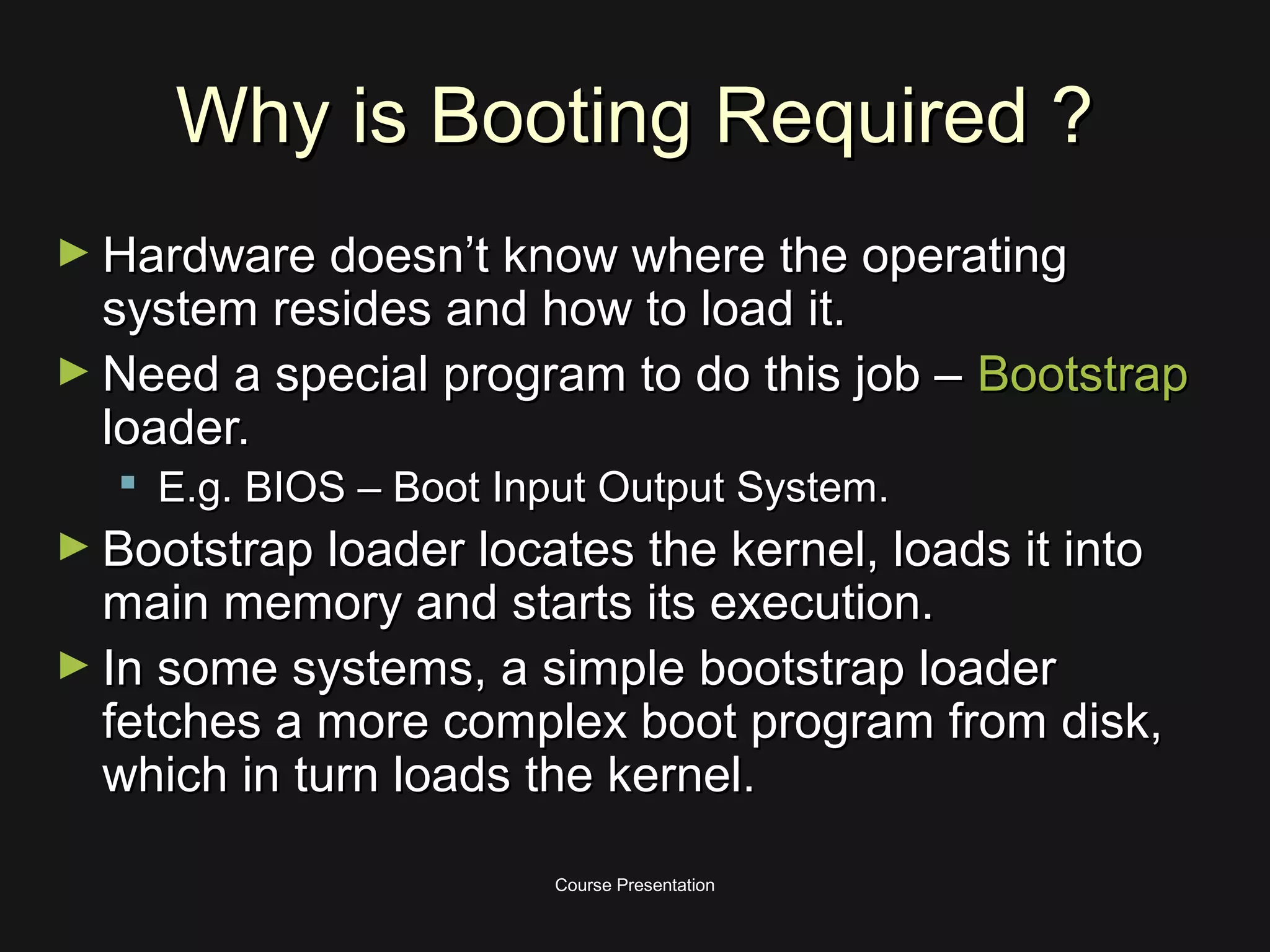
The document provides information about booting of a computer system. It discusses that booting is required because the hardware does not know where the operating system resides or how to load it. A bootstrap loader, such as BIOS, is needed to locate the kernel and load it into memory.
The boot process begins with a reset event that loads instructions into the instruction register from a predefined memory location containing a jump to the bootstrap program stored in ROM. The bootstrap program then runs diagnostics, loads device drivers and initializes memory before locating and loading the operating system kernel to start the system startup process.