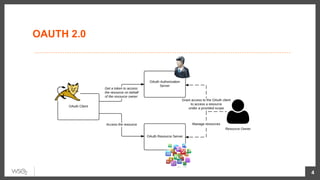
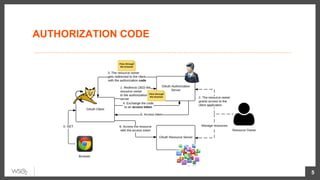
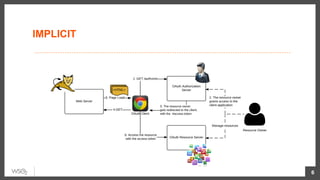
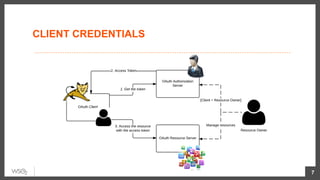
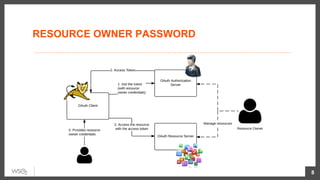
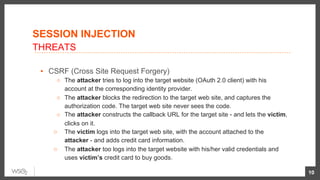
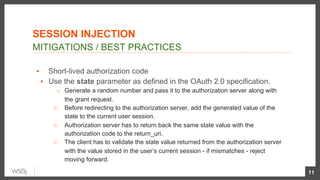
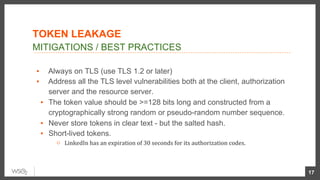
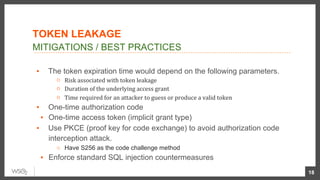
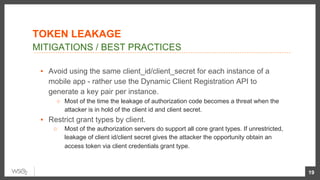
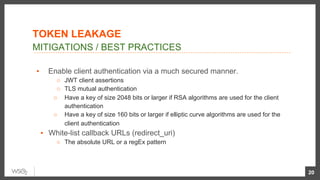
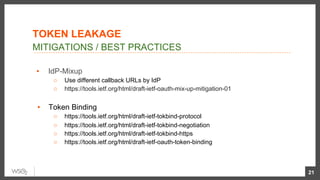
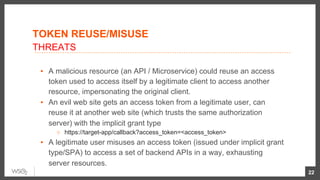
This document summarizes OAuth 2.0 threat landscapes and best practices for mitigation. It discusses threats such as CSRF, session injection, token leakage, IDP mix-up, and token reuse/misuse. Recommended mitigations include using the state parameter, PKCE, short-lived tokens, TLS, white-listing callback URLs, scoped tokens, audience restriction, OpenID Connect, and throttling. The document provides technical details on various OAuth 2.0 flows and threats as well as references to relevant IETF draft specifications.