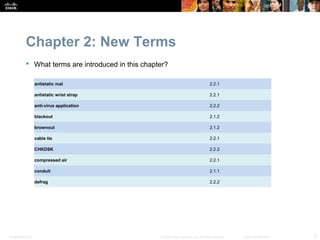
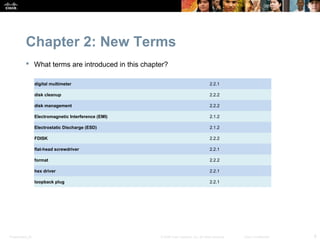
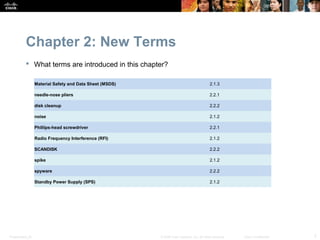
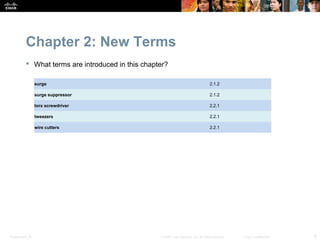
This chapter discusses safe lab procedures for working with computer hardware and tools. It covers electrical, fire, and chemical safety guidelines. Much of the chapter focuses on identifying and properly using hand tools and software diagnostic tools. Safe computer disassembly and preventative maintenance techniques are also examined. The objectives are to explain safe working conditions, identify computer components and tools, and demonstrate proper tool usage.