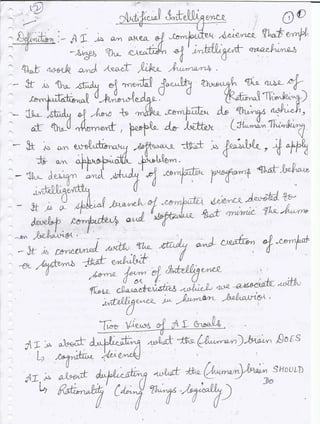
Artificial Intelligence Notes- Set2
•
8 likes•4,356 views
Introduction to AI, Sub areas, Pros, Cons
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
HCI is the study, planning, design of the interaction between humans and computers. A human’s interaction with the outside world occurs through information being received and sent: input and output. In an interaction with a computer the user
receives information that is output by the computer, and responds by providing input to the computer.Human Computer Interaction - INPUT OUTPUT CHANNELS

Human Computer Interaction - INPUT OUTPUT CHANNELSInternational Institute of Information Technology (I²IT)
More Related Content
What's hot
HCI is the study, planning, design of the interaction between humans and computers. A human’s interaction with the outside world occurs through information being received and sent: input and output. In an interaction with a computer the user
receives information that is output by the computer, and responds by providing input to the computer.Human Computer Interaction - INPUT OUTPUT CHANNELS

Human Computer Interaction - INPUT OUTPUT CHANNELSInternational Institute of Information Technology (I²IT)
What's hot (20)
Cricket match outcome prediction using machine learning

Cricket match outcome prediction using machine learning
Python Programming ADP VTU CSE 18CS55 Module 1 Chapter 1

Python Programming ADP VTU CSE 18CS55 Module 1 Chapter 1
Python Programming ADP VTU CSE 18CS55 Module 4 Chapter 1

Python Programming ADP VTU CSE 18CS55 Module 4 Chapter 1
Human Computer Interaction - INPUT OUTPUT CHANNELS

Human Computer Interaction - INPUT OUTPUT CHANNELS
VTU Network & cyber security (1-5 Module) Full notes

VTU Network & cyber security (1-5 Module) Full notes
Viewers also liked
Viewers also liked (6)
Explain Communication among agents in Artificial Intelligence

Explain Communication among agents in Artificial Intelligence
More from Gurpreet singh
More from Gurpreet singh (20)
Understanding Flex Fields with Accounting Flexfields(Chart of Accounts) in O...

Understanding Flex Fields with Accounting Flexfields(Chart of Accounts) in O...
IO Streams, Serialization, de-serialization, autoboxing

IO Streams, Serialization, de-serialization, autoboxing
Recently uploaded
Recently uploaded (20)
Query optimization and processing for advanced database systems

Query optimization and processing for advanced database systems
PE 459 LECTURE 2- natural gas basic concepts and properties

PE 459 LECTURE 2- natural gas basic concepts and properties
Digital Communication Essentials: DPCM, DM, and ADM .pptx

Digital Communication Essentials: DPCM, DM, and ADM .pptx
Electromagnetic relays used for power system .pptx

Electromagnetic relays used for power system .pptx
Cara Menggugurkan Sperma Yang Masuk Rahim Biyar Tidak Hamil

Cara Menggugurkan Sperma Yang Masuk Rahim Biyar Tidak Hamil
Standard vs Custom Battery Packs - Decoding the Power Play

Standard vs Custom Battery Packs - Decoding the Power Play
8086 Microprocessor Architecture: 16-bit microprocessor

8086 Microprocessor Architecture: 16-bit microprocessor
NO1 Top No1 Amil Baba In Azad Kashmir, Kashmir Black Magic Specialist Expert ...

NO1 Top No1 Amil Baba In Azad Kashmir, Kashmir Black Magic Specialist Expert ...
"Lesotho Leaps Forward: A Chronicle of Transformative Developments"

"Lesotho Leaps Forward: A Chronicle of Transformative Developments"
