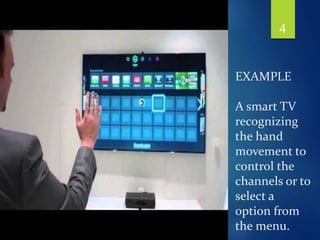
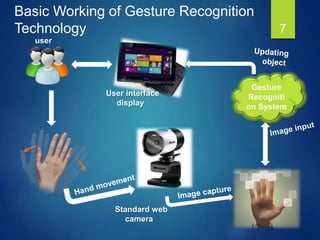
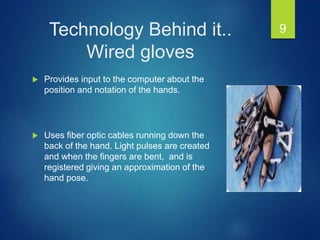
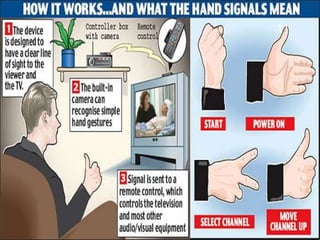
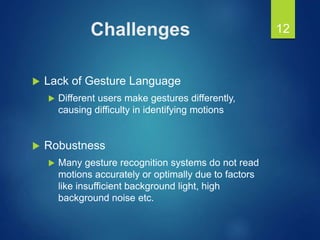
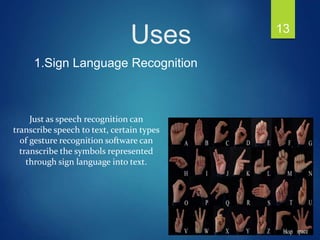
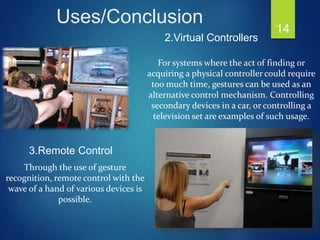
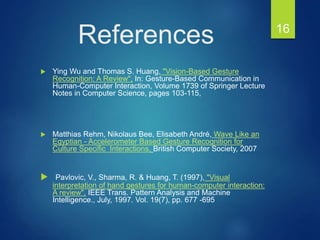
This document provides an overview of gesture recognition technology. It begins with introducing gestures as a form of non-verbal communication and defines gesture recognition as interpreting human gestures through mathematical algorithms. It then discusses the motivation for gesture recognition, including its naturalness and applications in overcoming interaction problems with traditional input devices. The document outlines different types of gestures, input devices like gloves and cameras, challenges like developing standardized gesture languages, and uses like sign language recognition, virtual controllers, and assisting disabled individuals. It concludes with references for further reading.