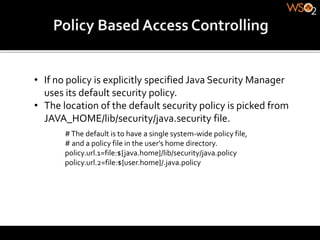
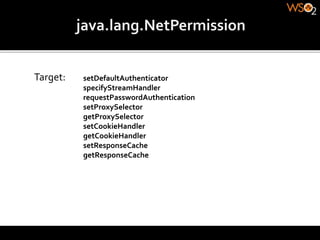
The document discusses Java security and how to configure a security manager and policy in Java. It explains that a security manager creates a sandbox for Java applications and uses a security policy to define permissions. The policy grants or denies permissions to code based on code location, trust via signing, and the user running the code. It provides examples of policy syntax and common permissions.