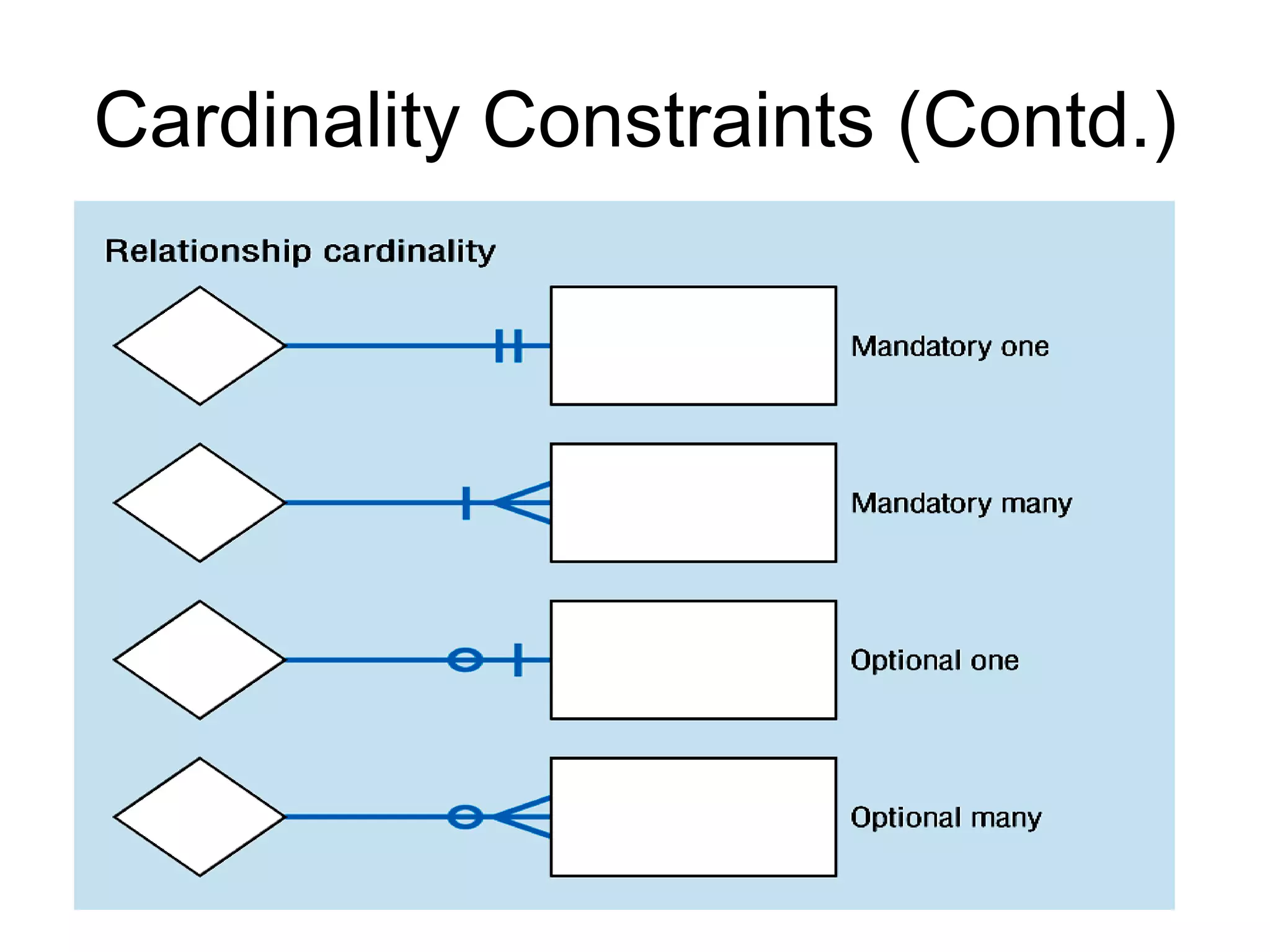
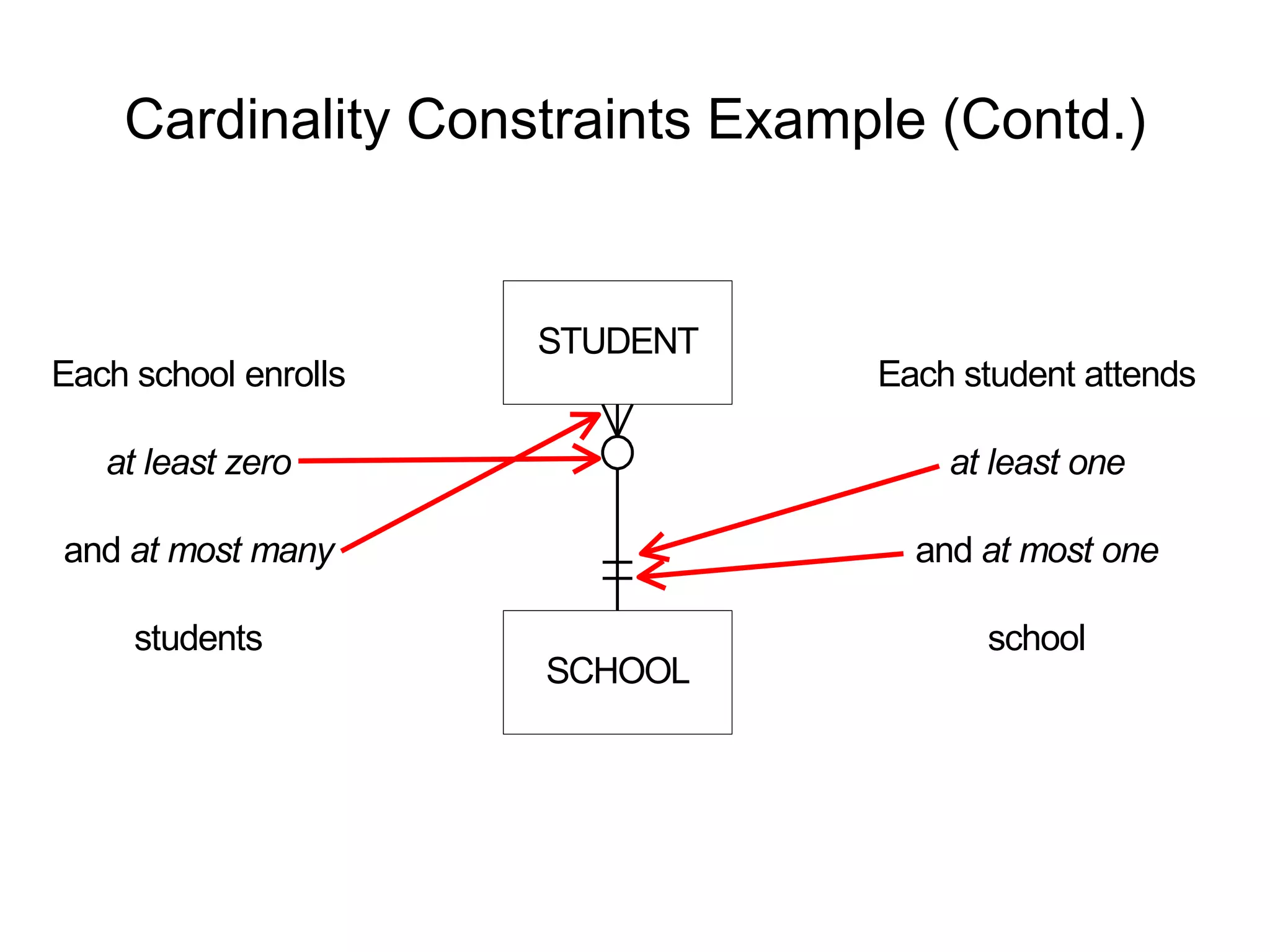
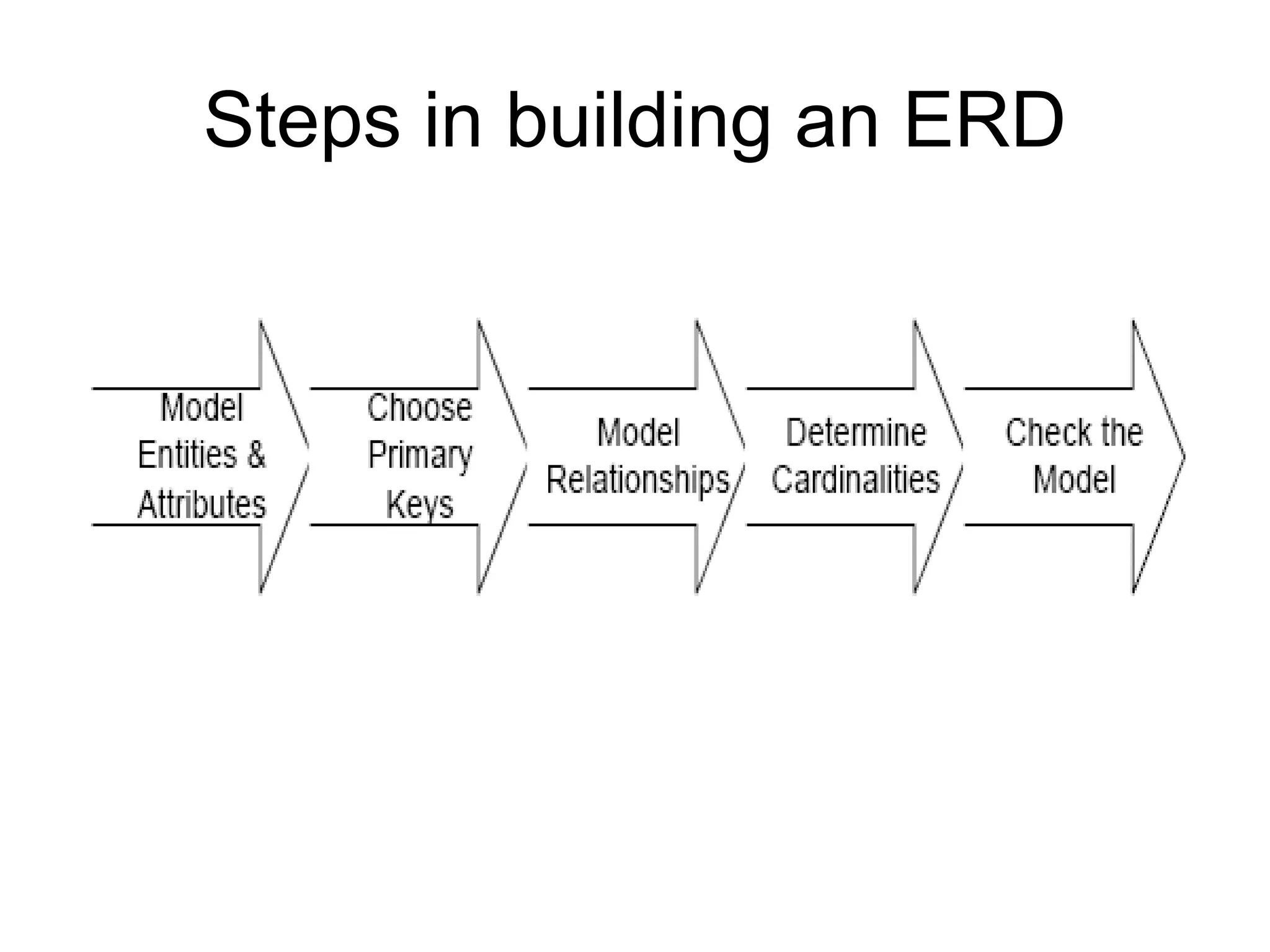
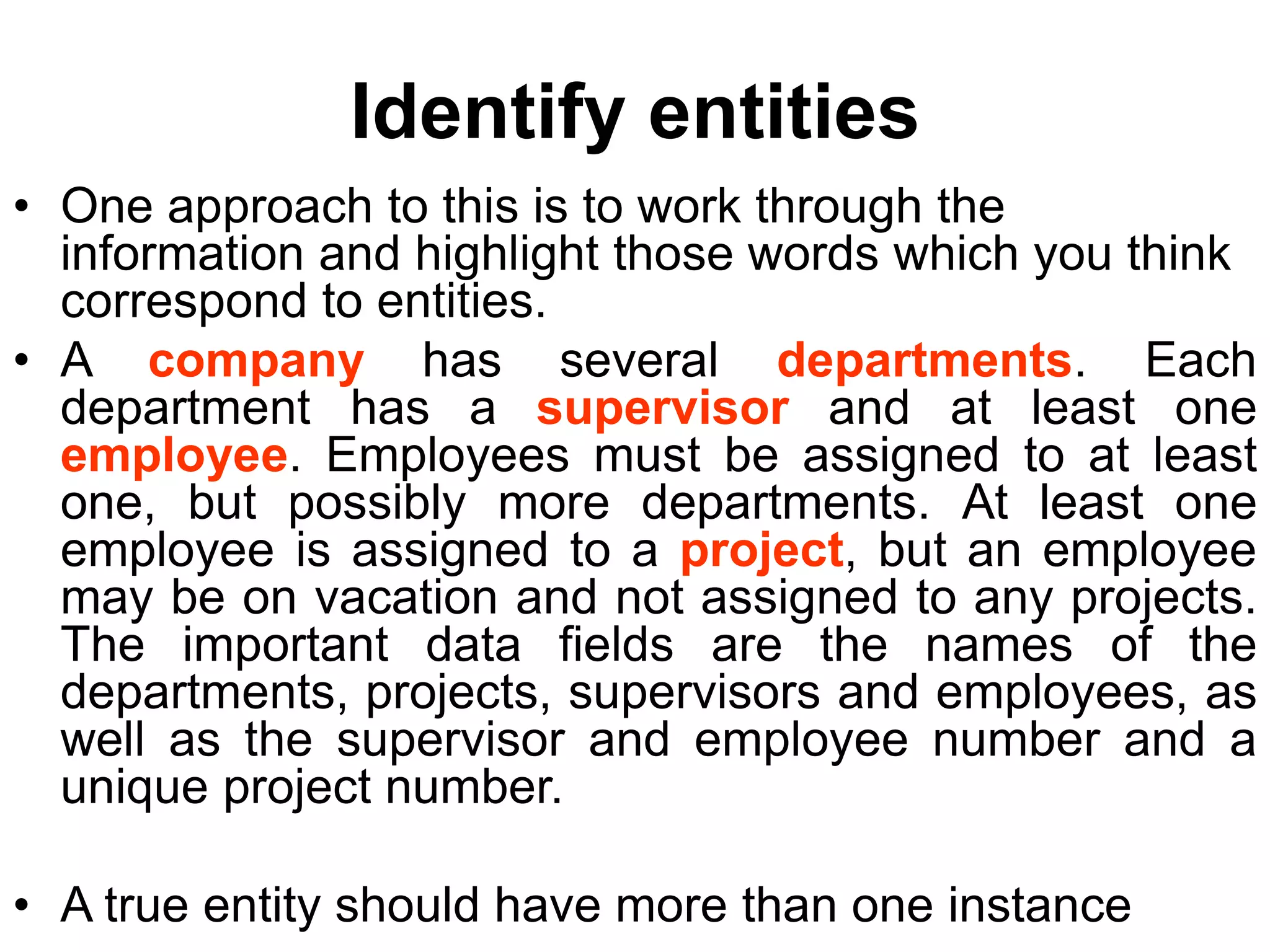
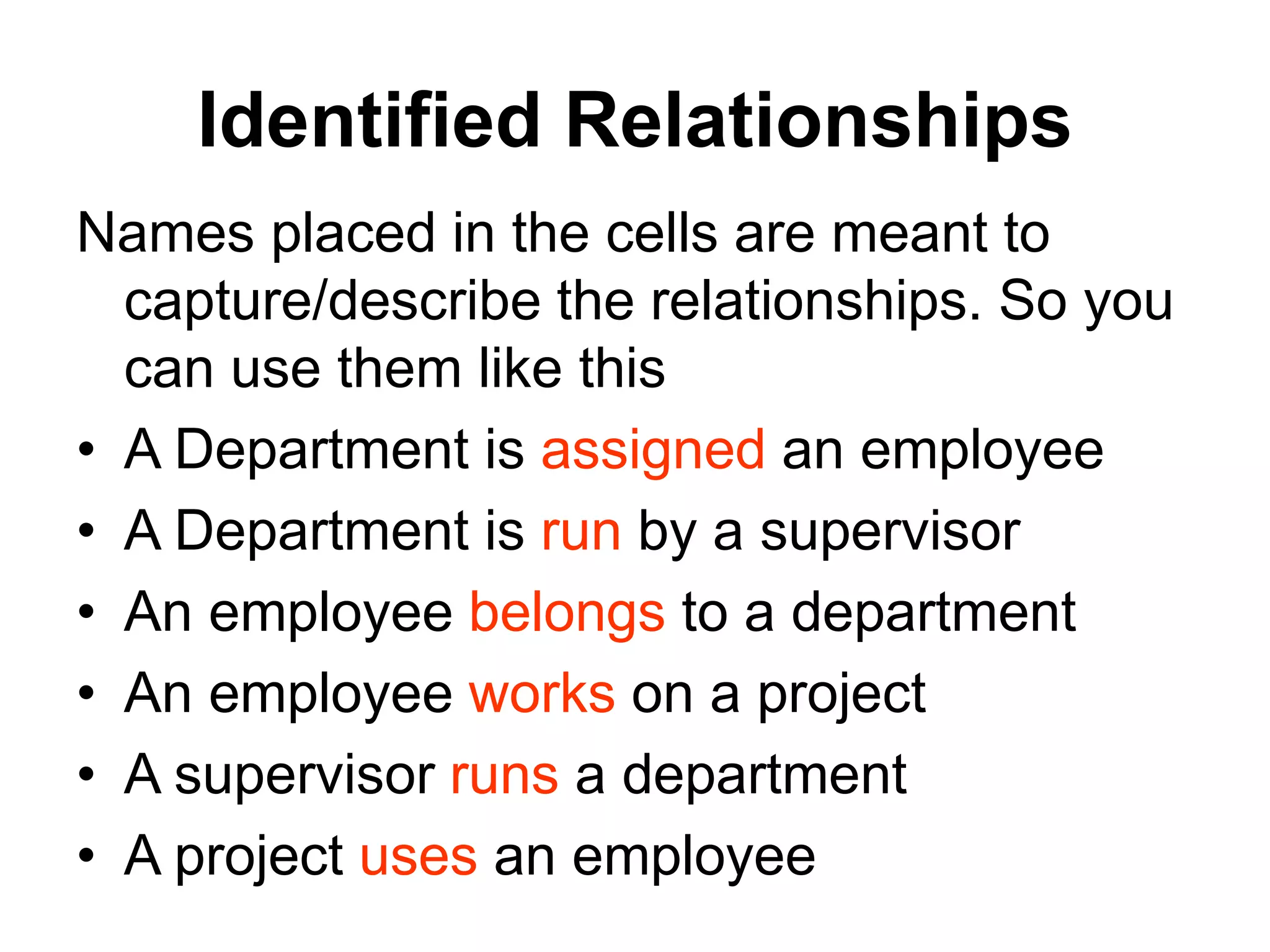
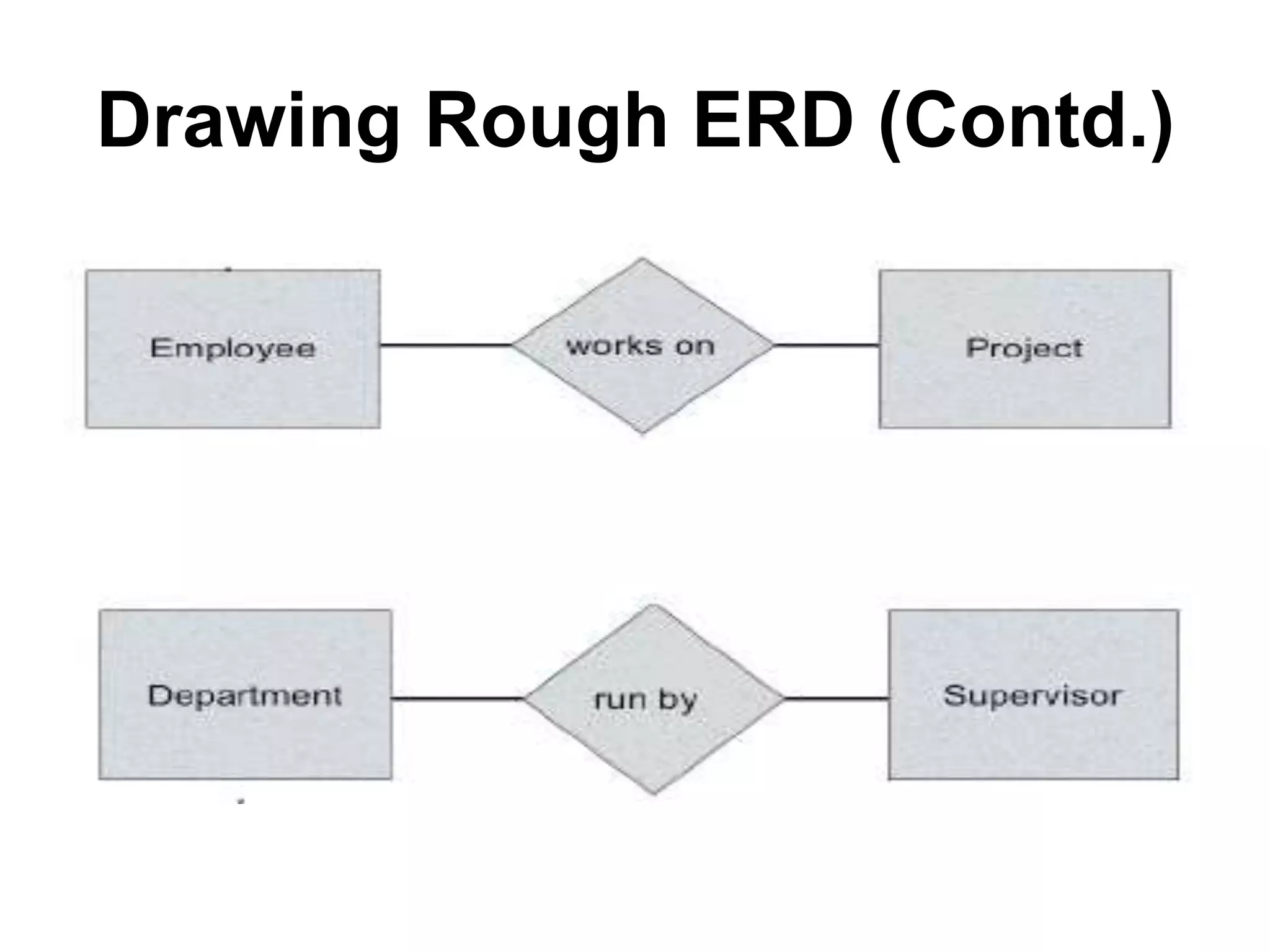
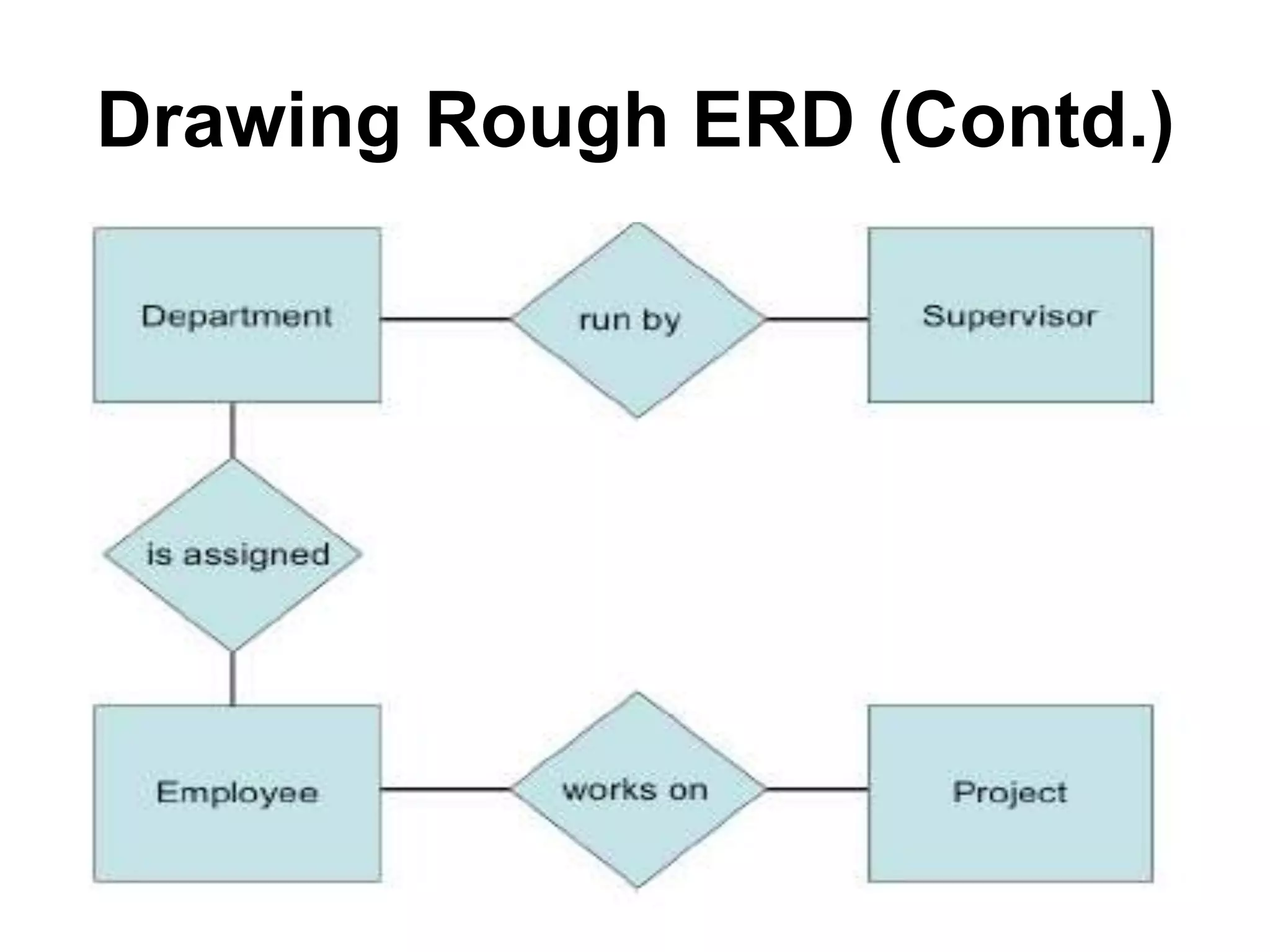
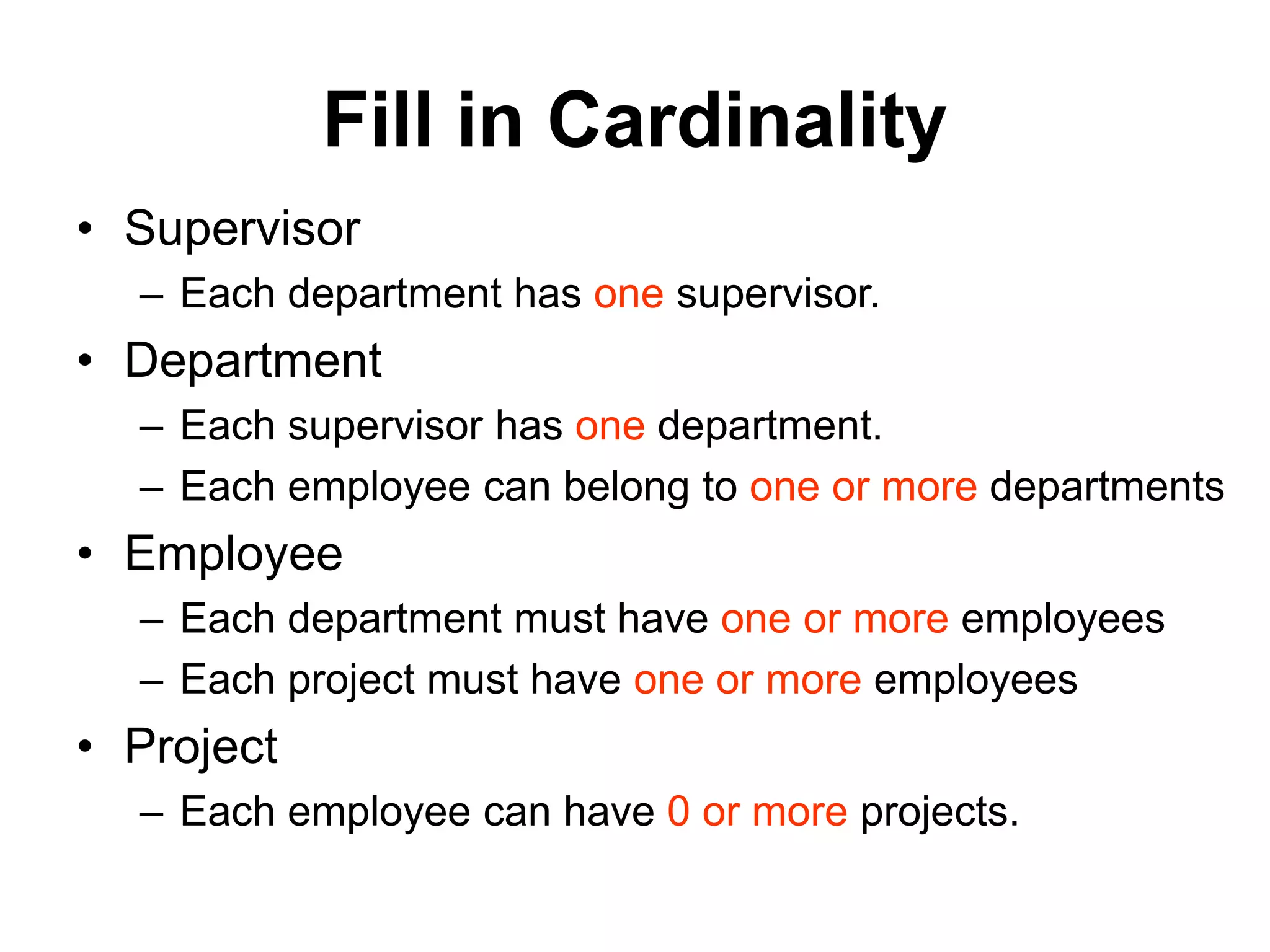
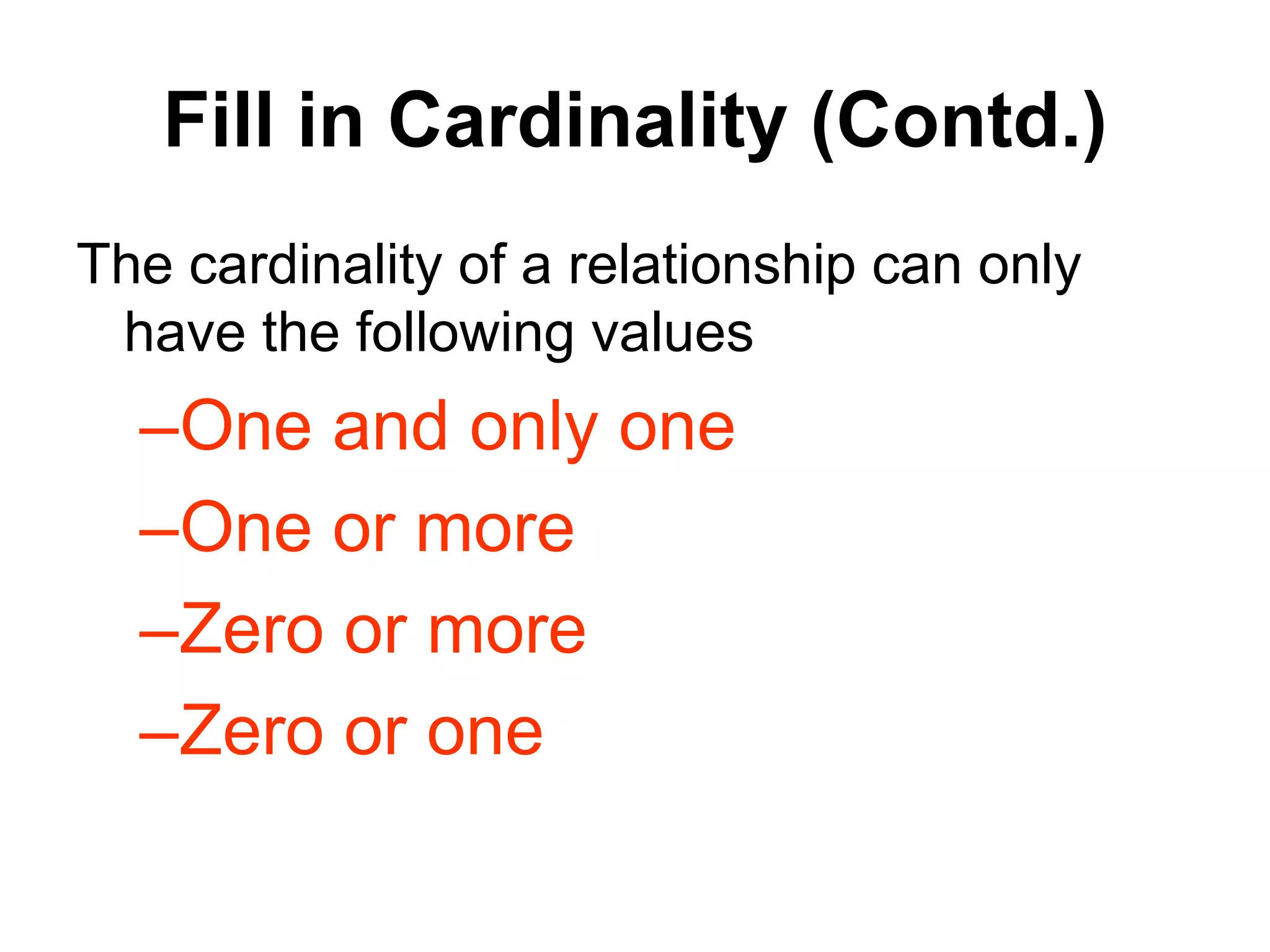
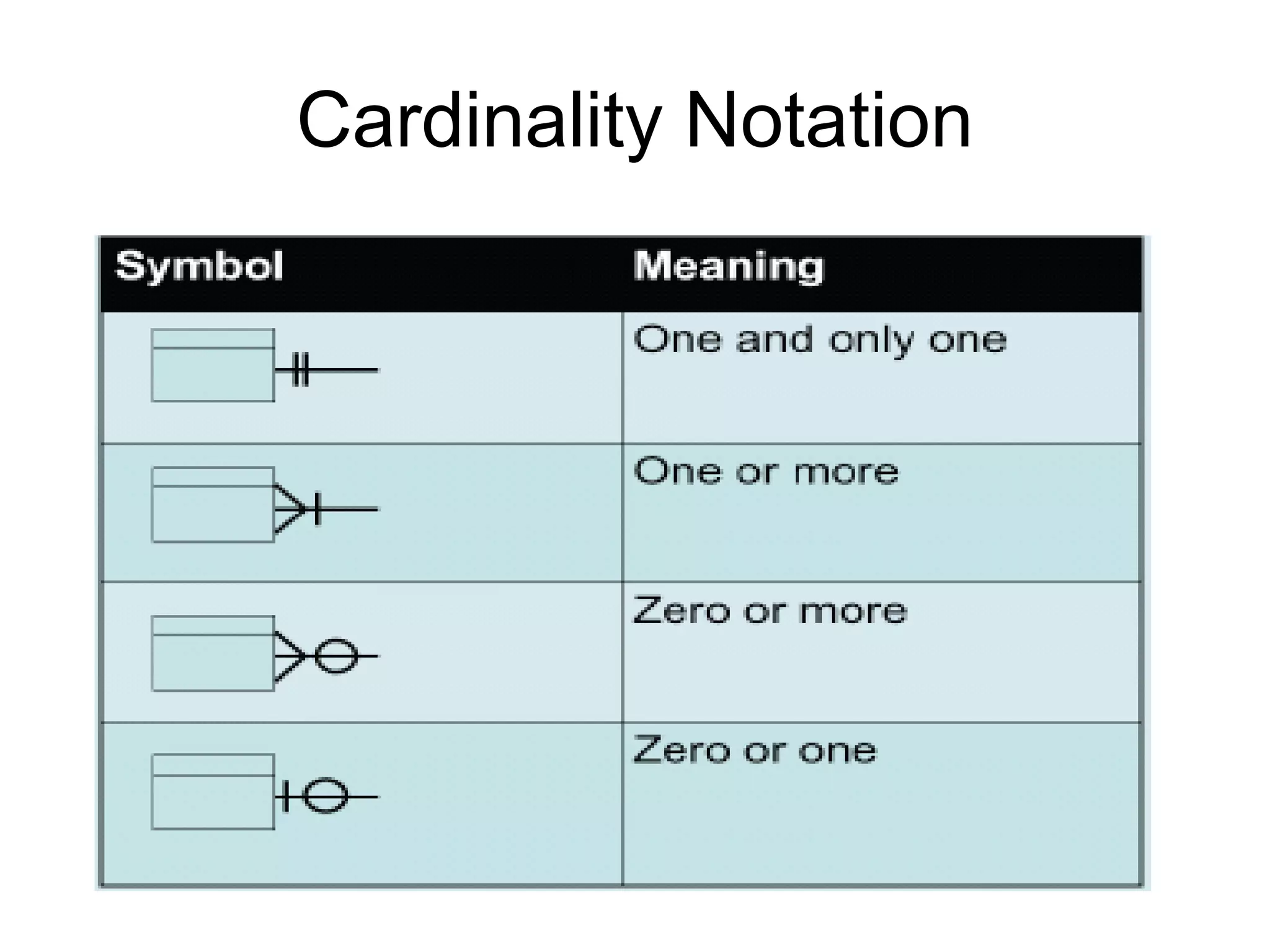
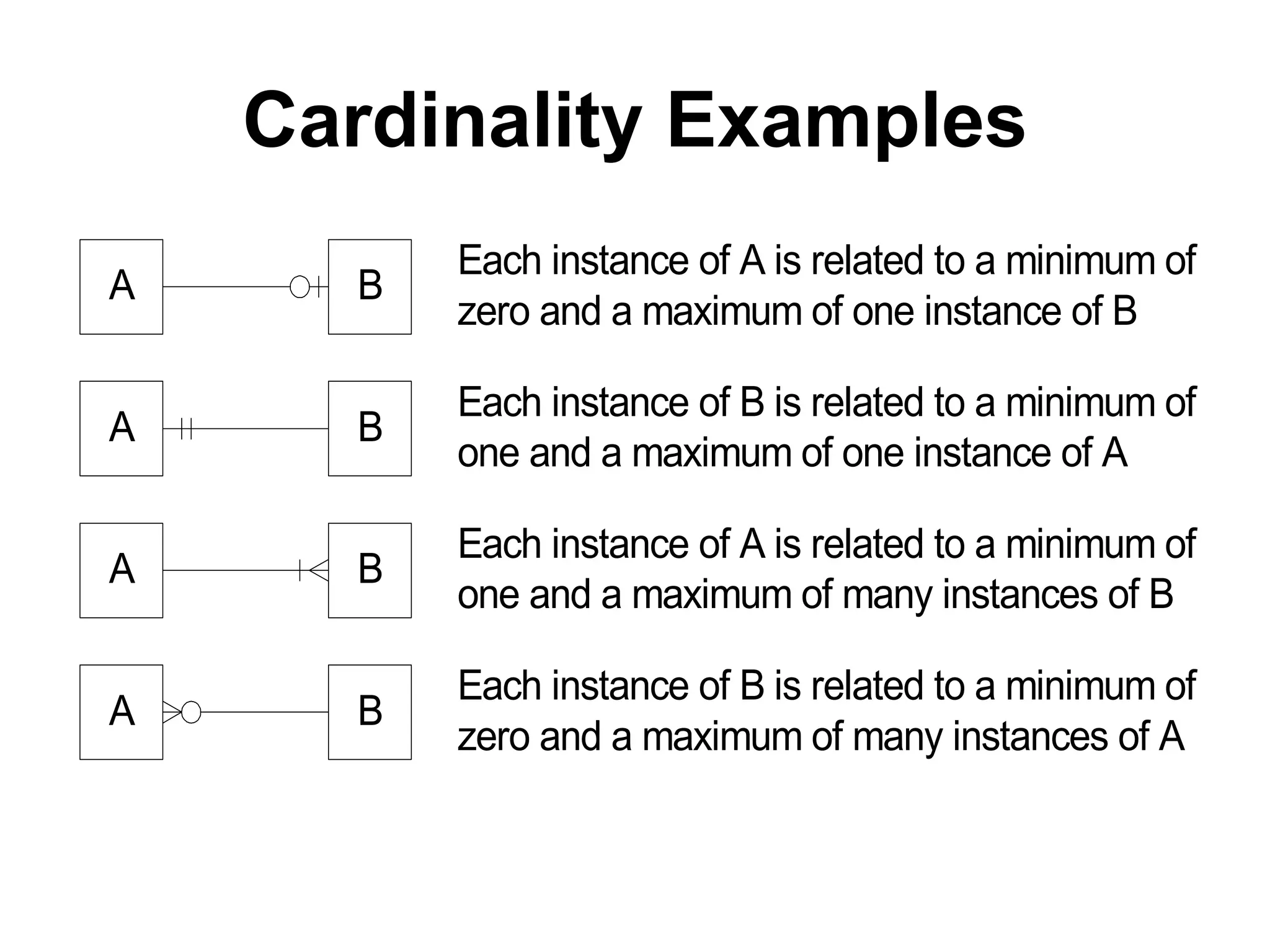
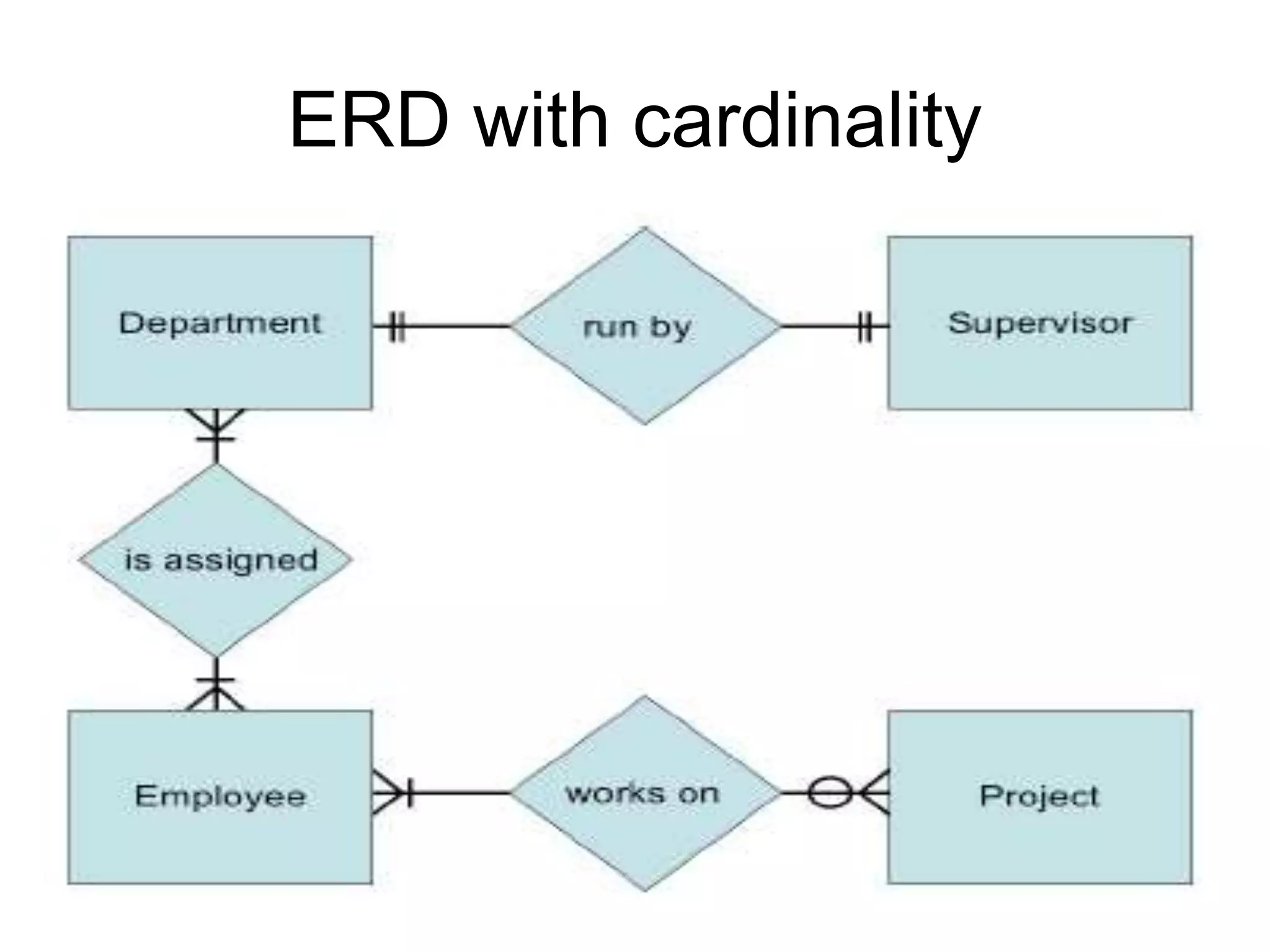
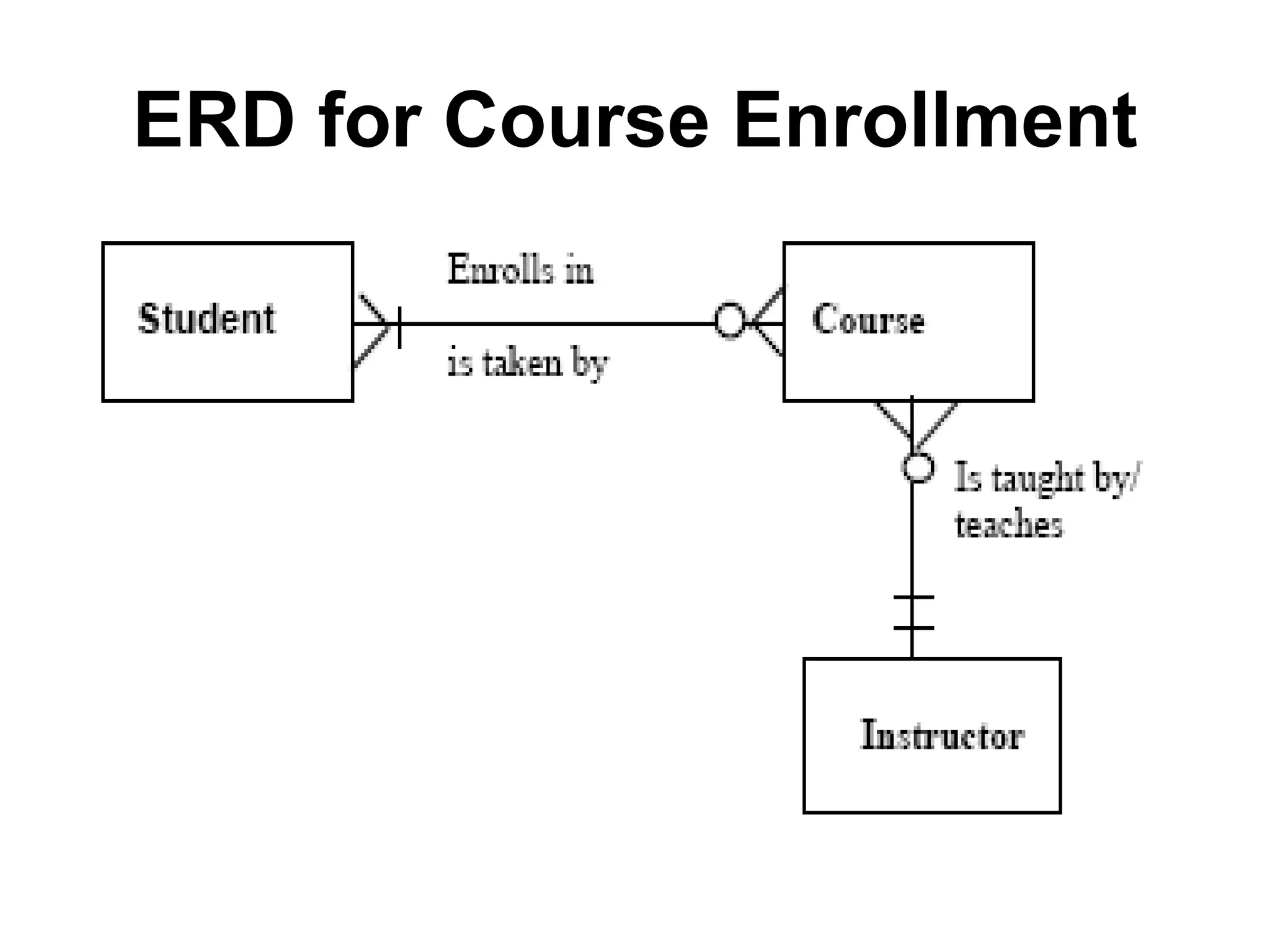
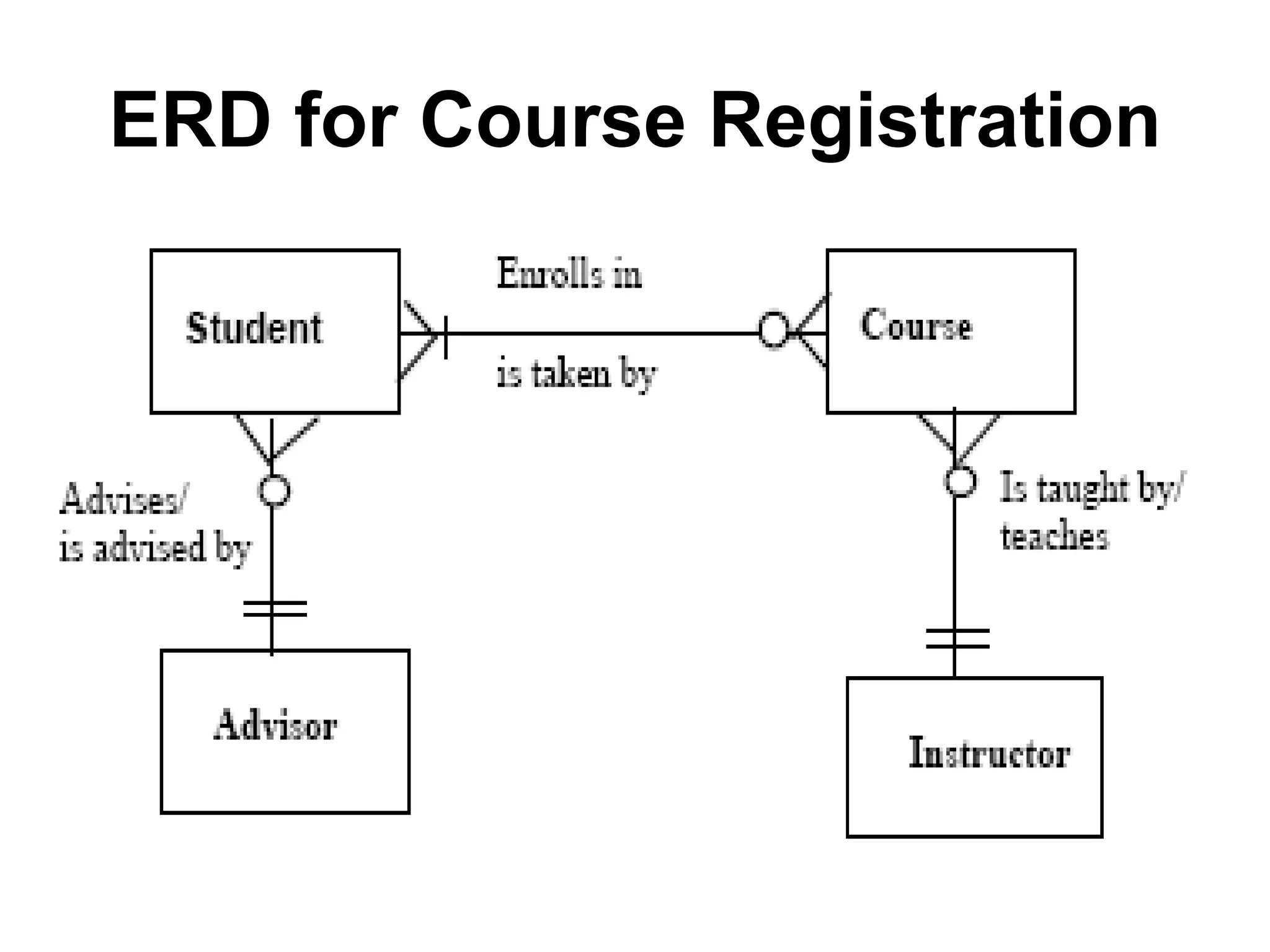
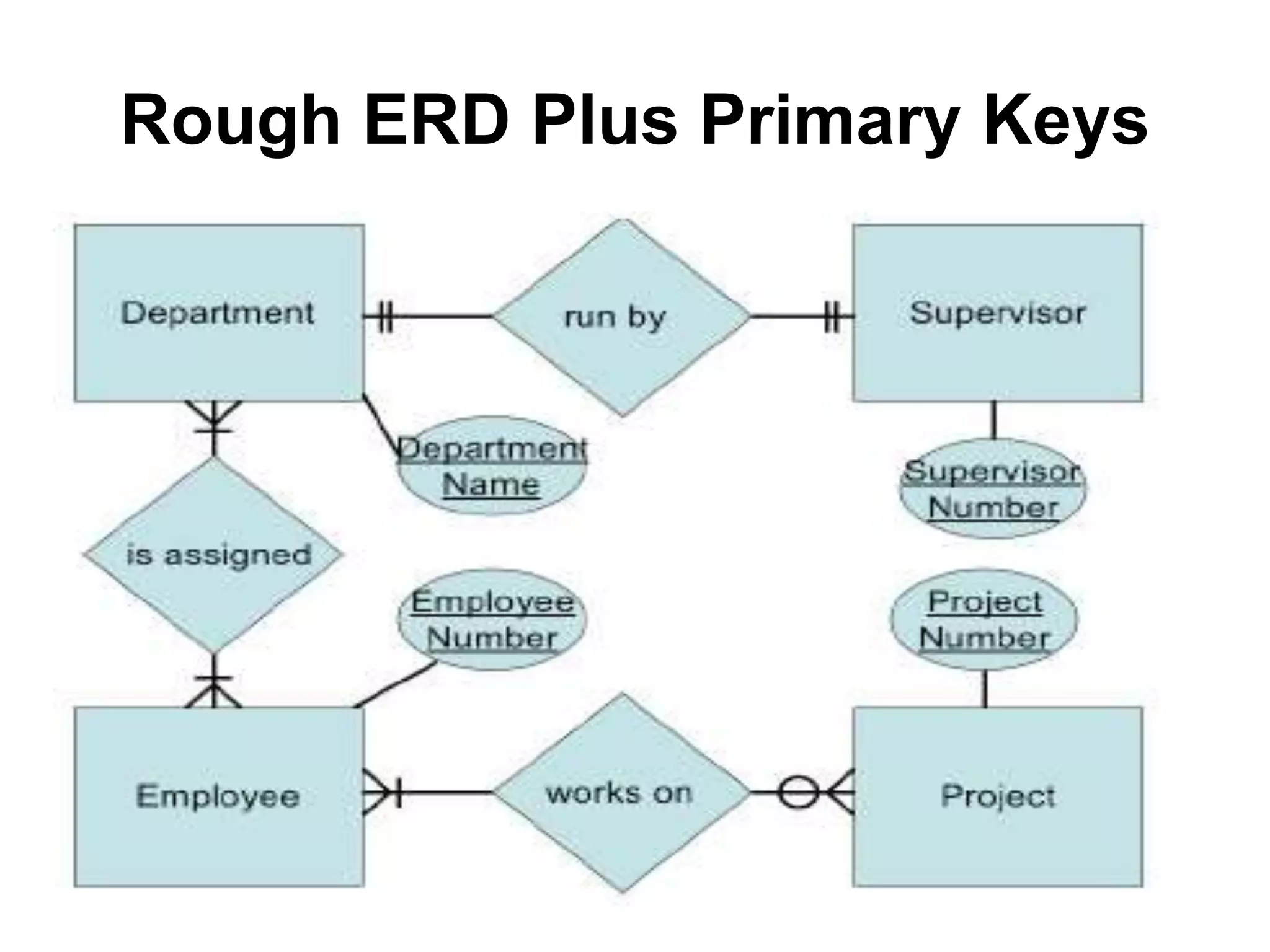
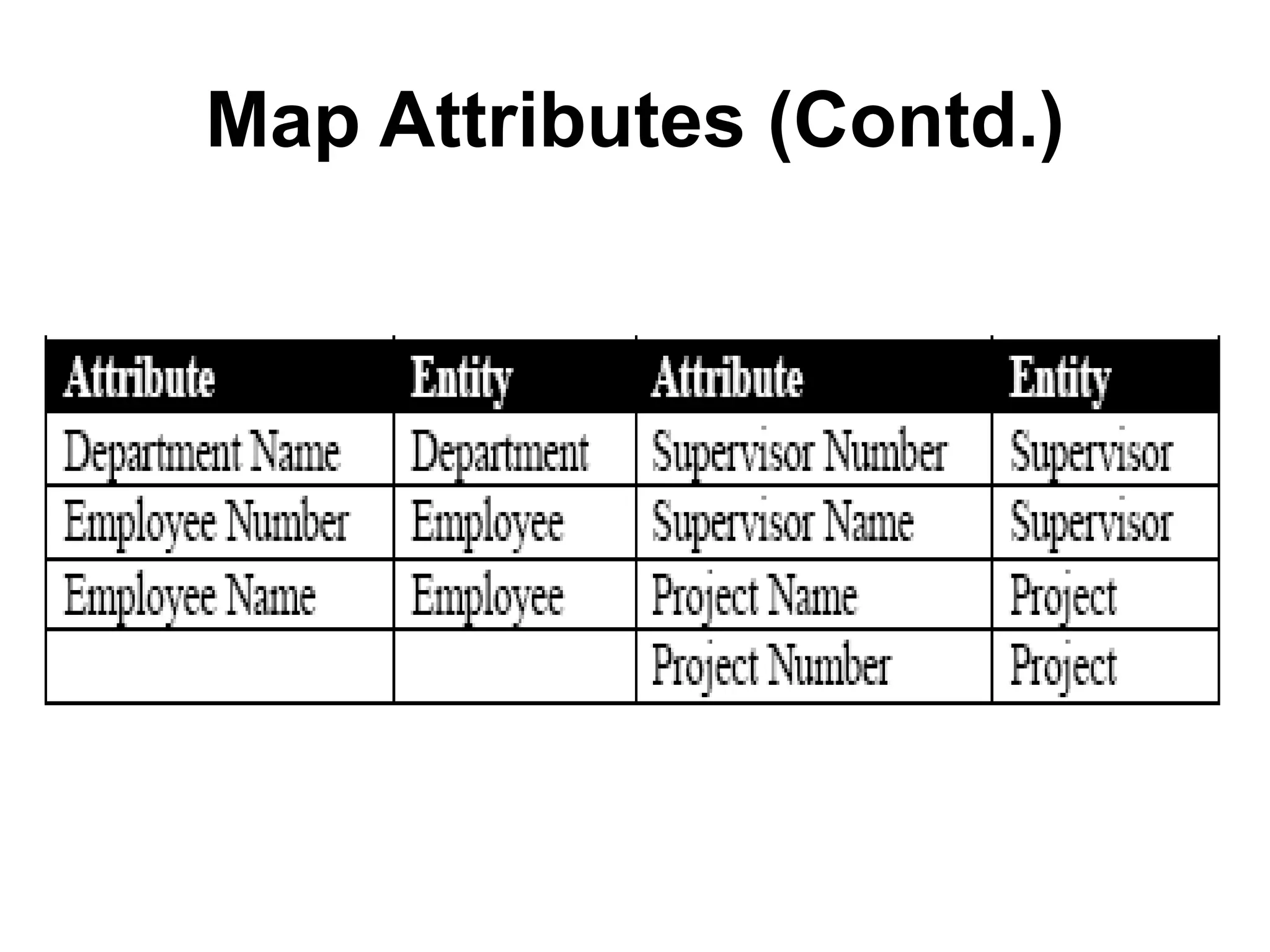
The document provides information on entity relationship diagrams (ERDs), including the objectives, components, and steps to create an ERD. It defines key ERD concepts like entities, attributes, relationships, and cardinality. It describes the entity modeling process and discusses how to recognize entities, attributes, relationships, and cardinalities in a database. It outlines the general steps to create an ERD, including identifying entities, finding relationships between entities, drawing a rough ERD, defining primary keys, identifying attributes, mapping attributes to entities, and drawing a fully attributed ERD. Sample ERDs are provided to illustrate concepts like cardinality constraints.