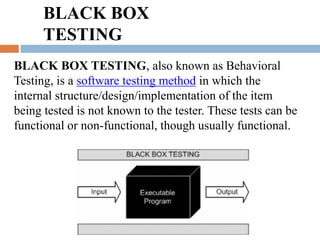
This document provides information about software testing. It discusses different types of software testing like unit testing, black box testing, and white box testing. It also describes various techniques used for testing like equivalence partitioning, boundary value analysis, and cause-effect graphing. The key objectives of testing are to discover faults and ensure software works as intended by identifying differences between expected and actual results.


























![Example 1 for Boundary Value Analysis :
Password field accepts minimum 6 characters and maximum 12 characters. [Range
is 6-12]
Write Test Cases considering values from Valid region and each Invalid Region
and Values which define exact boundary.
We need to execute 5 Test Cases for our Example 1.
1. Consider password length less than 6
2. Consider password of length exactly 6
3. Consider password of length between 7 and 11
4. Consider password of length exactly 12
5. Consider password of length more than 12
Note : 1st and 5th Test Cases are considered for Negative Testing](https://image.slidesharecdn.com/unittesting-200310061858/85/Unit-testing-33-320.jpg)