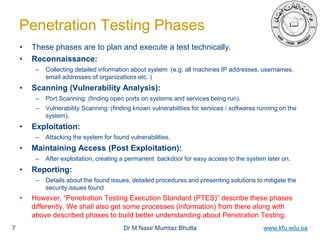
This document outlines the phases of a penetration testing execution, with a focus on the reconnaissance phase. It discusses the reconnaissance phase in depth, including levels of information gathering, goals of information gathering through open source intelligence (OSINT), and types of corporate and target details that should be collected. The key aspects covered are the importance of gathering information before launching attacks, doing so in a legal and ethical manner according to the rules of engagement, and focusing reconnaissance efforts on information directly relevant to the goals of the penetration test. The overall goal of the reconnaissance phase is to safely and effectively collect intelligence on the target to inform subsequent phases of testing.