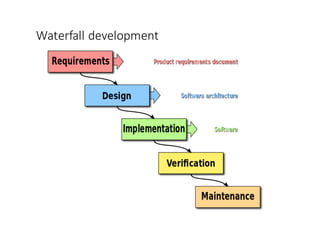
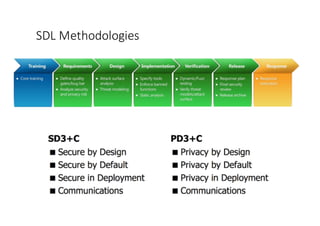
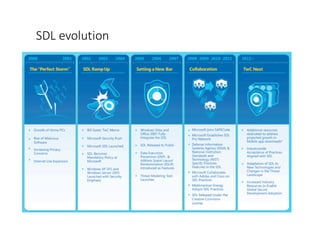
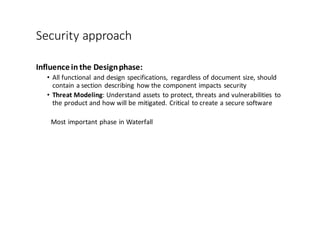
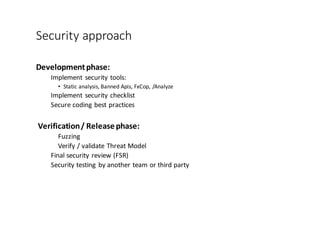
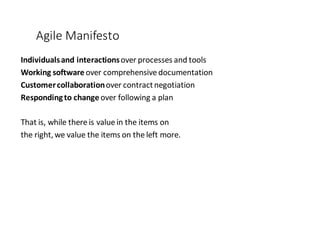
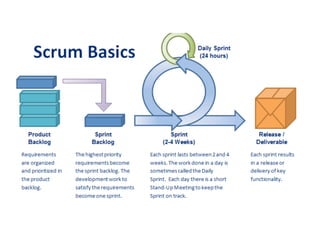
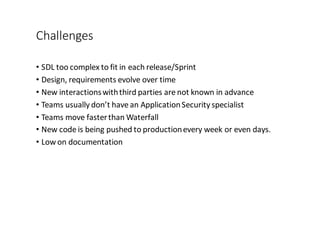
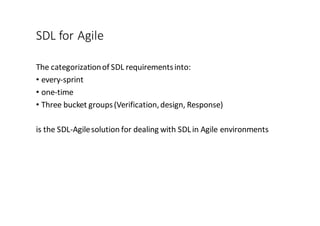
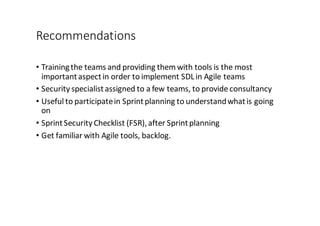
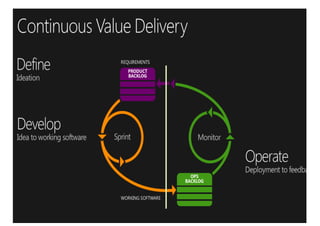
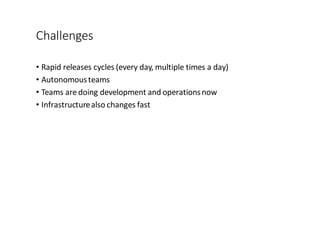
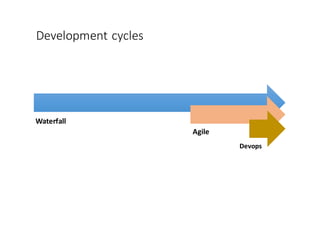
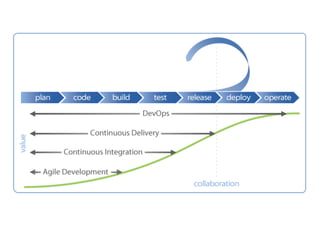
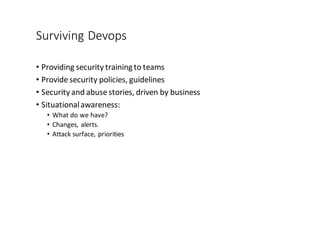
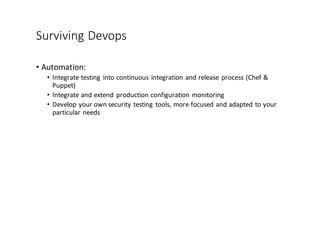
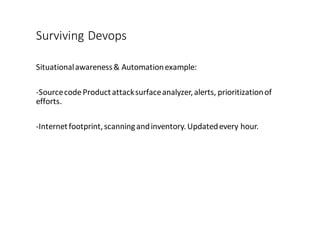
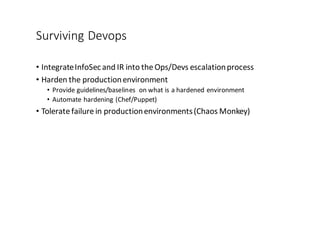
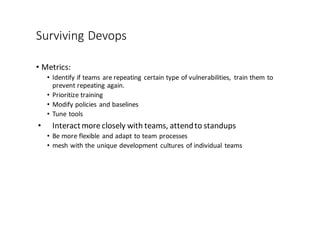
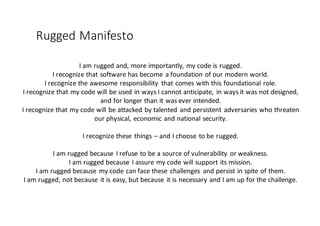
The document discusses the evolution of application security in relation to software development methodologies, contrasting the traditional waterfall model with agile and DevOps approaches. It emphasizes the need for security to be integrated throughout the development phases, backed by the Microsoft Secure Development Lifecycle (SDL) and adapts its practices for agile environments. Additionally, it presents 'rugged software' as a concept for organizations to proactively create secure and resilient software amidst evolving threats.