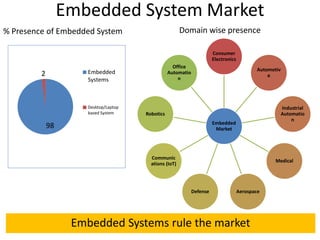
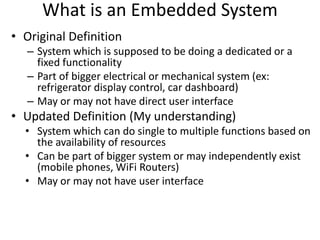
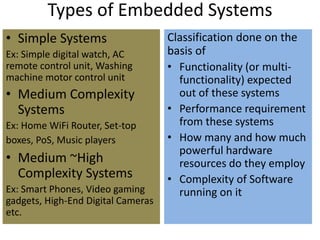
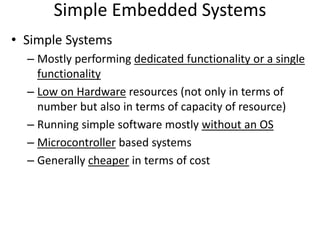
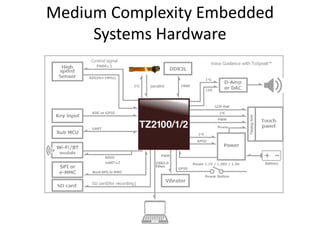
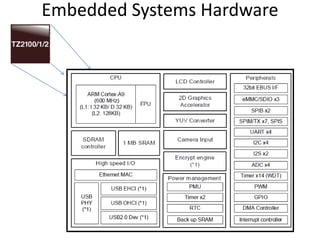
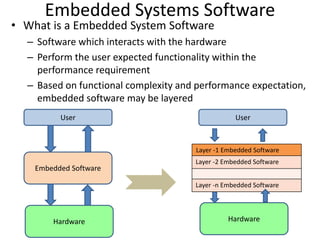
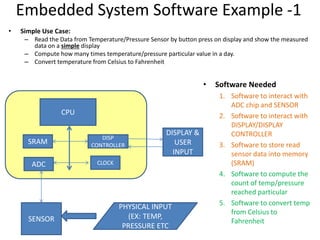
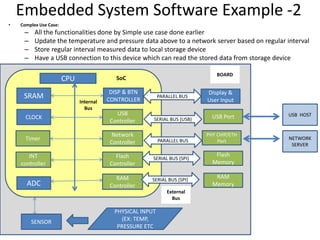
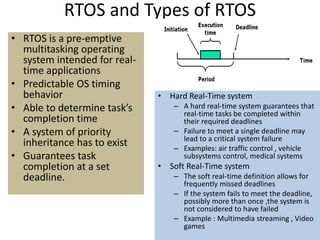
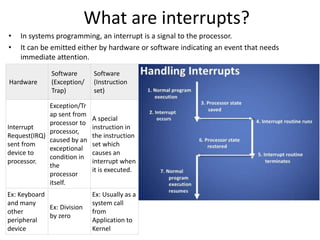
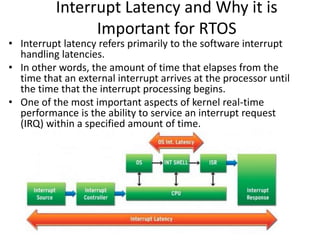
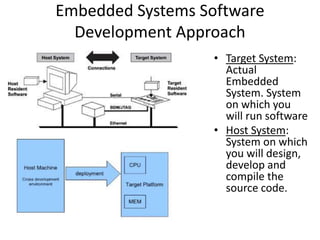
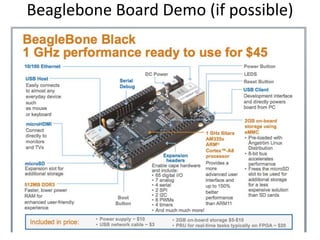
An embedded systems overview document discusses embedded systems, including what they are, common types, hardware components, software, and operating systems. It defines embedded systems as systems that perform dedicated or fixed functions, which may be part of larger mechanical or electrical systems. Examples include appliances, vehicles, and industrial equipment. The document outlines categories of embedded systems based on complexity, and common hardware elements like microprocessors, memory, and peripherals. It also discusses layered embedded software and the roles of operating systems, device drivers, and application software.