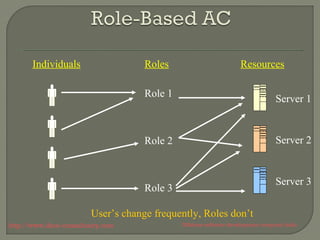
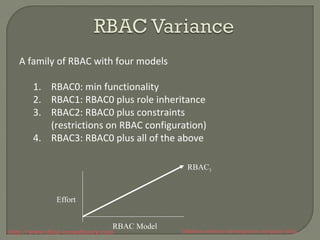
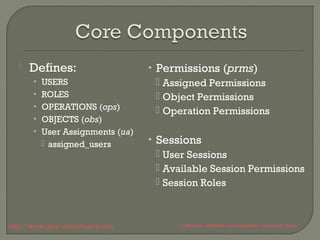
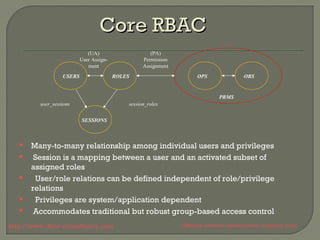
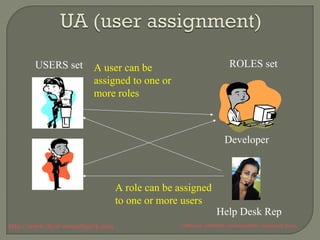
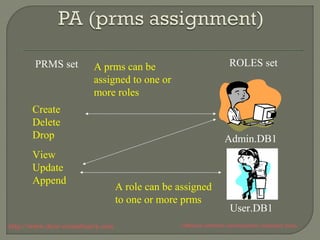
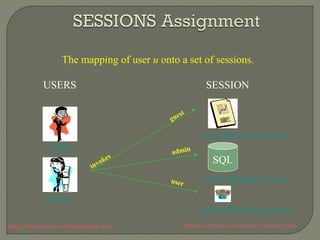
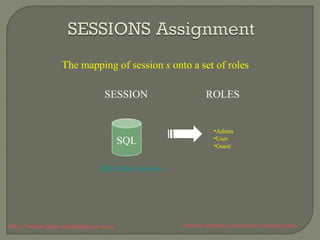
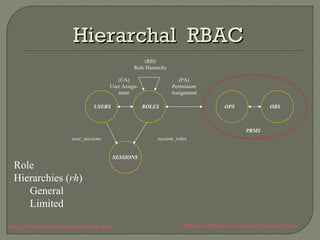
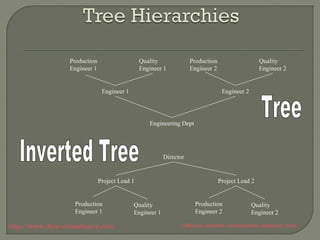
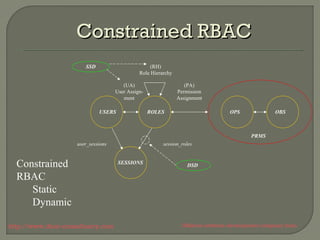
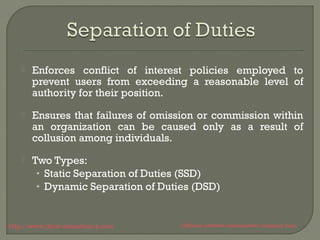
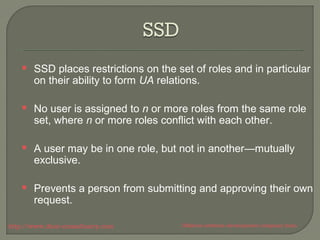
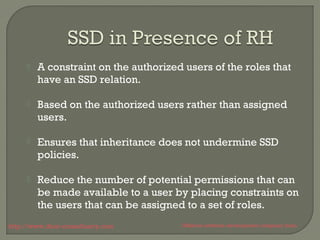
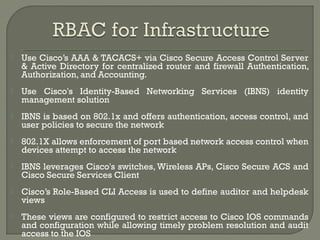
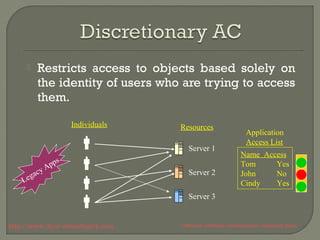
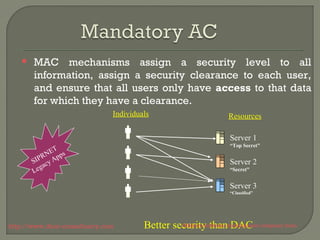
The document discusses access control and role-based access control (RBAC) models. It describes the core components of RBAC including users, roles, permissions, and role hierarchies. RBAC assigns system access based on a user's role within an organization and restricts access to authorized users. The document outlines how RBAC can be implemented in a small company and used to define roles for network devices, applications, and systems to enforce access controls and facilitate auditing.
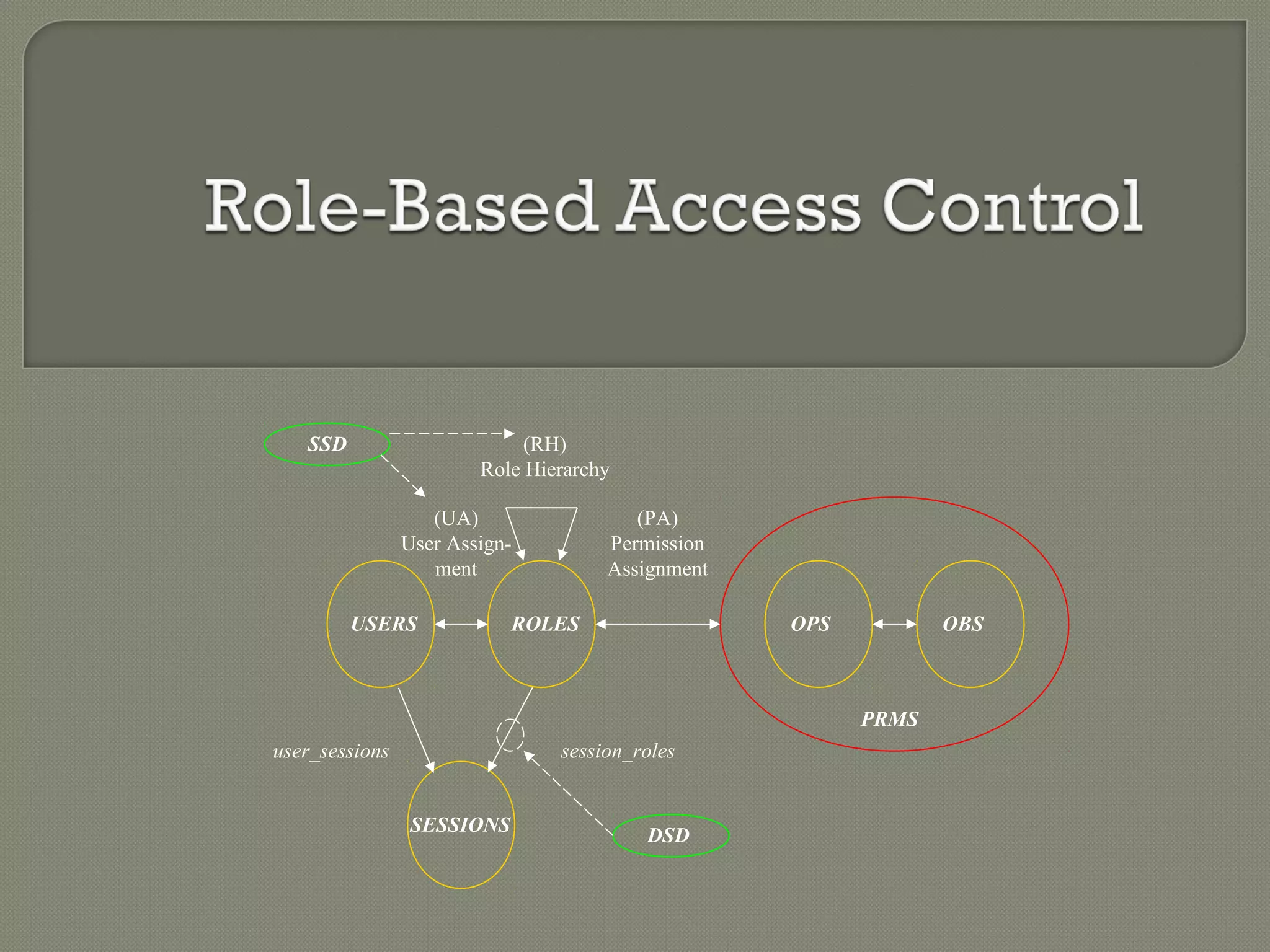
![ A user has access to an object based on
the assigned role.
Roles are defined based on job functions.
Permissions are defined based on job
authority and responsibilities within a job
function.
Operations on an object are invocated
based on the permissions.
The object is concerned with the user’s
role and not the user.
“Ideally, the [RBAC]
system is clearly
defined and agile,
making the addition
of new applications,
roles, and employees
as efficient as
possible”
http://www.ifour-consultancy.com Offshore software development company India](https://image.slidesharecdn.com/rolebasedaccesscontrol-rbac-140910002632-phpapp02/85/Role-based-access-control-RBAC-5-320.jpg)