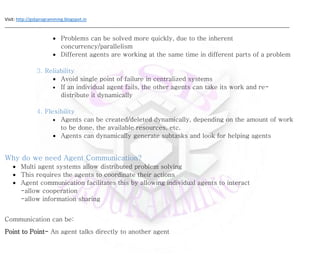
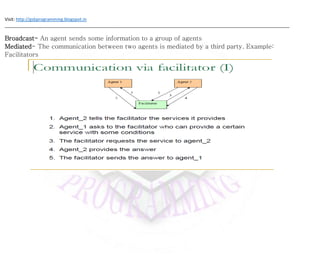
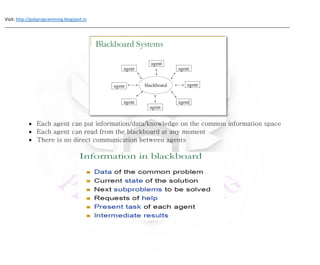
Agents in a multi-agent system can communicate and cooperate to solve problems. They communicate through various methods like point-to-point, broadcast, or mediated communication to coordinate actions and share information. Common communication approaches include blackboard-based communication where agents access a shared information space, and message passing where agents directly exchange varied information to facilitate cooperation.