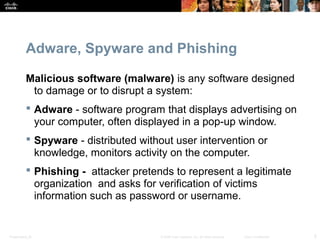
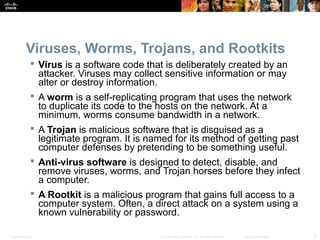
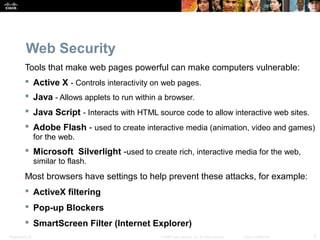
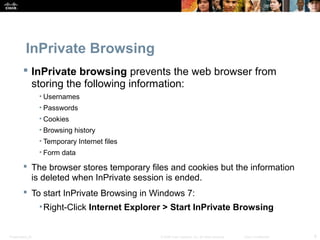
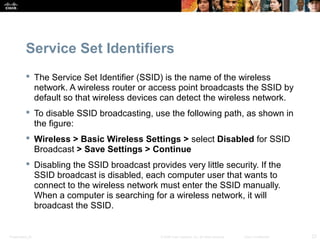
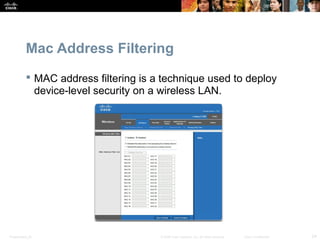
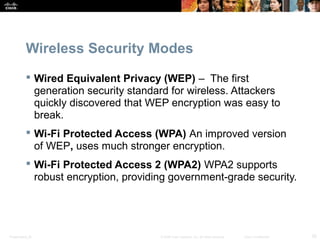
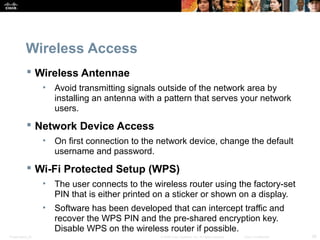
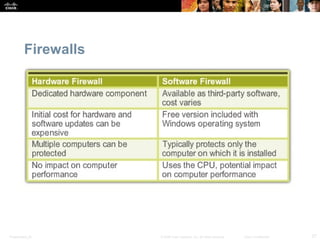
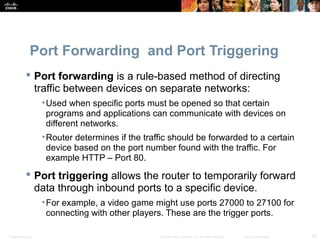
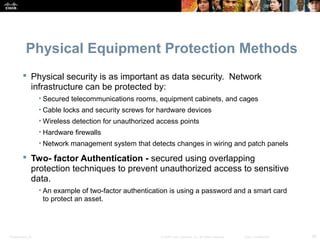
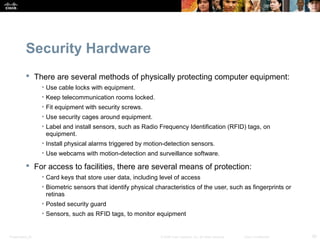
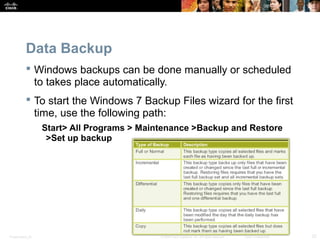
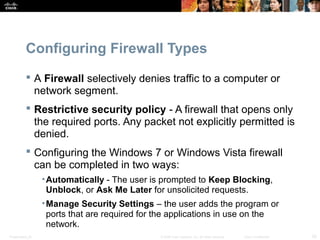
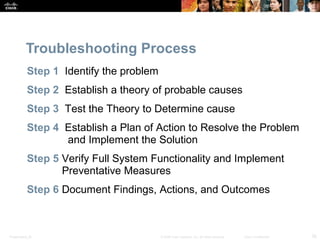
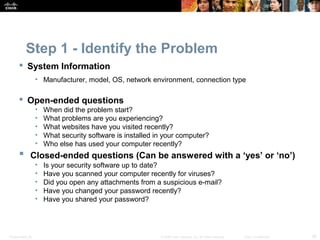
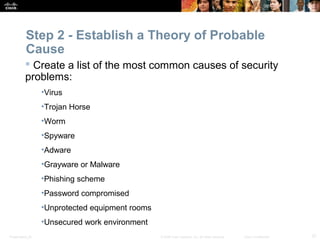
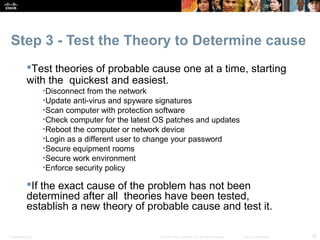
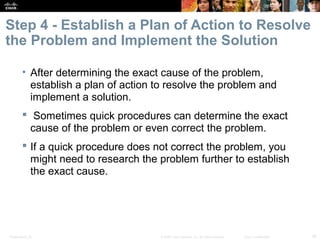
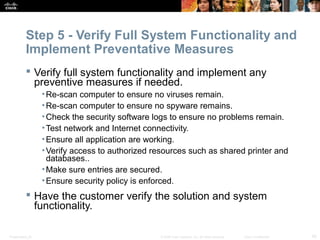
Security is important to protect private information, company secrets, and equipment from threats. A chapter discusses security procedures like identifying threats, maintaining security through techniques like passwords and updates, and troubleshooting security issues. Potential threats include viruses, hacking, and loss of data or equipment. The document outlines various security methods and best practices for networks, data, wireless access, and hardware to maintain security.