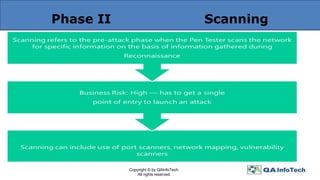
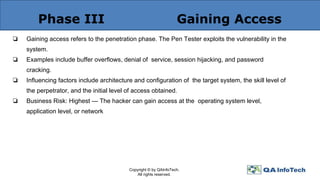
The document outlines an agenda for a security and penetration testing discussion, introducing key concepts including information security, vulnerability scanning, and penetration testing methodologies. It emphasizes the importance of ethical hacking, the need for security tests, and details the phases of penetration testing, such as reconnaissance and gaining access. The final deliverables of a penetration test include a comprehensive report detailing findings, analyses, and recommended remediation measures.