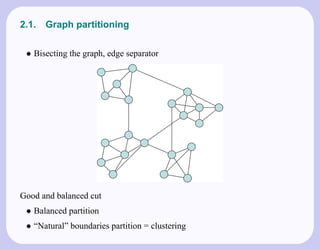
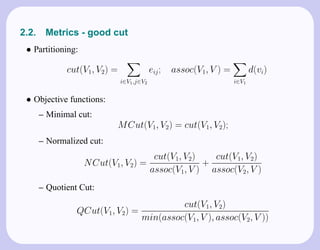
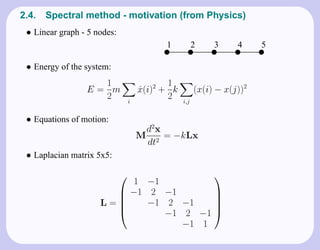
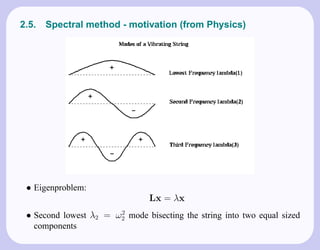
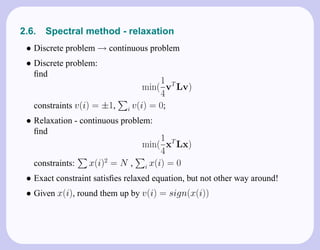
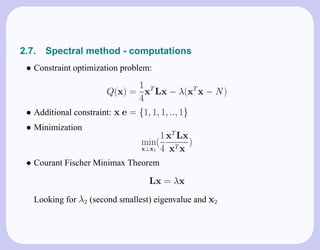
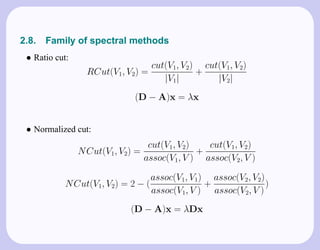
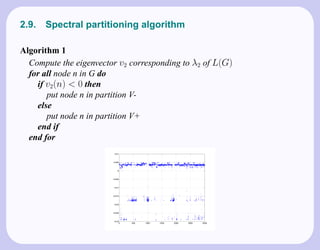
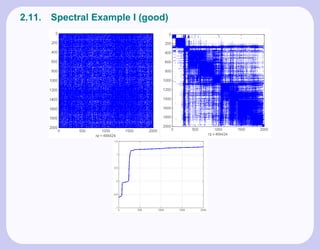
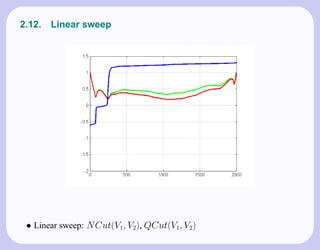
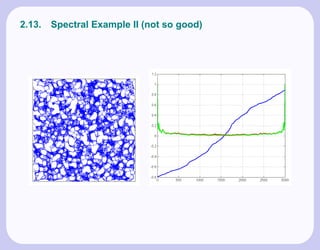
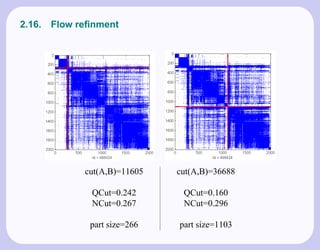
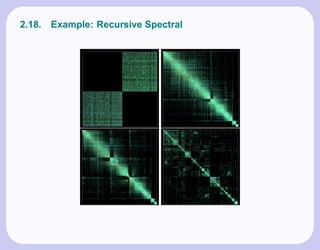
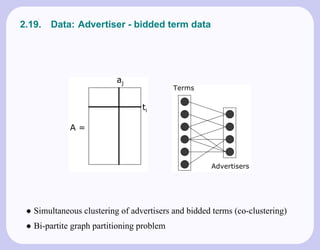
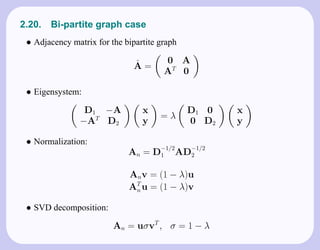
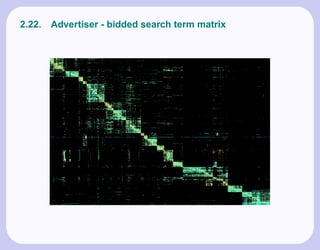
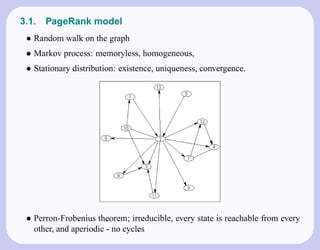
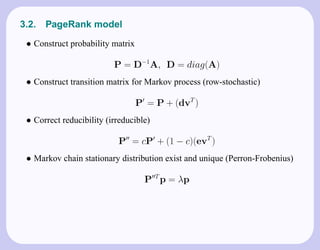
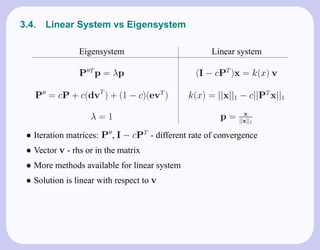
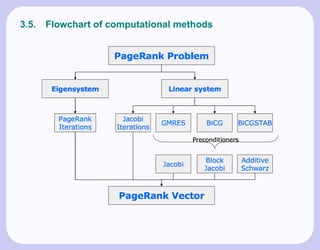
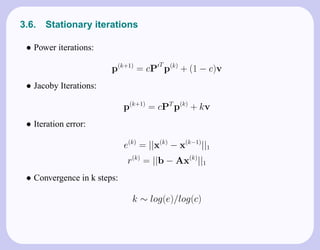
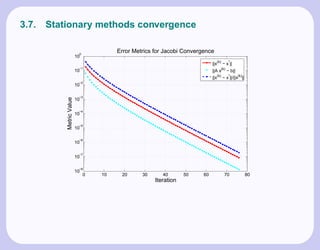
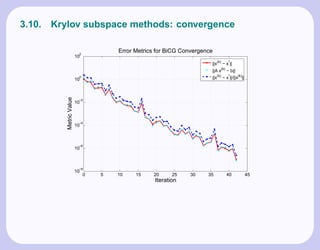
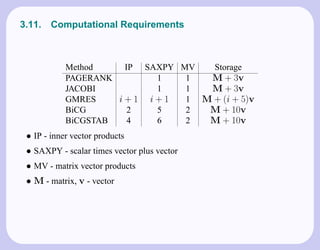
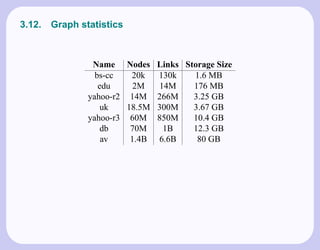
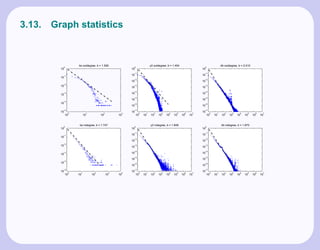
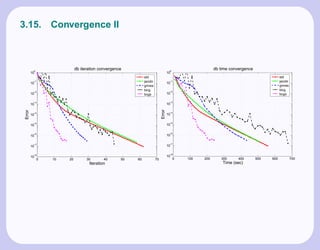
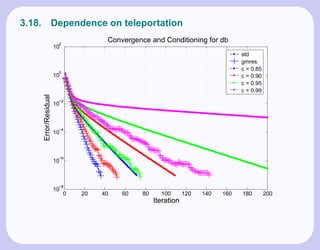
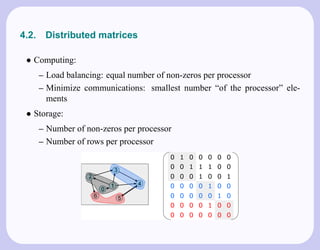
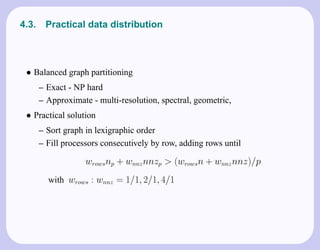
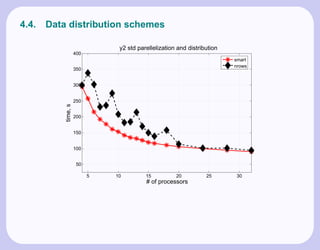
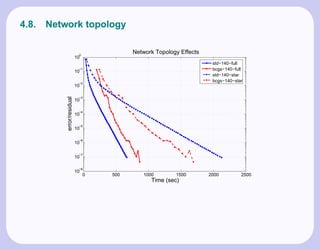
The document discusses the role of numerical linear algebra in improving data and link analysis, focusing on methods like spectral graph partitioning and web graph link analysis. It details practical applications such as clustering of advertisers and bidded terms in market data and introduces Krylov subspace methods for efficient solutions in algorithms like PageRank. The speaker also highlights implementation challenges and future research directions.