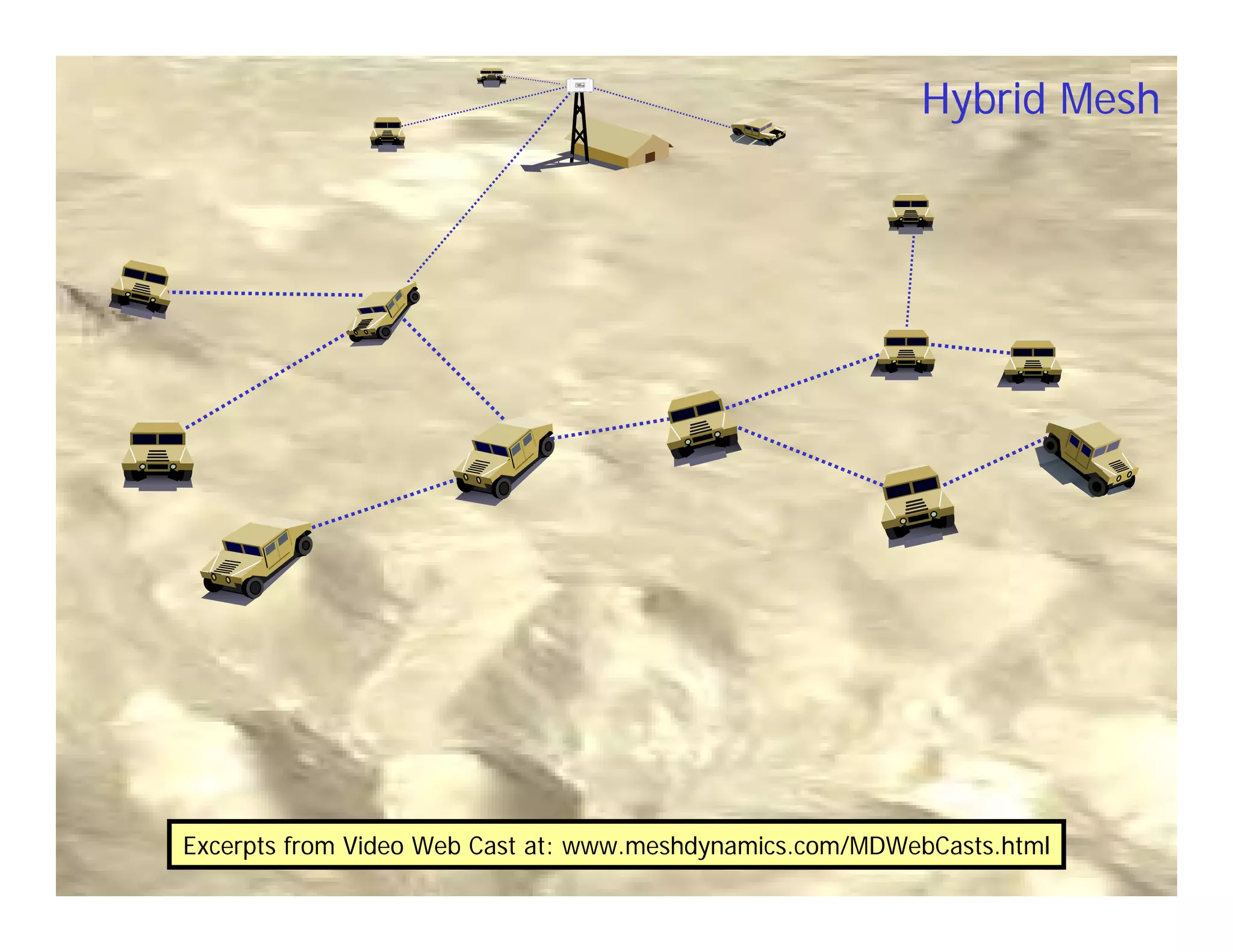
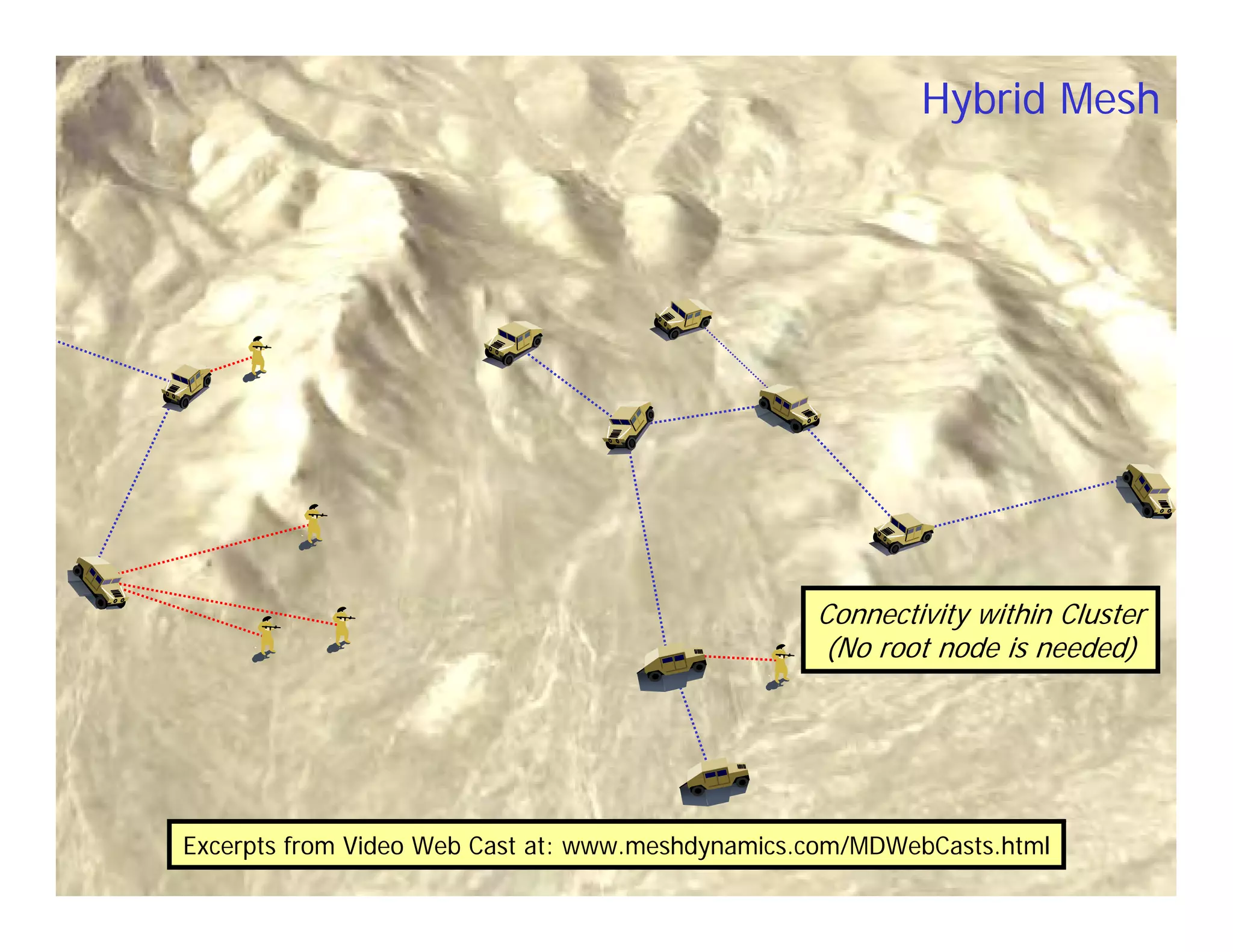
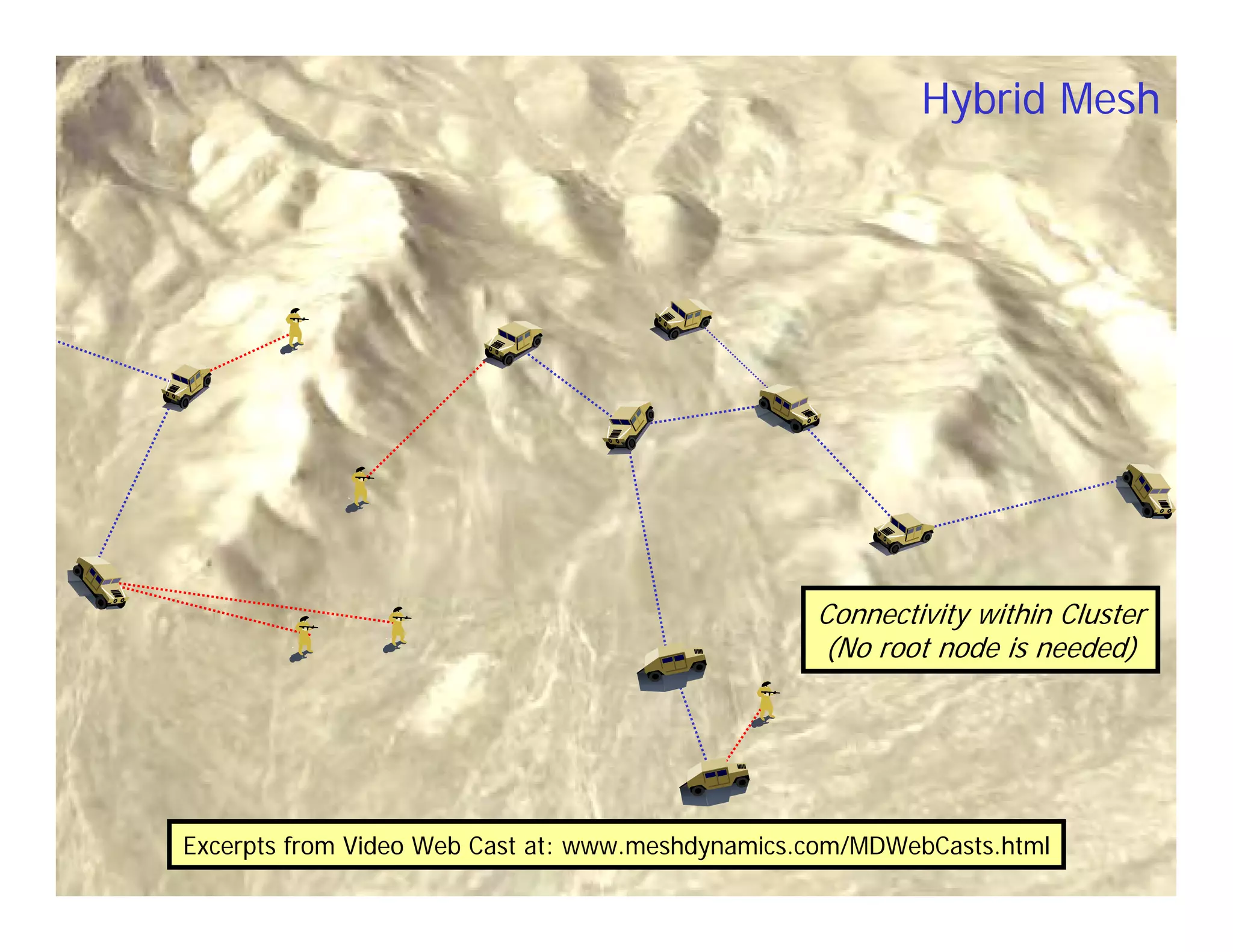
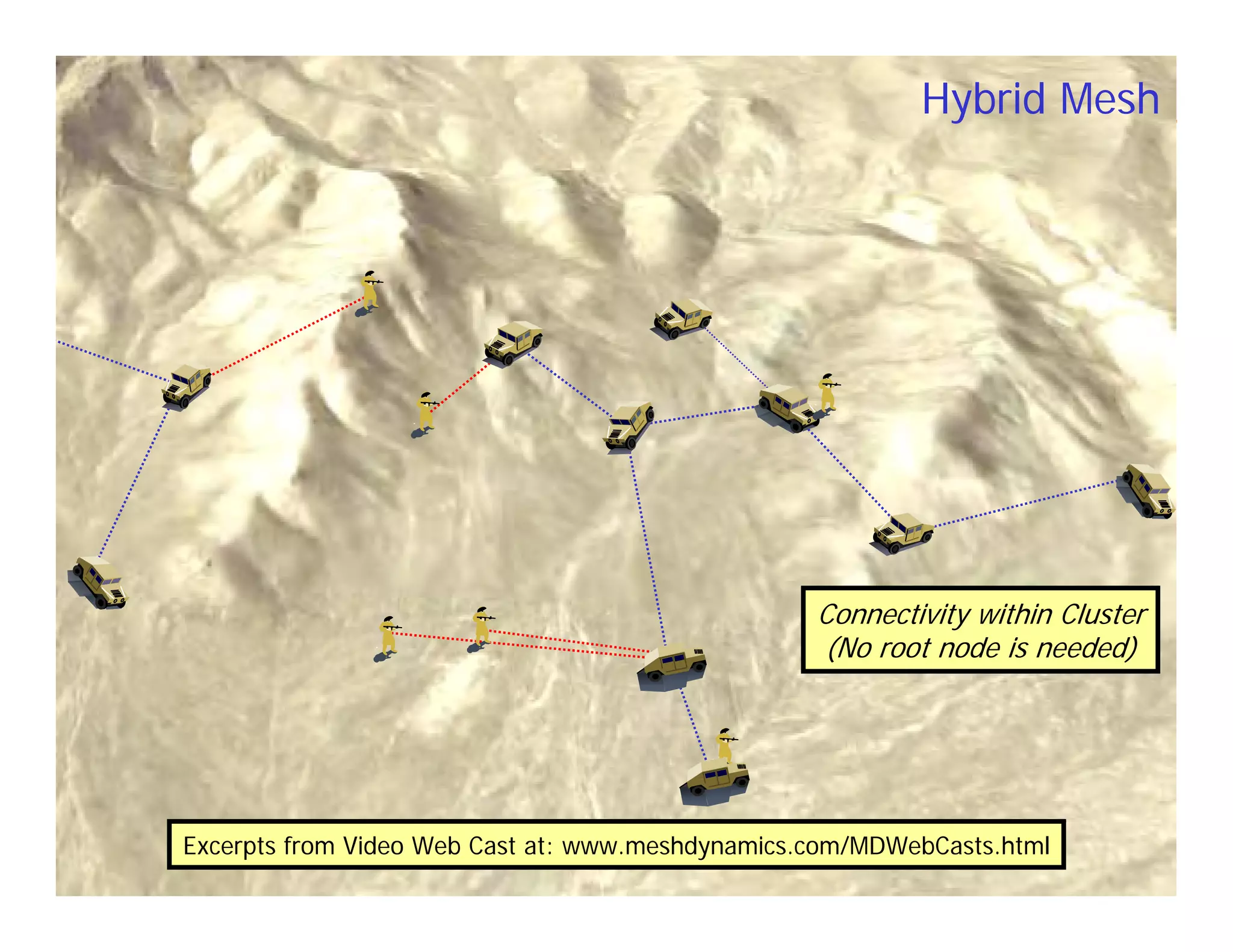
MeshDynamics provides a comprehensive overview of its multi-radio mesh technology, highlighting the company's development milestones, product releases, and extensive network deployments across various sectors, including military, mining, and public safety. Key competitive advantages include high performance, exceptional scalability, dynamic radio intelligence, and a platform-agnostic software architecture. The document emphasizes the technology's capability to maintain high bandwidth and low latency, enabling effective communication in challenging environments.

![Proven Scalability
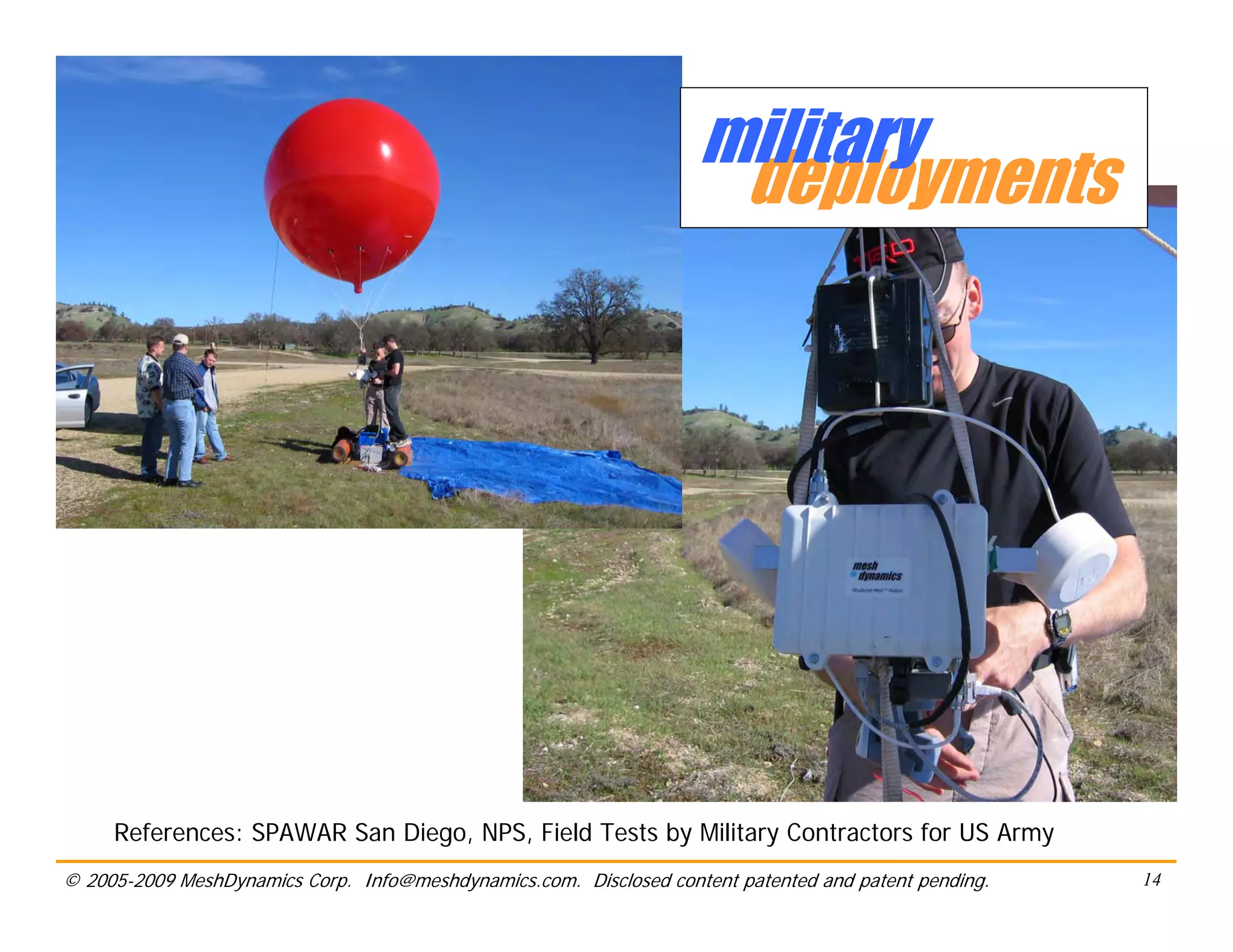
• Events/tactical networks
– Fast set-up, interference avoidance, high performance for video
– 100+ Nodes with Professional Golfers Assoc.[IBM/PGA]
• Mining, Seismic Exploration
– High performance over many hops, compact size
– Scalability demonstrated in underground mine 25+ hops long, 75+ nodes.
– 100+ Nodes in Wireless Sensor Grids for Seismic exploration
• Rail and transportation corridors
– Mobility, consistent high performance over many hops
– 60+ Nodes evaluation in progress in Korea
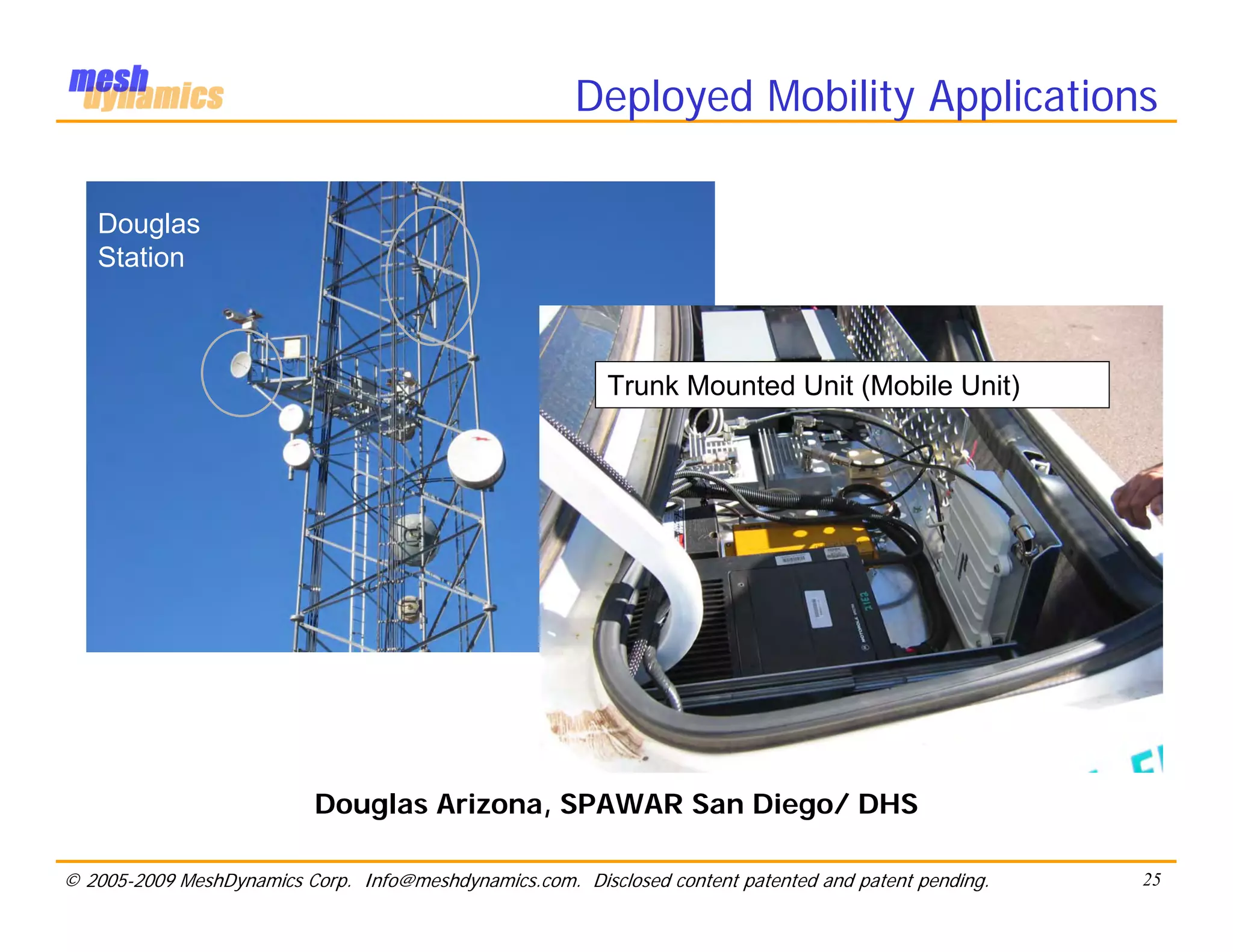
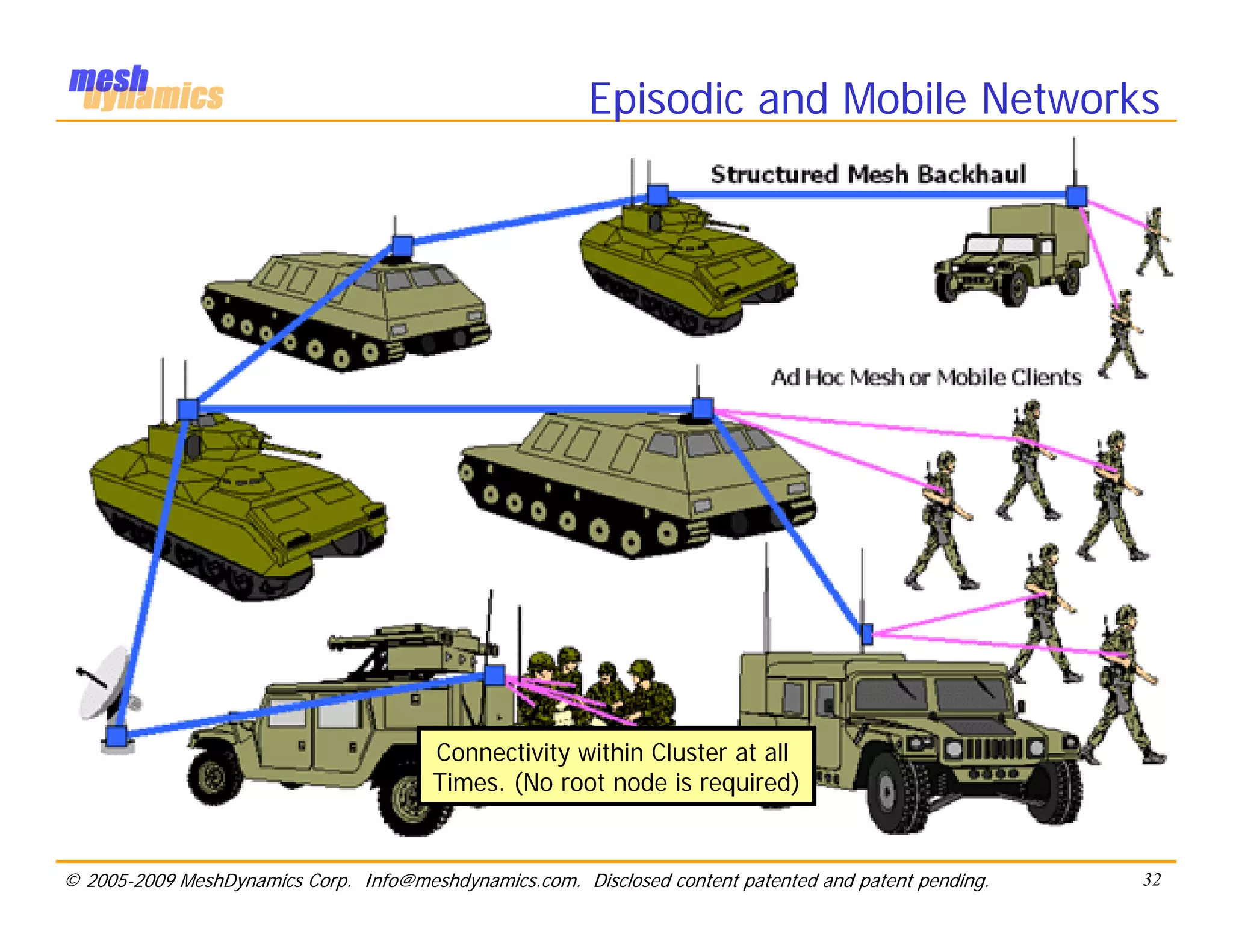
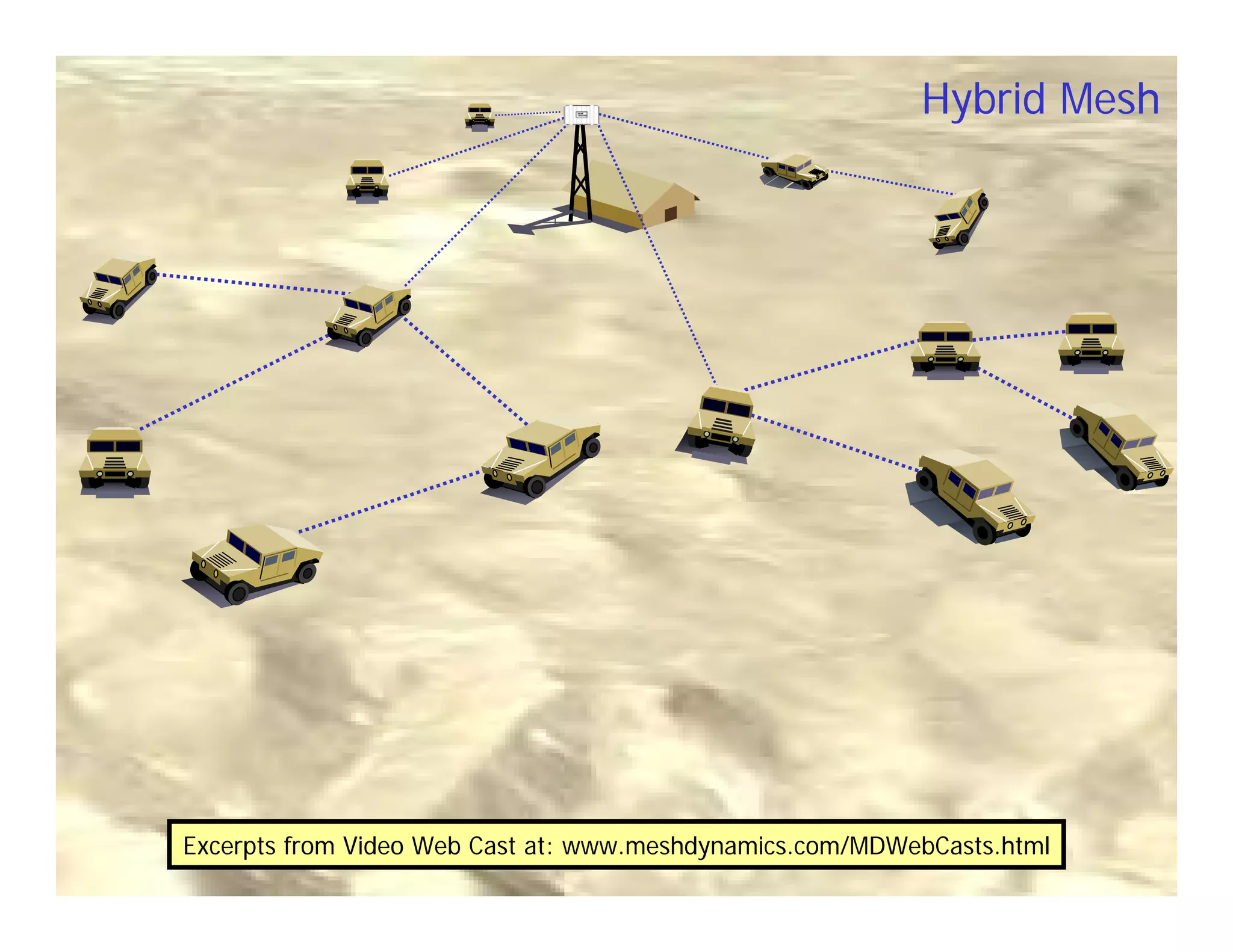
• Military and mobility
– High performance, automated network formation at speed
– 25+ nodes Truck Convoy tested in Iraq, Army bases.
• Border and perimeter security
– High performance for video over many hops, fast set-up
– 25+ nodes deployed along Arizona-Mexico border for DHS
© 2005-2009 MeshDynamics Corp. Info@meshdynamics.com. Disclosed content patented and patent pending. 4](https://image.slidesharecdn.com/mdtechoverview-130126052609-phpapp01/75/MeshDynamics-MD4000-Product-Overview-4-2048.jpg)