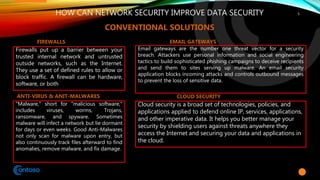
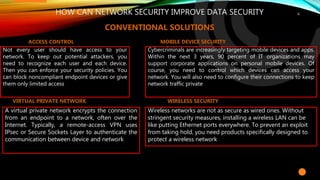
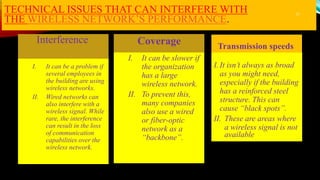
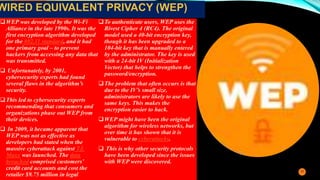
The document discusses network and data security. It notes that there is a hacker attack every 39 seconds and over 300,000 new malware are created daily, posing significant threats. It then defines network security and data protection, and discusses various technical and organizational strategies that can help improve security, such as firewalls, antivirus software, access control, encryption protocols like WPA2, and employee training. The document emphasizes adopting a holistic, next-generation approach to endpoint security to effectively combat modern cyber threats.




![19
Steps
Instructions
Concept/Main
Purpose[Abstract/Introduction]
Problem[technological
significance or any problem
solved→ look in the Introduction
part of this paper]
Solutions[Experiment/Methodology+
Discussion]
Discussion[Conclusion]
o C1;P2;L3;S4
Review Paper](https://image.slidesharecdn.com/networksecuritydataprotectiontems-210303170324/85/Network-Security-of-Data-Protection-19-320.jpg)
