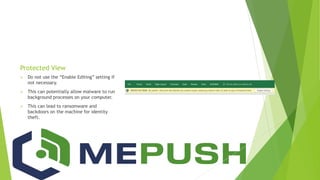
The document outlines critical information on internet safety, emphasizing the rising costs and frequency of cyber attacks, particularly on small businesses. It highlights various forms of malware and social engineering tactics like phishing, along with best practices for protecting data and ensuring compliance with regulations such as HIPAA and PCI. Additionally, the document discusses cybersecurity insurance and risk management strategies, and offers tips for maintaining security and backup protocols.