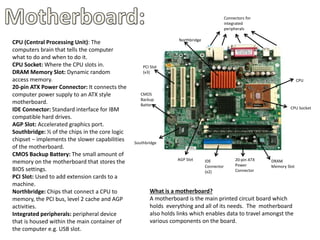
A motherboard is the main circuit board that holds and connects all the components of a computer system. It contains the CPU socket, memory slots, expansion slots, connectors for peripherals and power supply. Key components include the northbridge and southbridge chips, BIOS chip, and connectors for devices like graphics cards, hard drives, and expansion cards.