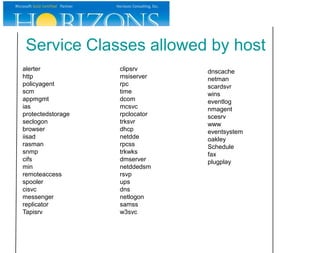
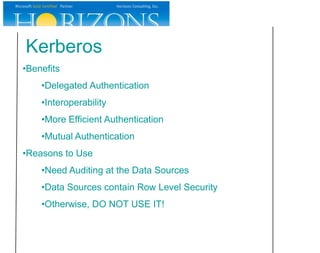
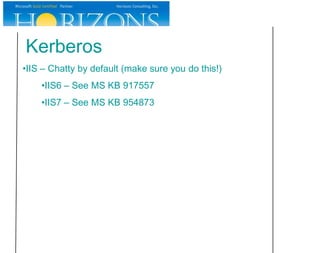
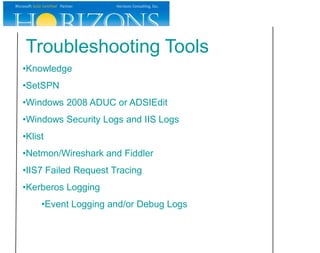
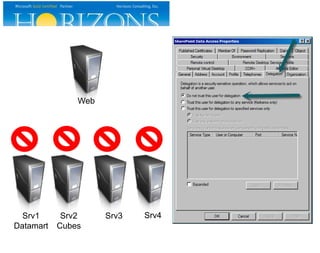
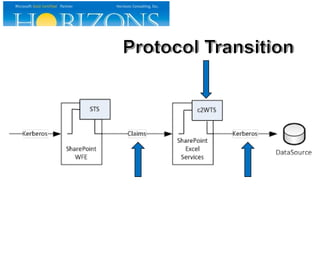
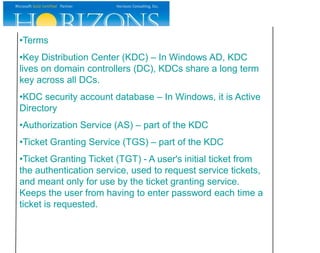
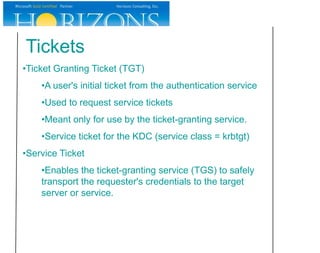
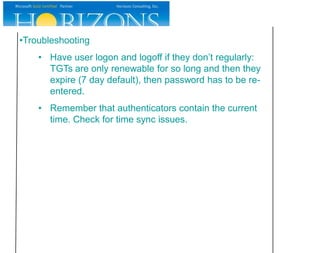
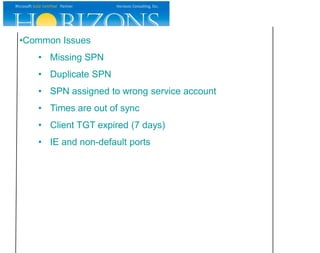
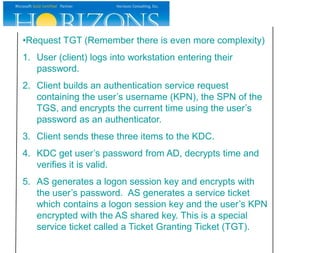
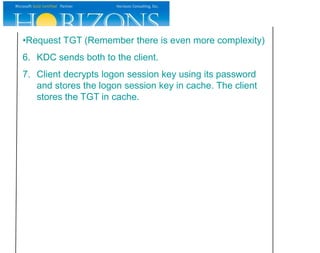
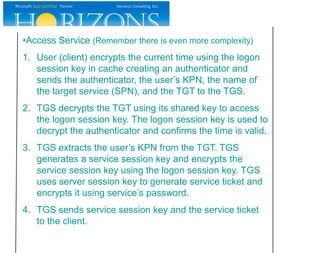
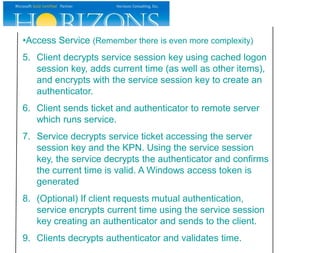
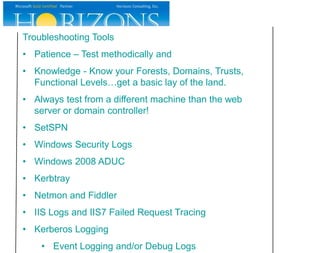
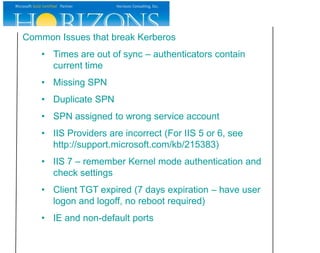
This document provides an overview and agenda for a Kerberos survival guide presentation. The presentation will cover Kerberos logon process, accessing a web site using Kerberos, miscellaneous Kerberos information, and complex Kerberos configurations. It includes dependencies, service principal names (SPNs), and troubleshooting tools for Kerberos. The presentation aims to provide essential information about Kerberos without overcomplicating details.