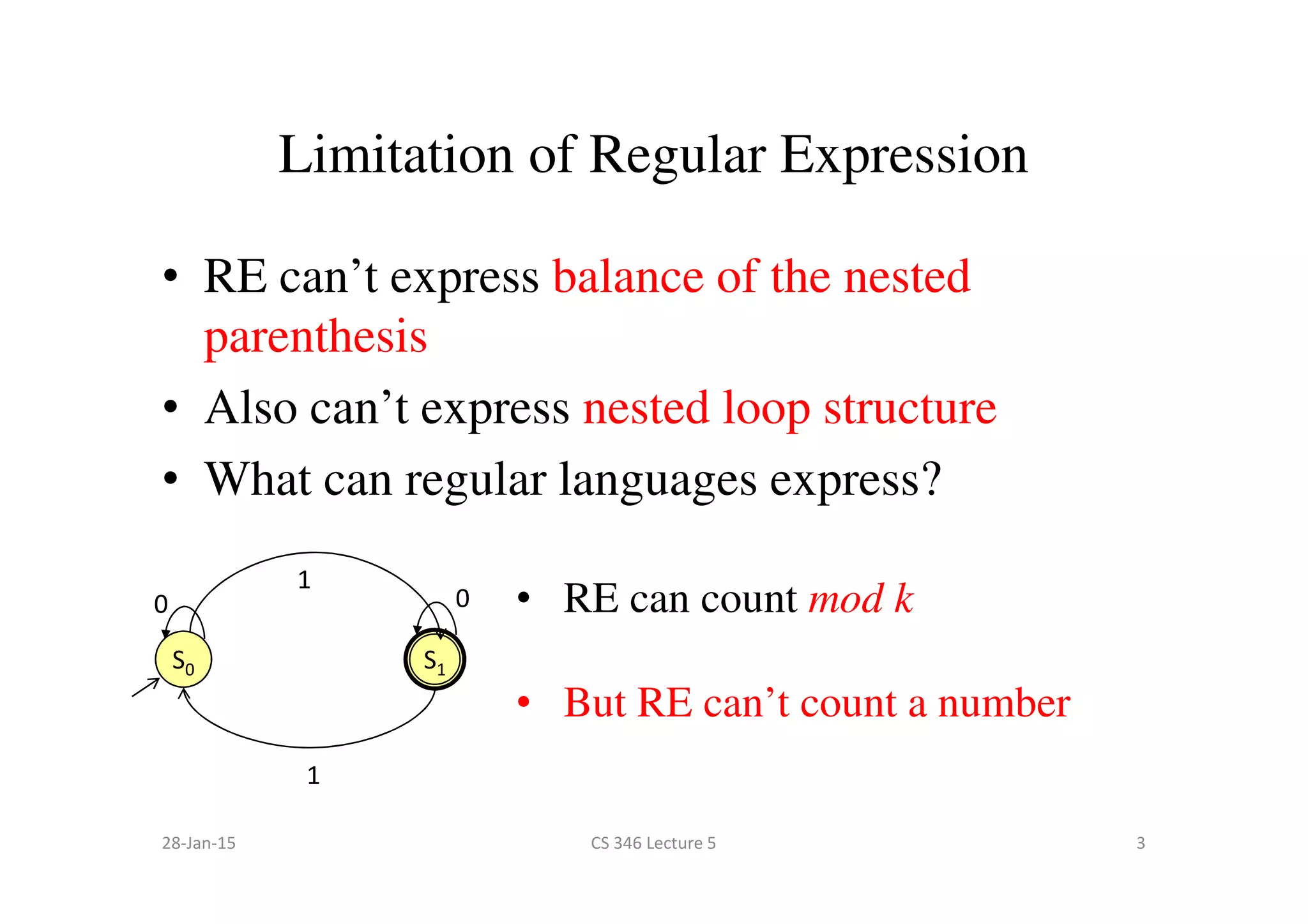
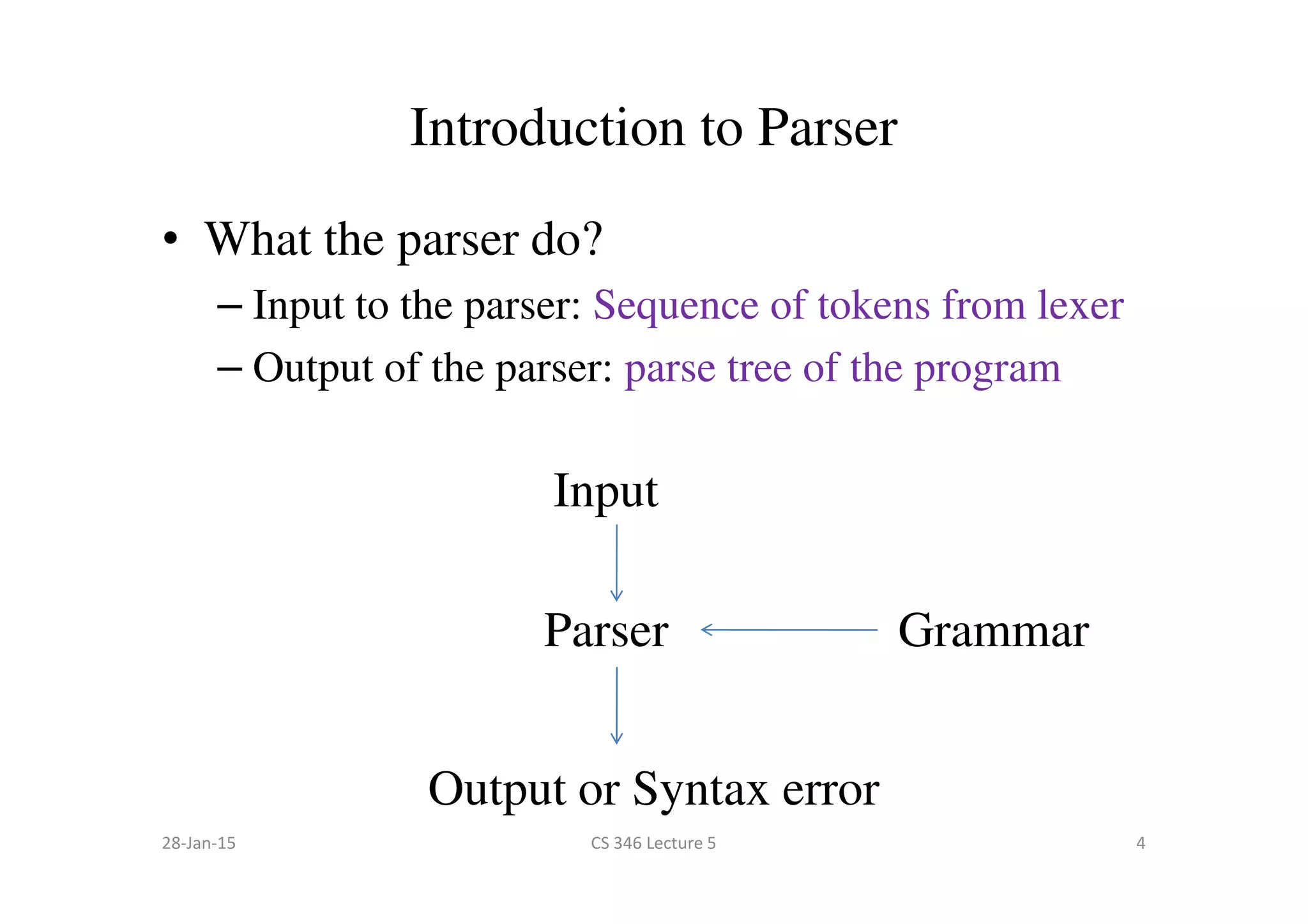
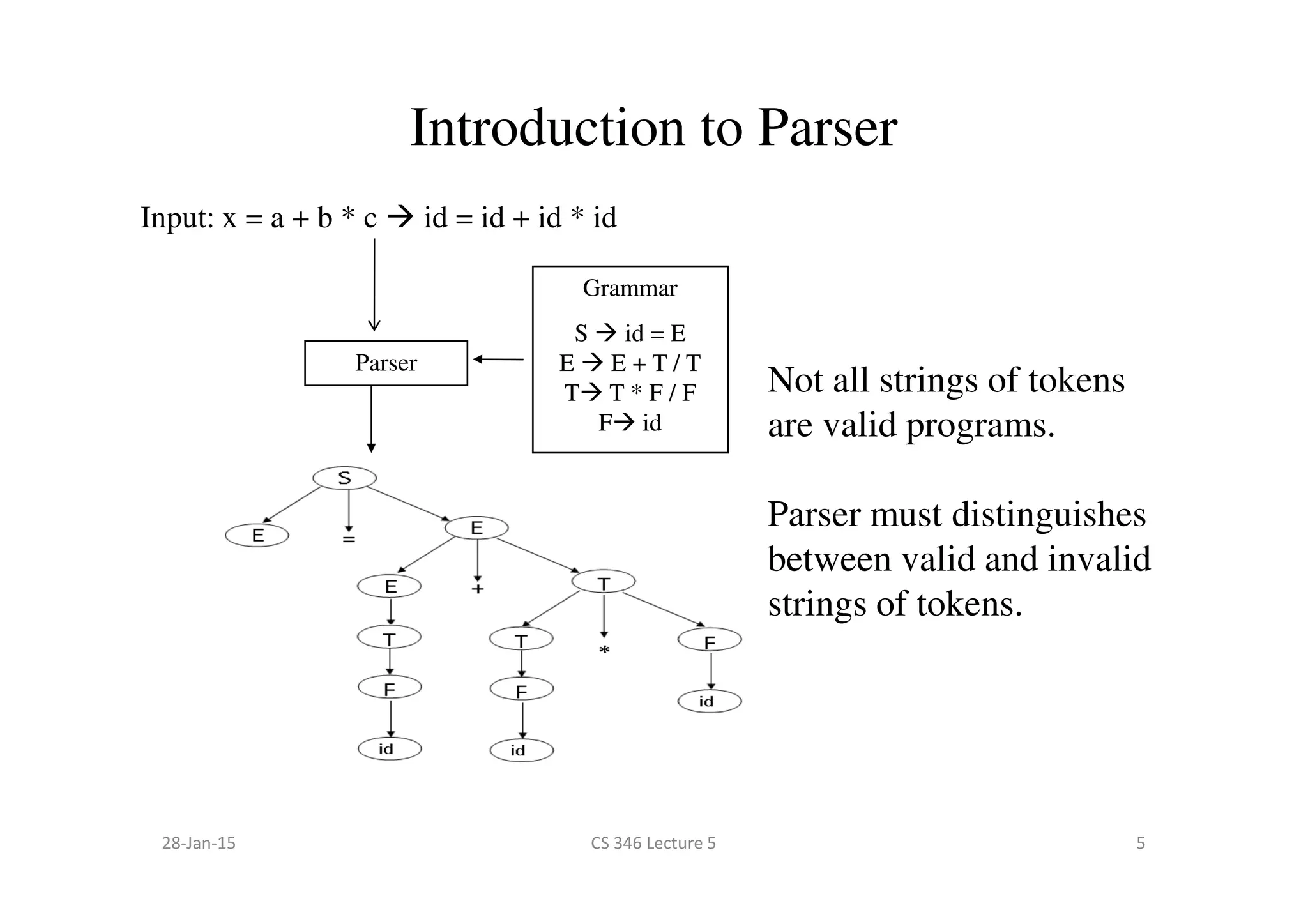
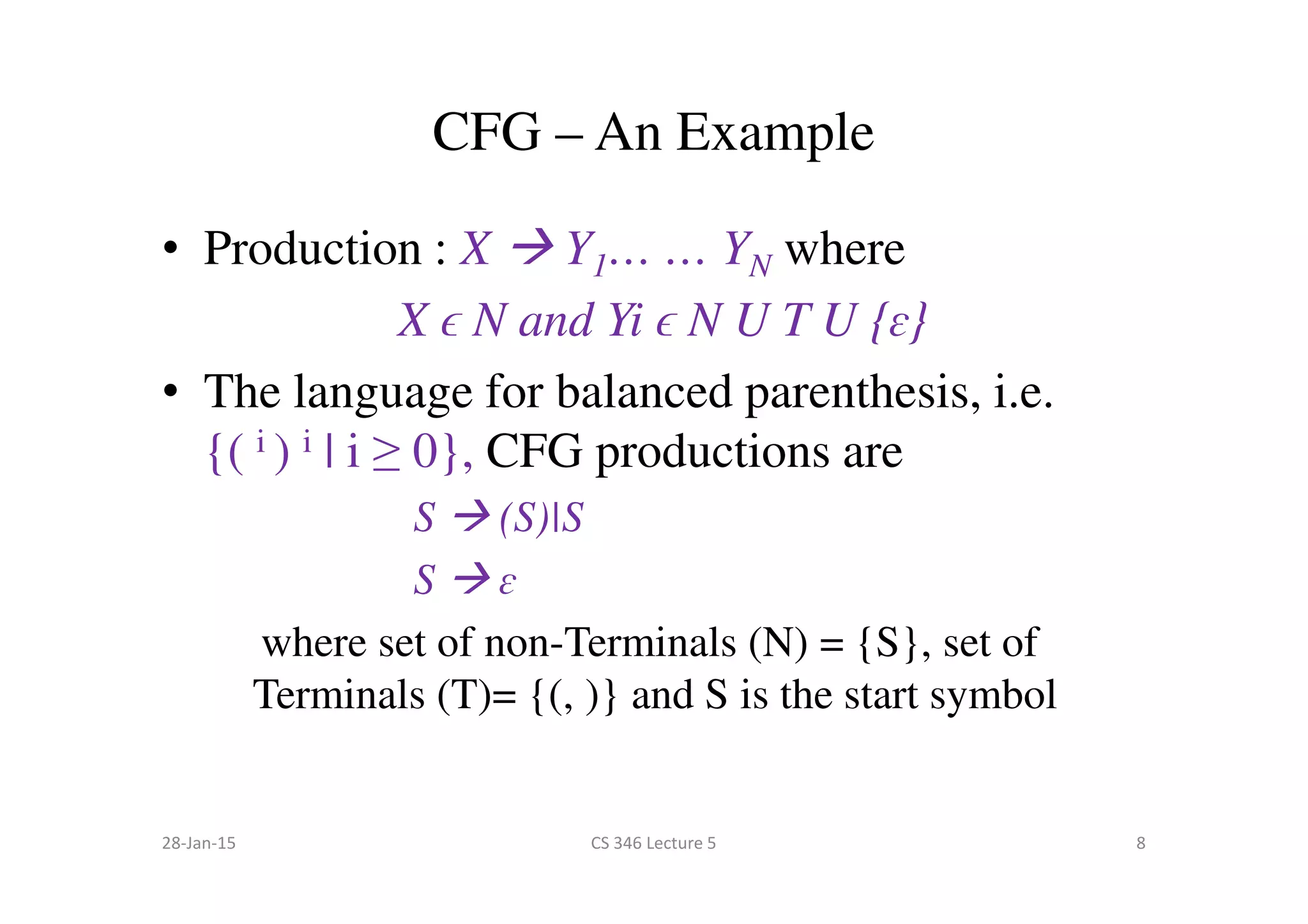
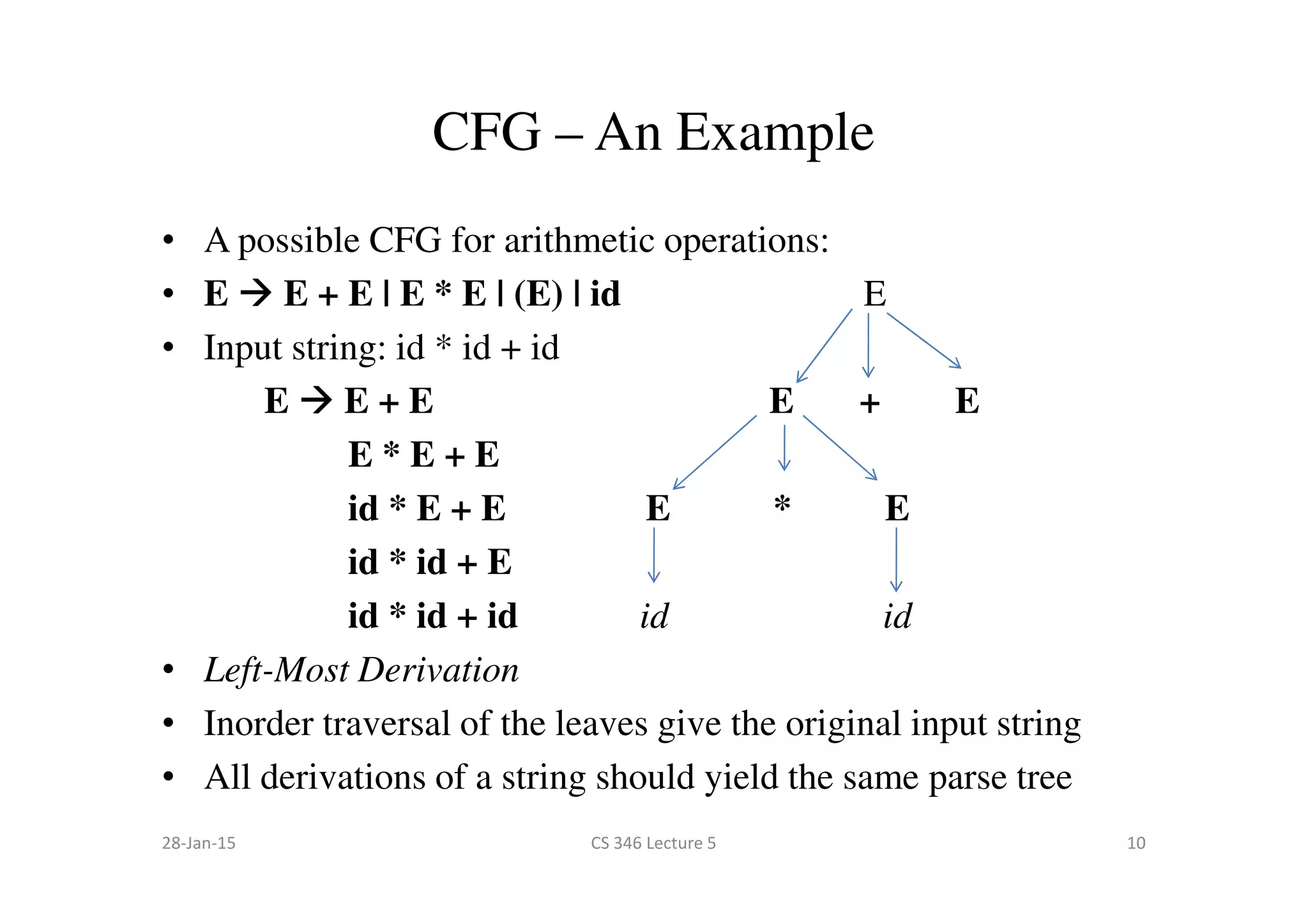
This document discusses context-free grammars and parsing. It introduces regular languages and their limitations, such as not being able to express balanced parentheses. A context-free grammar is then presented as a formal way to describe the valid strings of a language using terminals, non-terminals, productions, and a start symbol. An example grammar for balanced parentheses is given. The role of a parser to take tokens as input and output a parse tree or syntax error based on a grammar is described.