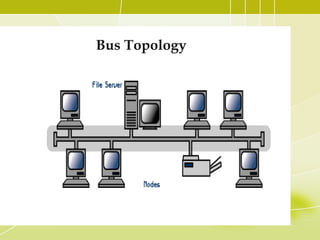
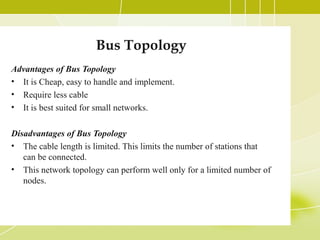
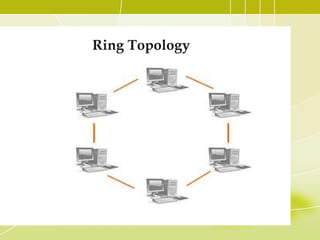
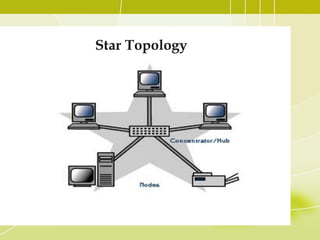
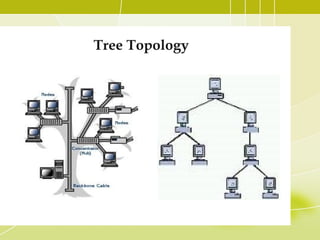
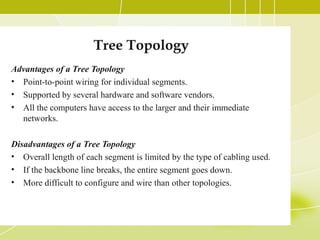
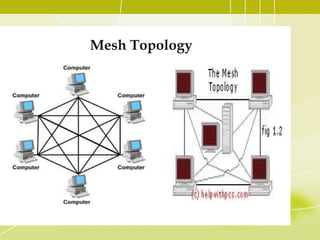
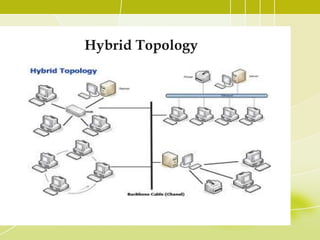
This document discusses different types of computer network topologies. It describes bus, star, ring, tree, mesh, and hybrid topologies. For each topology, it provides details on the logical arrangement of nodes, advantages like ease of installation and disadvantages like single point of failure. A hybrid topology combines two or more standard topologies to achieve flexibility and reliability, though it is more expensive than a single topology.