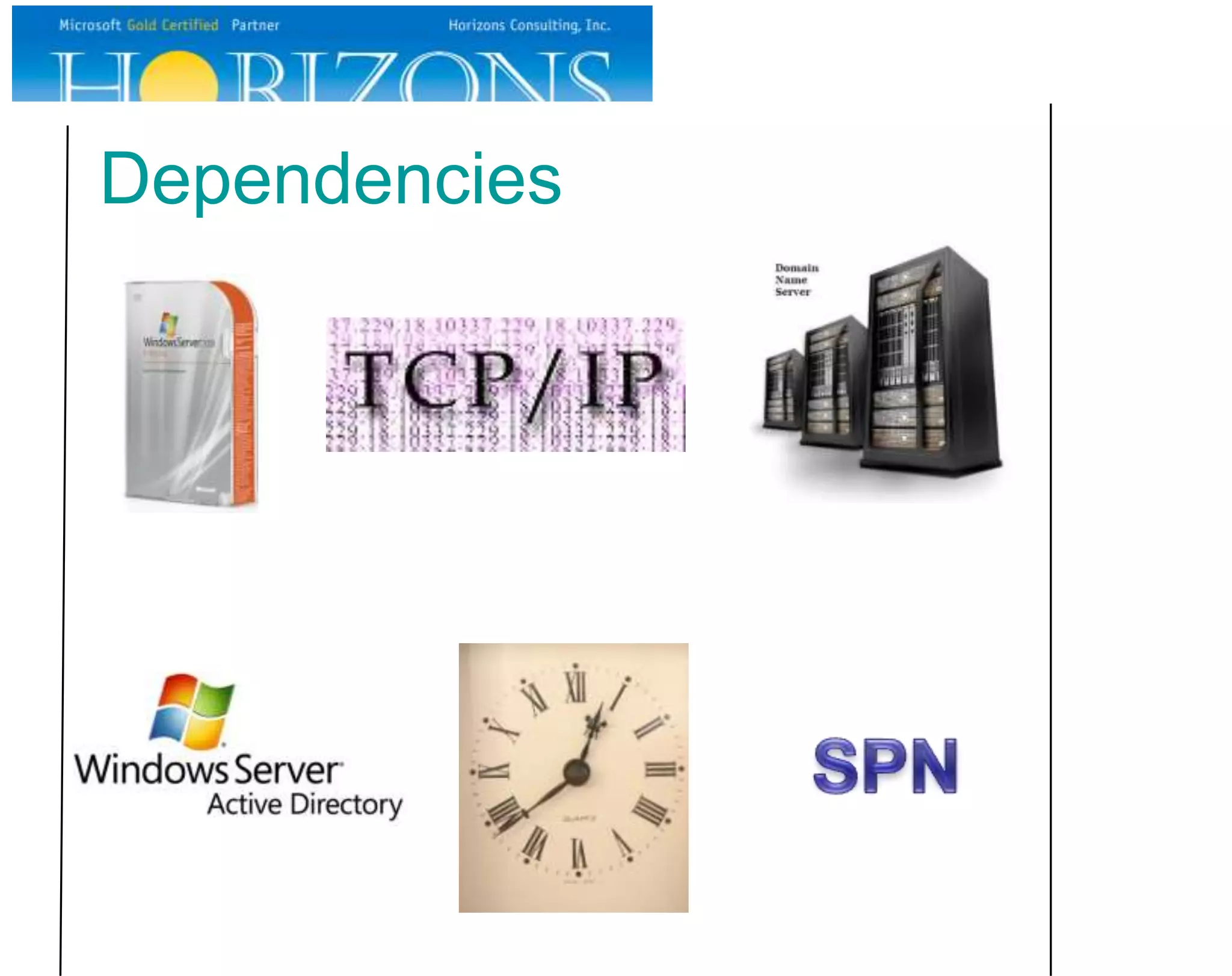
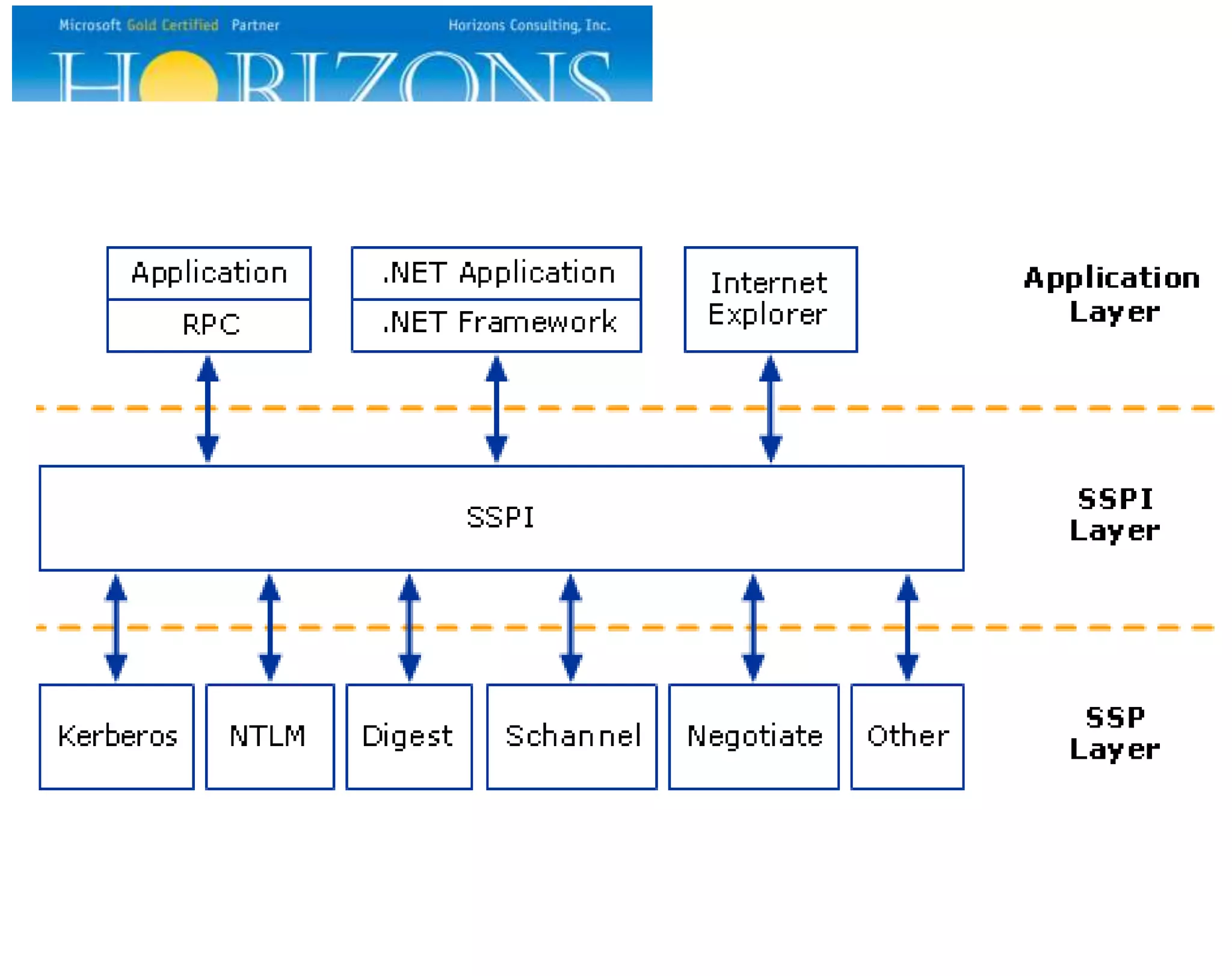
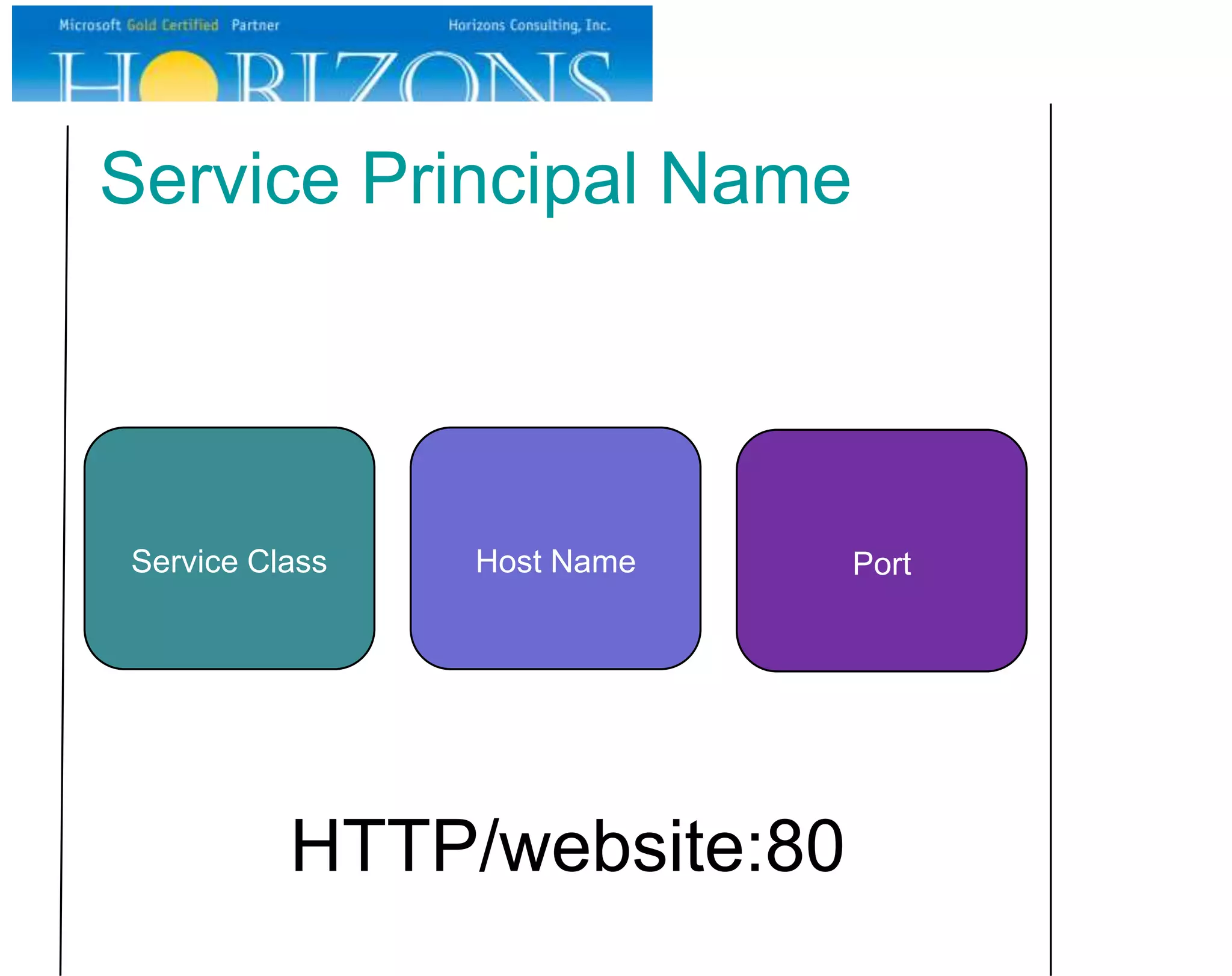
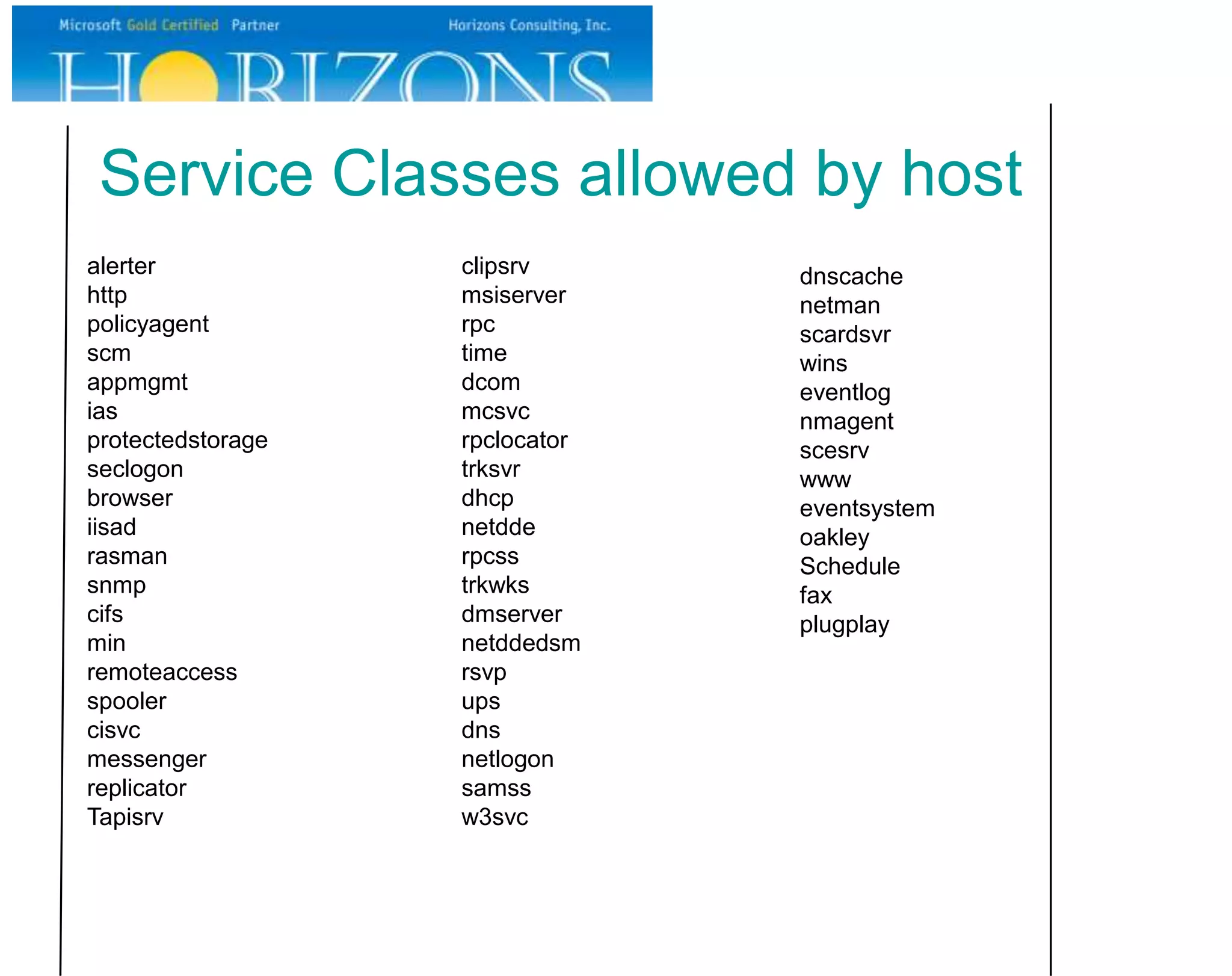
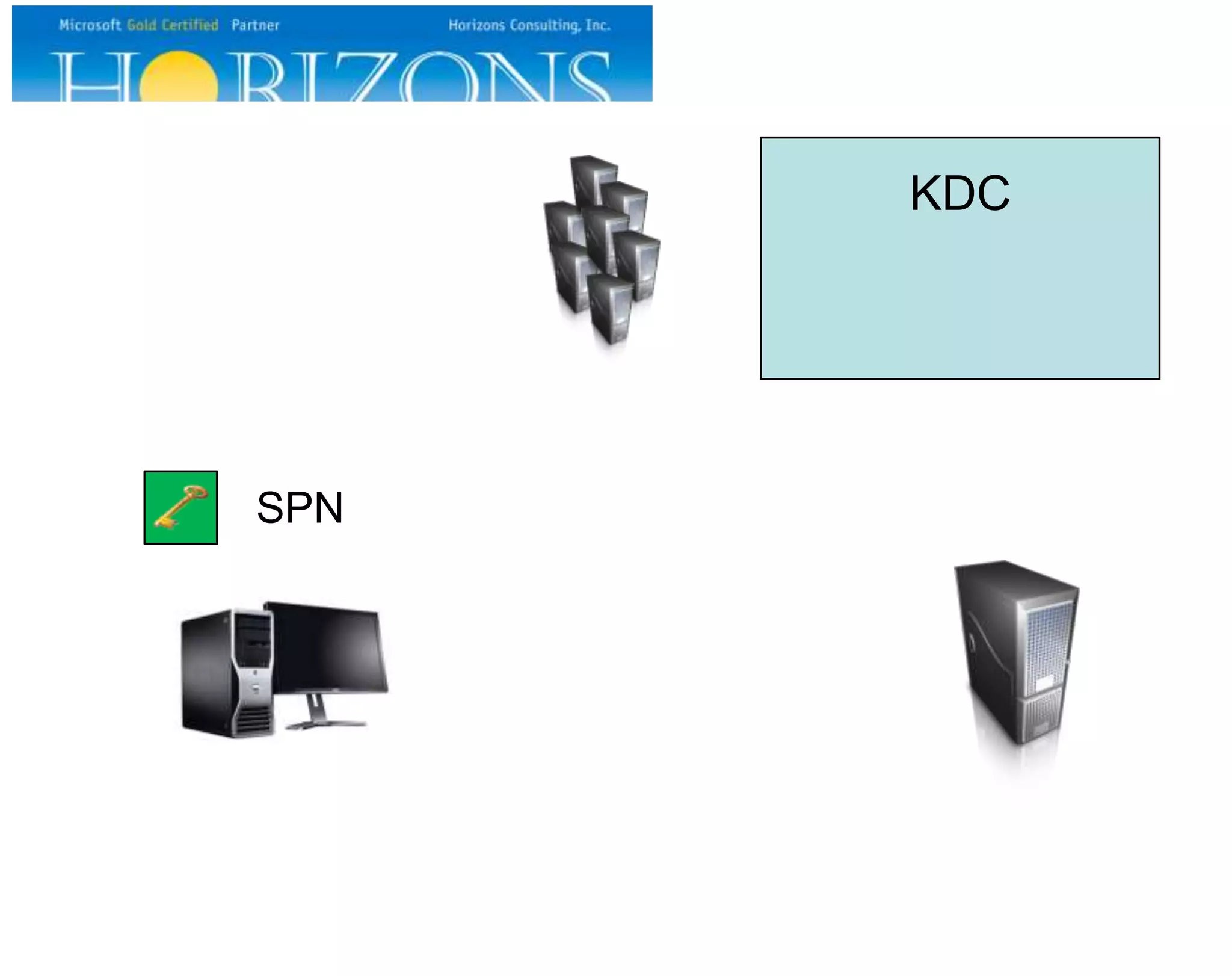
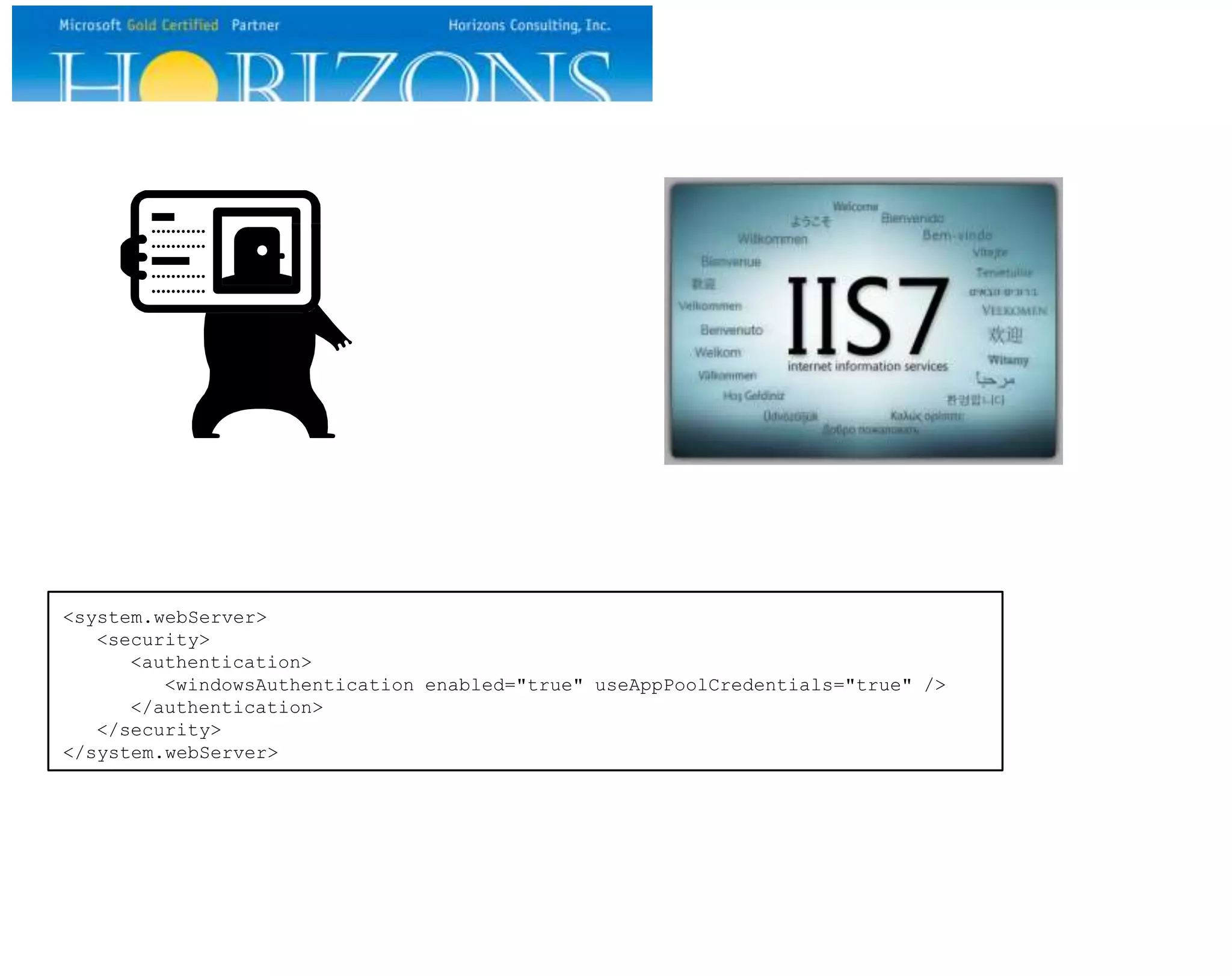
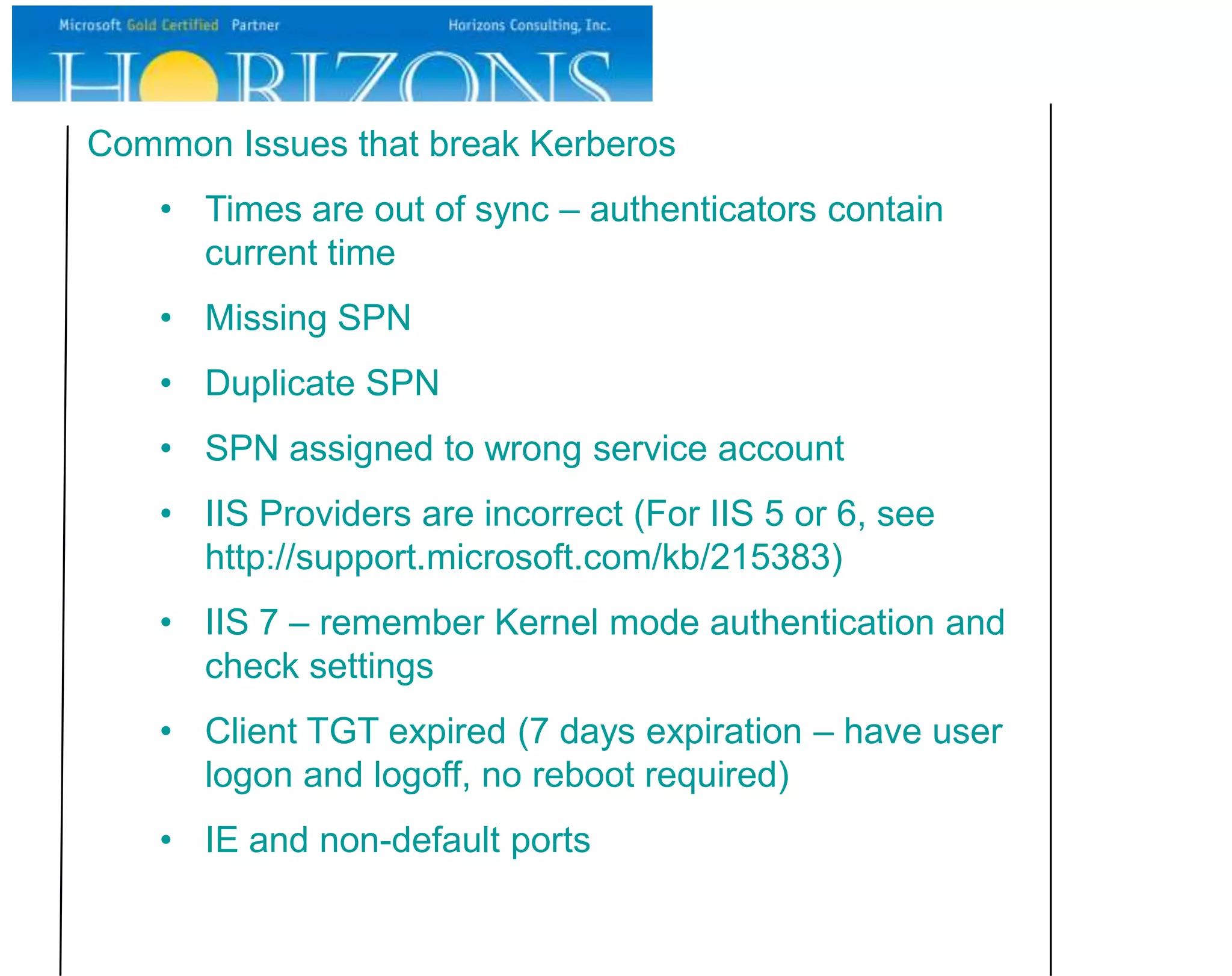
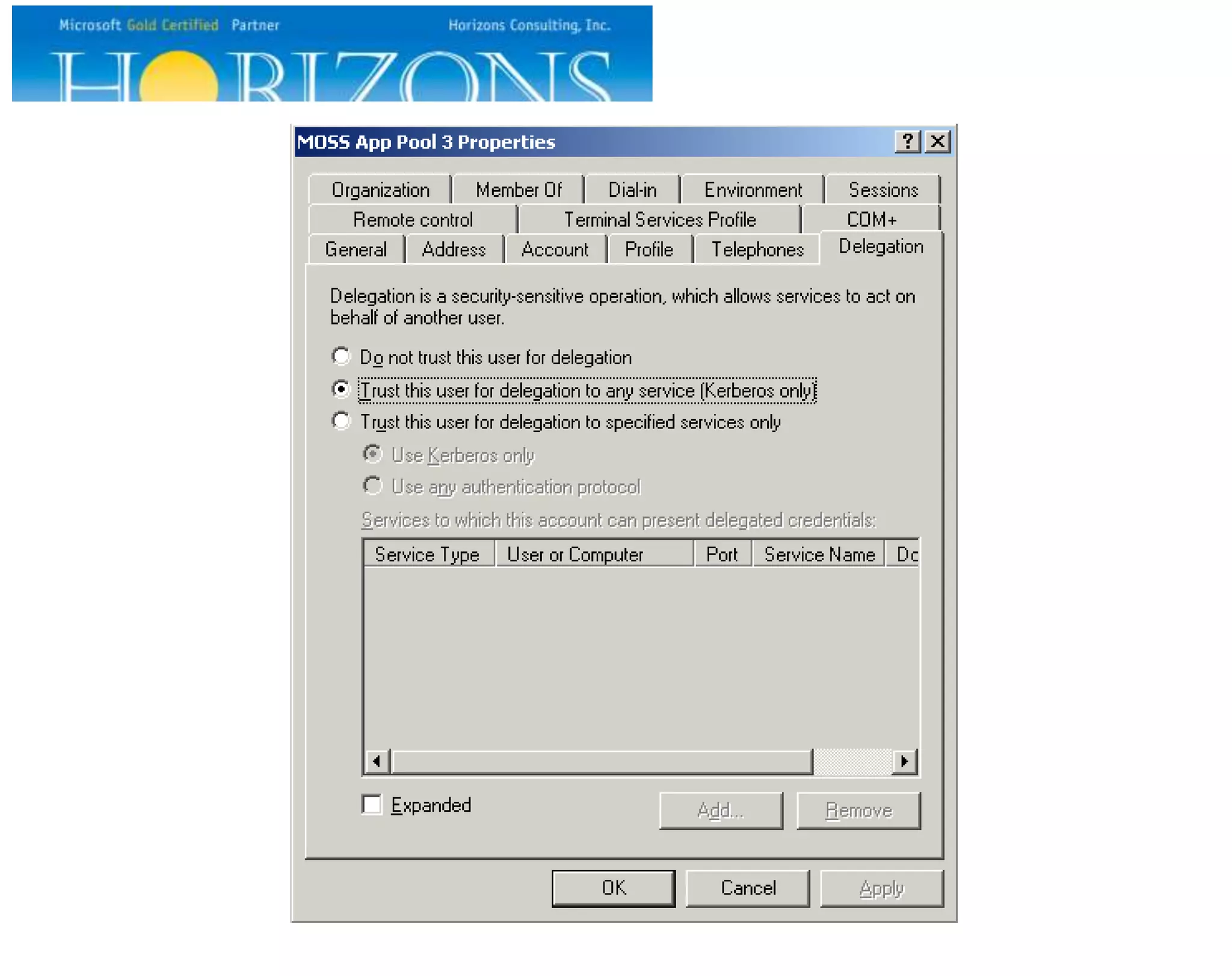
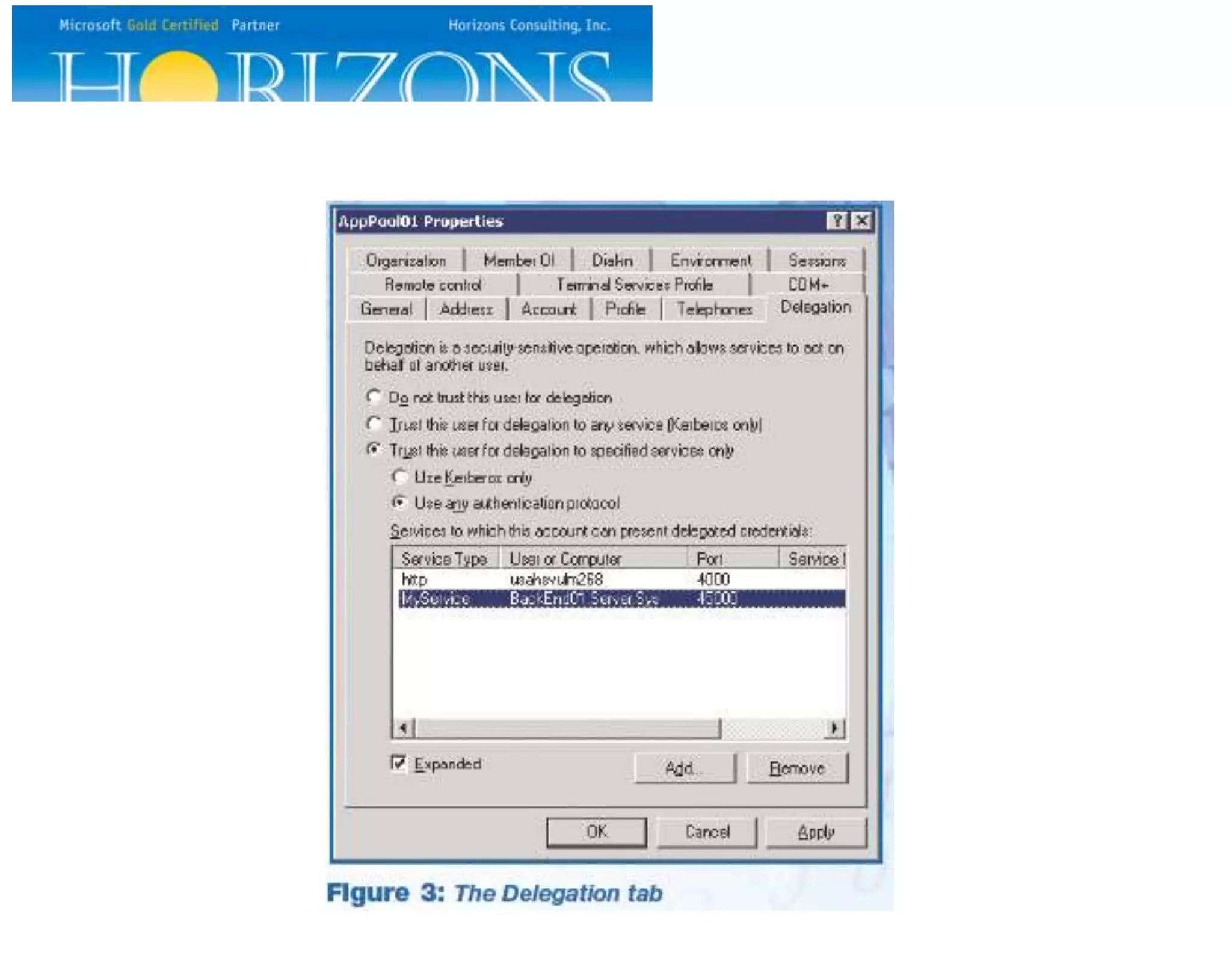
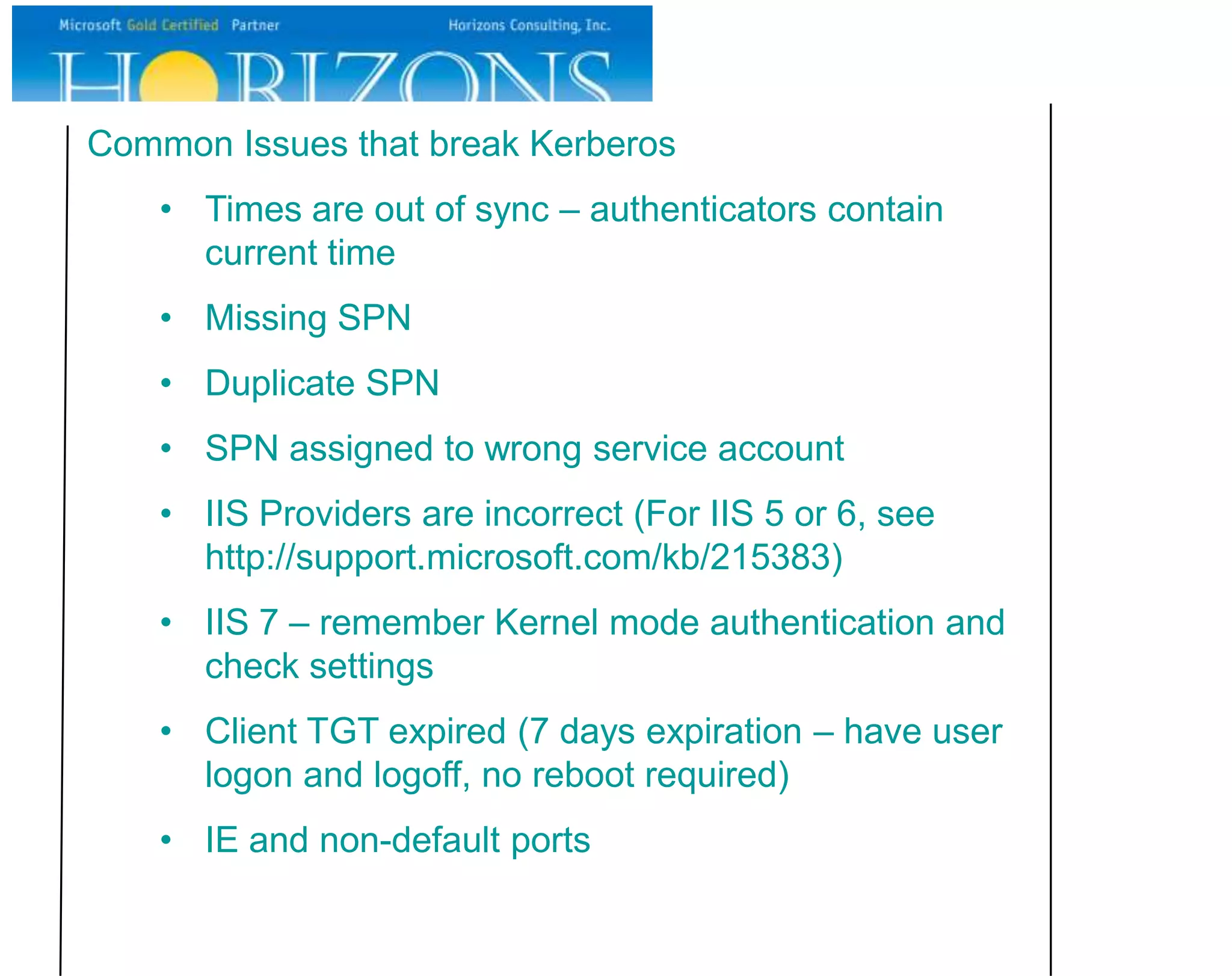
This document provides an overview and guide to Kerberos authentication. It begins with introductions and an agenda. The agenda covers Kerberos overview, the logon process, accessing a website, troubleshooting Kerberos, and delegation. It then discusses Kerberos details such as dependencies, service principal names, and references. It concludes with a Q&A section and appendix.