, organization, customers, and society. Creating value means making a difference through achieving goals, creating products, enhancing human interactions, or increasing one's own and others' capacities. The document provides examples of focusing on value through better customer service, trusting teammates, and the contributions of significant historical figures to society. It concludes that focusing on value makes one results-oriented and able to continuously work towards revising visions and achieving dreams.