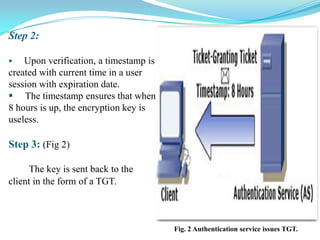
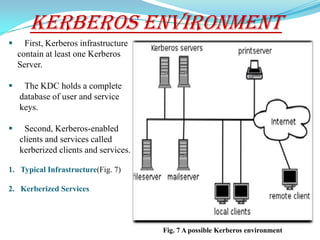
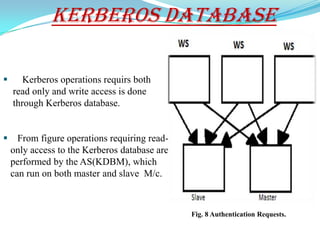
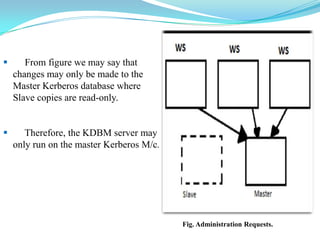
This document discusses Kerberos, an authentication system that allows nodes communicating over an insecure network to verify each other's identity. It provides a history of Kerberos, an overview of how it works using tickets and session keys, the roles of various components like the KDC, and advantages like password encryption. Kerberos allows for secure authentication in open network computing environments and has been widely adopted by companies. Public key cryptography also enhances Kerberos by easing key distribution.