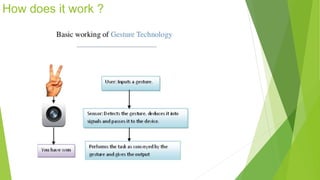
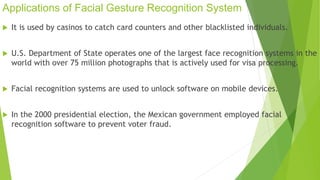
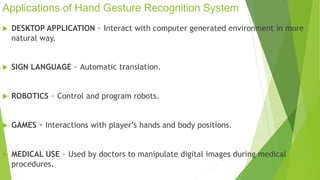
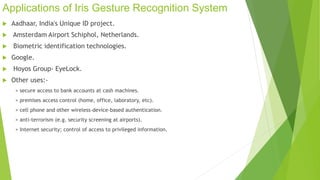
Gesture recognition is a form of non-verbal communication where visible body actions convey messages, enabling computers to recognize human gestures for device control. Applications include facial recognition for security and identification, hand gesture recognition for gaming and medical uses, and iris recognition for secure access systems. These technologies are utilized in various sectors such as security, healthcare, and financial services.