Embed presentation
Downloaded 408 times
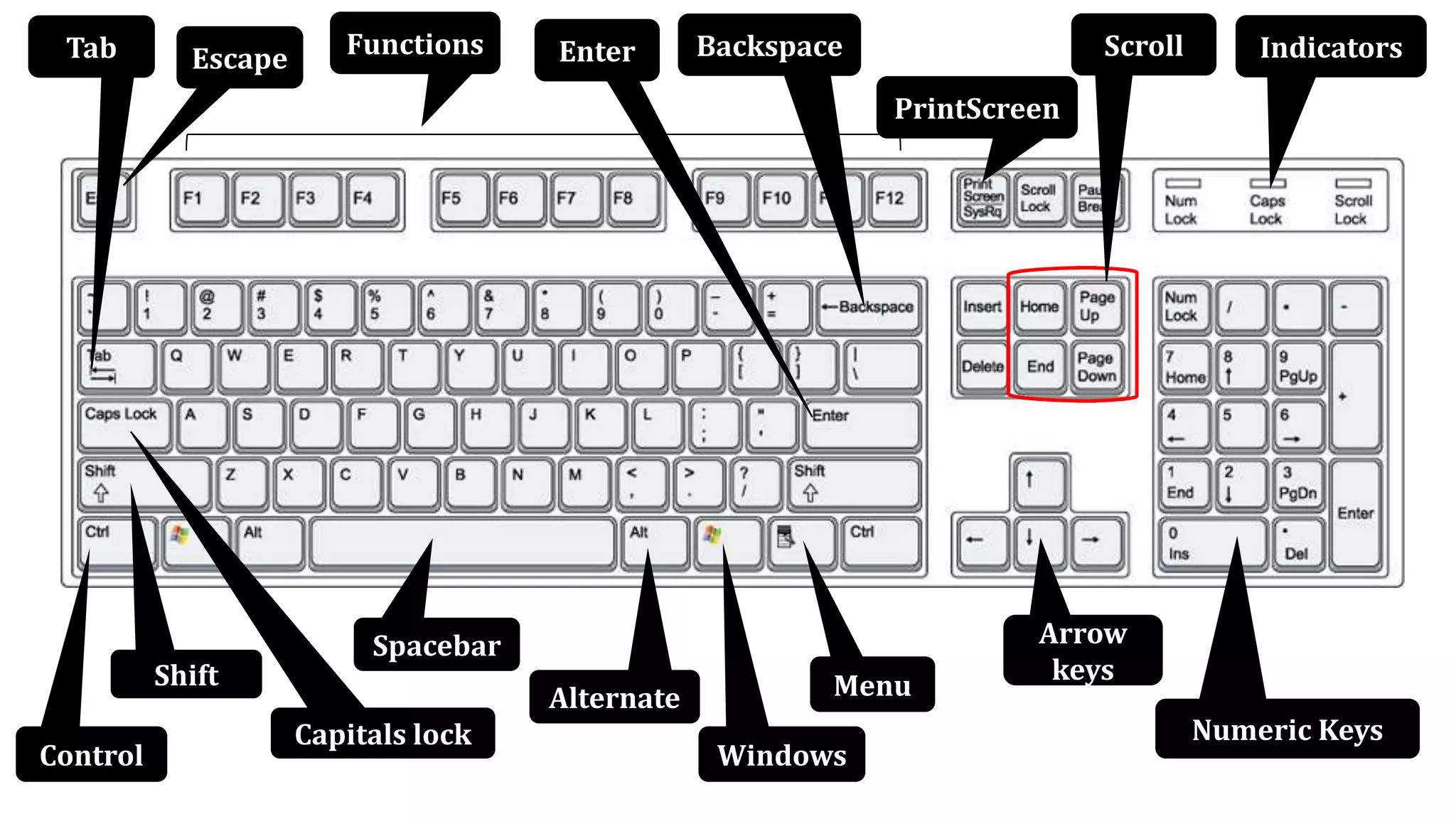
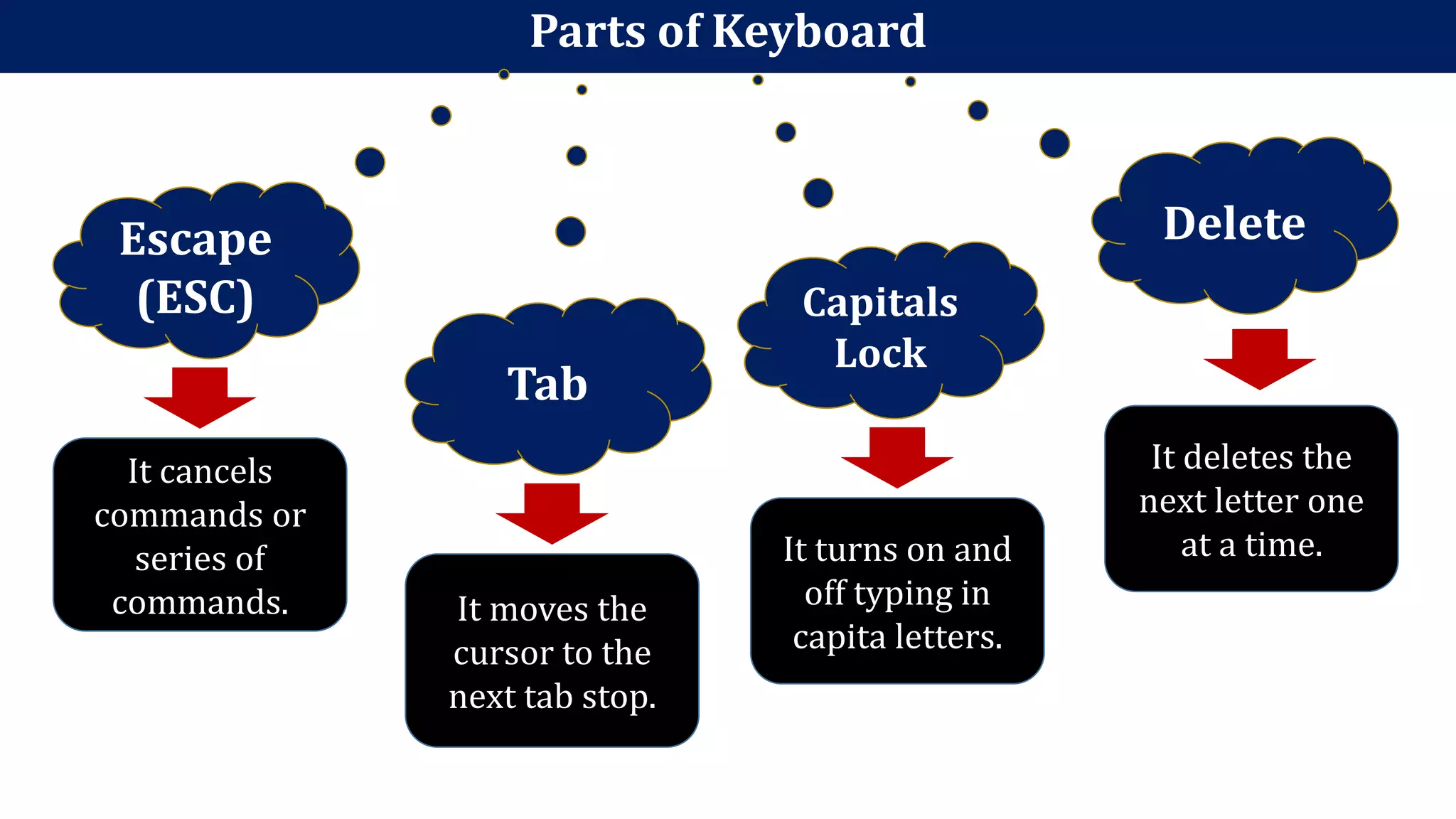
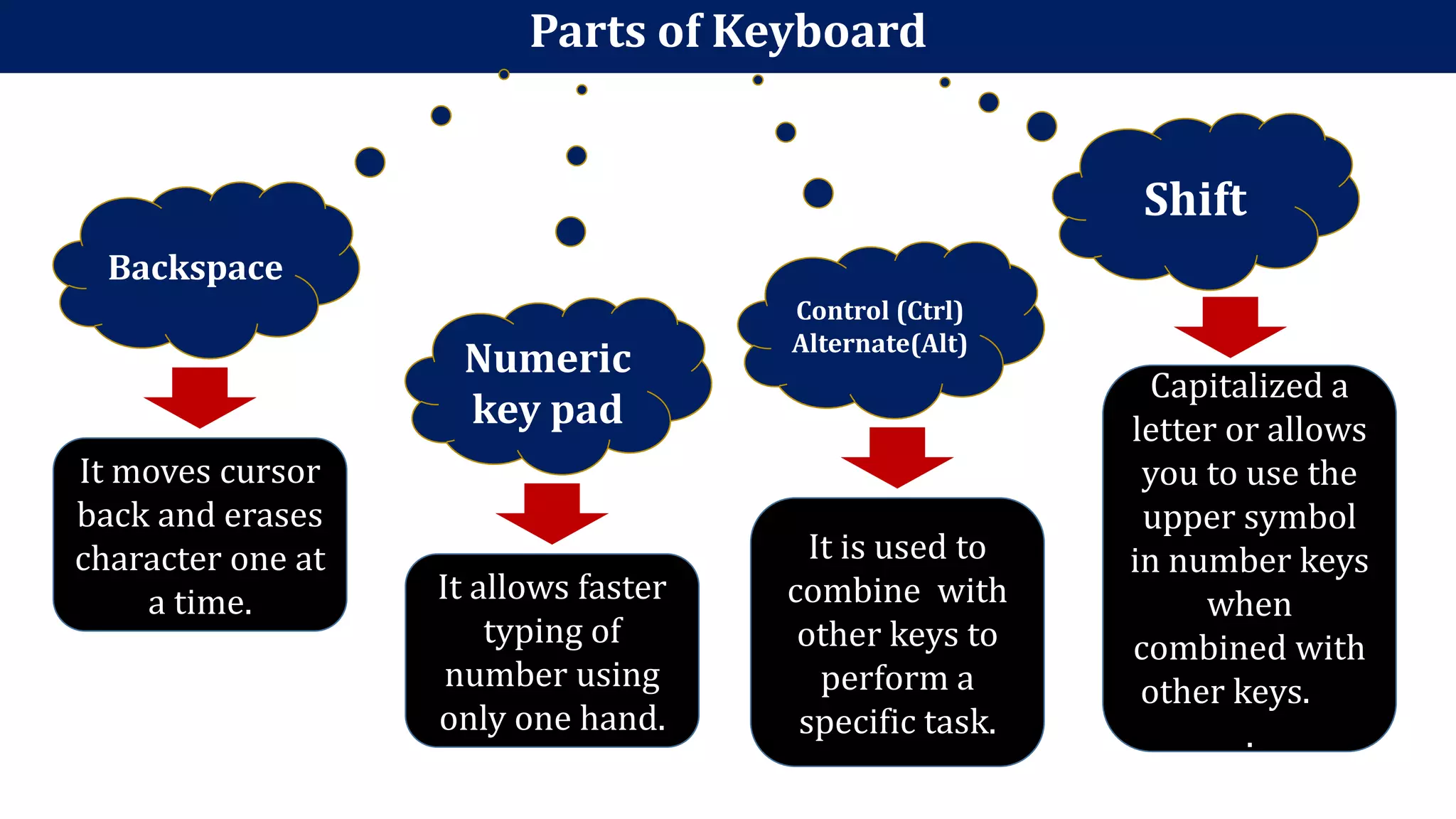
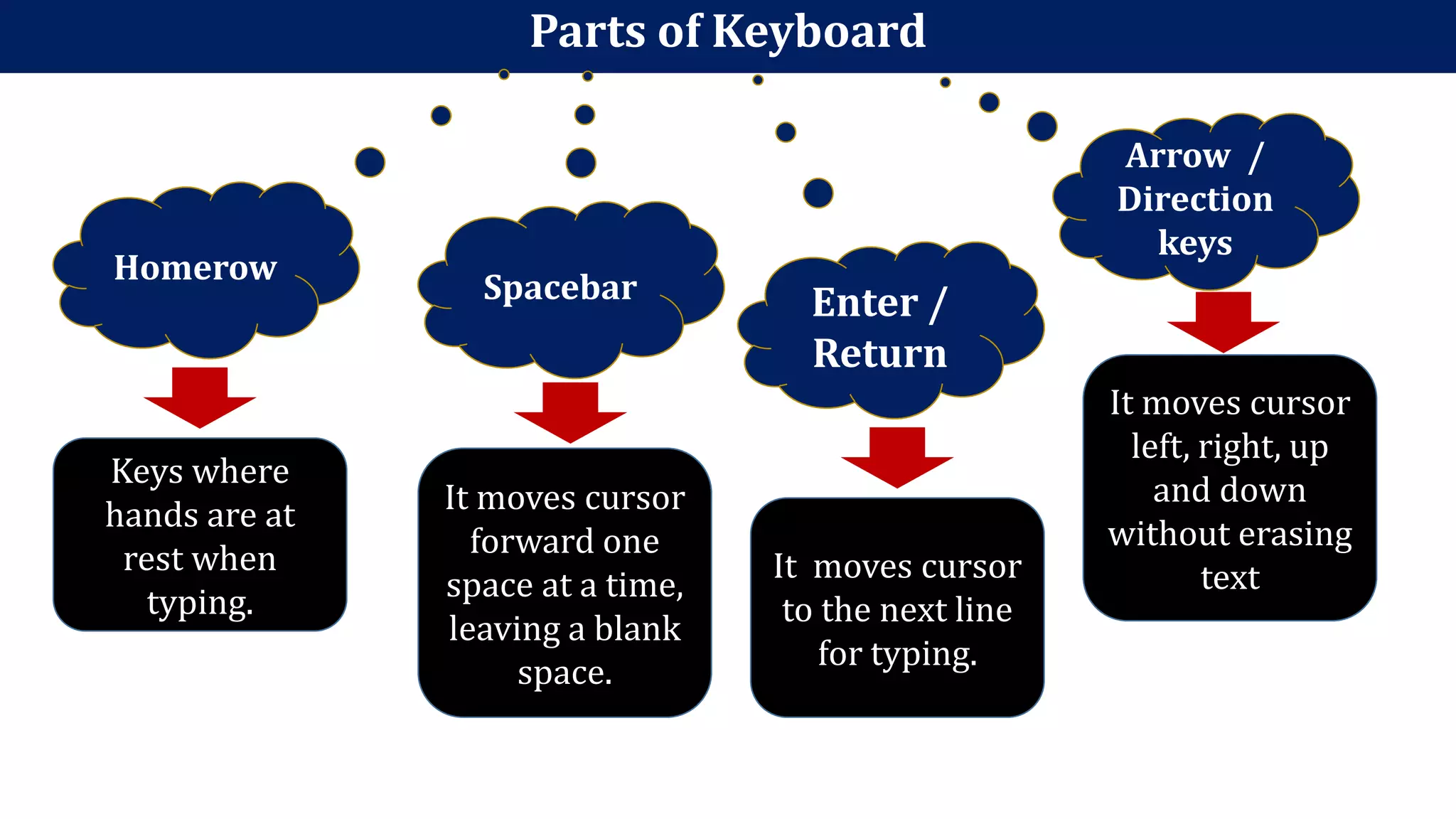
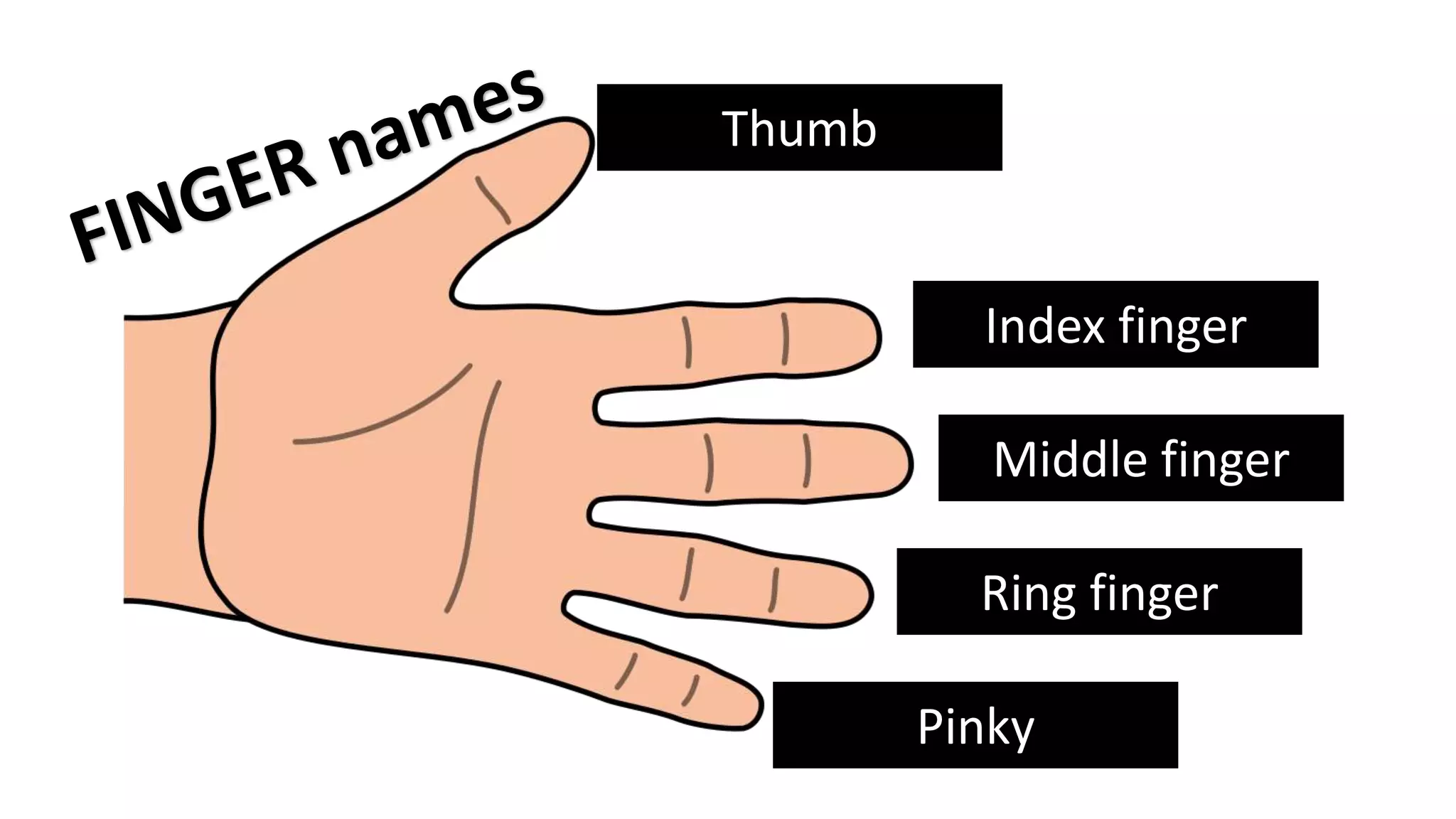
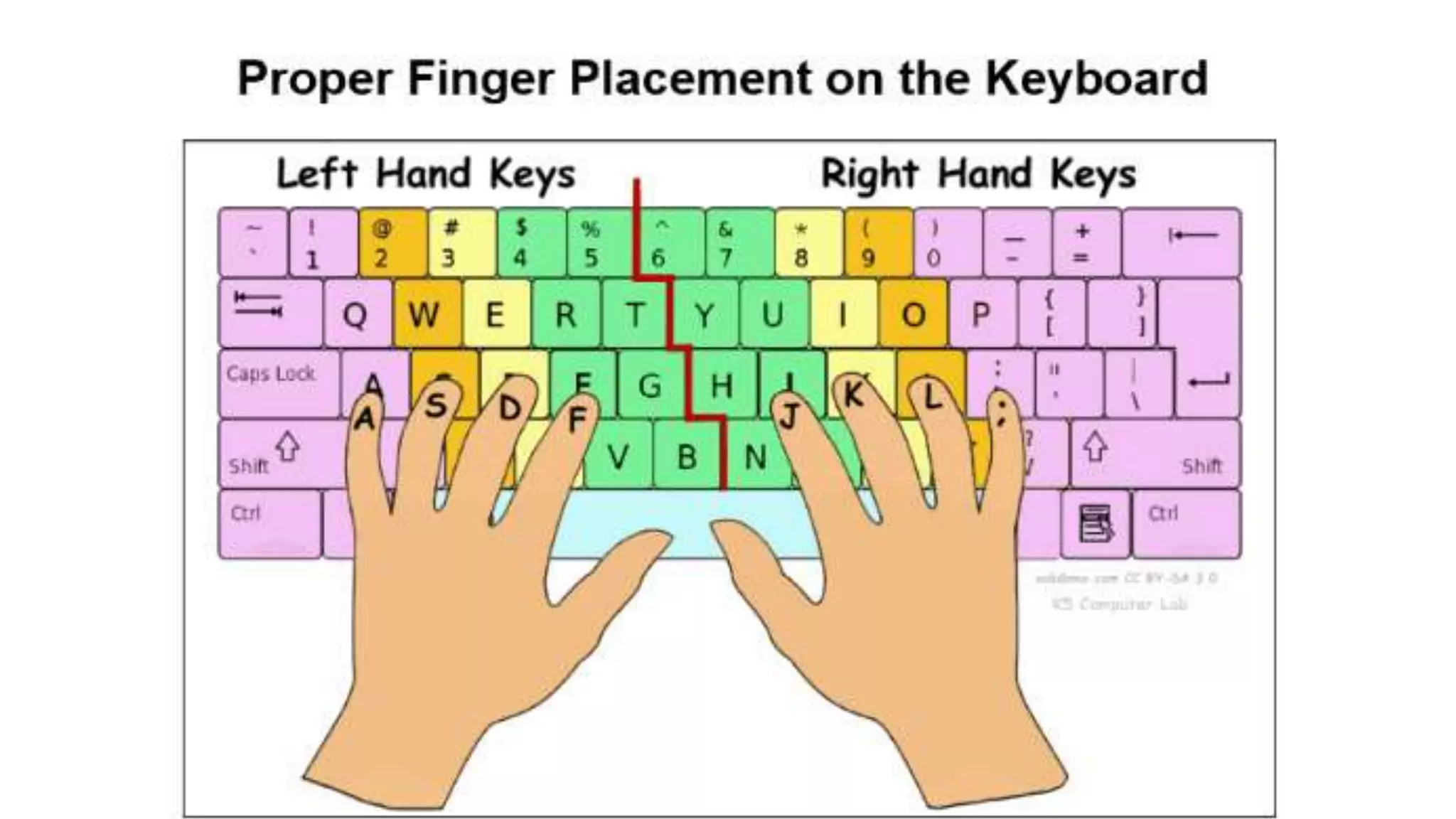
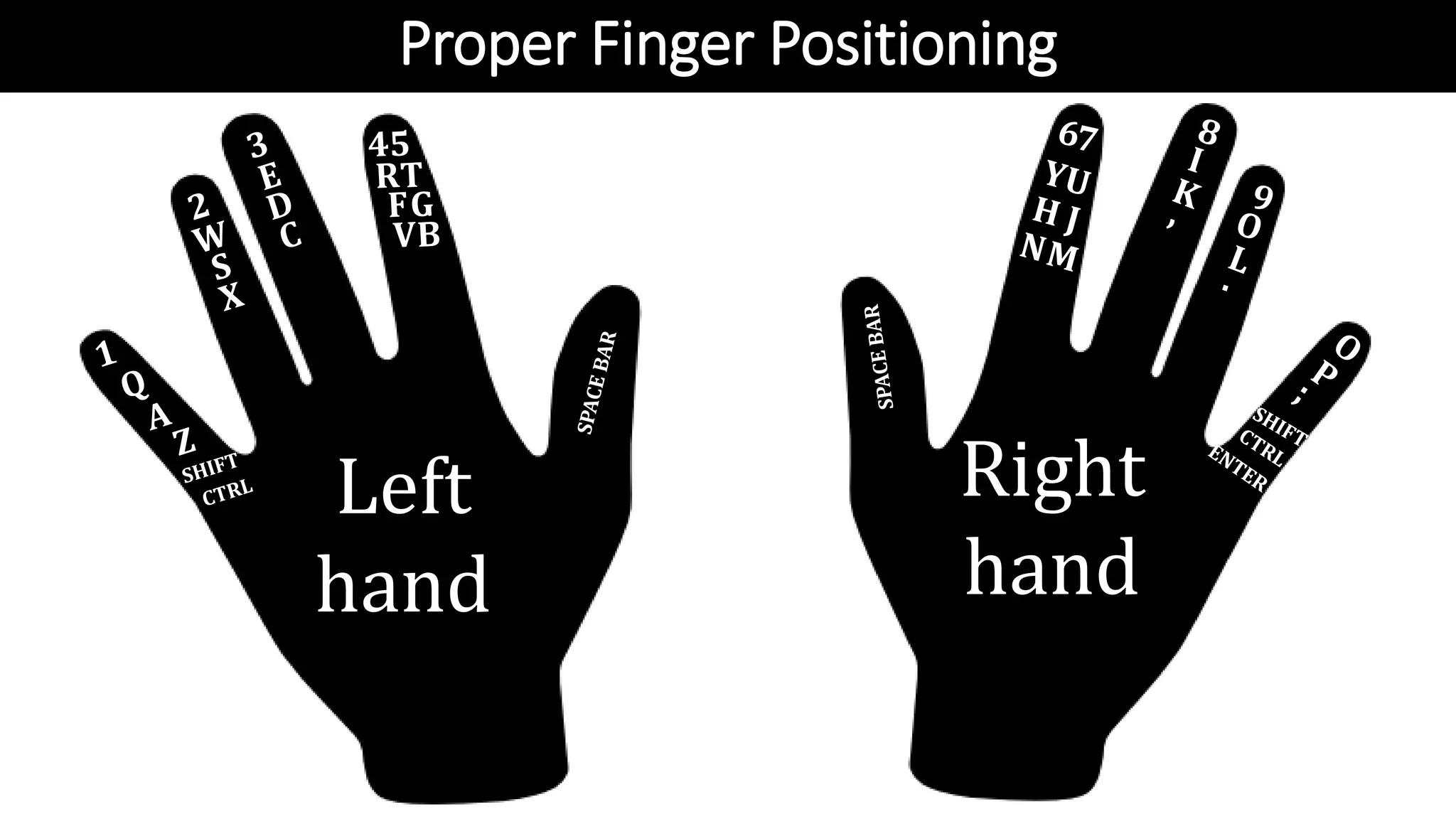
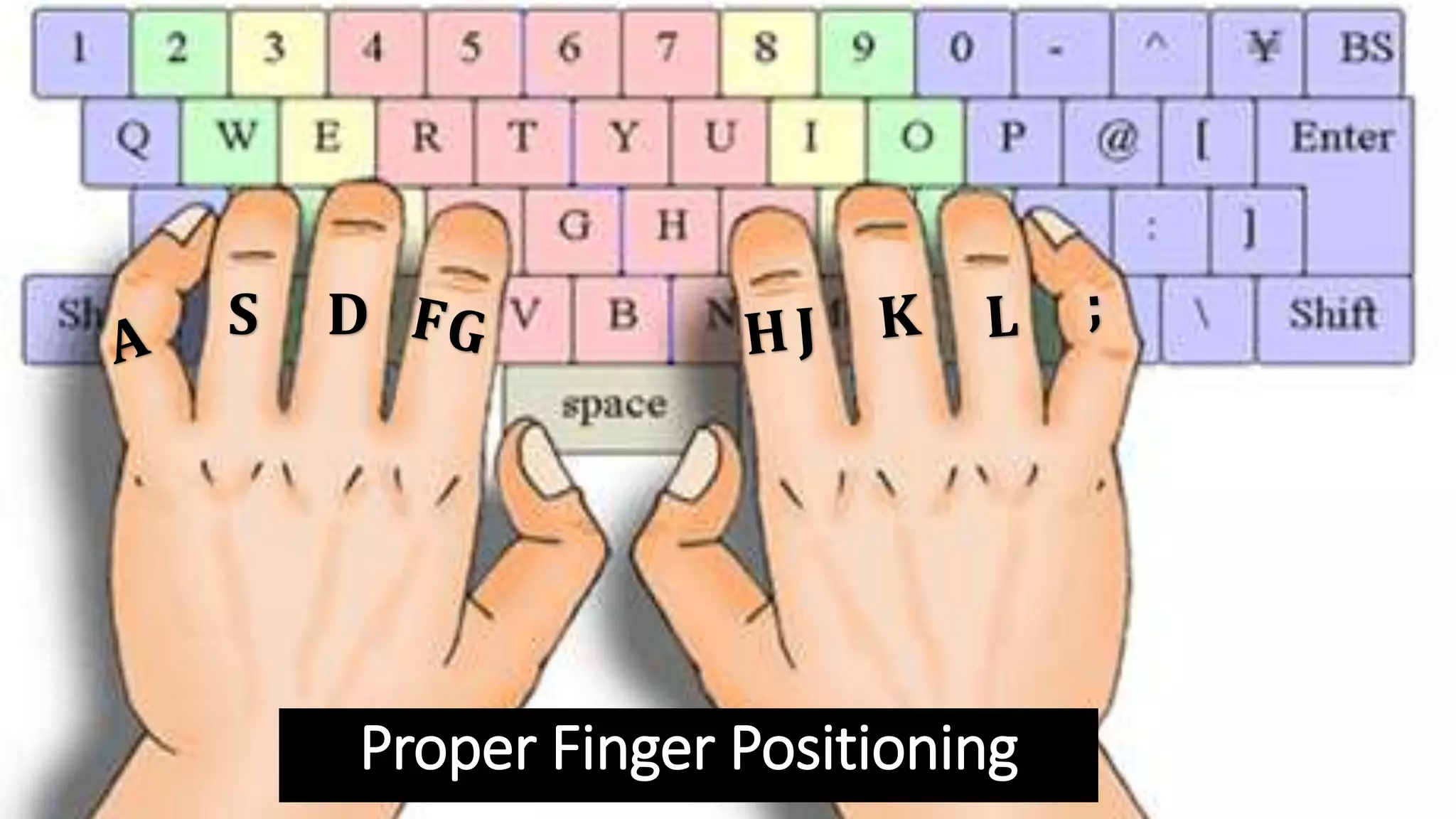
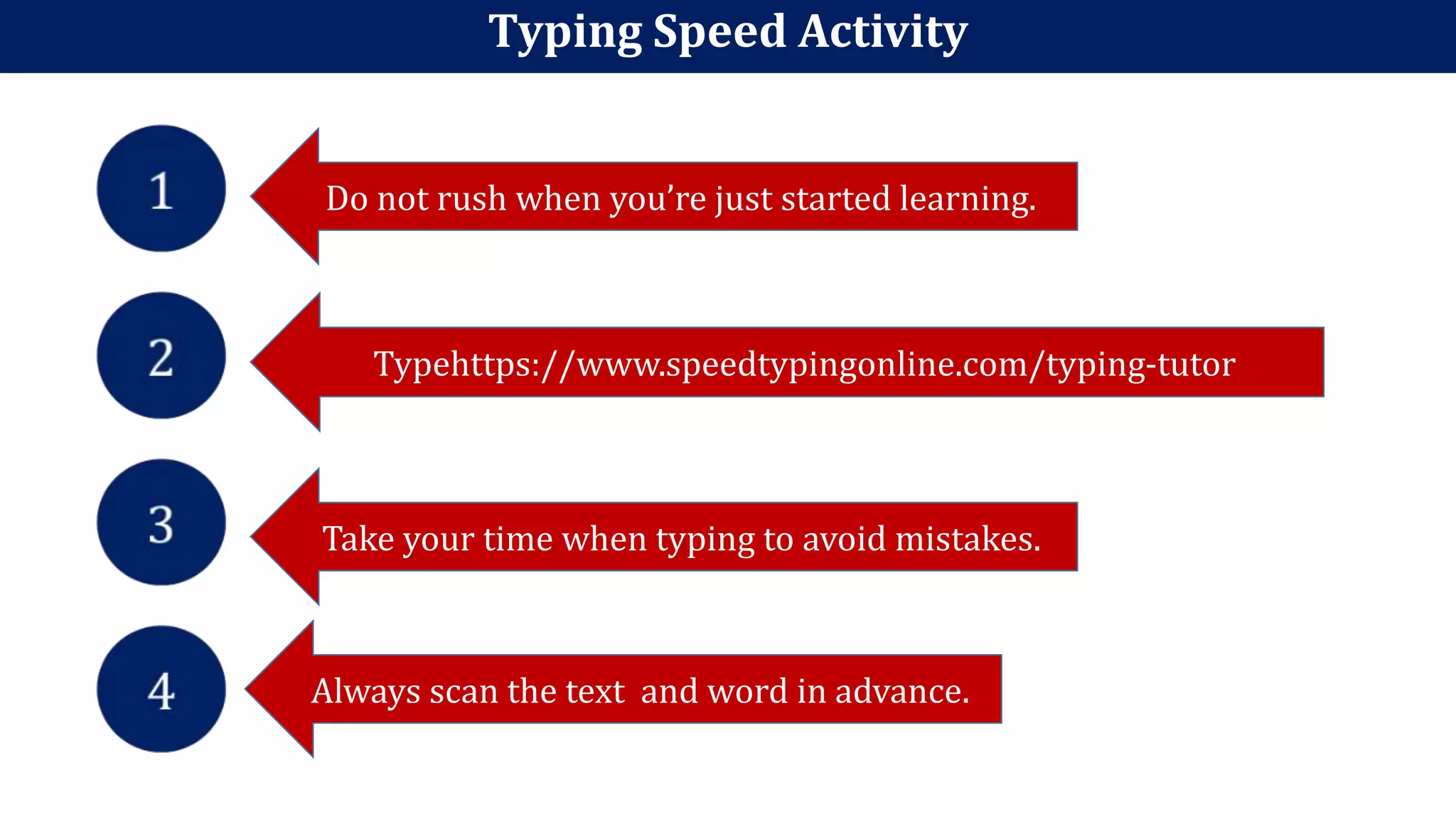
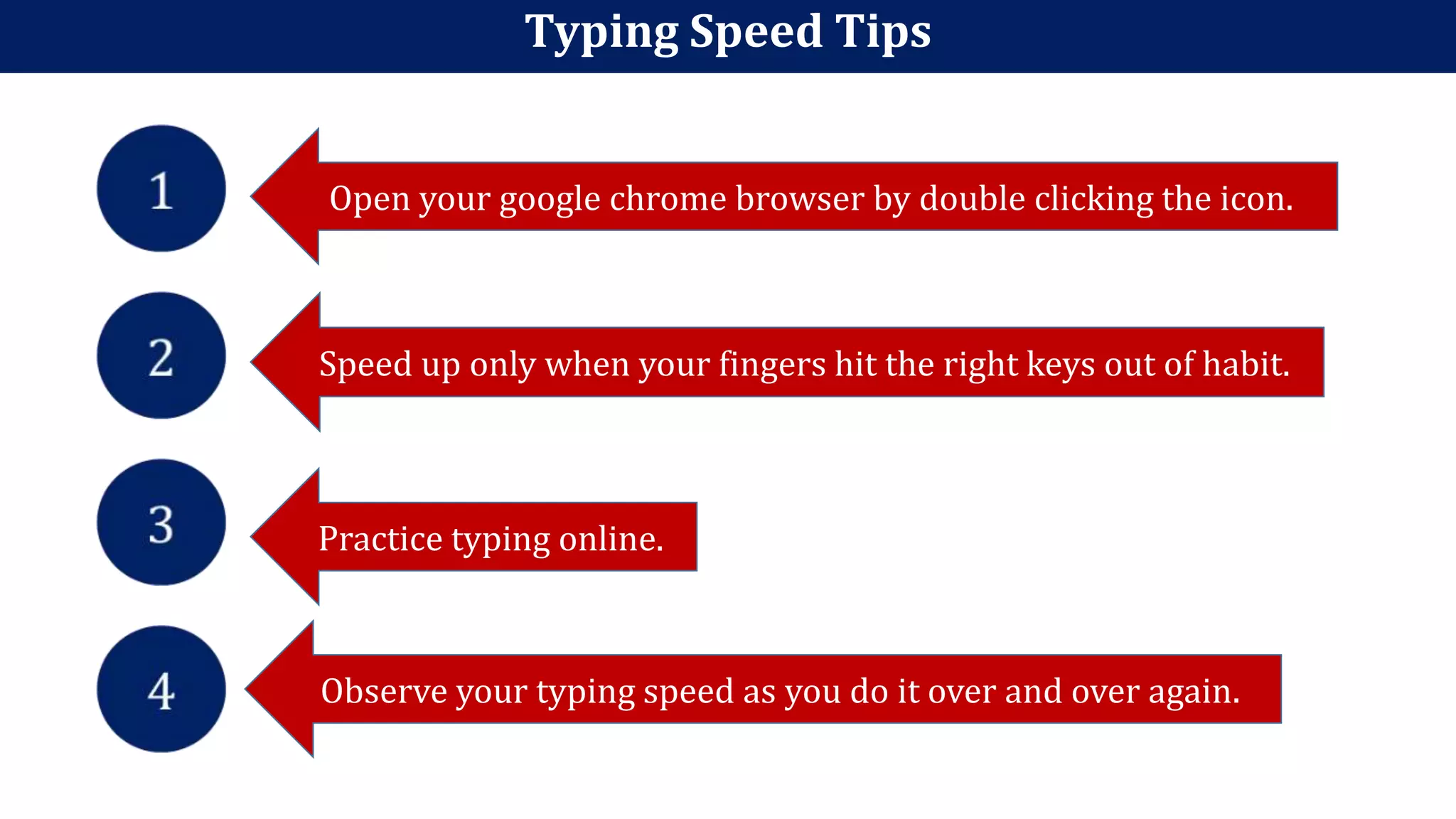

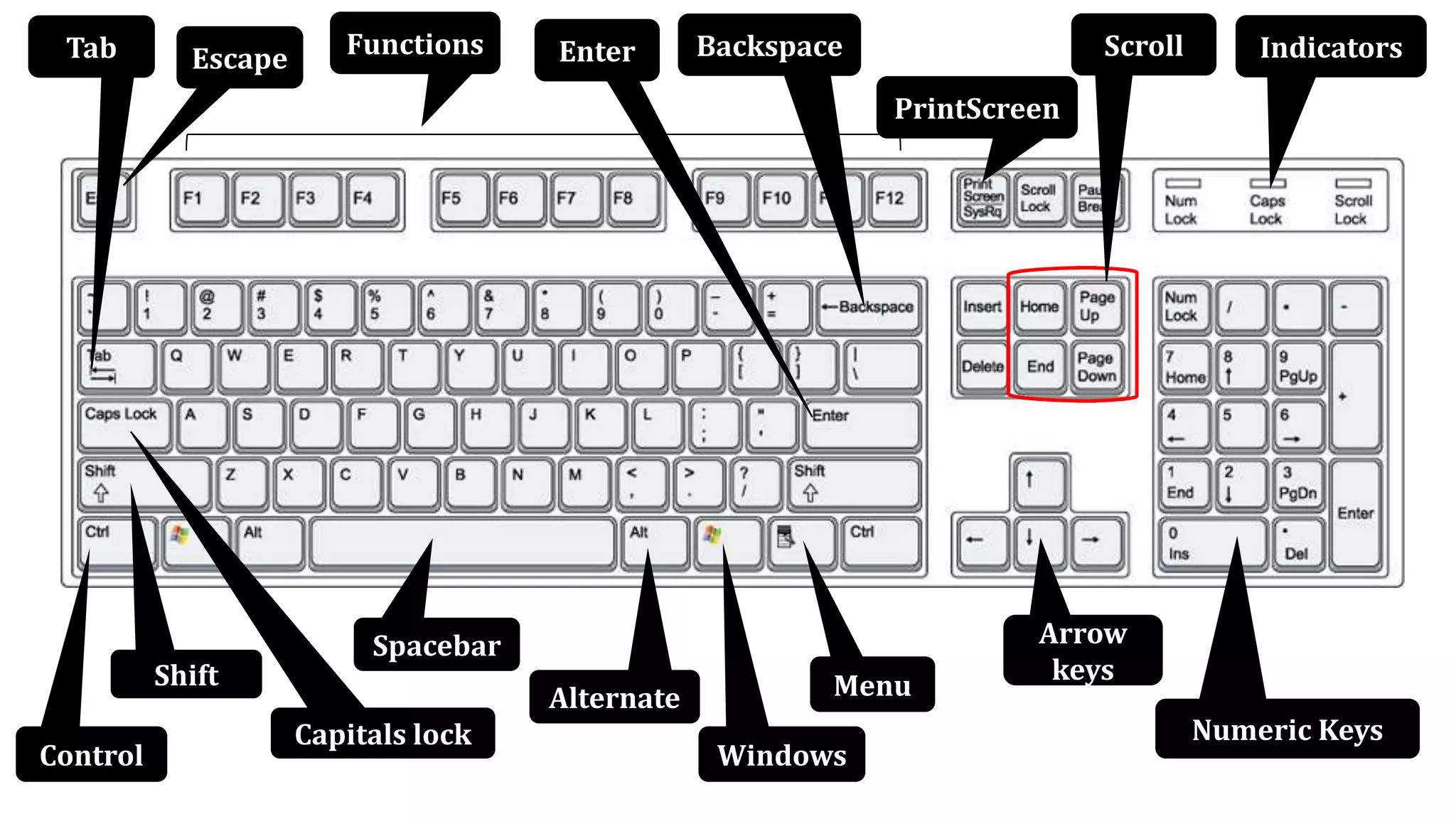
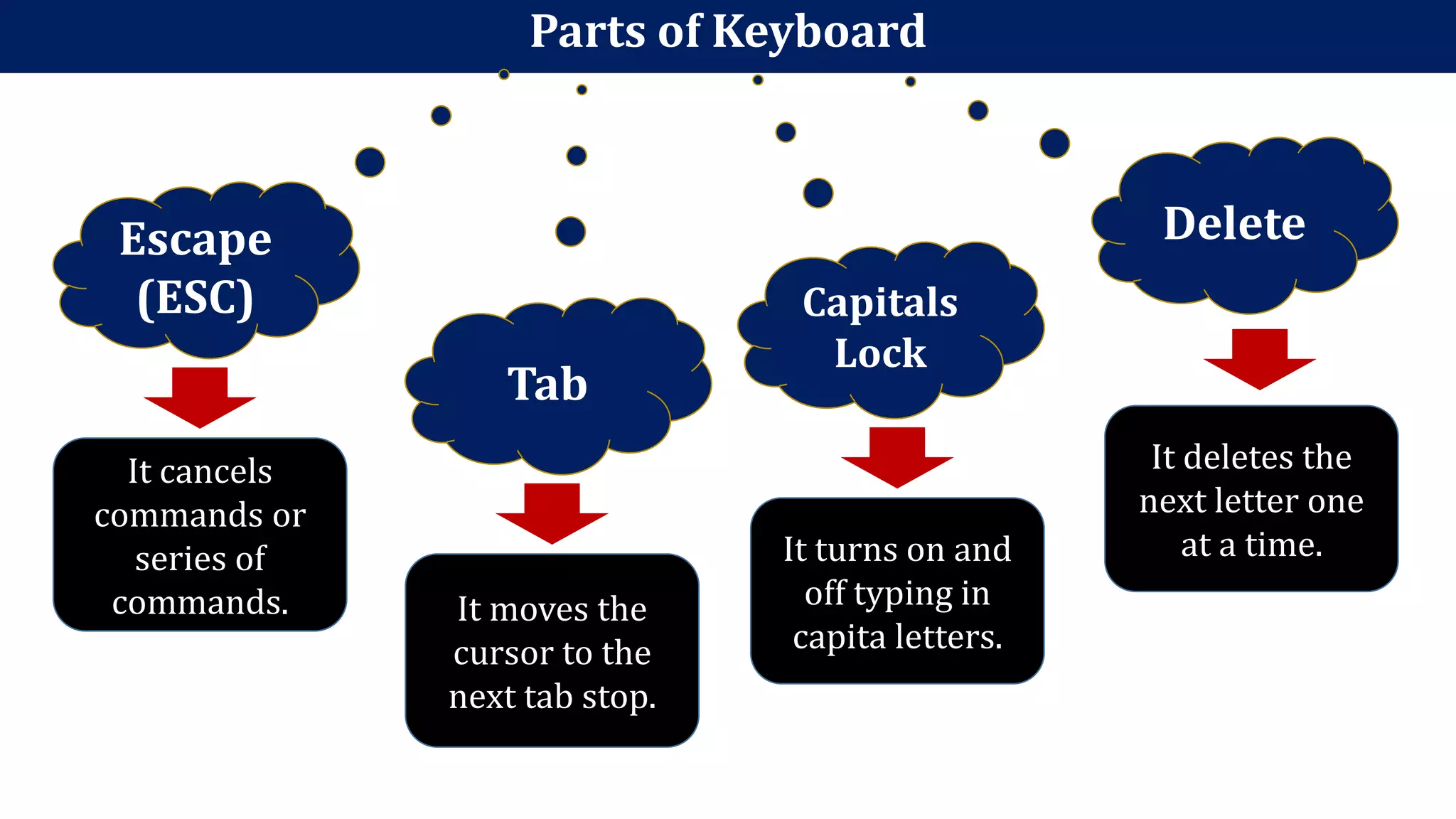
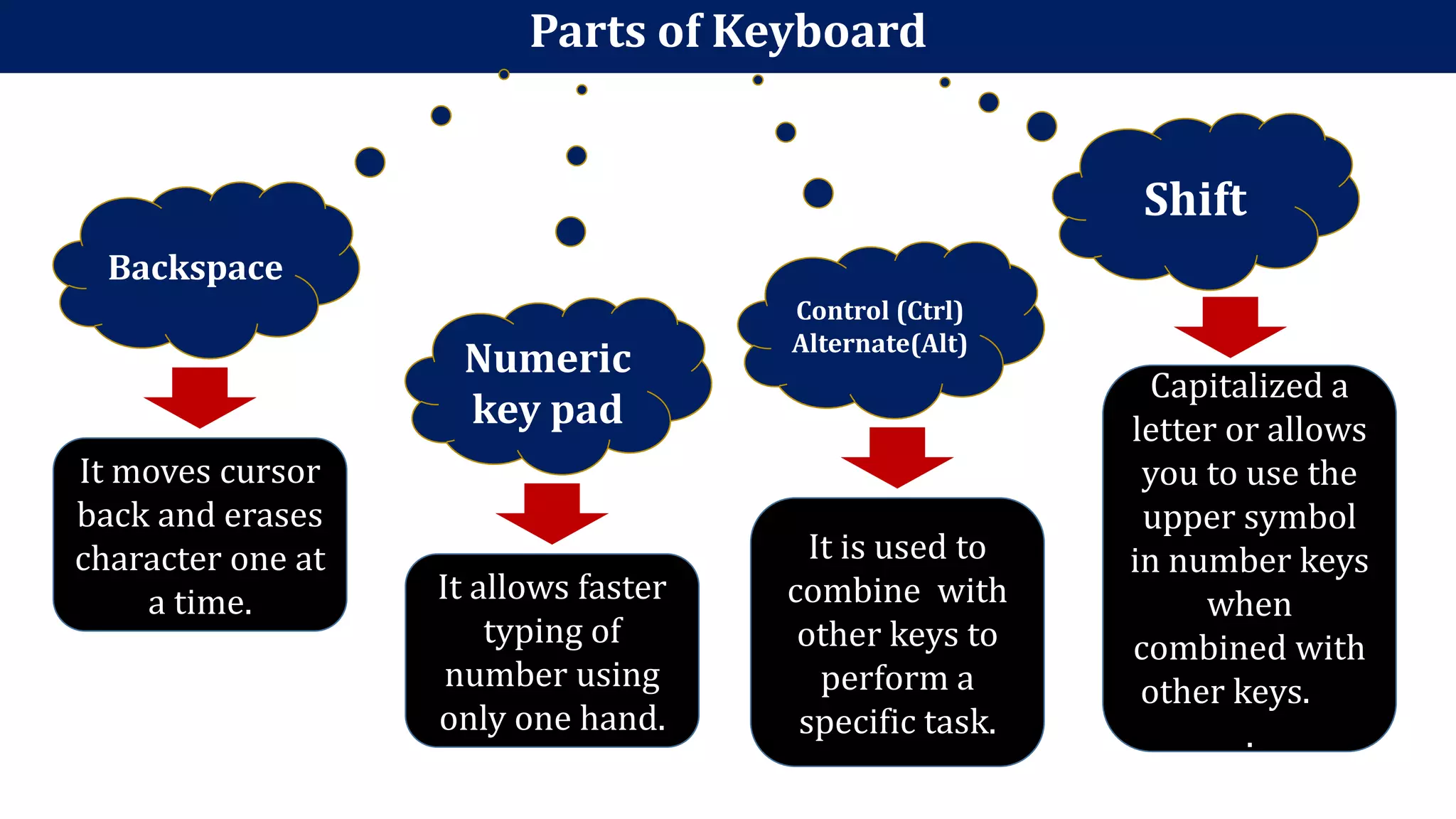
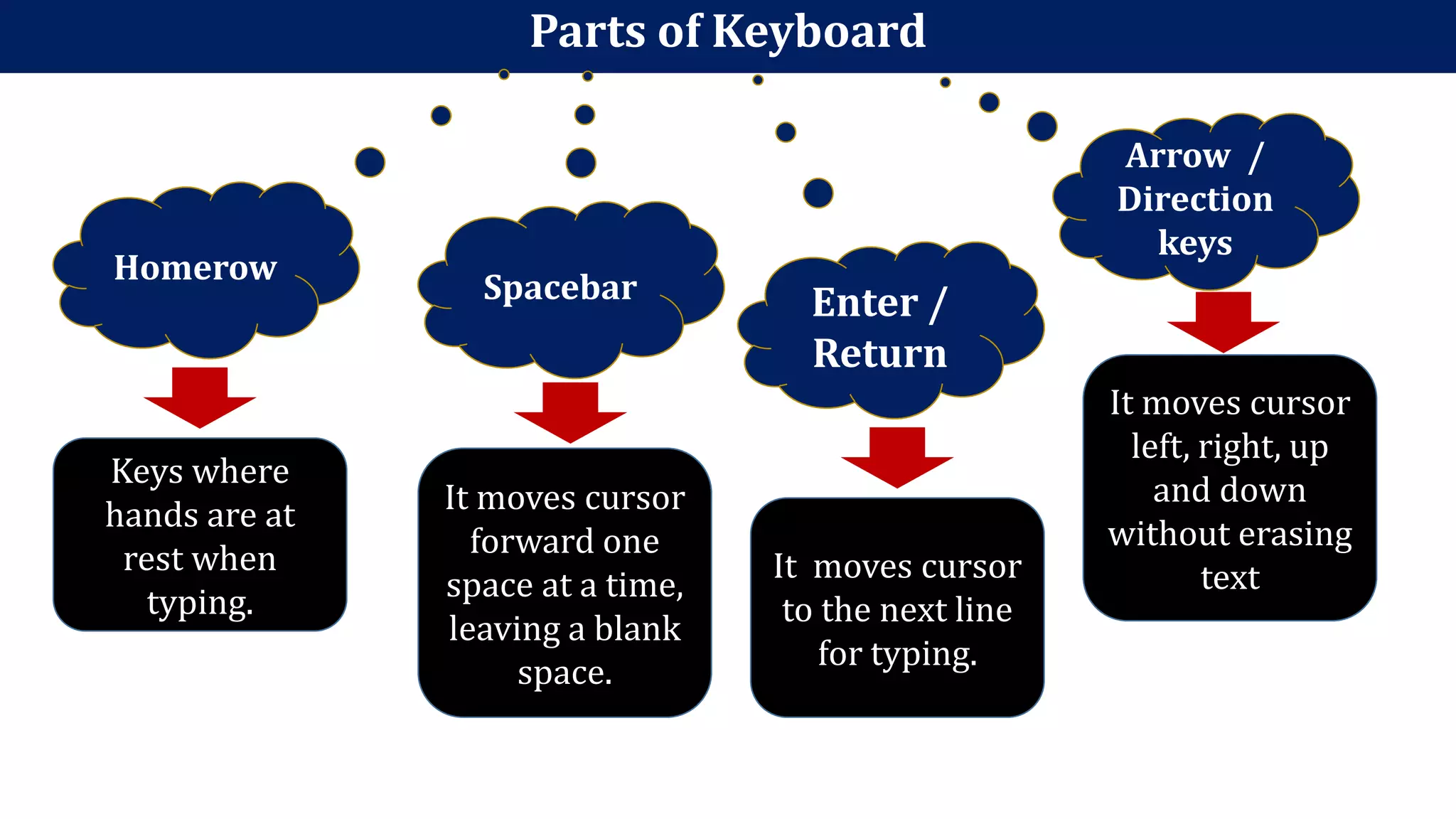
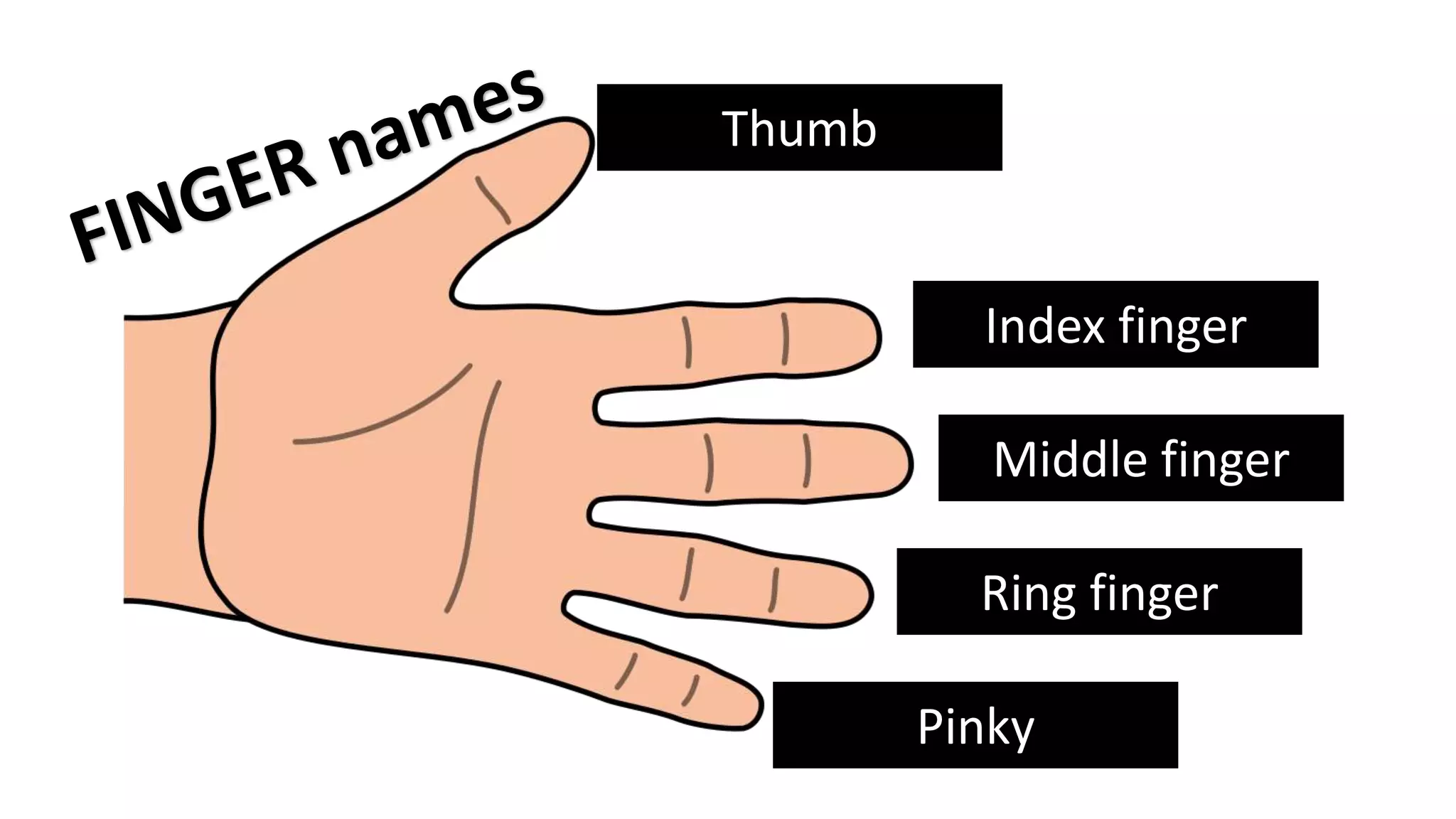
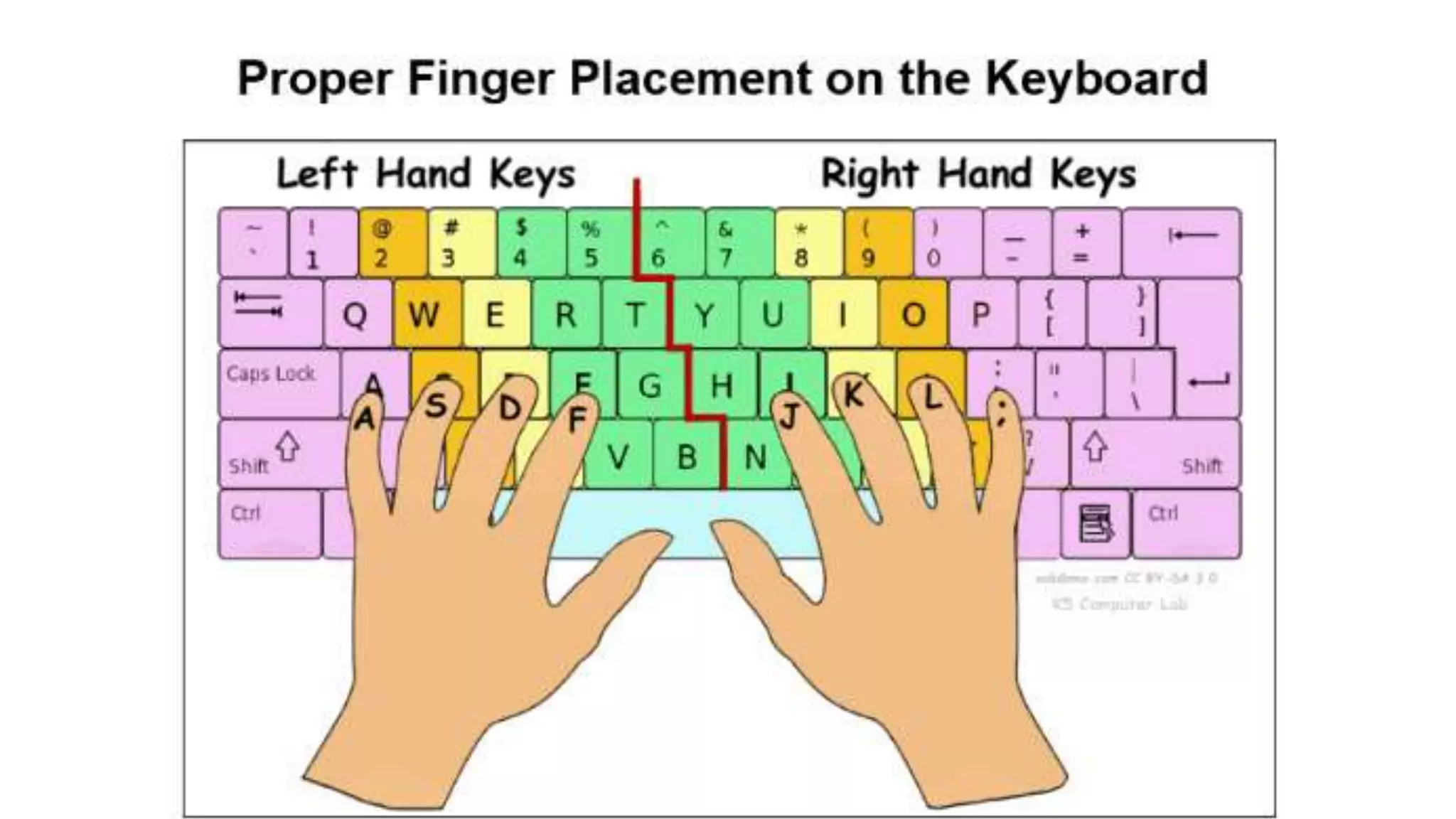
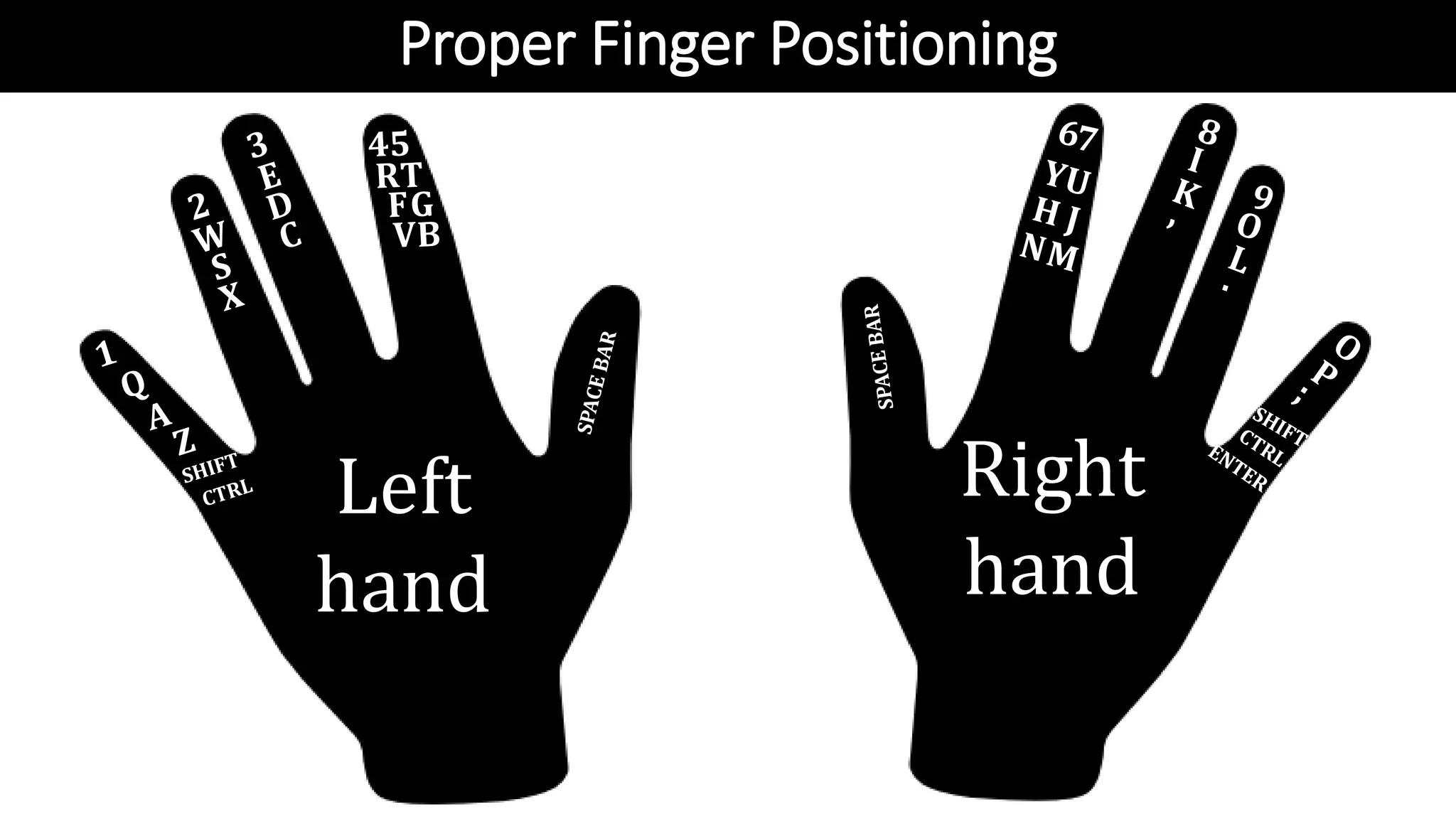
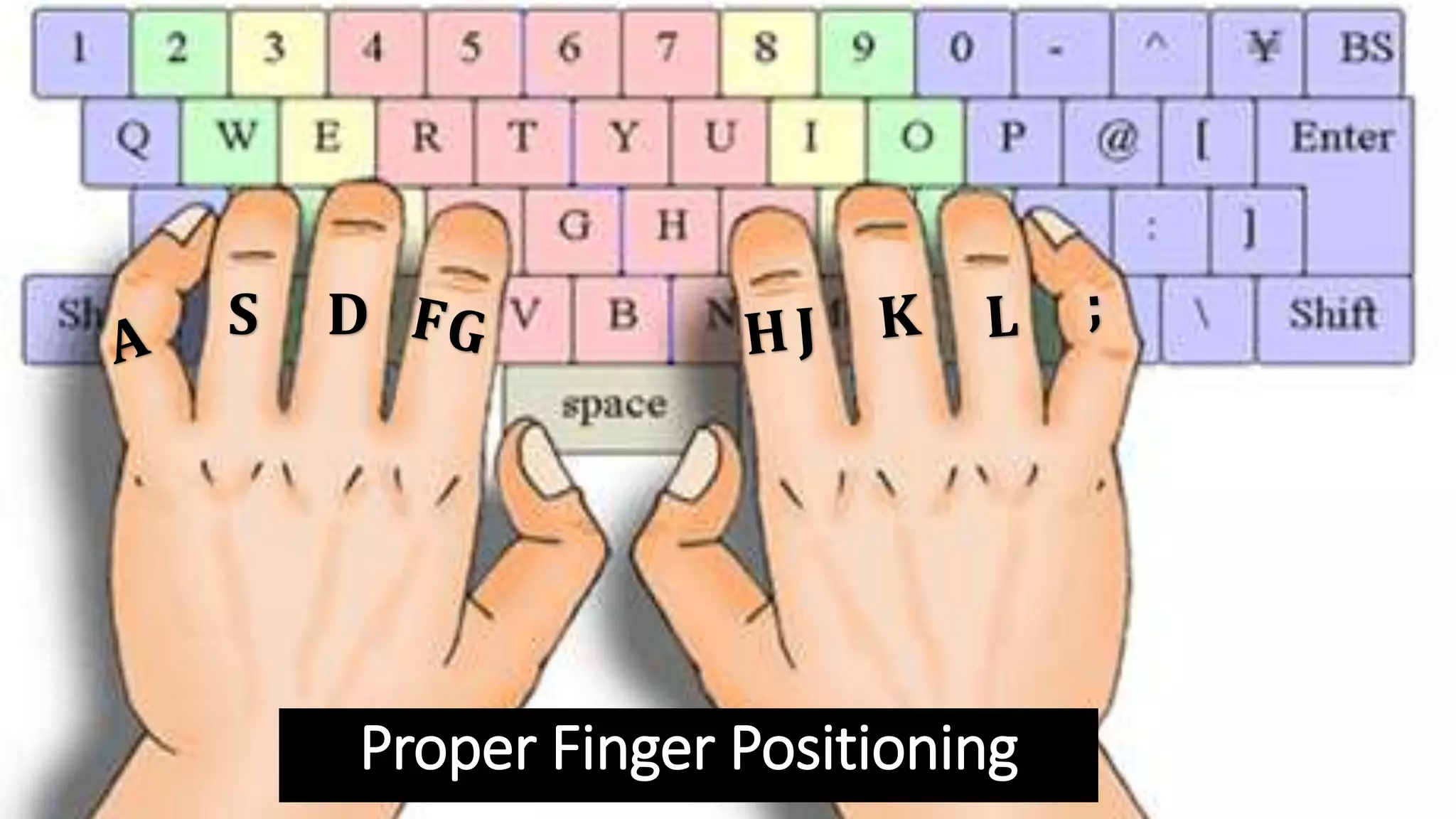
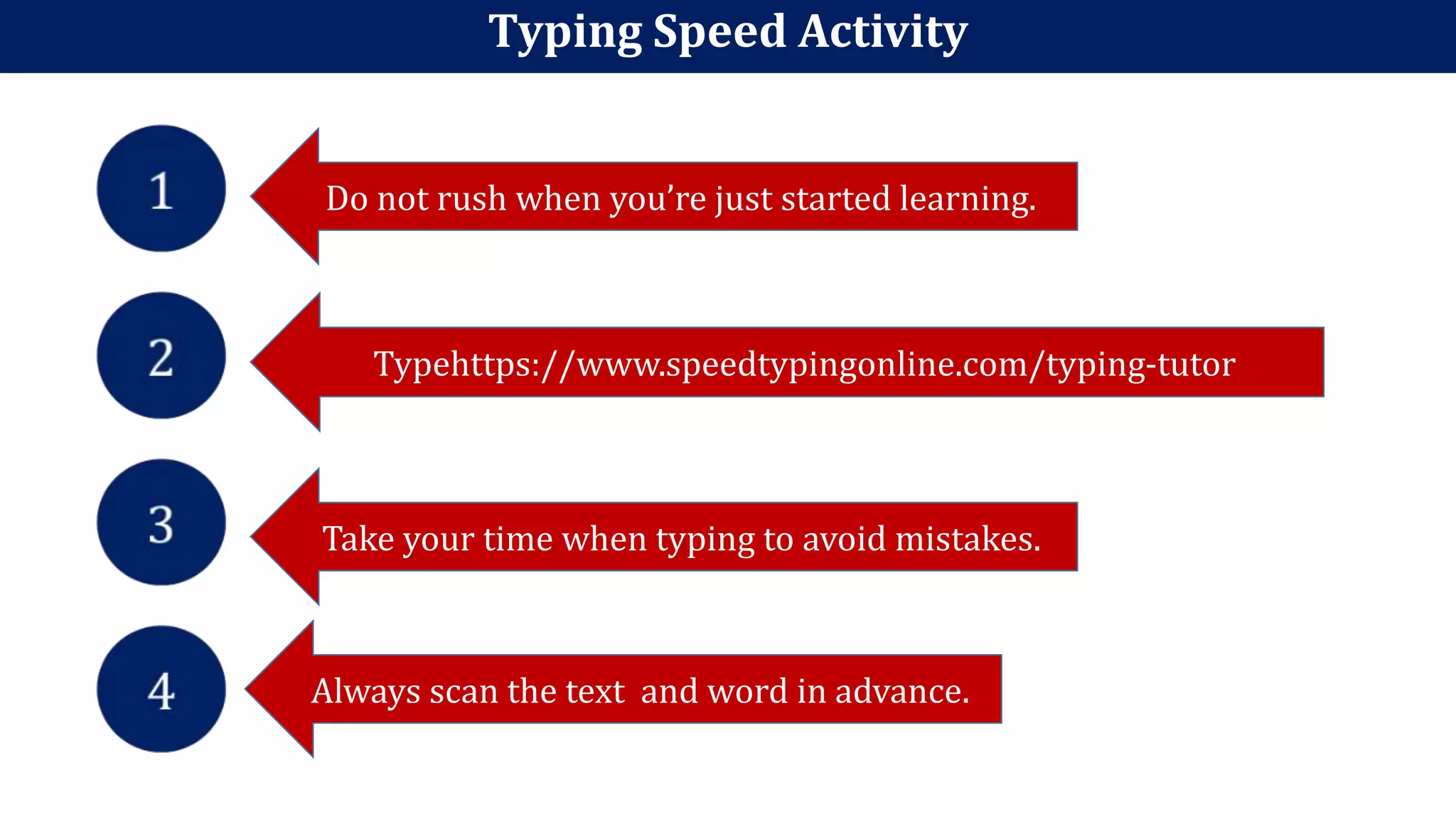
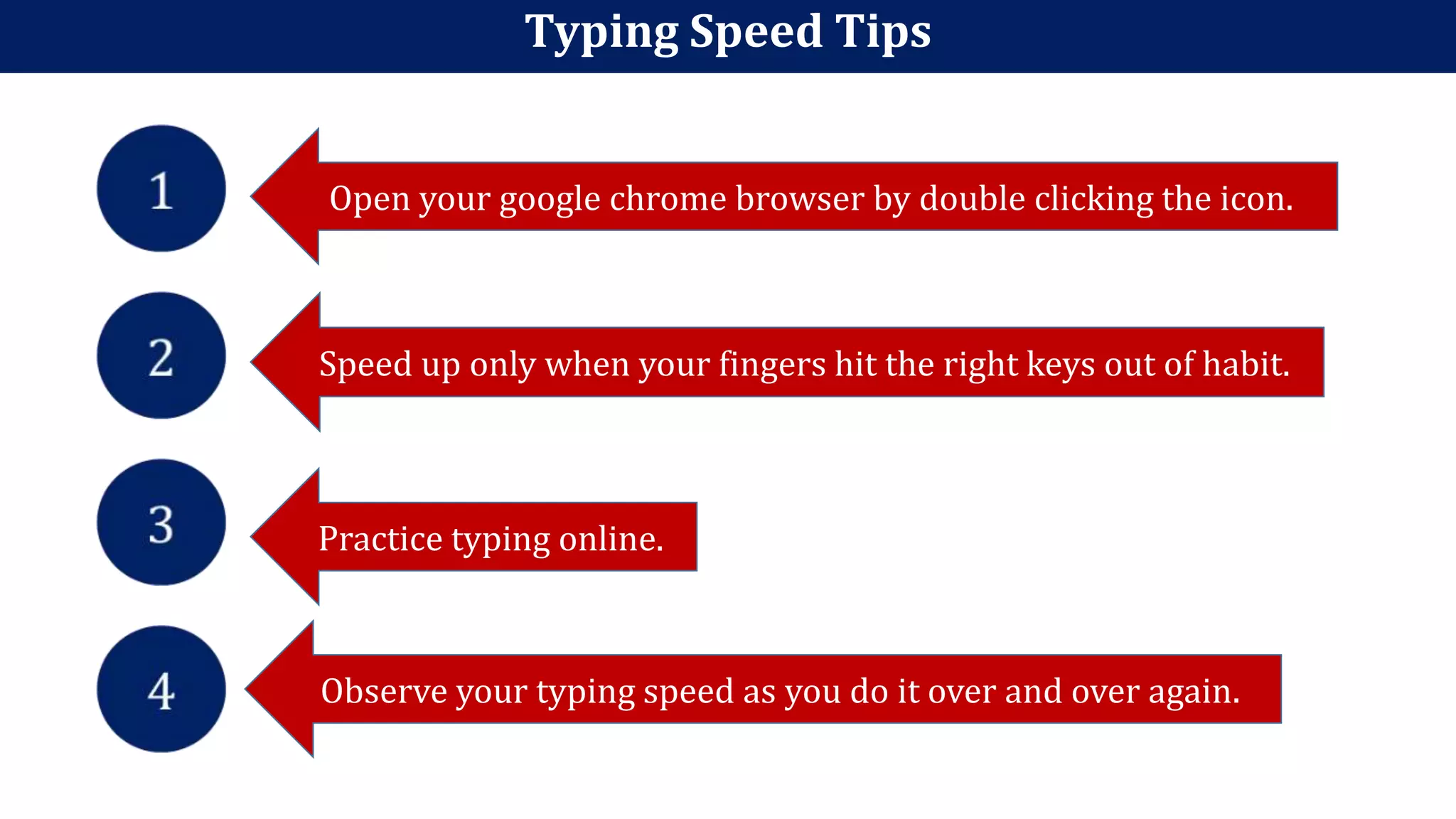
The document provides information on proper keyboard finger positioning and typing techniques. It discusses the functions of common keyboard keys like Escape, Control, Shift, and Spacebar. It explains that the home row keys are where hands rest and identifies the left and right hand fingers. The document encourages taking your time when learning, scanning ahead, and practicing online to build speed and reduce mistakes over time.