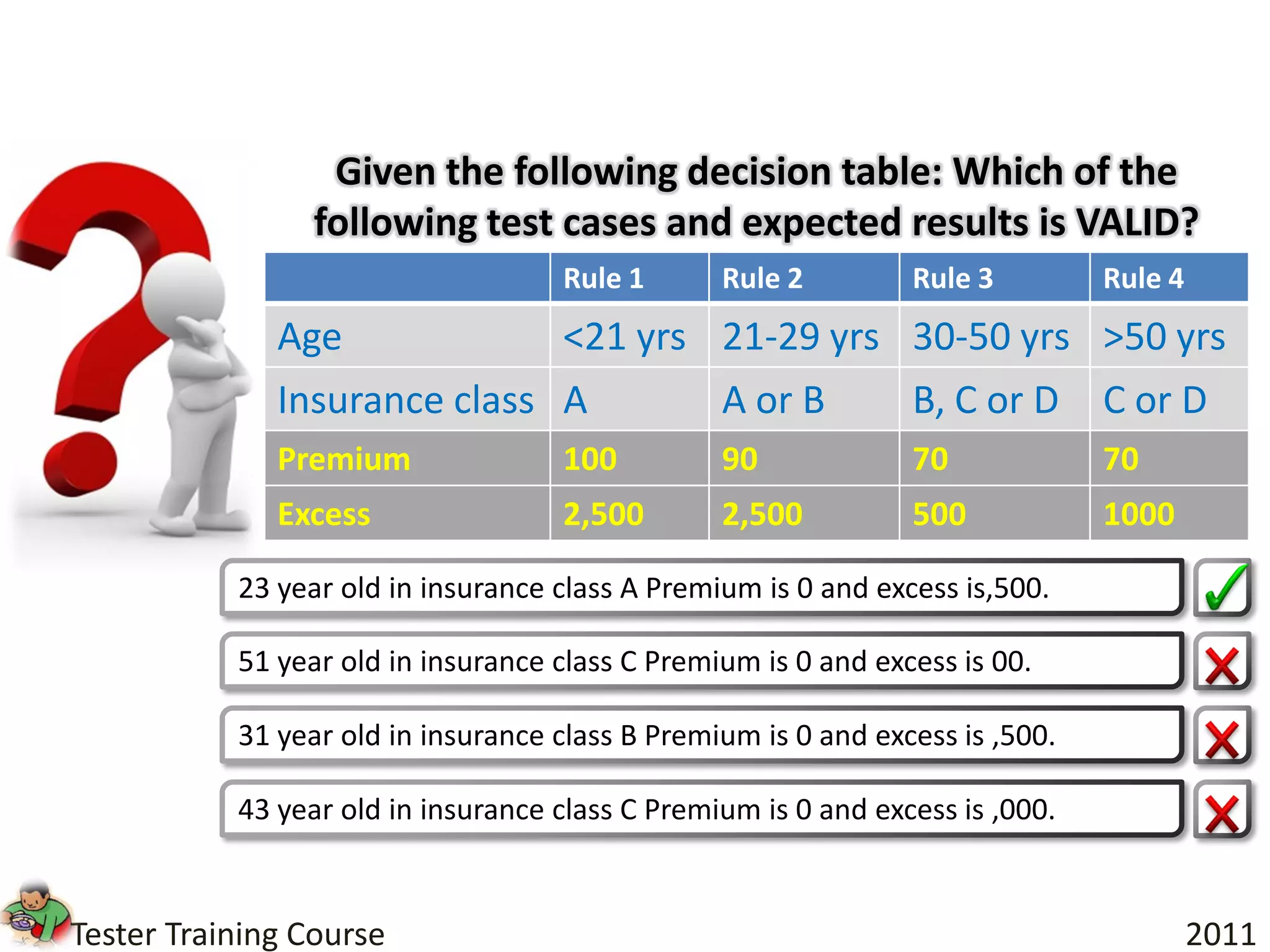
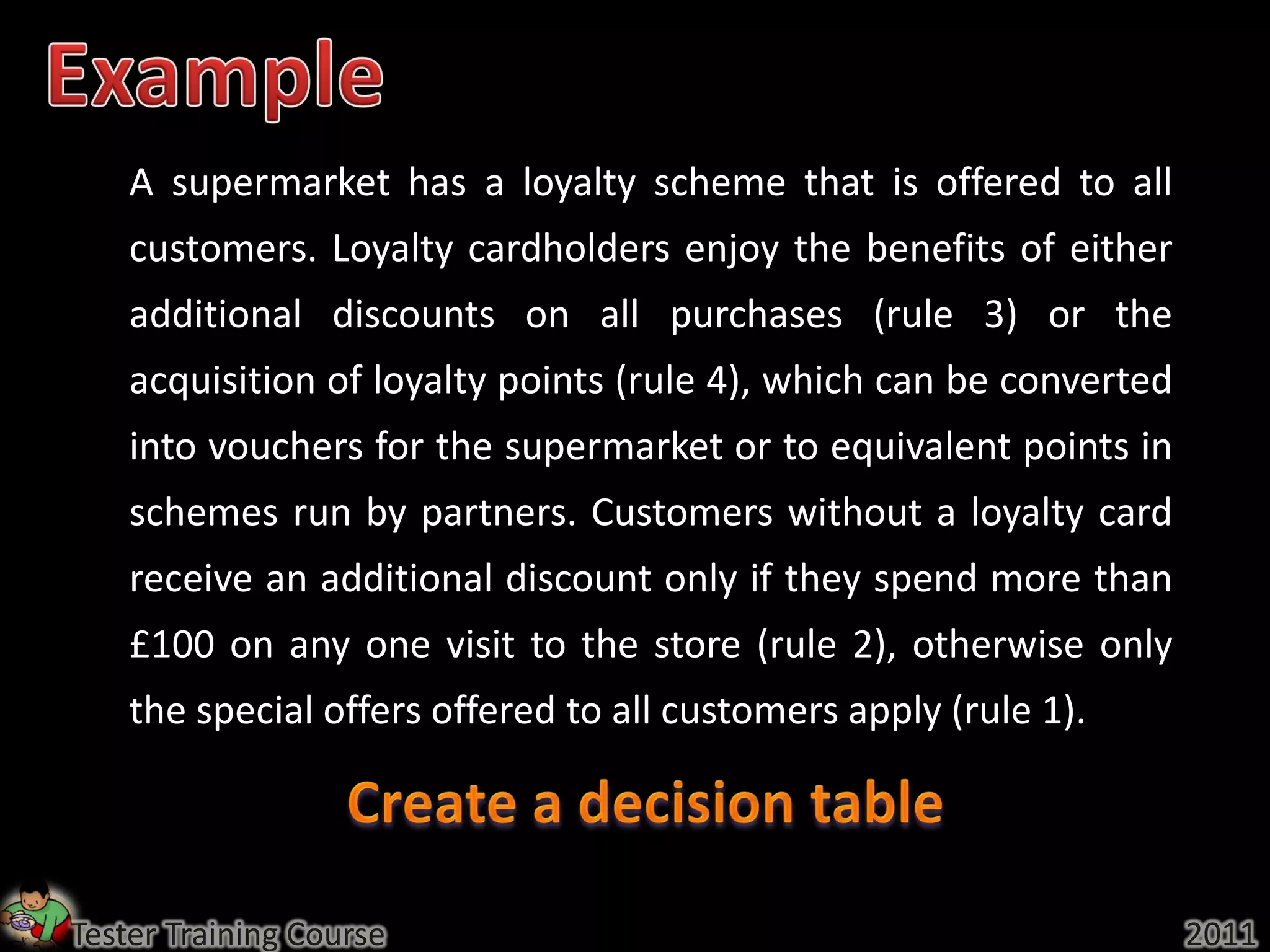
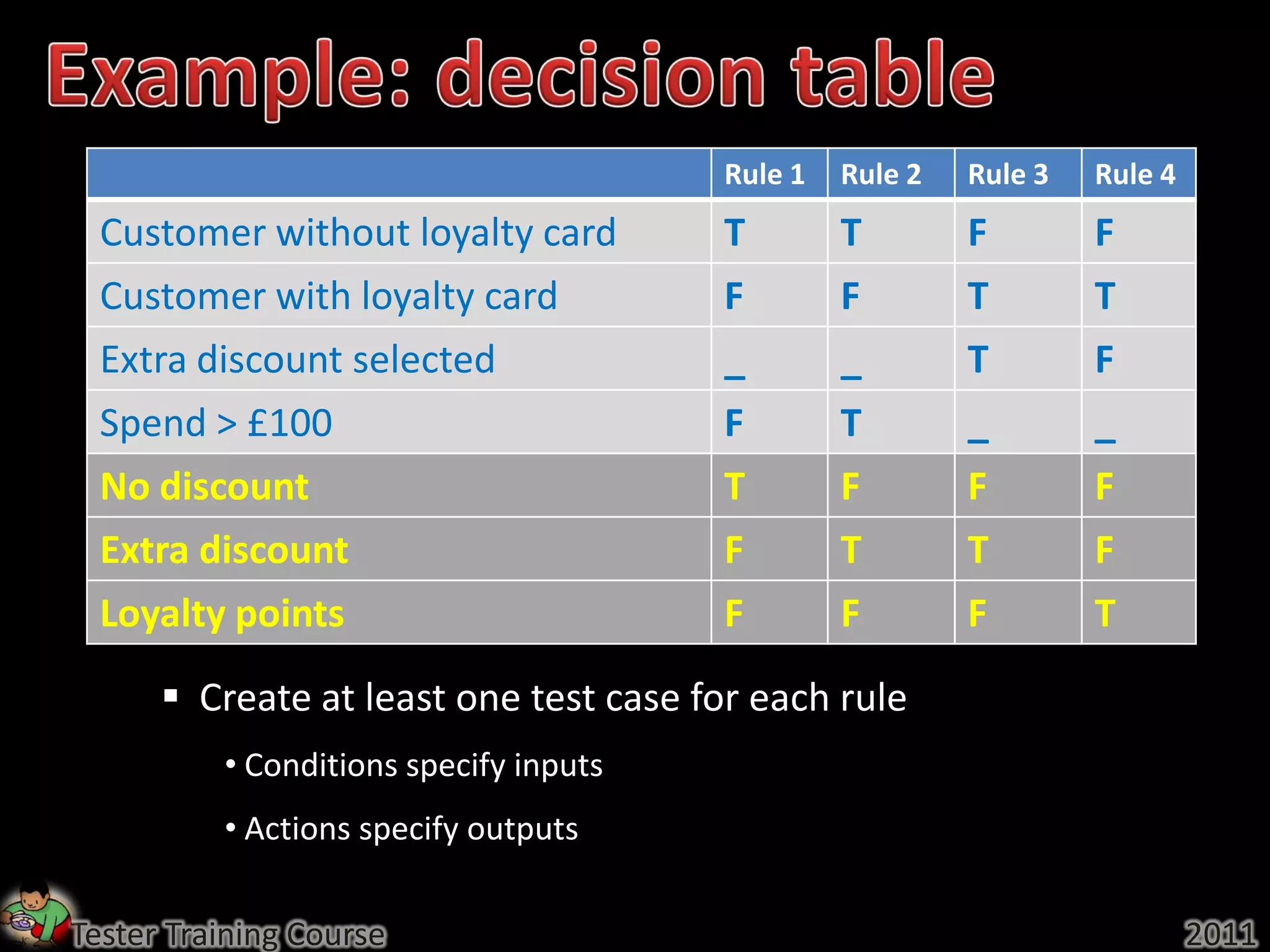
Here are the rules for the supermarket loyalty scheme:
Rule 1: All customers are eligible for a loyalty card.
Rule 2: Loyalty cardholders get either additional discounts on all purchases or earn loyalty points.
Rule 3: Additional discounts are offered on all purchases to loyalty cardholders.
Rule 4: Loyalty cardholders can earn points which can be converted to vouchers or points with partner schemes.
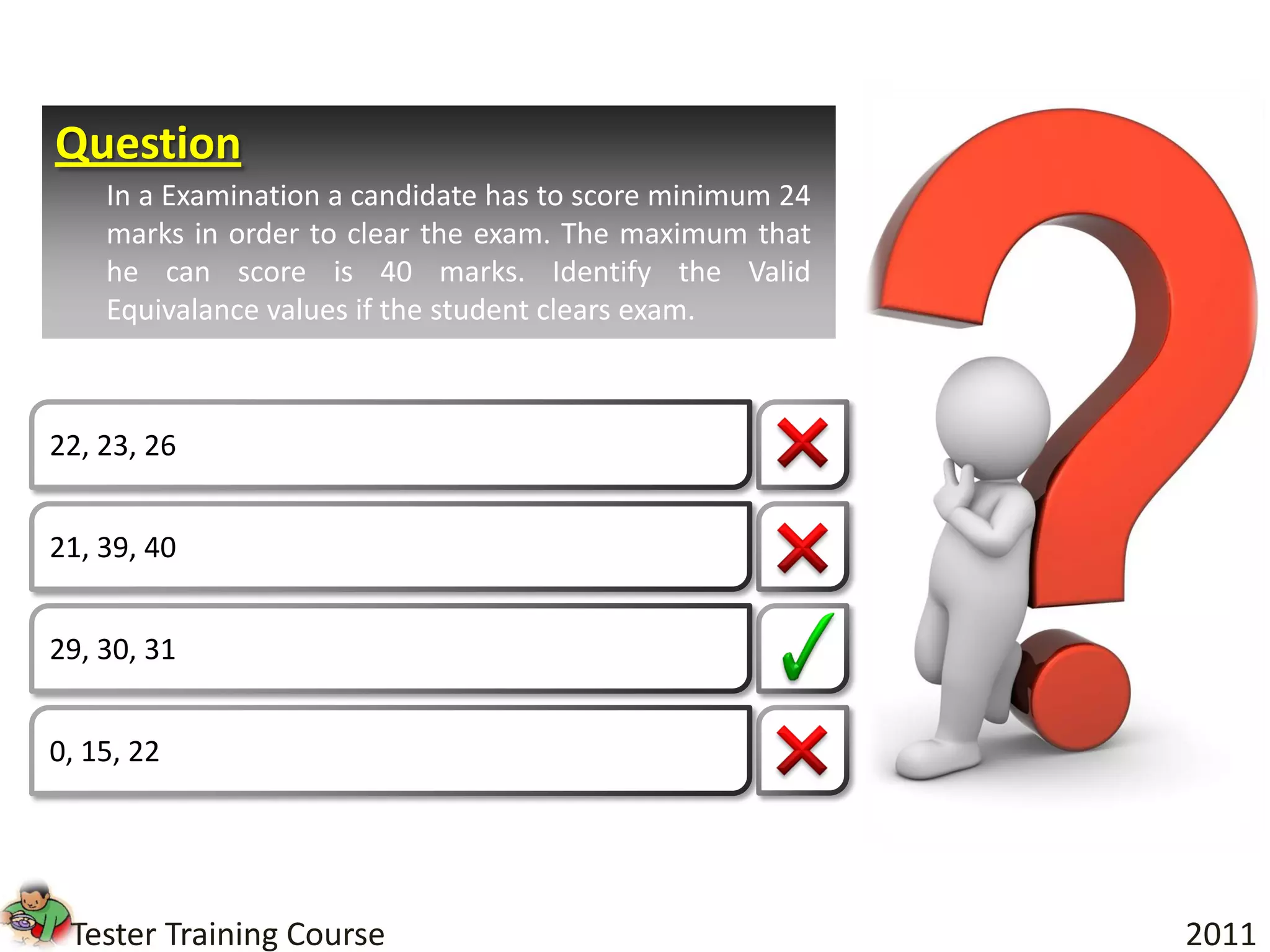
Given:
- Customer has a loyalty card
- Made a purchase of £50
Test case: Loyalty cardholder who made a £50 purchase earns 50 loyalty points
Expected result: Valid (matches Rule 4)