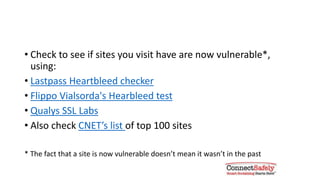
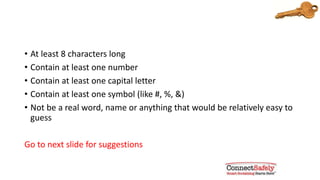
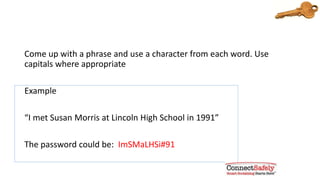
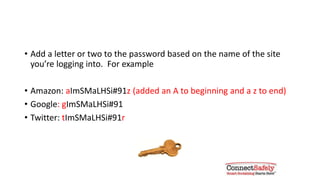
This document provides tips on how to protect yourself from the Heartbleed security flaw. It advises users to check if sites they visit are vulnerable, change passwords once sites are confirmed not vulnerable, monitor accounts for suspicious activity, use strong and unique passwords at least 8 characters with numbers, symbols and capital letters, consider two-factor authentication, avoid phishing scams, and use a password manager for strong randomly generated passwords.