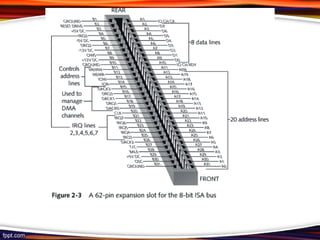
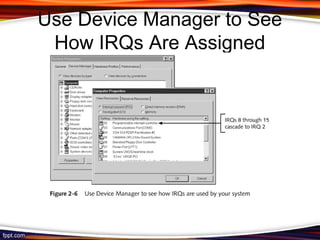
The document explains the interaction between hardware and software, detailing how system resources like memory addresses, I/O addresses, and DMA channels facilitate communication. It discusses categories of computer software, including BIOS, operating systems, and device drivers, as well as the booting process that brings a computer to an operable state. The summary outlines essential concepts like IRQs, hardware component configuration, and the loading of an operating system during startup.