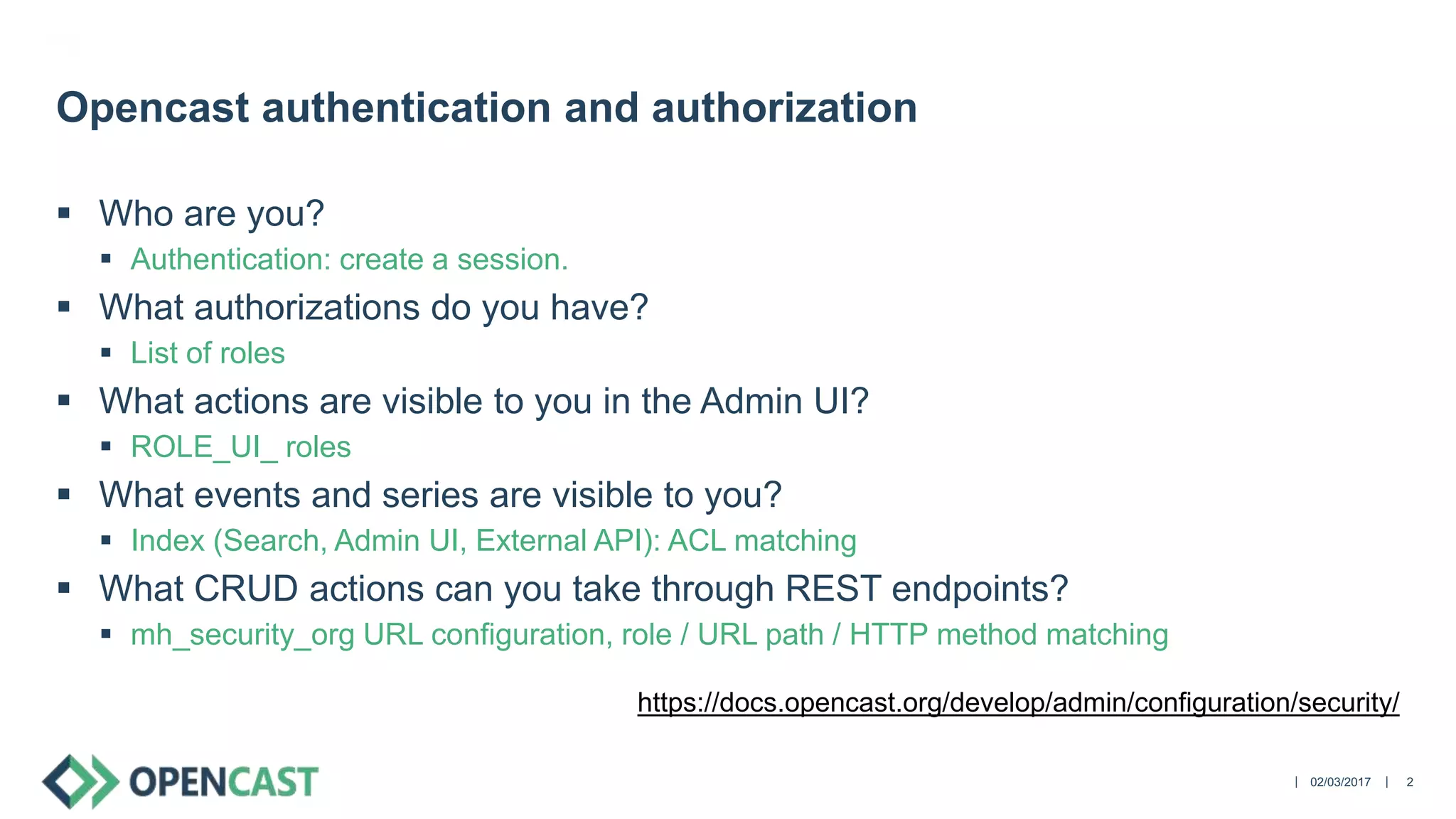
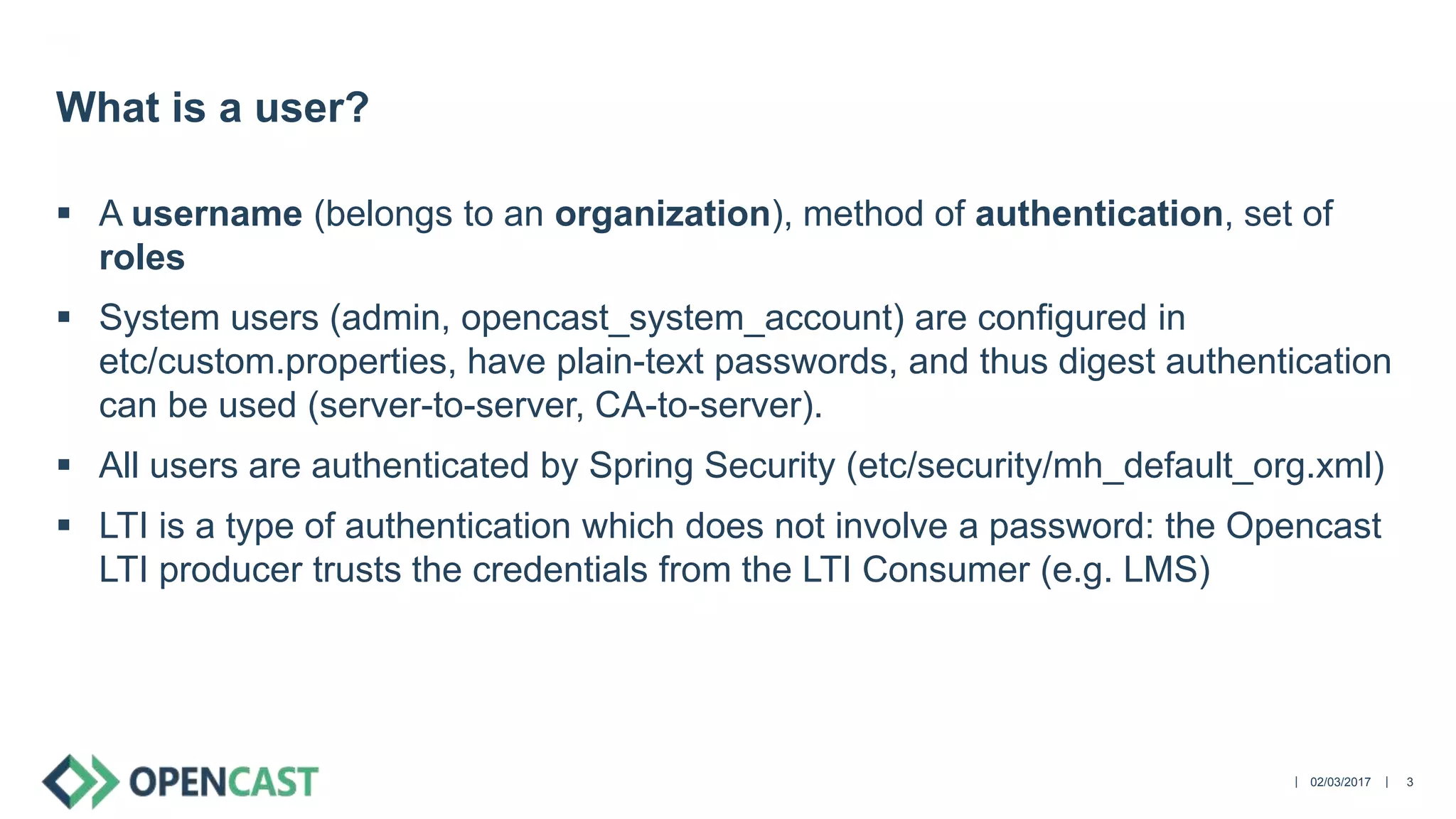
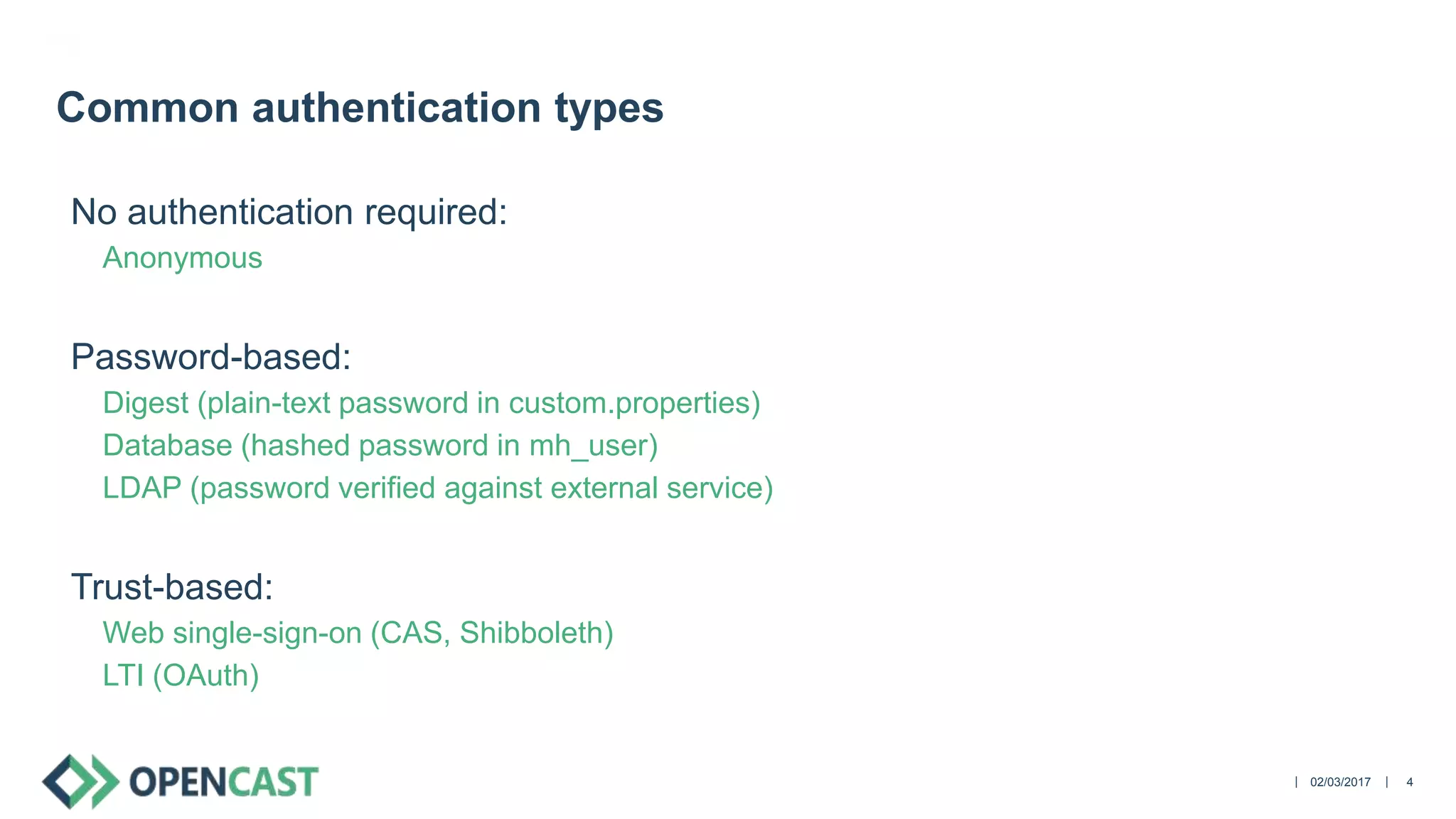
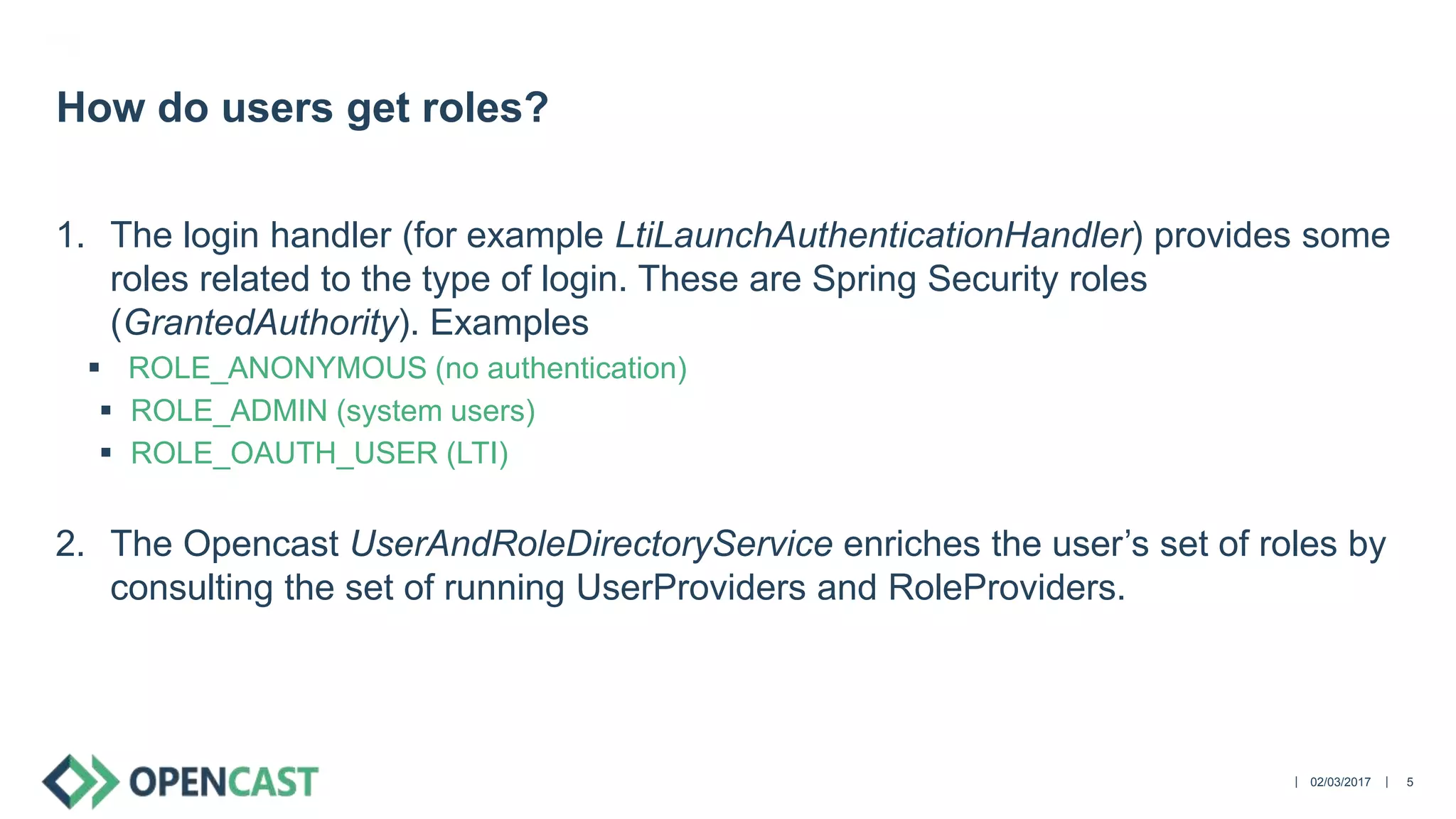
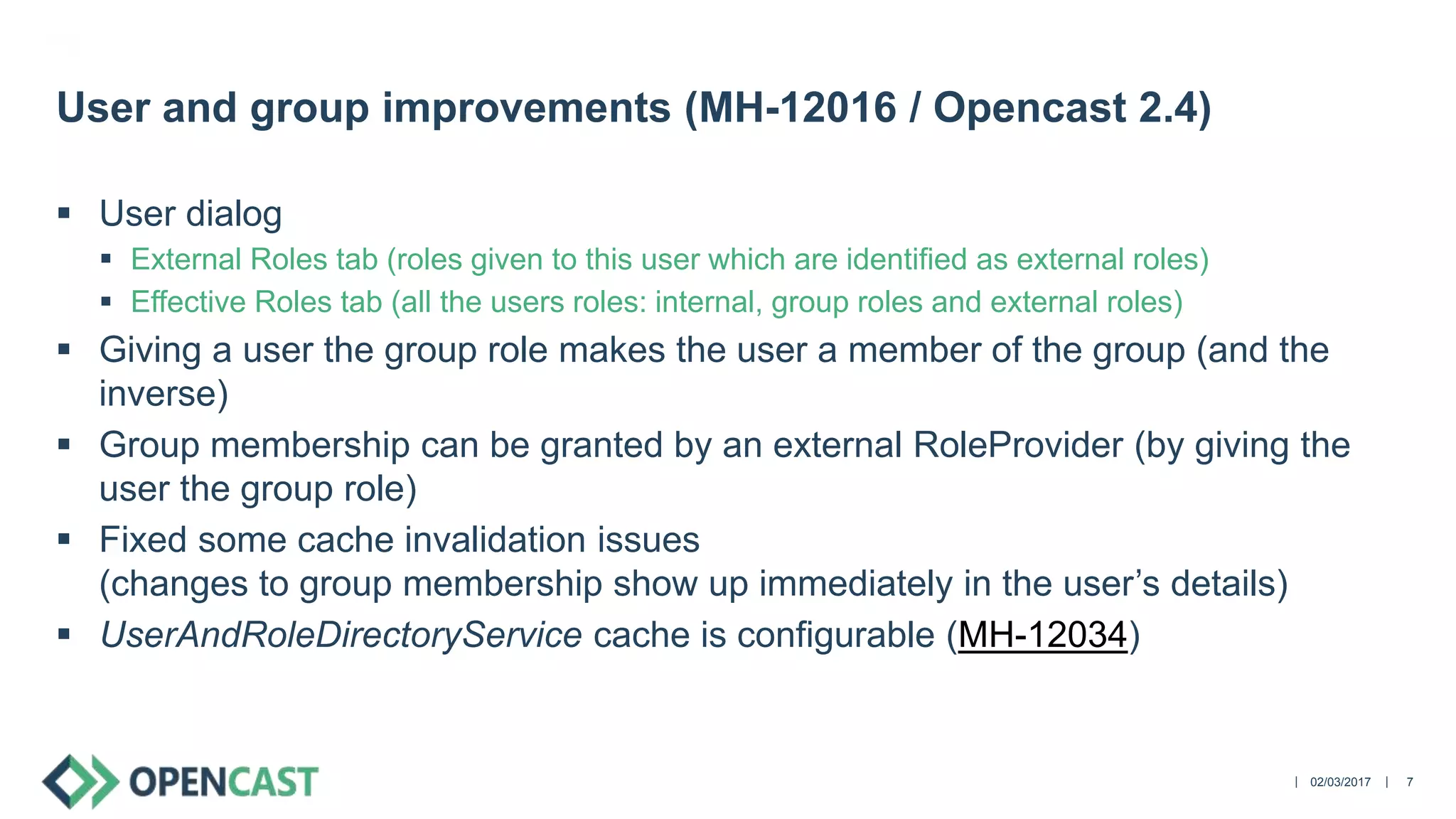
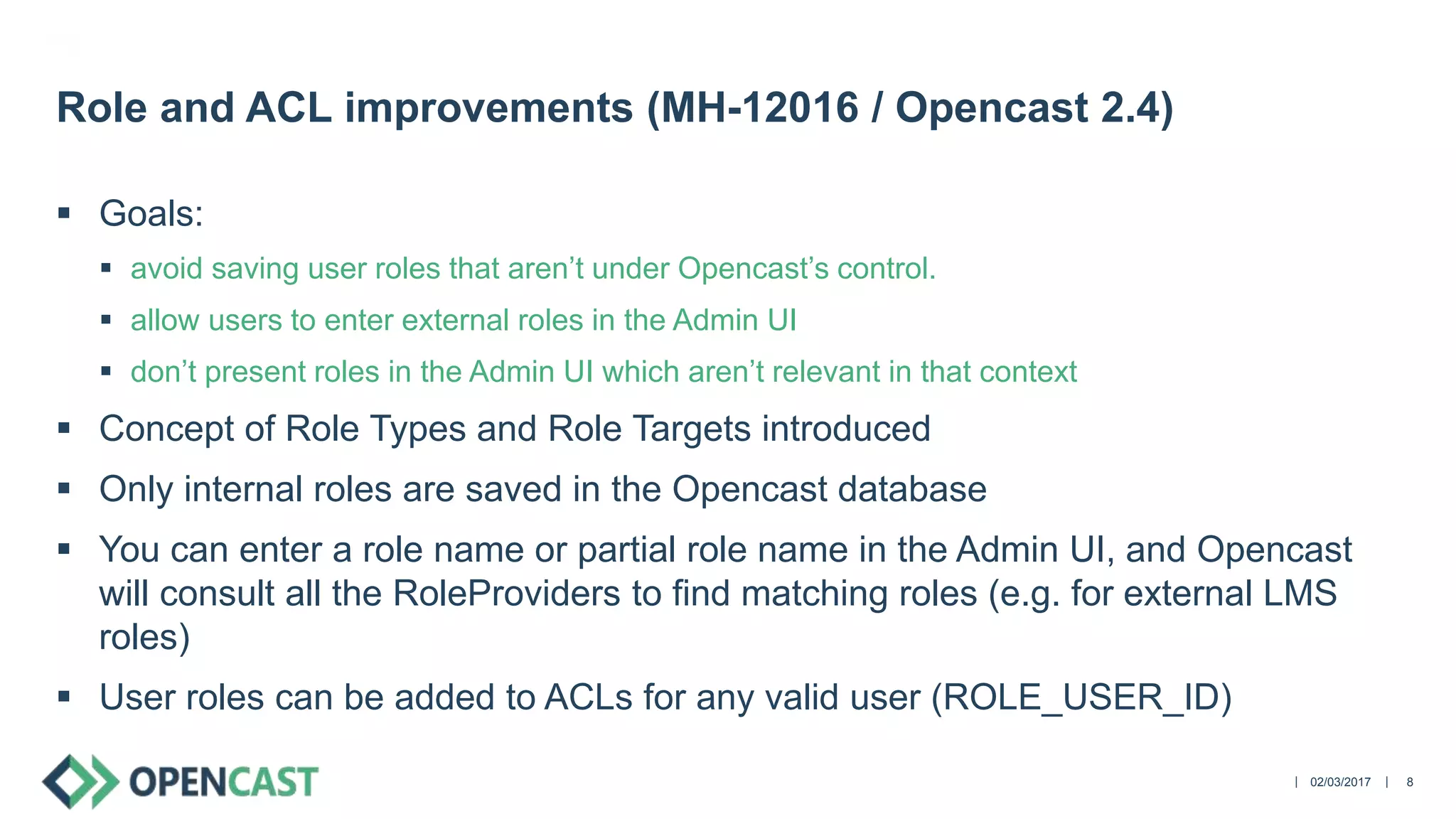
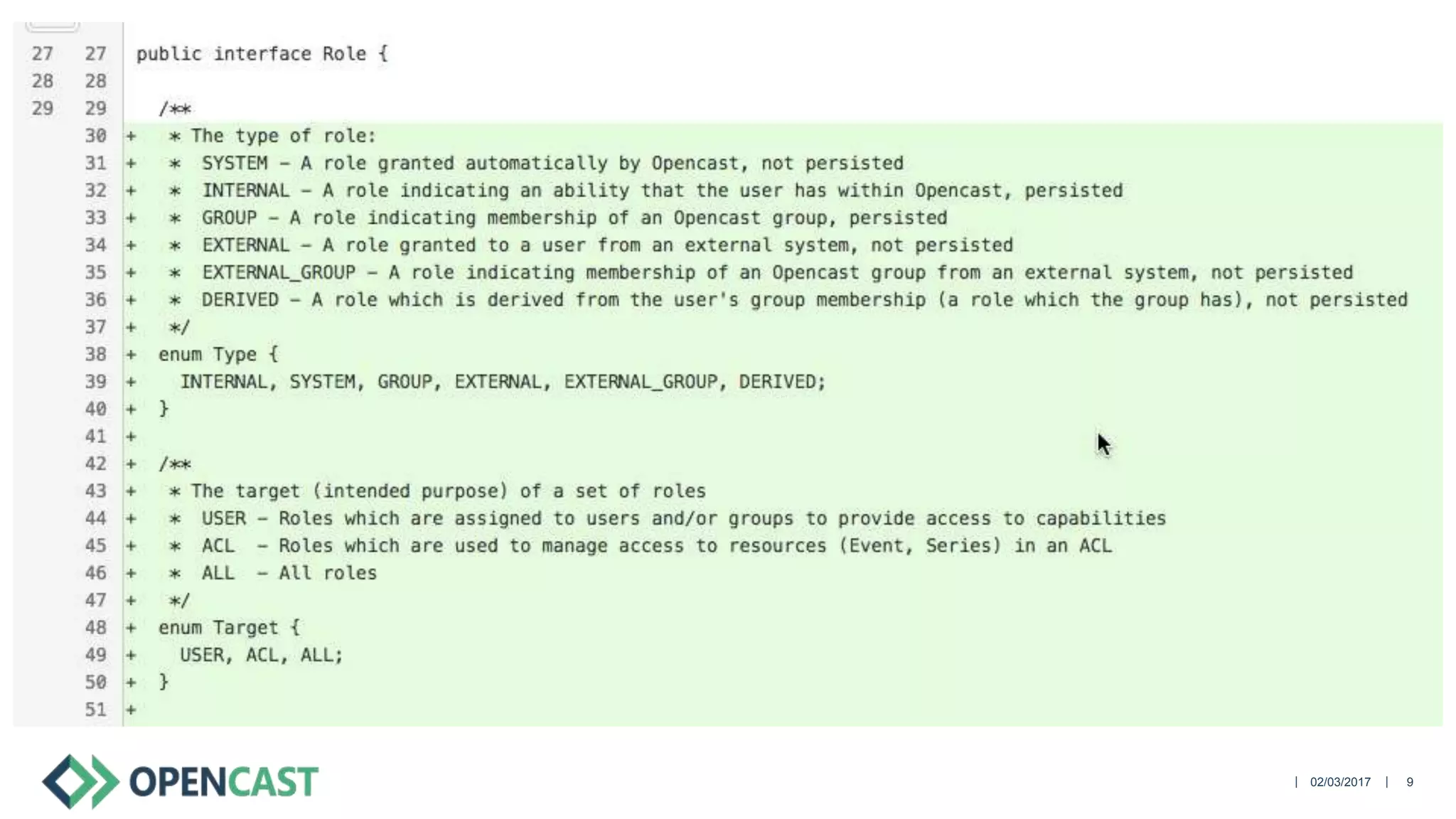
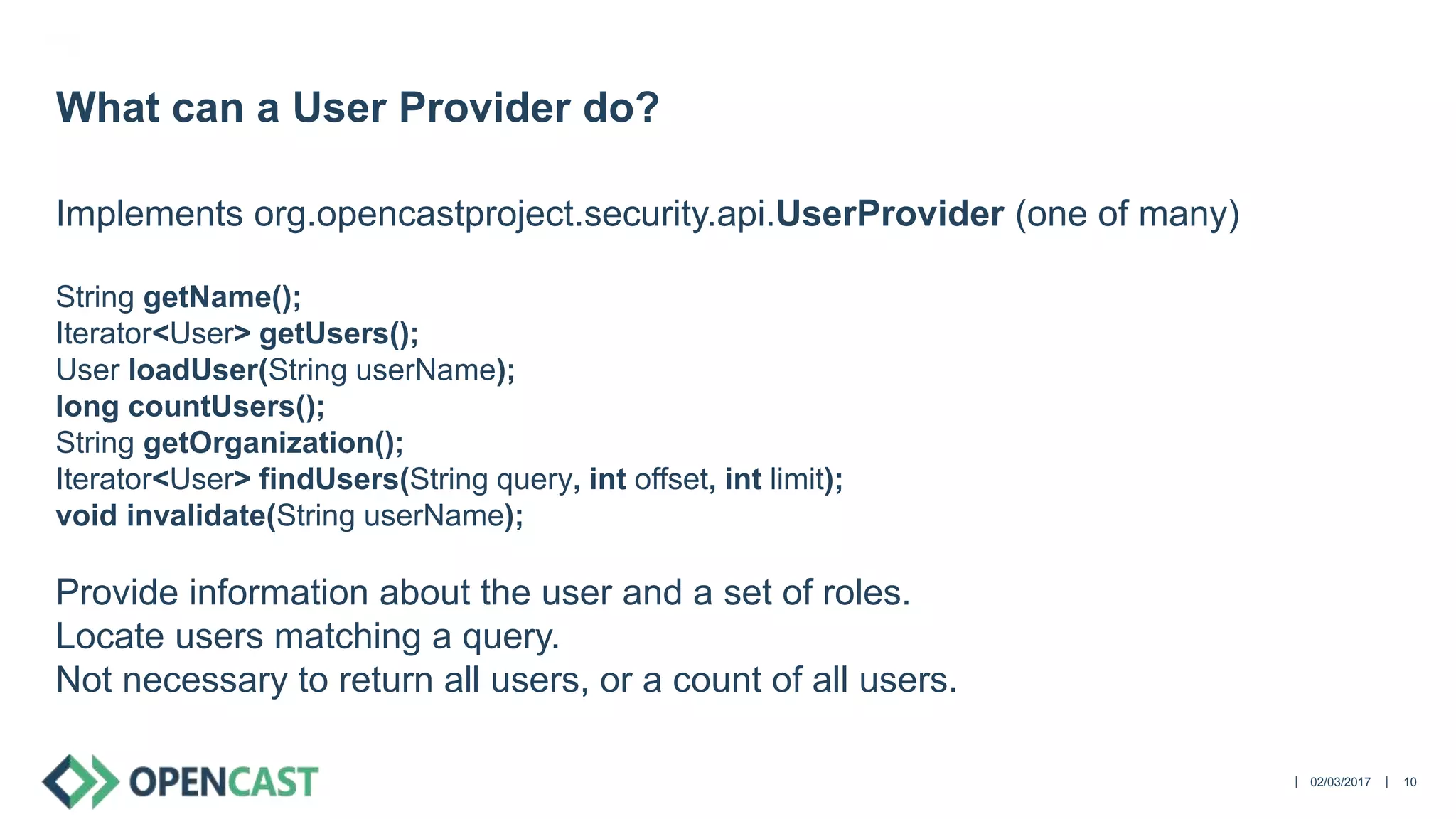
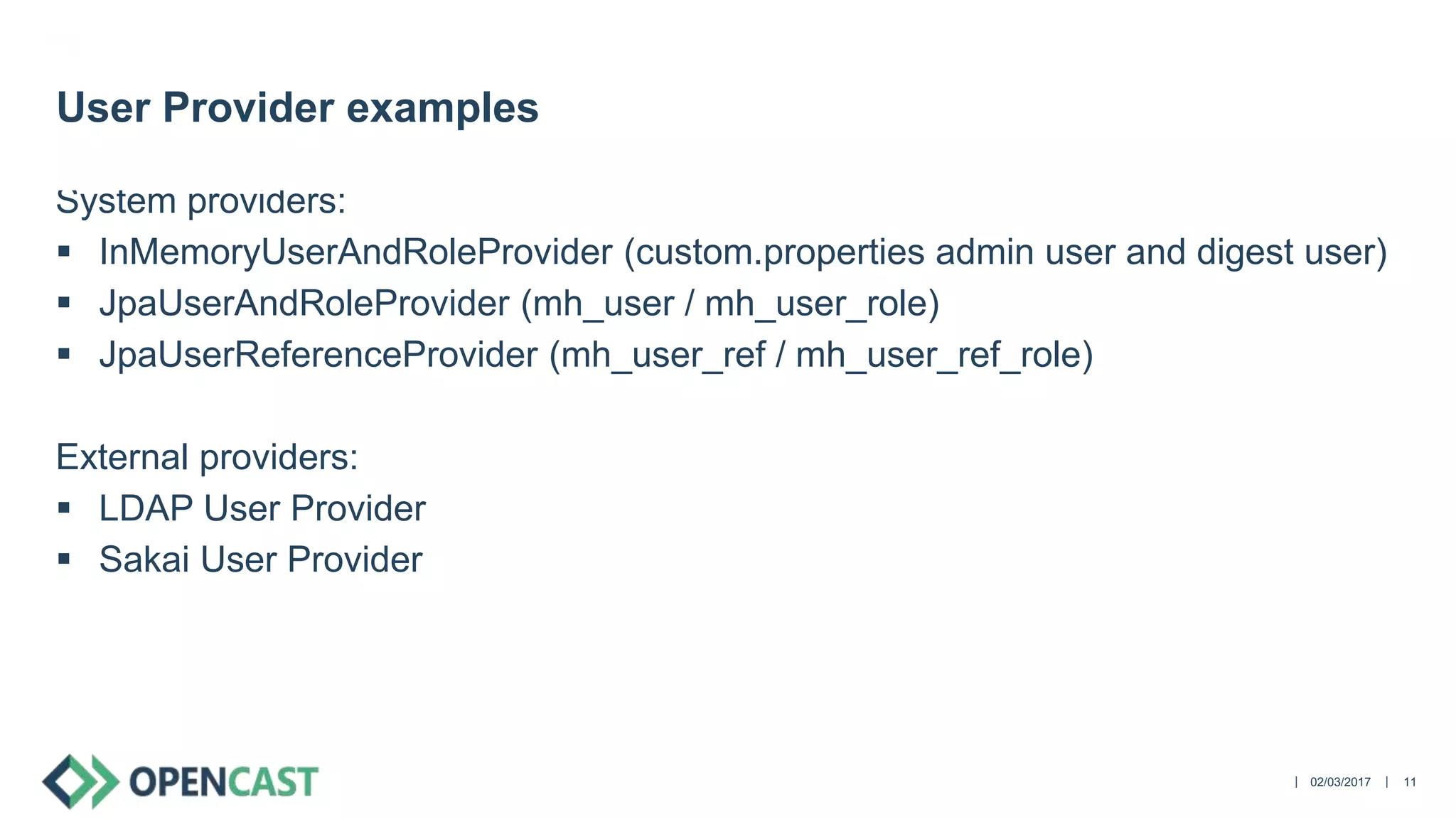
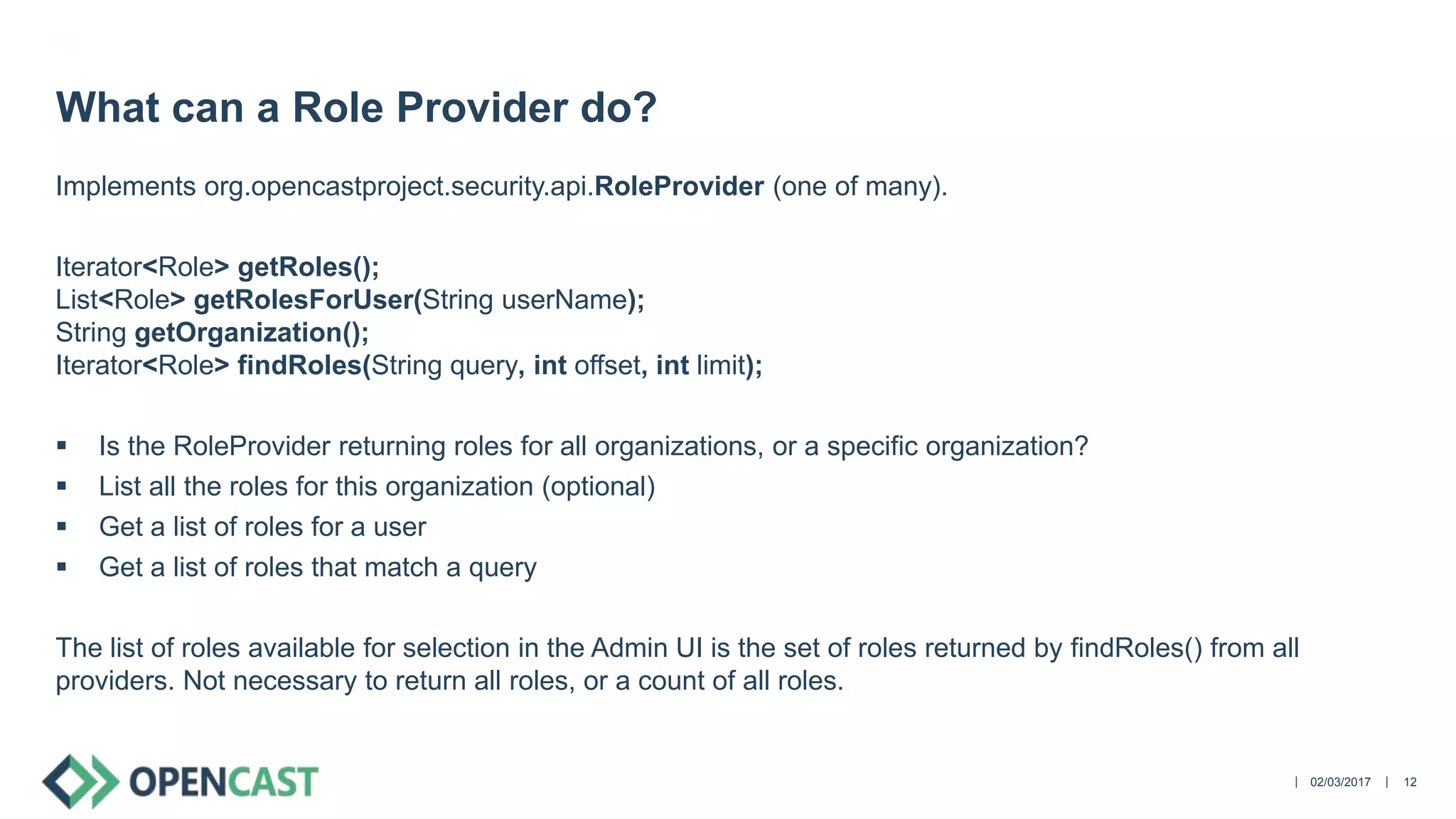
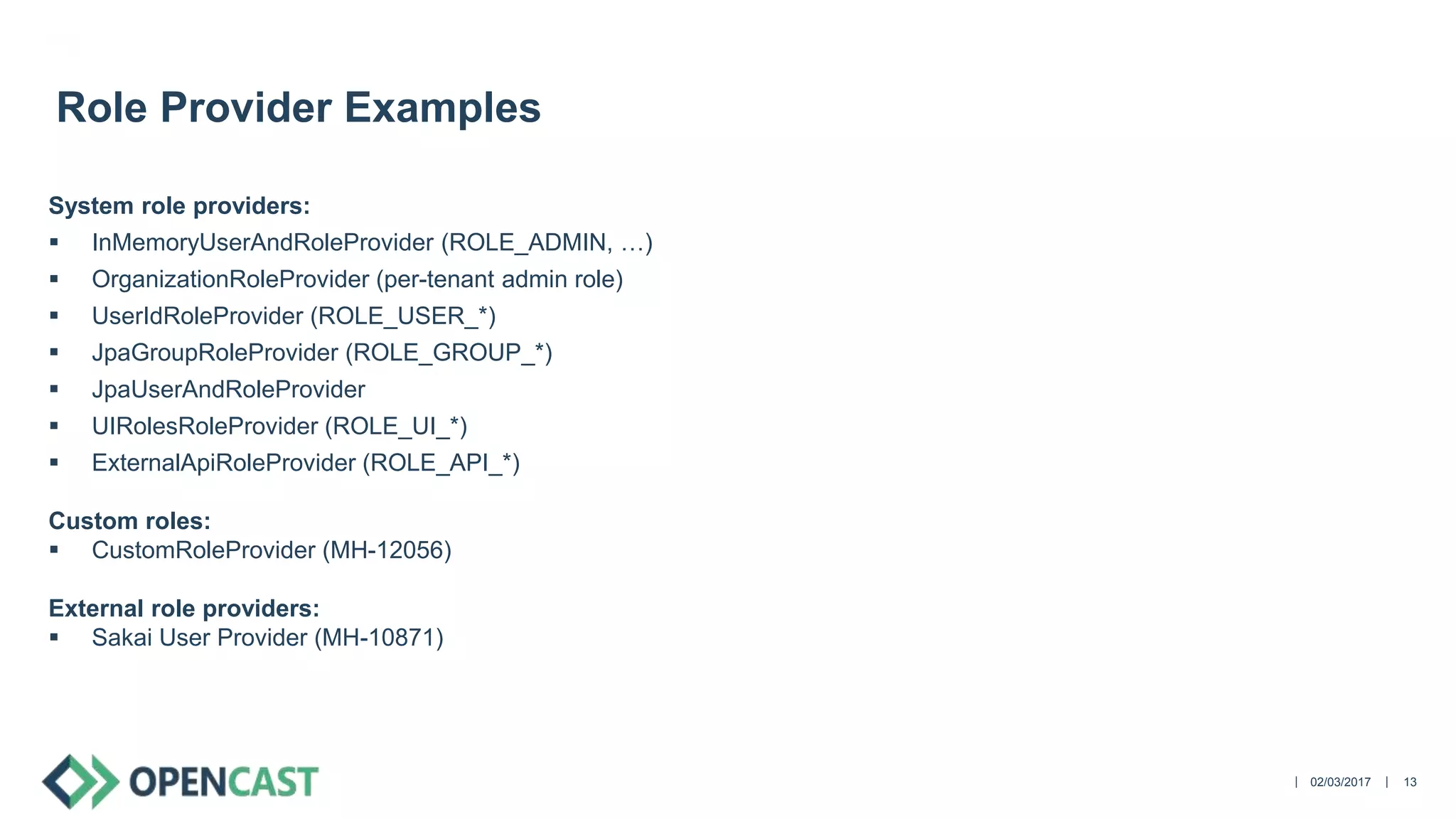
El documento describe la integración de OpenCast con sistemas externos, citando aspectos claves como la autenticación y autorización de usuarios, y la gestión de roles y grupos. Se presentan diferentes métodos de autenticación como LTI y LDAP, y se discuten mejoras en la administración de roles y grupos para evitar complicaciones y mejorar el rendimiento del sistema. Además, se abordan las funcionalidades de los proveedores de usuarios y roles en el contexto de OpenCast.