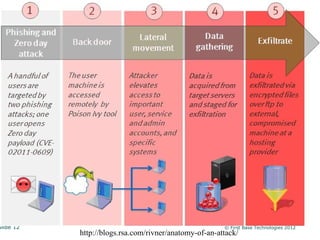
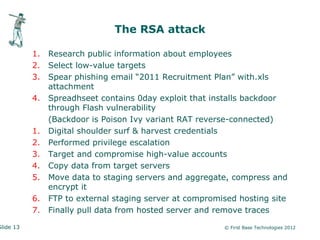
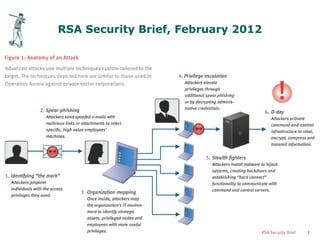
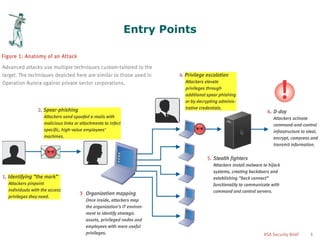
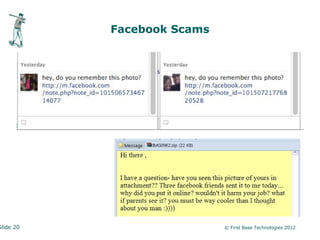
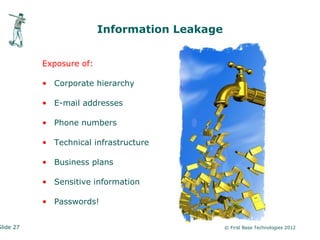
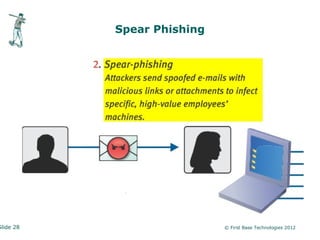
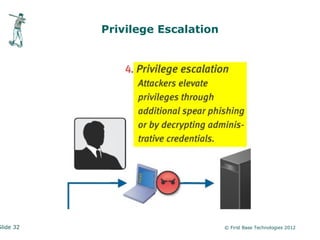
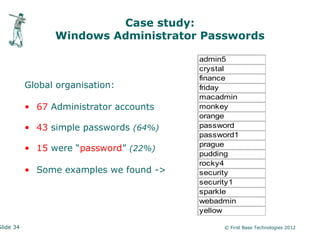
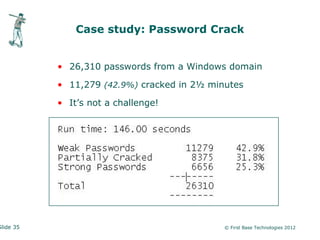
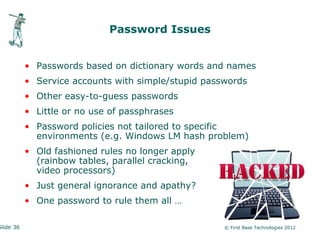
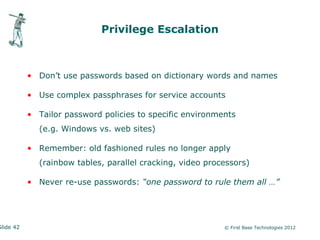
The document, presented by Peter Wood, focuses on advanced persistent threats (APTs) and their implications for security intelligence. It discusses the evolution of sophisticated adversaries, case studies, entry points for attacks, and prevention strategies, highlighting the importance of understanding one's threat landscape. Key takeaways emphasize the need for tailored security policies, awareness of social engineering tactics, and the necessity for strong, complex passwords.
![Advanced Persistent Threat (APT)
• “An advanced and normally clandestine means to gain
continual, persistent intelligence on an individual, or group of
individuals” [Wikipedia]
• “… a sophisticated, mercurial way that advanced attackers can
break into systems, not get caught, keeping long-term access
to exfiltrate data at will.” [McAfee]
• “… a sophisticated and organized cyber attack to access and
steal information from compromised computers.” [MANDIANT]
Slide 6 © First Base Technologies 2012](https://image.slidesharecdn.com/secintel-apt-pw-120808062916-phpapp02/85/Security-Intelligence-Advanced-Persistent-Threats-6-320.jpg)





![Think Like an Attacker!
Hacking is a way of thinking:
- A hacker is someone who thinks outside the box
- It's someone who discards conventional wisdom, and does
something else instead
- It's someone who looks at the edge and wonders what's
beyond
- It's someone who sees a set of rules and wonders what
happens if you don't follow them
[Bruce Schneier]
Hacking applies to all aspects of life - not just computers
Slide 43 © First Base Technologies 2012](https://image.slidesharecdn.com/secintel-apt-pw-120808062916-phpapp02/85/Security-Intelligence-Advanced-Persistent-Threats-43-320.jpg)