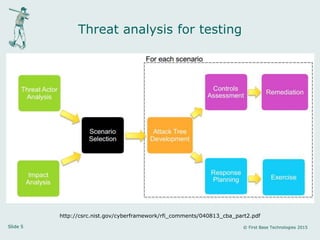
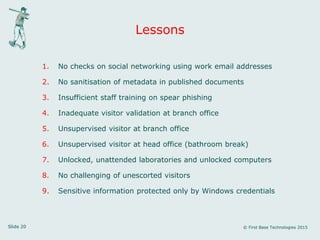
Peter Wood is the CEO of First Base Technologies LLP and has extensive experience in engineering, IT, information security, and cybersecurity. He gave a presentation summarizing a simulated criminal attack or "red team exercise" that his company conducted. The summary included gathering information online and on-site, conducting a successful spear phishing attack, gaining unauthorized access to an office network by posing as a contractor, and accessing unattended computers at a company headquarters by posing as press. The presentation concluded by identifying nine lessons learned from the exercise, including issues with social media checks, document metadata, staff training, visitor validation, and computer security practices.