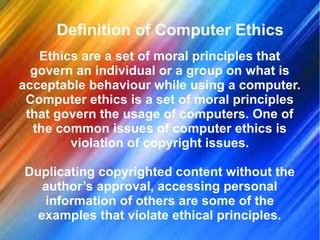
Internet ethics refers to the acceptable behavior for using the internet, emphasizing honesty and respect for others' rights. It encompasses computer ethics, which includes principles like not harming others, respecting copyright, and safeguarding personal information. Ethical rules are critical for responsible computer and internet usage, highlighting the importance of respecting privacy and adhering to laws.