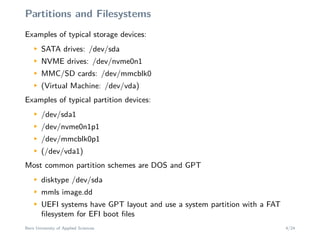
This document provides an overview of a workshop on forensic artifacts in modern Linux systems. It will cover topics such as partitions and filesystems, boot loaders, the Linux file system layout, systemd configuration for services and scheduled tasks, installed software and packages, log files and the systemd journal. The workshop format will involve both presentations and demonstrations of analyzing disk images and artifacts. It is aimed at forensic investigators and showing what can be discovered from compromised, criminal, or seized Linux systems.