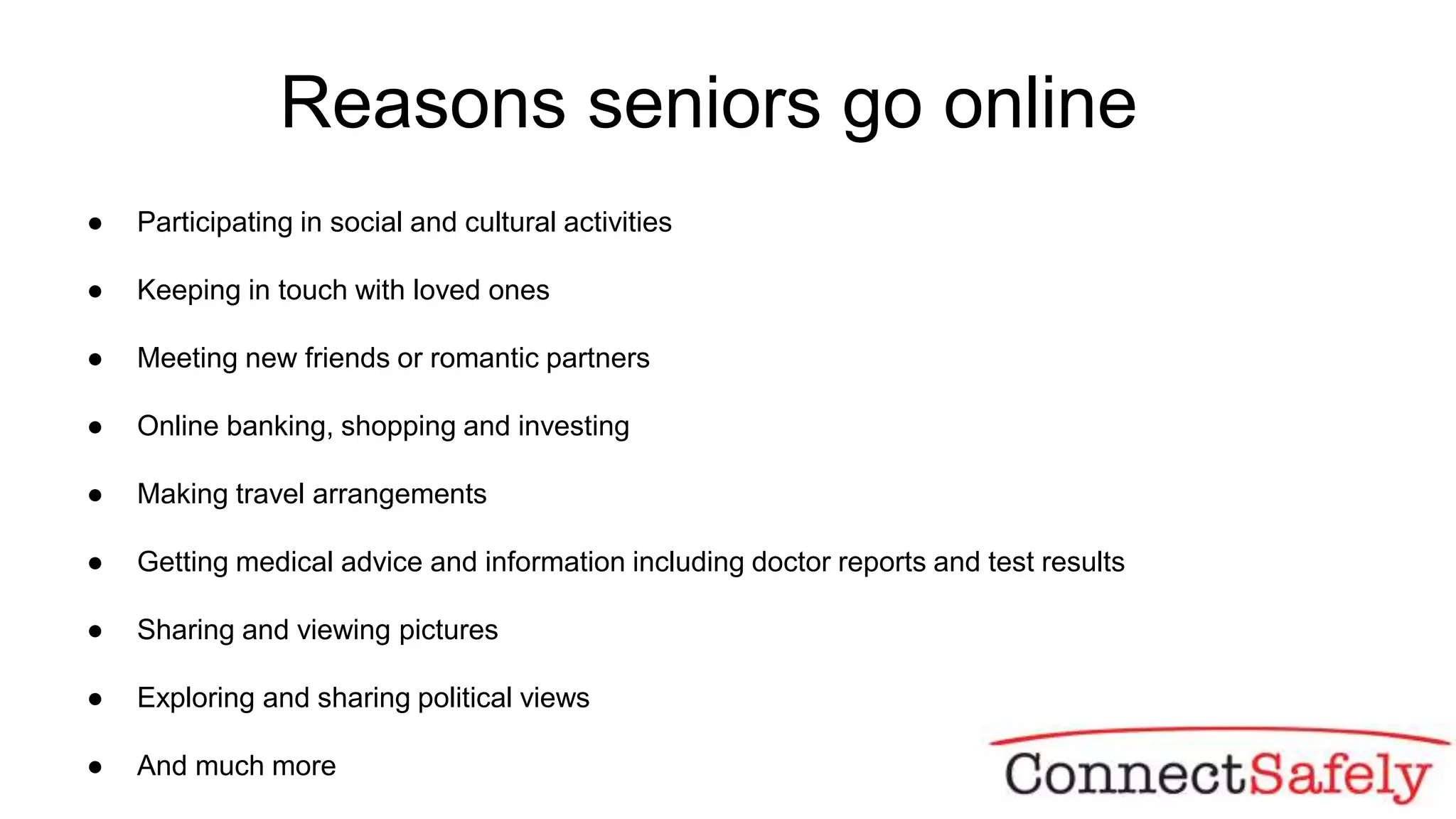
This document provides online safety tips for seniors. It discusses common online activities seniors engage in and basic safety practices like using strong passwords and privacy settings. Common scams targeting seniors are described such as personal emergency scams and online dating scams. Tips are provided for safe online banking, shopping, social media use, and identifying fake news. The document encourages fact checking information before sharing and outlines strategies for dealing with hate speech.